Table of Contents
- 5.1. The MySQL Server
- 5.1.1. Server Option and Variable Reference
- 5.1.2. Server Command Options
- 5.1.3. Server Options for Loading Plugins
- 5.1.4. Server System Variables
- 5.1.5. Session System Variables
- 5.1.6. Using System Variables
- 5.1.7. Server Status Variables
- 5.1.8. Server SQL Modes
- 5.1.9. Server-Side Help
- 5.1.10. Server Response to Signals
- 5.1.11. The Shutdown Process
- 5.2. MySQL Server Logs
- 5.3. General Security Issues
- 5.4. The MySQL Access Privilege System
- 5.5. MySQL User Account Management
- 5.6. Running Multiple MySQL Servers on the Same Machine
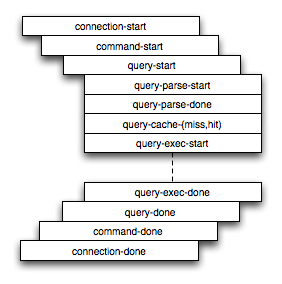
- 5.7. Tracing mysqld Using DTrace
MySQL Server (mysqld) is the main program that does most of the work in a MySQL installation. This section provides an overview of MySQL Server and covers topics that deal with administering a MySQL installation:
Server configuration
The server log files
Security issues and user-account management
Management of multiple servers on a single machine
- 5.1.1. Server Option and Variable Reference
- 5.1.2. Server Command Options
- 5.1.3. Server Options for Loading Plugins
- 5.1.4. Server System Variables
- 5.1.5. Session System Variables
- 5.1.6. Using System Variables
- 5.1.7. Server Status Variables
- 5.1.8. Server SQL Modes
- 5.1.9. Server-Side Help
- 5.1.10. Server Response to Signals
- 5.1.11. The Shutdown Process
mysqld is the MySQL server. The following discussion covers these MySQL server configuration topics:
Startup options that the server supports
Server system variables
Server status variables
How to set the server SQL mode
The server shutdown process
Note
Not all storage engines are supported by all MySQL server binaries
and configurations. To find out how to determine which storage
engines your MySQL server installation supports, see
Section 12.5.5.17, “SHOW ENGINES Syntax”.
The following table provides a list of all the command line
options, server and status variables applicable within
mysqld.
The table lists command-line options (Cmd-line), options valid in configuration files (Option file), server system variables (System Var), and status variables (Status var) in one unified list, with notification of where each option/variable is valid. If a server option set on the command line or in an option file differs from the name of the corresponding server system or status variable, the variable name is noted immediately below the corresponding option. For status variables, the scope of the variable is shown (Scope) as either global, session, or both. Please see the corresponding sections for details on setting and using the options and variables. Where appropriate, a direct link to further information on the item as available.
Table 5.1. Option/Variable Summary
When you start the mysqld server, you can specify program options using any of the methods described in Section 4.2.3, “Specifying Program Options”. The most common methods are to provide options in an option file or on the command line. However, in most cases it is desirable to make sure that the server uses the same options each time it runs. The best way to ensure this is to list them in an option file. See Section 4.2.3.3, “Using Option Files”.
MySQL Enterprise For expert advice on setting command options, subscribe to the MySQL Enterprise Monitor. For more information, see http://www.mysql.com/products/enterprise/advisors.html.
mysqld reads options from the
[mysqld] and [server]
groups. mysqld_safe reads options from the
[mysqld], [server],
[mysqld_safe], and
[safe_mysqld] groups.
mysql.server reads options from the
[mysqld] and [mysql.server]
groups.
An embedded MySQL server usually reads options from the
[server], [embedded], and
[
groups, where xxxxx_SERVER]xxxxx is the name of the
application into which the server is embedded.
mysqld accepts many command options. For a brief summary, execute mysqld --help. To see the full list, use mysqld --verbose --help.
The following list shows some of the most common server options. Additional options are described in other sections:
Options that affect security: See Section 5.3.4, “Security-Related mysqld Options”.
SSL-related options: See Section 5.5.6.3, “SSL Command Options”.
Binary log control options: See Section 5.2.4, “The Binary Log”.
Replication-related options: See Section 16.1.3, “Replication and Binary Logging Options and Variables”.
Options for loading plugins such as pluggable storage engines: See Section 5.1.3, “Server Options for Loading Plugins”.
Options specific to particular storage engines: See Section 13.5.1, “
MyISAMStartup Options”, and Section 13.6.3, “InnoDBStartup Options and System Variables”.
You can also set the values of server system variables by using variable names as options, as described at the end of this section.
Some options control the size of buffers or caches. For a given buffer, the server might need to allocate internal data structures. These structures typically are allocated from the total memory allocated to the buffer, and the amount of space required might be platform dependent. This means that when you assign a value to an option that controls a buffer size, the amount of space actually available might differ from the value assigned. In some cases, the amount might be less than the value assigned. It is also possible that the server will adjust a value upward. For example, if you assign a value of 0 to an option for which the minimal value is 1024, the server will set the value to 1024.
Values for buffer sizes, lengths, and stack sizes are given in bytes unless otherwise specified.
Some options take file name values. Unless otherwise specified,
the default file location is the data directory if the value is a
relative path name. To specify the location explicitly, use an
absolute path name. Suppose that the data directory is
/var/mysql/data. If a file-valued option is
given as a relative path name, it will be located under
/var/mysql/data. If the value is an absolute
path name, its location is as given by the path name.
--help,-?Command-Line Format -?Config-File Format helpDisplay a short help message and exit. Use both the
--verboseand--helpoptions to see the full message.Command-Line Format --allow-suspicious-udfsConfig-File Format allow-suspicious-udfsPermitted Values Type booleanDefault FALSEThis option controls whether user-defined functions that have only an
xxxsymbol for the main function can be loaded. By default, the option is off and only UDFs that have at least one auxiliary symbol can be loaded; this prevents attempts at loading functions from shared object files other than those containing legitimate UDFs. See Section 22.3.2.6, “User-Defined Function Security Precautions”.Command-Line Format --ansiConfig-File Format ansiUse standard (ANSI) SQL syntax instead of MySQL syntax. For more precise control over the server SQL mode, use the
--sql-modeoption instead. See Section 1.8.3, “Running MySQL in ANSI Mode”, and Section 5.1.8, “Server SQL Modes”.Command-Line Format --basedir=nameConfig-File Format basedirOption Sets Variable Yes, basedirVariable Name basedirVariable Scope Global Dynamic Variable No Permitted Values Type filenameThe path to the MySQL installation directory. All paths are usually resolved relative to this directory.
Command-Line Format --big-tablesConfig-File Format big-tablesOption Sets Variable Yes, big_tablesVariable Name big-tablesVariable Scope Session Dynamic Variable Yes Permitted Values Type booleanAllow large result sets by saving all temporary sets in files. This option prevents most “table full” errors, but also slows down queries for which in-memory tables would suffice. Since MySQL 3.23.2, the server is able to handle large result sets automatically by using memory for small temporary tables and switching to disk tables where necessary.
Command-Line Format --bind-address=nameConfig-File Format bind-addressPermitted Values Type stringDefault 0.0.0.0Range 0.0.0.0-255.255.255.255The IP address to bind to. Only one address can be selected. If this option is specified multiple times, the last address given is used.
If no address or
0.0.0.0is specified, the server listens on all interfaces.--binlog-format={ROW|STATEMENT|MIXED}Command-Line Format --binlog-formatConfig-File Format binlog-formatOption Sets Variable Yes, binlog_formatVariable Name binlog_formatVariable Scope Both Dynamic Variable Yes Permitted Values Type enumerationDefault STATEMENTValid Values ROW,STATEMENT,MIXEDSpecify whether to use row-based, statement-based, or mixed replication. Statement-based is the default in MySQL 5.5. See Section 16.1.2, “Replication Formats”.
Previous to MySQL 5.5, setting the binary logging format without enabling binary logging prevented the MySQL server from starting. In MySQL 5.5, the server starts in such cases, the
binlog_formatglobal system variable is set, and a warning is logged instead of an error. (Bug#42928)Command-Line Format --bootstrapConfig-File Format bootstrapThis option is used by the mysql_install_db script to create the MySQL privilege tables without having to start a full MySQL server.
This option is unavailable if MySQL was configured with the
--disable-grant-optionsoption. See Section 2.10.2, “Typical configure Options”.Command-Line Format --character-sets-dir=nameConfig-File Format character-sets-dirOption Sets Variable Yes, character_sets_dirVariable Name character-sets-dirVariable Scope Global Dynamic Variable No Permitted Values Type filenameThe directory where character sets are installed. See Section 9.5, “Character Set Configuration”.
--character-set-client-handshakeCommand-Line Format --character-set-client-handshakeConfig-File Format character-set-client-handshakePermitted Values Type booleanDefault TRUEDon't ignore character set information sent by the client. To ignore client information and use the default server character set, use
--skip-character-set-client-handshake; this makes MySQL behave like MySQL 4.0.--character-set-filesystem=charset_nameCommand-Line Format --character-set-filesystem=nameConfig-File Format character-set-filesystemOption Sets Variable Yes, character_set_filesystemVariable Name character_set_filesystemVariable Scope Both Dynamic Variable Yes Permitted Values Type stringThe file system character set. This option sets the
character_set_filesystemsystem variable.--character-set-server=,charset_name-Ccharset_nameCommand-Line Format --character-set-serverConfig-File Format character-set-serverOption Sets Variable Yes, character_set_serverVariable Name character_set_serverVariable Scope Both Dynamic Variable Yes Permitted Values Type stringUse
charset_nameas the default server character set. See Section 9.5, “Character Set Configuration”. If you use this option to specify a nondefault character set, you should also use--collation-serverto specify the collation.--chroot=,path-rpathCommand-Line Format --chroot=nameConfig-File Format chrootPermitted Values Type filenamePut the mysqld server in a closed environment during startup by using the
chroot()system call. This is a recommended security measure. Note that use of this option somewhat limitsLOAD DATA INFILEandSELECT ... INTO OUTFILE.--collation-server=collation_nameCommand-Line Format --collation-serverConfig-File Format collation-serverOption Sets Variable Yes, collation_serverVariable Name collation_serverVariable Scope Both Dynamic Variable Yes Permitted Values Type stringUse
collation_nameas the default server collation. See Section 9.5, “Character Set Configuration”.Command-Line Format --consoleConfig-File Format consolePlatform Specific windows (Windows only.) Write error log messages to
stderrandstdouteven if--log-erroris specified. mysqld does not close the console window if this option is used.Command-Line Format --core-fileConfig-File Format core-filePermitted Values Type booleanDefault FALSEWrite a core file if mysqld dies. The name and location of the core file is system dependent. On Linux, a core file named
core.is written to the current working directory of the process, which for mysqld is the data directory.pidpidrepresents the process ID of the server process. On Mac OS X, a core file namedcore.is written to thepid/coresdirectory. On Solaris, use the coreadm command to specify where to write the core file and how to name it.For some systems, to get a core file you must also specify the
--core-file-sizeoption to mysqld_safe. See Section 4.3.2, “mysqld_safe — MySQL Server Startup Script”. On some systems, such as Solaris, you do not get a core file if you are also using the--useroption. There might be additional restrictions or limitations. For example, it might be necessary to execute ulimit -c unlimited before starting the server. Consult your system documentation.--datadir=,path-hpathCommand-Line Format --datadir=nameConfig-File Format datadirOption Sets Variable Yes, datadirVariable Name datadirVariable Scope Global Dynamic Variable No Permitted Values Type filenameThe path to the data directory.
--debug[=,debug_options]-# [debug_options]Command-Line Format --debug[=debug_options]Config-File Format debugVariable Name debugVariable Scope Both Dynamic Variable Yes Permitted Values Type stringDefault 'd:t:o,/tmp/mysqld.trace'If MySQL is configured with
--with-debug, you can use this option to get a trace file of what mysqld is doing. A typicaldebug_optionsstring is'd:t:o,. The default isfile_name''d:t:i:o,mysqld.trace'. See MySQL Internals: Porting.Using
--with-debugto configure MySQL with debugging support enables you to use the--debug="d,parser_debug"option when you start the server. This causes the Bison parser that is used to process SQL statements to dump a parser trace to the server's standard error output. Typically, this output is written to the error log.This option may be given multiple times. Values that begin with
+or-are added to or subtracted from the previous value. For example,--debug=T--debug=+Psets the value toP:T.Command-Line Format --debug-sync-timeout[=#]Config-File Format debug-sync-timeoutPermitted Values Type numericControls whether the Debug Sync facility for testing and debugging is enabled. Use of Debug Sync requires that MySQL be configured with the
--enable-debug-syncoption (see Section 2.10.2, “Typical configure Options”). If Debug Sync is not compiled in, this option is not available. The option value is a timeout in seconds. The default value is 0, which disables Debug Sync. To enable it, specify a value greater than 0; this value also becomes the default timeout for individual synchronization points. If the option is given without a value, the timeout is set to 300 seconds.For a description of the Debug Sync facility and how to use synchronization points, see MySQL Internals: Test Synchronization.
--default-character-set=(DEPRECATED)charset_nameCommand-Line Format --default-character-set=nameConfig-File Format default-character-setDeprecated 5.0 Permitted Values Type stringUse
charset_nameas the default character set. This option is deprecated in favor of--character-set-server. See Section 9.5, “Character Set Configuration”.--default-character-setwas removed in MySQL 5.5.3.--default-collation=collation_nameCommand-Line Format --default-collation=nameVariable Name default-collationVariable Scope Dynamic Variable No Deprecated 4.1.3 Permitted Values Type stringUse
collation_nameas the default collation. This option is deprecated in favor of--collation-server. See Section 9.5, “Character Set Configuration”.--default-collationwas removed in MySQL 5.5.3.Command-Line Format --default-storage-engine=nameConfig-File Format default-storage-engineSet the default storage engine (table type) for tables. See Chapter 13, Storage Engines.
Command-Line Format --default-time-zone=nameConfig-File Format default-time-zonePermitted Values Type stringSet the default server time zone. This option sets the global
time_zonesystem variable. If this option is not given, the default time zone is the same as the system time zone (given by the value of thesystem_time_zonesystem variable.--delay-key-write[={OFF|ON|ALL}]Command-Line Format --delay-key-write[=name]Config-File Format delay-key-writeOption Sets Variable Yes, delay_key_writeVariable Name delay-key-writeVariable Scope Global Dynamic Variable Yes Permitted Values Type enumerationDefault ONValid Values ON,OFF,ALLSpecify how to use delayed key writes. Delayed key writing causes key buffers not to be flushed between writes for
MyISAMtables.OFFdisables delayed key writes.ONenables delayed key writes for those tables that were created with theDELAY_KEY_WRITEoption.ALLdelays key writes for allMyISAMtables. See Section 7.5.3, “Tuning Server Parameters”, and Section 13.5.1, “MyISAMStartup Options”.Note
If you set this variable to
ALL, you should not useMyISAMtables from within another program (such as another MySQL server or myisamchk) when the tables are in use. Doing so leads to index corruption.Command-Line Format --des-key-file=nameConfig-File Format des-key-fileRead the default DES keys from this file. These keys are used by the
DES_ENCRYPT()andDES_DECRYPT()functions.Command-Line Format --named_pipeConfig-File Format enable-named-pipePlatform Specific windows Enable support for named pipes. This option applies only on Windows NT, 2000, XP, and 2003 systems.
Command-Line Format --enable-pstackConfig-File Format enable-pstackPermitted Values Type booleanDefault FALSEPrint a symbolic stack trace on failure. This capability is available only on Intel Linux systems, and only if MySQL was configured with the
--with-pstackoption.--engine-condition-pushdown={ON|OFF}Command-Line Format --engine-condition-pushdownConfig-File Format engine-condition-pushdownOption Sets Variable Yes, engine_condition_pushdownVariable Name engine_condition_pushdownVariable Scope Both Dynamic Variable Yes Permitted Values Type booleanDefault ONSets the
engine_condition_pushdownsystem variable. For more information, see Section 7.2.7, “Condition Pushdown Optimization”.Command-Line Format --event-scheduler[=value]Config-File Format event-schedulerOption Sets Variable Yes, event_schedulerVariable Name event_schedulerVariable Scope Global Dynamic Variable Yes Permitted Values Type enumerationDefault OFFValid Values ON,OFF,DISABLEDEnable or disable, and start or stop, the event scheduler.
For detailed information, see The
--event-schedulerOption.--exit-info[=,flags]-T [flags]Command-Line Format --exit-info[=flags]Config-File Format exit-infoPermitted Values Type numericThis is a bit mask of different flags that you can use for debugging the mysqld server. Do not use this option unless you know exactly what it does!
Command-Line Format --external-lockingConfig-File Format external-lockingOption Sets Variable Yes, skip_external_lockingDisabled by skip-external-lockingPermitted Values Type booleanDefault FALSEEnable external locking (system locking), which is disabled by default as of MySQL 4.0. Note that if you use this option on a system on which
lockddoes not fully work (such as Linux), it is easy for mysqld to deadlock.For more information about external locking, including conditions under which it can and cannot be used, see Section 7.3.5, “External Locking”.
Command-Line Format --flushConfig-File Format flushVariable Name flushVariable Scope Global Dynamic Variable Yes Permitted Values Type booleanDefault OFFFlush (synchronize) all changes to disk after each SQL statement. Normally, MySQL does a write of all changes to disk only after each SQL statement and lets the operating system handle the synchronizing to disk. See Section B.5.4.2, “What to Do If MySQL Keeps Crashing”.
Command-Line Format --gdbConfig-File Format gdbPermitted Values Type booleanDefault FALSEInstall an interrupt handler for
SIGINT(needed to stop mysqld with^Cto set breakpoints) and disable stack tracing and core file handling. See MySQL Internals: Porting.Command-Line Format --general-logConfig-File Format general-logOption Sets Variable Yes, general_logVariable Name general_logVariable Scope Global Dynamic Variable Yes Permitted Values Type booleanDefault OFFSpecify the initial general query log state. With no argument or an argument of 1, the
--general-logoption enables the log. If omitted or given with an argument of 0, the option disables the log.Command-Line Format --init-file=nameConfig-File Format init-fileOption Sets Variable Yes, init_fileVariable Name init_fileVariable Scope Global Dynamic Variable No Permitted Values Type filenameRead SQL statements from this file at startup. Each statement must be on a single line and should not include comments.
This option is unavailable if MySQL was configured with the
--disable-grant-optionsoption. See Section 2.10.2, “Typical configure Options”.--innodb-xxxThe
InnoDBoptions are listed in Section 13.6.3, “InnoDBStartup Options and System Variables”.--language=lang_name, -Llang_nameVersion Deprecated 5.5.0 Command-Line Format --language=nameConfig-File Format languageOption Sets Variable Yes, languageVariable Name languageVariable Scope Global Dynamic Variable No Deprecated 5.5.0, by lc-messages-dirPermitted Values Type filenameDefault /usr/local/mysql/share/mysql/english/The language to use for error messages.
lang_namecan be given as the language name or as the full path name to the directory where the language files are installed. See Section 9.2, “Setting the Error Message Language”.As of MySQL 5.5,
--lc-messages-dirand--lc-messagesshould be used rather than--language, which is deprecated and handled as an alias for--lc-messages-dir.Command-Line Format --large-pagesConfig-File Format large-pagesOption Sets Variable Yes, large_pagesVariable Name large_pagesVariable Scope Global Dynamic Variable No Platform Specific linux Permitted Values Type (linux) booleanDefault FALSESome hardware/operating system architectures support memory pages greater than the default (usually 4KB). The actual implementation of this support depends on the underlying hardware and operating system. Applications that perform a lot of memory accesses may obtain performance improvements by using large pages due to reduced Translation Lookaside Buffer (TLB) misses.
MySQL 5.5 supports the Linux implementation of large page support (which is called HugeTLB in Linux). See Section 7.5.9, “Enabling Large Page Support”. For Solaris support of large pages, see the description of the
--super-large-pagesoption.--large-pagesis disabled by default.Command-Line Format --lc-messages=nameConfig-File Format lc-messagesOption Sets Variable Yes, lc_messagesVariable Name lc-messagesVariable Scope Both Dynamic Variable Yes Permitted Values Type stringThe locale to use for error messages. The server converts the argument to a language name and combines it with the value of the
--lc-messages-dirto produce the location for the error message file. See Section 9.2, “Setting the Error Message Language”.Command-Line Format --lc-messages-dir=pathConfig-File Format lc-messages-dirOption Sets Variable Yes, lc_messages_dirVariable Name lc-messages-dirVariable Scope Global Dynamic Variable No Permitted Values Type stringThe directory where error messages are located. The value is used together with the value of
--lc-messages-dirto produce the location for the error message file. See Section 9.2, “Setting the Error Message Language”.--log[=,file_name]-l [file_name]Command-Line Format --log[=name]Config-File Format logOption Sets Variable Yes, logVariable Name logVariable Scope Global Dynamic Variable Yes Deprecated 5.1.29, by general-logPermitted Values Type stringDefault OFFThis option enables logging to the general query log, which contains entries that record client connections and SQL statements received from clients. The log output destination can be selected with the
--log-outputoption. If you omit the file name, MySQL useshost_name.logThe
--logoption is deprecated and will be removed (along with thelogsystem variable) in MySQL 7.0. Instead, use the--general_logoption to enable the general query log and the--general_log_file=option to set the general query log file name.file_nameCommand-Line Format --log-error[=name]Config-File Format log-errorOption Sets Variable Yes, log_errorVariable Name log_errorVariable Scope Global Dynamic Variable No Permitted Values Type filenameLog errors and startup messages to this file. See Section 5.2.2, “The Error Log”. If you omit the file name, MySQL uses
host_name.err.err.Command-Line Format --log-isam[=name]Config-File Format log-isamPermitted Values Type filenameLog all
MyISAMchanges to this file (used only when debuggingMyISAM).--log-long-format(DEPRECATED)Command-Line Format --log-long-formatConfig-File Format log-long-formatDeprecated 4.1 Log extra information to the binary log and slow query log, if they have been activated. For example, the user name and timestamp are logged for all queries. This option is deprecated, as it now represents the default logging behavior. (See the description for
--log-short-format.) The--log-queries-not-using-indexesoption is available for the purpose of logging queries that do not use indexes to the slow query log.--log-long-formatwas removed in MySQL 5.5.3.Command-Line Format --log-output[=name]Config-File Format log-outputOption Sets Variable Yes, log_outputVariable Name log_outputVariable Scope Global Dynamic Variable Yes Permitted Values Type enumerationDefault FILEValid Values TABLE,FILE,NONEThis option determines the destination for general query log and slow query log output. The option value can be given as one or more of the words
TABLE,FILE, orNONE. If the option is given without a value, the default isFILE.TABLEselect logging to thegeneral_logandslow_logtables in themysqldatabase as a destination.FILEselects logging to log files as a destination.NONEdisables logging. IfNONEis present in the option value, it takes precedence over any other words that are present.TABLEandFILEcan both be given to select to both log output destinations.This option selects log output destinations, but does not enable log output. To do that, use the
--general_logand--slow_query_logoptions. ForFILElogging, the--general_log_fileand-slow_query_log_fileoptions determine the log file location. For more information, see Section 5.2.1, “Selecting General Query and Slow Query Log Output Destinations”.--log-queries-not-using-indexesCommand-Line Format --log-queries-not-using-indexesConfig-File Format log-queries-not-using-indexesOption Sets Variable Yes, log_queries_not_using_indexesVariable Name log_queries_not_using_indexesVariable Scope Global Dynamic Variable Yes Permitted Values Type booleanIf you are using this option with the slow query log enabled, queries that are expected to retrieve all rows are logged. See Section 5.2.5, “The Slow Query Log”. This option does not necessarily mean that no index is used. For example, a query that uses a full index scan uses an index but would be logged because the index would not limit the number of rows.
Command-Line Format --log-short-formatConfig-File Format log-short-formatPermitted Values Type booleanDefault FALSEOriginally intended to log less information to the binary log and slow query log, if they have been activated. However, this option is not operational.
Command-Line Format --log-slow-admin-statementsConfig-File Format log-slow-admin-statementsPermitted Values Type booleanDefault FALSELog slow administrative statements such as
OPTIMIZE TABLE,ANALYZE TABLE, andALTER TABLEto the slow query log.--log-slow-queries[=file_name]Command-Line Format --log-slow-queries[=name]Config-File Format log-slow-queriesOption Sets Variable Yes, log_slow_queriesVariable Name log_slow_queriesVariable Scope Global Dynamic Variable Yes Deprecated 5.1.29, by slow-query-logPermitted Values Type booleanThis option enables logging to the slow query log, which contains entries for all queries that have taken more than
long_query_timeseconds to execute. See the descriptions of the--log-long-formatand--log-short-formatoptions for details. The log output destination can be selected with the--log-outputoption. If you omit the file name, MySQL useshost_name-slow.logThe
--log-slow-queriesoption is deprecated and will be removed (along with thelog_slow_queriessystem variable) in MySQL 7.0. Instead, use the--slow_query_logoption to enable the slow query log and the--slow_query_log_file=option to set the slow query log file name.file_nameCommand-Line Format --log-tc=nameConfig-File Format log-tcPermitted Values Type filenameDefault tc.logThe name of the memory-mapped transaction coordinator log file (for XA transactions that affect multiple storage engines when the binary log is disabled). The default name is
tc.log. The file is created under the data directory if not given as a full path name. Currently, this option is unused.Command-Line Format --log-tc-size=#Config-File Format log-tc-sizePermitted Values Platform Bit Size 32Type numericDefault 24576Max Value 4294967295Permitted Values Platform Bit Size 64Type numericDefault 24576Max Value 18446744073709547520The size in bytes of the memory-mapped transaction coordinator log. The default size is 24KB.
--log-warnings[=,level]-W [level]Command-Line Format --log-warnings[=#]Config-File Format log-warningsOption Sets Variable Yes, log_warningsVariable Name log_warningsVariable Scope Both Dynamic Variable Yes Disabled by skip-log-warningsPermitted Values Platform Bit Size 64Type numericDefault 1Range 0-18446744073709547520Print out warnings such as
Aborted connection...to the error log. Enabling this option is recommended, for example, if you use replication (you get more information about what is happening, such as messages about network failures and reconnections). This option is enabled (1) by default, and the defaultlevelvalue if omitted is 1. To disable this option, use--log-warnings=0. If the value is greater than 1, aborted connections are written to the error log, and access-denied errors for new connection attempts are written. See Section B.5.2.11, “Communication Errors and Aborted Connections”.If a slave server was started with
--log-warningsenabled, the slave prints messages to the error log to provide information about its status, such as the binary log and relay log coordinates where it starts its job, when it is switching to another relay log, when it reconnects after a disconnect, and so forth. The server logs messages about statements that are unsafe for statement-based logging only if--log-warningsis enabled.Command-Line Format --low-priority-updatesConfig-File Format low-priority-updatesOption Sets Variable Yes, low_priority_updatesVariable Name low_priority_updatesVariable Scope Both Dynamic Variable Yes Permitted Values Type booleanDefault FALSEGive table-modifying operations (
INSERT,REPLACE,DELETE,UPDATE) lower priority than selects. This can also be done via{INSERT | REPLACE | DELETE | UPDATE} LOW_PRIORITY ...to lower the priority of only one query, or bySET LOW_PRIORITY_UPDATES=1to change the priority in one thread. This affects only storage engines that use only table-level locking (MyISAM,MEMORY,MERGE). See Section 7.3.2, “Table Locking Issues”.--min-examined-row-limit=numberCommand-Line Format --min-examined-row-limit=#Config-File Format min-examined-row-limitVariable Name min_examined_row_limitVariable Scope Both Dynamic Variable Yes Permitted Values Platform Bit Size 32Type numericDefault 0Range 0-4294967295Permitted Values Platform Bit Size 64Type numericDefault 0Range 0-18446744073709547520When this option is set, queries which examine fewer than
numberrows are not written to the slow query log. The default is 0.Command-Line Format --memlockConfig-File Format memlockVariable Name locked_in_memoryVariable Scope Global Dynamic Variable No Permitted Values Type booleanDefault FALSELock the mysqld process in memory. This option might help if you have a problem where the operating system is causing mysqld to swap to disk.
--memlockworks on systems that support themlockall()system call; this includes Solaris as well as most Linux distributions that use a 2.4 or newer kernel. On Linux systems, you can tell whether or notmlockall()(and thus this option) is supported by checking to see whether or not it is defined in the systemmman.hfile, like this:shell>
grep mlockall /usr/include/sys/mman.hIf
mlockall()is supported, you should see in the output of the previous command something like the following:extern int mlockall (int __flags) __THROW;
Important
Using this option requires that you run the server as
root, which, for reasons of security, is normally not a good idea. See Section 5.3.6, “How to Run MySQL as a Normal User”.You must not try to use this option on a system that does not support the
mlockall()system call; if you do so, mysqld will very likely crash as soon as you try to start it.Command-Line Format --myisam-block-size=#Config-File Format myisam-block-sizePermitted Values Type numericDefault 1024Range 1024-16384The block size to be used for
MyISAMindex pages.--myisam-recover[=option[,option]...]]Command-Line Format --myisam-recover[=name]Config-File Format myisam-recoverPermitted Values Type enumerationDefault OFFValid Values DEFAULT,BACKUP,FORCE,QUICKSet the
MyISAMstorage engine recovery mode. The option value is any combination of the values ofDEFAULT,BACKUP,FORCE, orQUICK. If you specify multiple values, separate them by commas. Specifying the option with no argument is the same as specifyingDEFAULT, and specifying with an explicit value of""disables recovery (same as not giving the option). If recovery is enabled, each time mysqld opens aMyISAMtable, it checks whether the table is marked as crashed or wasn't closed properly. (The last option works only if you are running with external locking disabled.) If this is the case, mysqld runs a check on the table. If the table was corrupted, mysqld attempts to repair it.The following options affect how the repair works.
Option Description DEFAULTRecovery without backup, forcing, or quick checking. BACKUPIf the data file was changed during recovery, save a backup of the tbl_name.MYDtbl_name-datetime.BAKFORCERun recovery even if we would lose more than one row from the .MYDfile.QUICKDon't check the rows in the table if there aren't any delete blocks. Before the server automatically repairs a table, it writes a note about the repair to the error log. If you want to be able to recover from most problems without user intervention, you should use the options
BACKUP,FORCE. This forces a repair of a table even if some rows would be deleted, but it keeps the old data file as a backup so that you can later examine what happened.Command-Line Format --old-alter-tableConfig-File Format old-alter-tableOption Sets Variable Yes, old_alter_tableVariable Name old-alter-tableVariable Scope Both Dynamic Variable Yes Permitted Values Type booleanDefault OFFWhen this option is given, the server does not use the optimized method of processing an
ALTER TABLEoperation. It reverts to using a temporary table, copying over the data, and then renaming the temporary table to the original, as used by MySQL 5.0 and earlier. For more information on the operation ofALTER TABLE, see Section 12.1.6, “ALTER TABLESyntax”.Command-Line Format --old_passwordsConfig-File Format old-passwordsOption Sets Variable Yes, old_passwordsVariable Name old_passwordsVariable Scope Both Dynamic Variable Yes Permitted Values Type booleanDefault FALSEForce the server to generate short (pre-4.1) password hashes for new passwords. This is useful for compatibility when the server must support older client programs. See Section 5.3.2.3, “Password Hashing in MySQL”.
Command-Line Format --old-style-user-limitsConfig-File Format old-style-user-limitsPermitted Values Type booleanDefault FALSEEnable old-style user limits. (Before MySQL 5.0.3, account resource limits were counted separately for each host from which a user connected rather than per account row in the
usertable.) See Section 5.5.4, “Setting Account Resource Limits”.Command-Line Format --one-threadConfig-File Format one-threadOnly use one thread (for debugging under Linux). This option is available only if the server is built with debugging enabled. See MySQL Internals: Porting.
This option is deprecated; use
--thread_handling=no-threadsinstead.Command-Line Format --open-files-limit=#Config-File Format open-files-limitOption Sets Variable Yes, open_files_limitVariable Name open_files_limitVariable Scope Global Dynamic Variable No Permitted Values Type numericDefault 0Range 0-65535Changes the number of file descriptors available to mysqld. You should try increasing the value of this option if mysqld gives you the error
Too many open files. mysqld uses the option value to reserve descriptors withsetrlimit(). If the requested number of file descriptors cannot be allocated, mysqld writes a warning to the error log.mysqld may attempt to allocate more than the requested number of descriptors (if they are available), using the values of
max_connectionsandtable_open_cacheto estimate whether more descriptors will be needed.Command-Line Format --partitionConfig-File Format partitionOption Sets Variable Yes, have_partitioningVariable Name partitionVariable Scope Global Dynamic Variable No Disabled by skip-partitionPermitted Values Type booleanDefault ONEnables or disables user-defined partitioning support in the MySQL Server.
Command-Line Format --pid-file=nameConfig-File Format pid-fileOption Sets Variable Yes, pid_fileVariable Name pid_fileVariable Scope Global Dynamic Variable No Permitted Values Type filenameThe path name of the process ID file. The server creates the file in the data directory unless an absolute path name is given to specify a different directory. This file is used by other programs such as mysqld_safe to determine the server's process ID.
Specifies an option that pertains to a server plugin. For example, many storage engines can be built as plugins, and for such engines, options for them can be specified with a
--pluginprefix. Thus, the--innodb_file_per_tableoption forInnoDBcan be specified as--plugin-innodb_file_per_table.For boolean options that can be enabled or disabled, the
--skipprefix and other alternative formats are supported as well (see Section 4.2.3.2, “Program Option Modifiers”). For example,--skip-plugin-innodb_file_per_tabledisablesinnodb_file_per_table.The rationale for the
--pluginprefix is that it enables plugin options to be specified unambigously if there is a name conflict with a built-in server option. For example, were a plugin writer to name a plugin “sql” and implement a “mode” option, the option name might be--sql-mode, which would conflict with the built-in option of the same name. In such cases, references to the conflicting name are resolved in favor of the built-in option. To avoid the ambiguity, users can specify the plugin option as--plugin-sql-mode. Use of the--pluginprefix for plugin options is recommended to avoid any question of ambiguity.Command-Line Format --plugin-load=plugin_listConfig-File Format plugin-loadPermitted Values Type stringUnder normal startup, the server determines which plugins to load by reading the
mysql.pluginssystem table. This option enables plugins to be loaded even when--skip-grant-tablesis given (which tells the server not to read system tables). This option also enables plugins to be loaded at startup under configurations when plugins cannot be loaded at runtime.The option value is a semicolon-separated list of
name=plugin_librarynameis the name of the plugin, andplugin_libraryis the name of the shared library that contains the plugin code. Each library file must be located in the directory named by theplugin_dirsystem variable. For example, if plugins namedmyplug1andmyplug2have library filesmyplug1.soandmyplug2.so, use this option to load them at startup:shell>
mysqld --plugin-load=myplug1=myplug1.so;myplug2=myplug2.soAll plugins to load must be named in the same
--plugin-loadoption. If multiple--plugin-loadoptions are given, only the last one is used.The plugins are loaded for a single invocation of mysqld only. After a restart, the plugins are not loaded unless
--plugin-loadis used again. This is in contrast toINSTALL PLUGIN, which adds an entry to themysql.pluginstable to cause the plugin to be loaded for every normal server startup.--port=,port_num-Pport_numCommand-Line Format --port=#Config-File Format portOption Sets Variable Yes, portVariable Name portVariable Scope Global Dynamic Variable No Permitted Values Type numericDefault 3306The port number to use when listening for TCP/IP connections. The port number must be 1024 or higher unless the server is started by the
rootsystem user.Command-Line Format --port-open-timeout=#Config-File Format port-open-timeoutPermitted Values Type numericDefault 0On some systems, when the server is stopped, the TCP/IP port might not become available immediately. If the server is restarted quickly afterward, its attempt to reopen the port can fail. This option indicates how many seconds the server should wait for the TCP/IP port to become free if it cannot be opened. The default is not to wait.
Command-Line Format --safe-modeConfig-File Format safe-modeDeprecated 5.0 Skip some optimization stages.
--safe-show-database(DEPRECATED)Command-Line Format --safe-show-databaseConfig-File Format safe-show-databaseVariable Name safe_show_databaseVariable Scope Global Dynamic Variable Yes Deprecated 4.0.2 Permitted Values Type booleanThis option is deprecated and does not do anything because there is a
SHOW DATABASESprivilege that can be used to control access to database names on a per-account basis. See Section 5.4.1, “Privileges Provided by MySQL”.--safe-show-databasewas removed in MySQL 5.5.3.Command-Line Format --safe-user-createConfig-File Format safe-user-createPermitted Values Type booleanDefault FALSEIf this option is enabled, a user cannot create new MySQL users by using the
GRANTstatement unless the user has theINSERTprivilege for themysql.usertable or any column in the table. If you want a user to have the ability to create new users that have those privileges that the user has the right to grant, you should grant the user the following privilege:GRANT INSERT(user) ON mysql.user TO '
user_name'@'host_name';This ensures that the user cannot change any privilege columns directly, but has to use the
GRANTstatement to give privileges to other users.Command-Line Format --secure-authConfig-File Format secure-authOption Sets Variable Yes, secure_authVariable Name secure_authVariable Scope Global Dynamic Variable Yes Permitted Values Type booleanDefault FALSEDisallow authentication by clients that attempt to use accounts that have old (pre-4.1) passwords.
Command-Line Format --secure-file-privConfig-File Format secure-file-privOption Sets Variable Yes, secure_file_privVariable Name secure_file_privVariable Scope Global Dynamic Variable No Permitted Values Type stringThis option limits the effect of the
LOAD_FILE()function and theLOAD DATAandSELECT ... INTO OUTFILEstatements to work only with files in the specified directory.Enable shared-memory connections by local clients. This option is available only on Windows.
--shared-memory-base-name=nameThe name of shared memory to use for shared-memory connections. This option is available only on Windows. The default name is
MYSQL. The name is case sensitive.Turn off the ability to select and insert at the same time on
MyISAMtables. (This is to be used only if you think you have found a bug in this feature.) See Section 7.3.3, “Concurrent Inserts”.Do not use external locking (system locking). For more information about external locking, including conditions under which it can and cannot be used, see Section 7.3.5, “External Locking”.
External locking has been disabled by default since MySQL 4.0.
Command-Line Format --skip-event-schedulerConfig-File Format skip-event-schedulerTurns the Event Scheduler
OFF. This is not the same as disabling the Event Scheduler, which requires setting--event-scheduler=DISABLED; see The--event-schedulerOption, for more information.This option causes the server to start without using the privilege system at all, which gives anyone with access to the server unrestricted access to all databases. You can cause a running server to start using the grant tables again by executing mysqladmin flush-privileges or mysqladmin reload command from a system shell, or by issuing a MySQL
FLUSH PRIVILEGESstatement after connecting to the server. This option also suppresses loading of plugins, user-defined functions (UDFs), and scheduled events. To cause plugins to be loaded anyway, use the--plugin-loadoption.--skip-grant-tablesis unavailable if MySQL was configured with the--disable-grant-optionsoption. See Section 2.10.2, “Typical configure Options”.Do not use the internal host name cache for faster name-to-IP resolution. Instead, query the DNS server every time a client connects. See Section 7.5.11, “How MySQL Uses DNS”.
Disable the
InnoDBstorage engine. This saves memory and disk space and might speed up some operations. Do not use this option if you requireInnoDBtables.Do not resolve host names when checking client connections. Use only IP numbers. If you use this option, all
Hostcolumn values in the grant tables must be IP numbers orlocalhost. See Section 7.5.11, “How MySQL Uses DNS”.Don't listen for TCP/IP connections at all. All interaction with mysqld must be made via named pipes or shared memory (on Windows) or Unix socket files (on Unix). This option is highly recommended for systems where only local clients are allowed. See Section 7.5.11, “How MySQL Uses DNS”.
Command-Line Format --skip-partitionConfig-File Format skip-partitionDisables user-defined partitioning. Existing partitioned tables cannot be accessed when the server has been started with this option.
Options that begin with
--sslspecify whether to allow clients to connect via SSL and indicate where to find SSL keys and certificates. See Section 5.5.6.3, “SSL Command Options”.Command-Line Format --standaloneConfig-File Format standalonePlatform Specific windows Available on Windows NT-based systems only; instructs the MySQL server not to run as a service.
Standard use of large pages in MySQL attempts to use the largest size supported, up to 4MB. Under Solaris, a “super large pages” feature enables uses of pages up to 256MB. This feature is available for recent SPARC platforms. It can be enabled or disabled by using the
--super-large-pagesor--skip-super-large-pagesoption.--symbolic-links,--skip-symbolic-linksCommand-Line Format --symbolic-linksConfig-File Format symbolic-linksEnable or disable symbolic link support. This option has different effects on Windows and Unix:
On Windows, enabling symbolic links allows you to establish a symbolic link to a database directory by creating a
db_name.symOn Unix, enabling symbolic links means that you can link a
MyISAMindex file or data file to another directory with theINDEX DIRECTORYorDATA DIRECTORYoptions of theCREATE TABLEstatement. If you delete or rename the table, the files that its symbolic links point to also are deleted or renamed. See Section 7.6.1.2, “Using Symbolic Links for Tables on Unix”.
Command-Line Format --skip-safe-mallocConfig-File Format skip-safemallocIf MySQL is configured with
--with-debug=full, all MySQL programs check for memory overruns during each memory allocation and memory freeing operation. This checking is very slow, so for the server you can avoid it when you don't need it by using the--skip-safemallocoption.Command-Line Format --skip-show-databaseConfig-File Format skip-show-databaseOption Sets Variable Yes, skip_show_databaseVariable Name skip_show_databaseVariable Scope Global Dynamic Variable No With this option, the
SHOW DATABASESstatement is allowed only to users who have theSHOW DATABASESprivilege, and the statement displays all database names. Without this option,SHOW DATABASESis allowed to all users, but displays each database name only if the user has theSHOW DATABASESprivilege or some privilege for the database. Note that any global privilege is considered a privilege for the database.Command-Line Format --skip-stack-traceConfig-File Format skip-stack-traceDon't write stack traces. This option is useful when you are running mysqld under a debugger. On some systems, you also must use this option to get a core file. See MySQL Internals: Porting.
Command-Line Format --skip-thread-priorityConfig-File Format skip-thread-priorityDeprecated 5.1.29 Disable using thread priorities for faster response time. This option is deprecated.
Command-Line Format --slow-query-logConfig-File Format slow-query-logOption Sets Variable Yes, slow_query_logVariable Name slow_query_logVariable Scope Global Dynamic Variable Yes Permitted Values Type booleanDefault OFFSpecify the initial slow query log state. With no argument or an argument of 1, the
--slow-query-logoption enables the log. If omitted or given with an argument of 0, the option disables the log.Command-Line Format --socket=nameConfig-File Format socketOption Sets Variable Yes, socketVariable Name socketVariable Scope Global Dynamic Variable No Permitted Values Type filenameDefault /tmp/mysql.sockOn Unix, this option specifies the Unix socket file to use when listening for local connections. The default value is
/tmp/mysql.sock. If this option is given, the server creates the file in the data directory unless an absolute path name is given to specify a different directory. On Windows, the option specifies the pipe name to use when listening for local connections that use a named pipe. The default value isMySQL(not case sensitive).--sql-mode=value[,value[,value...]]Command-Line Format --sql-mode=nameConfig-File Format sql-modeOption Sets Variable Yes, sql_modeVariable Name sql_modeVariable Scope Both Dynamic Variable Yes Permitted Values Type setDefault ''Valid Values ALLOW_INVALID_DATES,ANSI_QUOTES,ERROR_FOR_DIVISION_BY_ZERO,HIGH_NOT_PRECEDENCE,IGNORE_SPACE,NO_AUTO_CREATE_USER,NO_AUTO_VALUE_ON_ZERO,NO_BACKSLASH_ESCAPES,NO_DIR_IN_CREATE,NO_ENGINE_SUBSTITUTION,NO_FIELD_OPTIONS,NO_KEY_OPTIONS,NO_TABLE_OPTIONS,NO_UNSIGNED_SUBTRACTION,NO_ZERO_DATE,NO_ZERO_IN_DATE,ONLY_FULL_GROUP_BY,PAD_CHAR_TO_FULL_LENGTH,PIPES_AS_CONCAT,REAL_AS_FLOAT,STRICT_ALL_TABLES,STRICT_TRANS_TABLESSet the SQL mode. See Section 5.1.8, “Server SQL Modes”.
Command-Line Format --sysdate-is-nowConfig-File Format sysdate-is-nowPermitted Values Type booleanDefault FALSESYSDATE()by default returns the time at which it executes, not the time at which the statement in which it occurs begins executing. This differs from the behavior ofNOW(). This option causesSYSDATE()to be an alias forNOW(). For information about the implications for binary logging and replication, see the description forSYSDATE()in Section 11.6, “Date and Time Functions” and forSET TIMESTAMPin Section 5.1.5, “Session System Variables”.--tc-heuristic-recover={COMMIT|ROLLBACK}Command-Line Format --tc-heuristic-recover=nameConfig-File Format tc-heuristic-recoverPermitted Values Type enumerationValid Values COMMIT,RECOVERThe type of decision to use in the heuristic recovery process. Currently, this option is unused.
Command-Line Format --temp-poolConfig-File Format temp-poolPermitted Values Type booleanDefault TRUEThis option causes most temporary files created by the server to use a small set of names, rather than a unique name for each new file. This works around a problem in the Linux kernel dealing with creating many new files with different names. With the old behavior, Linux seems to “leak” memory, because it is being allocated to the directory entry cache rather than to the disk cache. This option is ignored except on Linux.
Command-Line Format --transaction-isolation=nameConfig-File Format transaction-isolationPermitted Values Type enumerationValid Values READ-UNCOMMITTED,READ-COMMITTED,REPEATABLE-READ,SERIALIZABLESets the default transaction isolation level. The
levelvalue can beREAD-UNCOMMITTED,READ-COMMITTED,REPEATABLE-READ, orSERIALIZABLE. See Section 12.4.6, “SET TRANSACTIONSyntax”.--tmpdir=,path-tpathCommand-Line Format --tmpdir=nameConfig-File Format tmpdirOption Sets Variable Yes, tmpdirVariable Name tmpdirVariable Scope Global Dynamic Variable No Permitted Values Type filenameThe path of the directory to use for creating temporary files. It might be useful if your default
/tmpdirectory resides on a partition that is too small to hold temporary tables. This option accepts several paths that are used in round-robin fashion. Paths should be separated by colon characters (“:”) on Unix and semicolon characters (“;”) on Windows, NetWare, and OS/2. If the MySQL server is acting as a replication slave, you should not set--tmpdirto point to a directory on a memory-based file system or to a directory that is cleared when the server host restarts. For more information about the storage location of temporary files, see Section B.5.4.4, “Where MySQL Stores Temporary Files”. A replication slave needs some of its temporary files to survive a machine restart so that it can replicate temporary tables orLOAD DATA INFILEoperations. If files in the temporary file directory are lost when the server restarts, replication fails.--user={,user_name|user_id}-u {user_name|user_id}Command-Line Format --user=nameConfig-File Format userPermitted Values Type stringRun the mysqld server as the user having the name
user_nameor the numeric user IDuser_id. (“User” in this context refers to a system login account, not a MySQL user listed in the grant tables.)This option is mandatory when starting mysqld as
root. The server changes its user ID during its startup sequence, causing it to run as that particular user rather than asroot. See Section 5.3.1, “General Security Guidelines”.To avoid a possible security hole where a user adds a
--user=rootoption to amy.cnffile (thus causing the server to run asroot), mysqld uses only the first--useroption specified and produces a warning if there are multiple--useroptions. Options in/etc/my.cnfand$MYSQL_HOME/my.cnfare processed before command-line options, so it is recommended that you put a--useroption in/etc/my.cnfand specify a value other thanroot. The option in/etc/my.cnfis found before any other--useroptions, which ensures that the server runs as a user other thanroot, and that a warning results if any other--useroption is found.Use this option with the
--helpoption for detailed help.--version,-VDisplay version information and exit.
You can assign a value to a server system variable by using an
option of the form
--.
For example, var_name=value--key_buffer_size=32M
sets the key_buffer_size variable
to a value of 32MB.
Note that when you assign a value to a variable, MySQL might automatically correct the value to stay within a given range, or adjust the value to the closest allowable value if only certain values are allowed.
If you want to restrict the maximum value to which a variable can
be set at runtime with
SET, you can
define this by using the
--maximum-
command-line option.
var_name=value
You can change the values of most system variables for a running
server with the
SET
statement. See Section 12.5.4, “SET Syntax”.
Section 5.1.4, “Server System Variables”, provides a full description for all variables, and additional information for setting them at server startup and runtime. Section 7.5.3, “Tuning Server Parameters”, includes information on optimizing the server by tuning system variables.
The server can load plugins under the control of startup options.
For example, many storage engines can be built in pluggable form
and loaded when the server starts. In the following descriptions,
plugin_name stands for a plugin name
such as innodb.
As of MySQL 5.4.2, options used to control plugin loading have a tristate format:
--plugin_name=OFFDo not enable the plugin.
--plugin_name[=ON]Enable the plugin. If plugin initialization fails, start the server anyway, but with the plugin disabled. Specifying the option as
--without a value also enables the plugin.plugin_name--plugin_name=FORCEEnable the plugin. If plugin initialization fails, do not start the server. In other words, force the server to run with the plugin or not at all.
The values OFF, ON, and
FORCE are not case sensitive.
If a plugin is disabled, either explicitly with
OFF or implicitly because it was enabled with
ON but failed to initialize, aspects of server
operation that require the plugin will change. For example, if the
plugin implements a storage engine, existing tables for the
storage engine become inaccessible, and attempts to create new
tables for the storage engine result in tables that use the
default storage engine unless the
NO_ENGINE_SUBSTITUTION SQL mode
has been enabled to cause an error to occur instead.
Suppose that CSV, InnoDB,
and ARCHIVE are built as pluggable storage
engines and that you want the server to load them at startup,
subject to these conditions: The server is allowed to run if
CSV initialization fails, but must require that
InnoDB initialization succeed.
ARCHIVE should be disabled. To accomplish that,
use these lines in an option file:
[mysqld] csv=ON innodb=FORCE archive=OFF
--enable-
is also supported and is the same as
plugin_name--.
plugin_name=ON--disable-
and plugin_name--skip-
are also supported and are the same as
plugin_name--.
plugin_name=OFF
Before MySQL 5.4.2, plugin options are boolean options (see Section 4.2.3.2, “Program Option Modifiers”). That is, any of these options enable the plugin:
--plugin_name--plugin_name=1 --enable-plugin_name
And these options disable the plugin:
--plugin_name=0 --disable-plugin_name--skip-plugin_name
If the plugin fails to initialize, the server runs with the plugin disabled.
If you upgrade to MySQL 5.4.2 or later from an older version and
previously used options of the form
-- or
plugin_name=0--, the
equivalent options are now
plugin_name=1-- and
plugin_name=OFF--,
respectively. You also have the choice of requiring plugins to
start successfully by using
plugin_name=ON--.
plugin_name=FORCE
Plugins can also be loaded at runtime, via the
INSTALL PLUGIN statement (see
Section 12.5.3.3, “INSTALL PLUGIN Syntax”).
The MySQL server maintains many system variables that indicate how
it is configured. Each system variable has a default value. System
variables can be set at server startup using options on the
command line or in an option file. Most of them can be changed
dynamically while the server is running by means of the
SET
statement, which enables you to modify operation of the server
without having to stop and restart it. You can refer to system
variable values in expressions.
There are several ways to see the names and values of system variables:
To see the values that a server will use based on its compiled-in defaults and any option files that it reads, use this command:
mysqld --verbose --help
To see the values that a server will use based on its compiled-in defaults, ignoring the settings in any option files, use this command:
mysqld --no-defaults --verbose --help
To see the current values used by a running server, use the
SHOW VARIABLESstatement.
This section provides a description of each system variable. Variables with no version indicated are present in all MySQL 5.5 releases. For historical information concerning their implementation, please see http://dev.mysql.com/doc/refman/5.0/en/, and http://dev.mysql.com/doc/refman/4.1/en/.
The following table lists all available system variables:
Table 5.2. System Variable Summary
| Name | Cmd-Line | Option file | System Var | Var Scope | Dynamic |
|---|---|---|---|---|---|
| auto_increment_increment | Yes | Yes | Yes | Both | Yes |
| auto_increment_offset | Yes | Yes | Yes | Both | Yes |
| autocommit | Yes | Session | Yes | ||
| automatic_sp_privileges | Yes | Global | Yes | ||
| back_log | Yes | Yes | Yes | Global | No |
| basedir | Yes | Yes | Yes | Global | No |
| big-tables | Yes | Yes | Yes | ||
| - Variable: big_tables | Yes | Session | Yes | ||
| binlog_cache_size | Yes | Yes | Yes | Global | Yes |
| binlog-format | Yes | Yes | Yes | ||
| - Variable: binlog_format | Yes | Both | Yes | ||
| bulk_insert_buffer_size | Yes | Yes | Yes | Both | Yes |
| character_set_client | Yes | Both | Yes | ||
| character_set_connection | Yes | Both | Yes | ||
| character_set_database[a] | Yes | Both | Yes | ||
| character-set-filesystem | Yes | Yes | Yes | ||
| - Variable: character_set_filesystem | Yes | Both | Yes | ||
| character_set_results | Yes | Both | Yes | ||
| character-set-server | Yes | Yes | Yes | ||
| - Variable: character_set_server | Yes | Both | Yes | ||
| character_set_system | Yes | Global | No | ||
| character-sets-dir | Yes | Yes | No | ||
| - Variable: character_sets_dir | Yes | Global | No | ||
| collation_connection | Yes | Both | Yes | ||
| collation_database[b] | Yes | Both | Yes | ||
| collation-server | Yes | Yes | Yes | ||
| - Variable: collation_server | Yes | Both | Yes | ||
| completion_type | Yes | Yes | Yes | Both | Yes |
| concurrent_insert | Yes | Yes | Yes | Global | Yes |
| connect_timeout | Yes | Yes | Yes | Global | Yes |
| datadir | Yes | Yes | Yes | Global | No |
| date_format | Yes | Both | No | ||
| datetime_format | Yes | Yes | Yes | Both | No |
| debug | Yes | Yes | Yes | Both | Yes |
| debug_sync | Yes | Both | Yes | ||
| default_week_format | Yes | Yes | Yes | Both | Yes |
| delay-key-write | Yes | Yes | Yes | ||
| - Variable: delay_key_write | Yes | Global | Yes | ||
| delayed_insert_limit | Yes | Yes | Yes | Global | Yes |
| delayed_insert_timeout | Yes | Yes | Yes | Global | Yes |
| delayed_queue_size | Yes | Yes | Yes | Global | Yes |
| div_precision_increment | Yes | Yes | Yes | Both | Yes |
| engine-condition-pushdown | Yes | Yes | Yes | ||
| - Variable: engine_condition_pushdown | Yes | Both | Yes | ||
| error_count | Yes | Session | No | ||
| event-scheduler | Yes | Yes | Yes | ||
| - Variable: event_scheduler | Yes | Global | Yes | ||
| expire_logs_days | Yes | Yes | Yes | Global | Yes |
| flush | Yes | Yes | Yes | Global | Yes |
| flush_time | Yes | Yes | Yes | Global | Yes |
| foreign_key_checks | Yes | Session | Yes | ||
| ft_boolean_syntax | Yes | Yes | Yes | Global | Yes |
| ft_max_word_len | Yes | Yes | Yes | Global | No |
| ft_min_word_len | Yes | Yes | Yes | Global | No |
| ft_query_expansion_limit | Yes | Yes | Yes | Global | No |
| ft_stopword_file | Yes | Yes | Yes | Global | No |
| general-log | Yes | Yes | Yes | ||
| - Variable: general_log | Yes | Global | Yes | ||
| general_log_file | Yes | Yes | Yes | Global | Yes |
| group_concat_max_len | Yes | Yes | Yes | Both | Yes |
| have_profiling | Yes | Global | No | ||
| hostname | Yes | Global | No | ||
| identity | Yes | Session | Yes | ||
| ignore_builtin_innodb | Yes | Yes | Yes | Global | No |
| init_connect | Yes | Yes | Yes | Global | Yes |
| init-file | Yes | Yes | No | ||
| - Variable: init_file | Yes | Global | No | ||
| init_slave | Yes | Yes | Yes | Global | Yes |
| innodb_adaptive_flushing | Yes | Yes | Yes | Global | Yes |
| innodb_adaptive_hash_index | Yes | Yes | Yes | Global | Yes |
| innodb_additional_mem_pool_size | Yes | Yes | Yes | Global | No |
| innodb_autoextend_increment | Yes | Yes | Yes | Global | Yes |
| innodb_autoinc_lock_mode | Yes | Yes | Yes | Global | No |
| innodb_buffer_pool_size | Yes | Yes | Yes | Global | No |
| innodb_change_buffering | Yes | Yes | Yes | Global | Yes |
| innodb_checksums | Yes | Yes | Yes | Global | No |
| innodb_commit_concurrency | Yes | Yes | Yes | Global | Yes |
| innodb_concurrency_tickets | Yes | Yes | Yes | Global | Yes |
| innodb_data_file_path | Yes | Yes | Yes | Global | No |
| innodb_data_home_dir | Yes | Yes | Yes | Global | No |
| innodb_doublewrite | Yes | Yes | Yes | Global | No |
| innodb_fast_shutdown | Yes | Yes | Yes | Global | Yes |
| innodb_file_format | Yes | Yes | Yes | Global | Yes |
| innodb_file_format_check | Yes | Yes | Yes | Global | Yes |
| innodb_file_per_table | Yes | Yes | Yes | Global | Yes |
| innodb_flush_log_at_trx_commit | Yes | Yes | Yes | Global | Yes |
| innodb_flush_method | Yes | Yes | Yes | Global | No |
| innodb_force_recovery | Yes | Yes | Yes | Global | No |
| innodb_io_capacity | Yes | Yes | Yes | Global | Yes |
| innodb_lock_wait_timeout | Yes | Yes | Yes | Both | Yes |
| innodb_locks_unsafe_for_binlog | Yes | Yes | Yes | Global | No |
| innodb_log_buffer_size | Yes | Yes | Yes | Global | No |
| innodb_log_file_size | Yes | Yes | Yes | Global | No |
| innodb_log_files_in_group | Yes | Yes | Yes | Global | No |
| innodb_log_group_home_dir | Yes | Yes | Yes | Global | No |
| innodb_max_dirty_pages_pct | Yes | Yes | Yes | Global | Yes |
| innodb_max_purge_lag | Yes | Yes | Yes | Global | Yes |
| innodb_mirrored_log_groups | Yes | Yes | Yes | Global | No |
| innodb_old_blocks_pct | Yes | Yes | Yes | Global | Yes |
| innodb_old_blocks_time | Yes | Yes | Yes | Global | Yes |
| innodb_open_files | Yes | Yes | Yes | Global | No |
| innodb_read_ahead_threshold | Yes | Yes | Yes | Global | Yes |
| innodb_read_io_threads | Yes | Yes | Yes | Global | No |
| innodb_replication_delay | Yes | Yes | Yes | Global | Yes |
| innodb_rollback_on_timeout | Yes | Yes | Yes | Global | No |
| innodb_spin_wait_delay | Yes | Yes | Yes | Global | Yes |
| innodb_stats_on_metadata | Yes | Yes | Yes | Global | Yes |
| innodb_stats_sample_pages | Yes | Yes | Yes | Global | Yes |
| innodb_strict_mode | Yes | Yes | Yes | Both | Yes |
| innodb_support_xa | Yes | Yes | Yes | Both | Yes |
| innodb_sync_spin_loops | Yes | Yes | Yes | Global | Yes |
| innodb_table_locks | Yes | Yes | Yes | Both | Yes |
| innodb_thread_concurrency | Yes | Yes | Yes | Global | Yes |
| innodb_thread_sleep_delay | Yes | Yes | Yes | Global | Yes |
| innodb_use_sys_malloc | Yes | Yes | Yes | Global | No |
| innodb_version | Yes | Global | No | ||
| innodb_write_io_threads | Yes | Yes | Yes | Global | No |
| insert_id | Yes | Session | Yes | ||
| interactive_timeout | Yes | Yes | Yes | Both | Yes |
| join_buffer_size | Yes | Yes | Yes | Both | Yes |
| keep_files_on_create | Yes | Yes | Yes | Both | Yes |
| key_buffer_size | Yes | Yes | Yes | Global | Yes |
| key_cache_age_threshold | Yes | Yes | Yes | Global | Yes |
| key_cache_block_size | Yes | Yes | Yes | Global | Yes |
| key_cache_division_limit | Yes | Yes | Yes | Global | Yes |
| language | Yes | Yes | Yes | Global | No |
| large_files_support | Yes | Global | No | ||
| large_page_size | Yes | Global | No | ||
| large-pages | Yes | Yes | No | ||
| - Variable: large_pages | Yes | Global | No | ||
| last_insert_id | Yes | Session | Yes | ||
| lc-messages | Yes | Yes | Yes | ||
| - Variable: lc_messages | Yes | Both | Yes | ||
| lc-messages-dir | Yes | Yes | No | ||
| - Variable: lc_messages_dir | Yes | Global | No | ||
| lc_time_names | Yes | Both | Yes | ||
| license | Yes | Global | No | ||
| local_infile | Yes | Global | Yes | ||
| lock_wait_timeout | Yes | Yes | Yes | Both | Yes |
| locked_in_memory | Yes | Global | No | ||
| log | Yes | Yes | Yes | Global | Yes |
| log_bin | Yes | Global | No | ||
| log-bin | Yes | Yes | Yes | Global | No |
| log-bin-trust-function-creators | Yes | Yes | Yes | ||
| - Variable: log_bin_trust_function_creators | Yes | Global | Yes | ||
| log-bin-trust-routine-creators | Yes | Yes | Yes | ||
| - Variable: log_bin_trust_routine_creators | Yes | Global | Yes | ||
| log-error | Yes | Yes | No | ||
| - Variable: log_error | Yes | Global | No | ||
| log-output | Yes | Yes | Yes | ||
| - Variable: log_output | Yes | Global | Yes | ||
| log-queries-not-using-indexes | Yes | Yes | Yes | ||
| - Variable: log_queries_not_using_indexes | Yes | Global | Yes | ||
| log-slave-updates | Yes | Yes | No | ||
| - Variable: log_slave_updates | Yes | Global | No | ||
| log-slow-queries | Yes | Yes | Yes | ||
| - Variable: log_slow_queries | Yes | Global | Yes | ||
| log-warnings | Yes | Yes | Yes | ||
| - Variable: log_warnings | Yes | Both | Yes | ||
| long_query_time | Yes | Yes | Yes | Both | Yes |
| low-priority-updates | Yes | Yes | Yes | ||
| - Variable: low_priority_updates | Yes | Both | Yes | ||
| lower_case_file_system | Yes | Yes | Yes | Global | No |
| lower_case_table_names | Yes | Yes | Yes | Global | No |
| master-bind | Yes | Yes | Yes | No | |
| max_allowed_packet | Yes | Yes | Yes | Both | Yes |
| max_binlog_cache_size | Yes | Yes | Yes | Global | Yes |
| max_binlog_size | Yes | Yes | Yes | Global | Yes |
| max_connect_errors | Yes | Yes | Yes | Global | Yes |
| max_connections | Yes | Yes | Yes | Global | Yes |
| max_delayed_threads | Yes | Yes | Yes | Both | Yes |
| max_error_count | Yes | Yes | Yes | Both | Yes |
| max_heap_table_size | Yes | Yes | Yes | Both | Yes |
| max_insert_delayed_threads | Yes | Both | Yes | ||
| max_join_size | Yes | Yes | Yes | Both | Yes |
| max_length_for_sort_data | Yes | Yes | Yes | Both | Yes |
| max_prepared_stmt_count | Yes | Yes | Yes | Global | Yes |
| max_relay_log_size | Yes | Yes | Yes | Global | Yes |
| max_seeks_for_key | Yes | Yes | Yes | Both | Yes |
| max_sort_length | Yes | Yes | Yes | Both | Yes |
| max_sp_recursion_depth | Yes | Yes | Yes | Both | Yes |
| max_tmp_tables | Yes | Yes | Yes | Both | Yes |
| max_user_connections | Yes | Yes | Yes | Both | Yes |
| max_write_lock_count | Yes | Yes | Yes | Global | Yes |
| memlock | Yes | Yes | Yes | Global | No |
| min-examined-row-limit | Yes | Yes | Yes | Both | Yes |
| myisam_data_pointer_size | Yes | Yes | Yes | Global | Yes |
| myisam_max_sort_file_size | Yes | Yes | Yes | Global | Yes |
| myisam_mmap_size | Yes | Yes | Yes | Global | No |
| myisam_recover_options | Yes | Global | No | ||
| myisam_repair_threads | Yes | Yes | Yes | Both | Yes |
| myisam_sort_buffer_size | Yes | Yes | Yes | Both | Yes |
| myisam_stats_method | Yes | Yes | Yes | Both | Yes |
| myisam_use_mmap | Yes | Yes | Yes | Global | Yes |
| ndb_autoincrement_prefetch_sz | Yes | Yes | Yes | Both | Yes |
| net_buffer_length | Yes | Yes | Yes | Both | Yes |
| net_read_timeout | Yes | Yes | Yes | Both | Yes |
| net_retry_count | Yes | Yes | Yes | Both | Yes |
| net_write_timeout | Yes | Yes | Yes | Both | Yes |
| new | Yes | Yes | Yes | Both | Yes |
| old | Yes | Yes | Yes | Global | No |
| old-alter-table | Yes | Yes | Yes | ||
| - Variable: old_alter_table | Yes | Both | Yes | ||
| old-passwords | Yes | Yes | Yes | ||
| - Variable: old_passwords | Yes | Both | Yes | ||
| open-files-limit | Yes | Yes | No | ||
| - Variable: open_files_limit | Yes | Global | No | ||
| optimizer_prune_level | Yes | Yes | Yes | Both | Yes |
| optimizer_search_depth | Yes | Yes | Yes | Both | Yes |
| optimizer_switch | Yes | Yes | Yes | Both | Yes |
| partition | Yes | Yes | No | ||
| - Variable: have_partitioning | Yes | Global | No | ||
| performance_schema | Yes | Yes | Yes | Global | No |
| performance_schema_events_waits_history_long_size | Yes | Yes | Yes | Global | No |
| performance_schema_events_waits_history_size | Yes | Yes | Yes | Global | No |
| performance_schema_max_cond_classes | Yes | Yes | Yes | Global | No |
| performance_schema_max_cond_instances | Yes | Yes | Yes | Global | No |
| performance_schema_max_file_classes | Yes | Yes | Yes | Global | No |
| performance_schema_max_file_handles | Yes | Yes | Yes | Global | No |
| performance_schema_max_file_instances | Yes | Yes | Yes | Global | No |
| performance_schema_max_mutex_classes | Yes | Yes | Yes | Global | No |
| performance_schema_max_mutex_instances | Yes | Yes | Yes | Global | No |
| performance_schema_max_rwlock_classes | Yes | Yes | Yes | Global | No |
| performance_schema_max_rwlock_instances | Yes | Yes | Yes | Global | No |
| performance_schema_max_table_handles | Yes | Yes | Yes | Global | No |
| performance_schema_max_table_instances | Yes | Yes | Yes | Global | No |
| performance_schema_max_thread_classes | Yes | Yes | Yes | Global | No |
| performance_schema_max_thread_instances | Yes | Yes | Yes | Global | No |
| pid-file | Yes | Yes | No | ||
| - Variable: pid_file | Yes | Global | No | ||
| plugin_dir | Yes | Yes | Yes | Global | No |
| port | Yes | Yes | Yes | Global | No |
| preload_buffer_size | Yes | Yes | Yes | Both | Yes |
| profiling | Yes | Session | Yes | ||
| profiling_history_size | Yes | Both | Yes | ||
| protocol_version | Yes | Global | No | ||
| pseudo_thread_id | Yes | Session | Yes | ||
| query_alloc_block_size | Yes | Yes | Yes | Both | Yes |
| query_cache_limit | Yes | Yes | Yes | Global | Yes |
| query_cache_min_res_unit | Yes | Yes | Yes | Global | Yes |
| query_cache_size | Yes | Yes | Yes | Global | Yes |
| query_cache_type | Yes | Yes | Yes | Both | Yes |
| query_cache_wlock_invalidate | Yes | Yes | Yes | Both | Yes |
| query_prealloc_size | Yes | Yes | Yes | Both | Yes |
| rand_seed1 | Yes | Session | Yes | ||
| rand_seed2 | Yes | Session | Yes | ||
| range_alloc_block_size | Yes | Yes | Yes | Both | Yes |
| read_buffer_size | Yes | Yes | Yes | Both | Yes |
| read_only | Yes | Yes | Yes | Global | Yes |
| read_rnd_buffer_size | Yes | Yes | Yes | Both | Yes |
| relay_log_purge | Yes | Yes | Yes | Global | Yes |
| relay_log_recovery | Yes | Yes | Yes | Global | Yes |
| relay_log_space_limit | Yes | Yes | Yes | Global | No |
| report-host | Yes | Yes | No | ||
| - Variable: report_host | Yes | Global | No | ||
| report-password | Yes | Yes | No | ||
| - Variable: report_password | Yes | Global | No | ||
| report-port | Yes | Yes | No | ||
| - Variable: report_port | Yes | Global | No | ||
| report-user | Yes | Yes | No | ||
| - Variable: report_user | Yes | Global | No | ||
| rpl_recovery_rank | Yes | Global | Yes | ||
| rpl_semi_sync_master_enabled | Yes | Global | Yes | ||
| rpl_semi_sync_master_timeout | Yes | Global | Yes | ||
| rpl_semi_sync_master_trace_level | Yes | Global | Yes | ||
| rpl_semi_sync_master_wait_no_slave | Yes | Global | Yes | ||
| rpl_semi_sync_slave_enabled | Yes | Global | Yes | ||
| rpl_semi_sync_slave_trace_level | Yes | Global | Yes | ||
| safe-show-database | Yes | Yes | Yes | Global | Yes |
| secure-auth | Yes | Yes | Yes | ||
| - Variable: secure_auth | Yes | Global | Yes | ||
| secure-file-priv | Yes | Yes | No | ||
| - Variable: secure_file_priv | Yes | Global | No | ||
| server-id | Yes | Yes | Yes | ||
| - Variable: server_id | Yes | Global | Yes | ||
| skip-external-locking | Yes | Yes | No | ||
| - Variable: skip_external_locking | Yes | Global | No | ||
| skip-networking | Yes | Yes | No | ||
| - Variable: skip_networking | Yes | Global | No | ||
| skip-show-database | Yes | Yes | No | ||
| - Variable: skip_show_database | Yes | Global | No | ||
| slave_compressed_protocol | Yes | Yes | Yes | Global | Yes |
| slave_exec_mode | Yes | Global | Yes | ||
| slave-load-tmpdir | Yes | Yes | No | ||
| - Variable: slave_load_tmpdir | Yes | Global | No | ||
| slave-net-timeout | Yes | Yes | Yes | ||
| - Variable: slave_net_timeout | Yes | Global | Yes | ||
| slave-skip-errors | Yes | Yes | No | ||
| - Variable: slave_skip_errors | Yes | Global | No | ||
| slave_transaction_retries | Yes | Yes | Yes | Global | Yes |
| slow_launch_time | Yes | Yes | Yes | Global | Yes |
| slow-query-log | Yes | Yes | Yes | ||
| - Variable: slow_query_log | Yes | Global | Yes | ||
| slow_query_log_file | Yes | Yes | Yes | Global | Yes |
| socket | Yes | Yes | Yes | Global | No |
| sort_buffer_size | Yes | Yes | Yes | Both | Yes |
| sql_auto_is_null | Yes | Session | Yes | ||
| sql_big_selects | Yes | Session | Yes | ||
| sql_big_tables | Yes | Session | Yes | ||
| sql_buffer_result | Yes | Session | Yes | ||
| sql_log_bin | Yes | Session | Yes | ||
| sql_log_off | Yes | Session | Yes | ||
| sql_log_update | Yes | Session | Yes | ||
| sql_low_priority_updates | Yes | Both | Yes | ||
| sql_max_join_size | Yes | Both | Yes | ||
| sql-mode | Yes | Yes | Yes | ||
| - Variable: sql_mode | Yes | Both | Yes | ||
| sql_notes | Yes | Session | Yes | ||
| sql_quote_show_create | Yes | Session | Yes | ||
| sql_safe_updates | Yes | Session | Yes | ||
| sql_select_limit | Yes | Both | Yes | ||
| sql_slave_skip_counter | Yes | Global | Yes | ||
| sql_warnings | Yes | Session | Yes | ||
| ssl-ca | Yes | Yes | No | ||
| - Variable: ssl_ca | Yes | Global | No | ||
| ssl-capath | Yes | Yes | No | ||
| - Variable: ssl_capath | Yes | Global | No | ||
| ssl-cert | Yes | Yes | No | ||
| - Variable: ssl_cert | Yes | Global | No | ||
| ssl-cipher | Yes | Yes | No | ||
| - Variable: ssl_cipher | Yes | Global | No | ||
| ssl-key | Yes | Yes | No | ||
| - Variable: ssl_key | Yes | Global | No | ||
| storage_engine | Yes | Both | Yes | ||
| sync_binlog | Yes | Yes | Yes | Global | Yes |
| sync_frm | Yes | Yes | Yes | Global | Yes |
| sync_master_info | Yes | Yes | Yes | ||
| - Variable: sync_relay_log | Yes | Global | Yes | ||
| sync_relay_log | Yes | Yes | Yes | Global | Yes |
| sync_relay_log_info | Yes | Yes | Yes | ||
| - Variable: sync_relay_log | Yes | Global | Yes | ||
| system_time_zone | Yes | Global | No | ||
| table_definition_cache | Yes | Yes | Yes | Global | Yes |
| table_lock_wait_timeout | Yes | Yes | Yes | Global | Yes |
| table_type | Yes | Both | Yes | ||
| time_zone | Yes | Yes | Yes | Both | Yes |
[a] This option is dynamic, but only the server should set this information. You should not set the value of this variable manually. [b] This option is dynamic, but only the server should set this information. You should not set the value of this variable manually. | |||||
For additional system variable information, see these sections:
Section 5.1.5, “Session System Variables”, describes system variables that exist only as session variables (that is, they do not have any global counterpart).
Section 5.1.6, “Using System Variables”, discusses the syntax for setting and displaying system variable values.
Section 5.1.6.2, “Dynamic System Variables”, lists the variables that can be set at runtime.
Information on tuning system variables can be found in Section 7.5.3, “Tuning Server Parameters”.
Section 13.6.3, “
InnoDBStartup Options and System Variables”, listsInnoDBsystem variables.MySQL Cluster System Variables, lists system variables which are specific to MySQL Cluster.
For information on server system variables specific to replication, see Section 16.1.3, “Replication and Binary Logging Options and Variables”.
Note
Some of the following variable descriptions refer to
“enabling” or “disabling” a variable.
These variables can be enabled with the
SET
statement by setting them to ON or
1, or disabled by setting them to
OFF or 0. However, to set
such a variable on the command line or in an option file, you
must set it to 1 or 0;
setting it to ON or OFF
will not work. For example, on the command line,
--delay_key_write=1 works but
--delay_key_write=ON does not.
Some system variables control the size of buffers or caches. For a given buffer, the server might need to allocate internal data structures. These structures typically are allocated from the total memory allocated to the buffer, and the amount of space required might be platform dependent. This means that when you assign a value to a system variable that controls a buffer size, the amount of space actually available might differ from the value assigned. In some cases, the amount might be less than the value assigned. It is also possible that the server will adjust a value upward. For example, if you assign a value of 0 to a variable for which the minimal value is 1024, the server will set the value to 1024.
Values for buffer sizes, lengths, and stack sizes are given in bytes unless otherwise specified.
Some system variables take file name values. Unless otherwise
specified, the default file location is the data directory if the
value is a relative path name. To specify the location explicitly,
use an absolute path name. Suppose that the data directory is
/var/mysql/data. If a file-valued variable is
given as a relative path name, it will be located under
/var/mysql/data. If the value is an absolute
path name, its location is as given by the path name.
Variable Name automatic_sp_privilegesVariable Scope Global Dynamic Variable Yes Permitted Values Type booleanDefault TRUEWhen this variable has a value of 1 (the default), the server automatically grants the
EXECUTEandALTER ROUTINEprivileges to the creator of a stored routine, if the user cannot already execute and alter or drop the routine. (TheALTER ROUTINEprivilege is required to drop the routine.) The server also automatically drops those privileges from the creator when the routine is dropped. Ifautomatic_sp_privilegesis 0, the server does not automatically add or drop these privileges.The creator of a routine is the account used to execute the
CREATEstatement for it. This might not be the same as the account named as theDEFINERin the routine definition.See also Section 18.2.2, “Stored Routines and MySQL Privileges”.
Command-Line Format --back_log=#Config-File Format back_logOption Sets Variable Yes, back_logVariable Name back_logVariable Scope Global Dynamic Variable No Permitted Values Type numericDefault 50Range 1-65535The number of outstanding connection requests MySQL can have. This comes into play when the main MySQL thread gets very many connection requests in a very short time. It then takes some time (although very little) for the main thread to check the connection and start a new thread. The
back_logvalue indicates how many requests can be stacked during this short time before MySQL momentarily stops answering new requests. You need to increase this only if you expect a large number of connections in a short period of time.In other words, this value is the size of the listen queue for incoming TCP/IP connections. Your operating system has its own limit on the size of this queue. The manual page for the Unix
listen()system call should have more details. Check your OS documentation for the maximum value for this variable.back_logcannot be set higher than your operating system limit.Command-Line Format --basedir=nameConfig-File Format basedirOption Sets Variable Yes, basedirVariable Name basedirVariable Scope Global Dynamic Variable No Permitted Values Type filenameThe MySQL installation base directory. This variable can be set with the
--basediroption. Relative path names for other variables usually are resolved relative to the base directory.Command-Line Format --bulk_insert_buffer_size=#Config-File Format bulk_insert_buffer_sizeOption Sets Variable Yes, bulk_insert_buffer_sizeVariable Name bulk_insert_buffer_sizeVariable Scope Both Dynamic Variable Yes Permitted Values Platform Bit Size 32Type numericDefault 8388608Range 0-4294967295Permitted Values Platform Bit Size 64Type numericDefault 8388608Range 0-18446744073709547520MyISAMuses a special tree-like cache to make bulk inserts faster forINSERT ... SELECT,INSERT ... VALUES (...), (...), ..., andLOAD DATA INFILEwhen adding data to nonempty tables. This variable limits the size of the cache tree in bytes per thread. Setting it to 0 disables this optimization. The default value is 8MB.Variable Name character_set_clientVariable Scope Both Dynamic Variable Yes Permitted Values Type stringThe character set for statements that arrive from the client. The session value of this variable is set using the character set requested by the client when the client connects to the server. (Many clients support a
--default-character-setoption to enable this character set to be specified explicitly. See also Section 9.1.4, “Connection Character Sets and Collations”.) The global value of the variable is used to set the session value in cases when the client-requested value is unknown or not available, or the server is configured to ignore client requests:The client is from a version of MySQL older than MySQL 4.1, and thus does not request a character set.
The client requests a character set not known to the server. For example, a Japanese-enabled client requests
sjiswhen connecting to a server not configured withsjissupport.mysqld was started with the
--skip-character-set-client-handshakeoption, which causes it to ignore client character set configuration. This reproduces MySQL 4.0 behavior and is useful should you wish to upgrade the server without upgrading all the clients.
Variable Name character_set_connectionVariable Scope Both Dynamic Variable Yes Permitted Values Type stringThe character set used for literals that do not have a character set introducer and for number-to-string conversion.
Variable Name character_set_databaseVariable Scope Both Dynamic Variable Yes Footnote This option is dynamic, but only the server should set this information. You should not set the value of this variable manually. Permitted Values Type stringThe character set used by the default database. The server sets this variable whenever the default database changes. If there is no default database, the variable has the same value as
character_set_server.Command-Line Format --character-set-filesystem=nameConfig-File Format character-set-filesystemOption Sets Variable Yes, character_set_filesystemVariable Name character_set_filesystemVariable Scope Both Dynamic Variable Yes Permitted Values Type stringThe file system character set. This variable is used to interpret string literals that refer to file names, such as in the
LOAD DATA INFILEandSELECT ... INTO OUTFILEstatements and theLOAD_FILE()function. Such file names are converted fromcharacter_set_clienttocharacter_set_filesystembefore the file opening attempt occurs. The default value isbinary, which means that no conversion occurs. For systems on which multi-byte file names are allowed, a different value may be more appropriate. For example, if the system represents file names using UTF-8, setcharacter_set_filesystemto'utf8'.Variable Name character_set_resultsVariable Scope Both Dynamic Variable Yes Permitted Values Type stringThe character set used for returning query results such as result sets or error messages to the client.
Command-Line Format --character-set-serverConfig-File Format character-set-serverOption Sets Variable Yes, character_set_serverVariable Name character_set_serverVariable Scope Both Dynamic Variable Yes Permitted Values Type stringThe server's default character set.
Variable Name character_set_systemVariable Scope Global Dynamic Variable No Permitted Values Type stringThe character set used by the server for storing identifiers. The value is always
utf8.Command-Line Format --character-sets-dir=nameConfig-File Format character-sets-dirOption Sets Variable Yes, character_sets_dirVariable Name character-sets-dirVariable Scope Global Dynamic Variable No Permitted Values Type filenameThe directory where character sets are installed.
Variable Name collation_connectionVariable Scope Both Dynamic Variable Yes Permitted Values Type stringThe collation of the connection character set.
Variable Name collation_databaseVariable Scope Both Dynamic Variable Yes Footnote This option is dynamic, but only the server should set this information. You should not set the value of this variable manually. Permitted Values Type stringThe collation used by the default database. The server sets this variable whenever the default database changes. If there is no default database, the variable has the same value as
collation_server.Command-Line Format --collation-serverConfig-File Format collation-serverOption Sets Variable Yes, collation_serverVariable Name collation_serverVariable Scope Both Dynamic Variable Yes Permitted Values Type stringThe server's default collation.
Command-Line Format --completion_type=#Config-File Format completion_typeOption Sets Variable Yes, completion_typeVariable Name competion_typeVariable Scope Both Dynamic Variable Yes Permitted Values Type numericDefault 0Valid Values 0,1,2The transaction completion type:
If the value is 0 (the default),
COMMITandROLLBACKare unaffected.If the value is 1,
COMMITandROLLBACKare equivalent toCOMMIT AND CHAINandROLLBACK AND CHAIN, respectively. (A new transaction starts immediately with the same isolation level as the just-terminated transaction.)If the value is 2,
COMMITandROLLBACKare equivalent toCOMMIT RELEASEandROLLBACK RELEASE, respectively. (The server disconnects after terminating the transaction.)
Command-Line Format --concurrent_insert[=#]Config-File Format concurrent_insertOption Sets Variable Yes, concurrent_insertVariable Name concurrent_insertVariable Scope Global Dynamic Variable Yes Permitted Values Type numericDefault 1Valid Values 0,1,2If 1 (the default), MySQL allows
INSERTandSELECTstatements to run concurrently forMyISAMtables that have no free blocks in the middle of the data file. You can turn this option off by starting mysqld with--safe-modeor--skip-new.This variable can take three integer values.
Value Description 0 Off 1 (Default) Enables concurrent insert for MyISAMtables that don't have holes2 Enables concurrent inserts for all MyISAMtables, even those that have holes. For a table with a hole, new rows are inserted at the end of the table if it is in use by another thread. Otherwise, MySQL acquires a normal write lock and inserts the row into the hole.See also Section 7.3.3, “Concurrent Inserts”.
Command-Line Format --connect_timeout=#Config-File Format connect_timeoutOption Sets Variable Yes, connect_timeoutVariable Name connect_timeoutVariable Scope Global Dynamic Variable Yes Permitted Values Type numericDefault 10The number of seconds that the mysqld server waits for a connect packet before responding with
Bad handshake. The default value is 10 seconds.Increasing the
connect_timeoutvalue might help if clients frequently encounter errors of the formLost connection to MySQL server at '.XXX', system error:errnoCommand-Line Format --datadir=nameConfig-File Format datadirOption Sets Variable Yes, datadirVariable Name datadirVariable Scope Global Dynamic Variable No Permitted Values Type filenameThe MySQL data directory. This variable can be set with the
--datadiroption.This variable is unused.
This variable is unused.
Command-Line Format --debug[=debug_options]Config-File Format debugVariable Name debugVariable Scope Both Dynamic Variable Yes Permitted Values Type stringDefault 'd:t:o,/tmp/mysqld.trace'This variable indicates the current debugging settings. It is available only for servers built with debugging support. The initial value comes from the value of instances of the
--debugoption given at server startup. The global and session values may be set at runtime; theSUPERprivilege is required, even for the session value.Assigning a value that begins with
+or-cause the value to added to or subtracted from the current value:mysql>
SET debug = 'T';mysql>SELECT @@debug;+---------+ | @@debug | +---------+ | T | +---------+ mysql>SET debug = '+P';mysql>SELECT @@debug;+---------+ | @@debug | +---------+ | P:T | +---------+ mysql>SET debug = '-P';mysql>SELECT @@debug;+---------+ | @@debug | +---------+ | T | +---------+Variable Name debug_syncVariable Scope Both Dynamic Variable Yes Permitted Values Type stringThis variable is the user interface to the Debug Sync facility. Use of Debug Sync requires that MySQL be configured with the
--enable-debug-syncoption (see Section 2.10.2, “Typical configure Options”). If Debug Sync is not compiled in, this system variable is not available.The global variable value is read only and indicates whether the facility is enabled. By default, Debug Sync is disabled and the value of
debug_syncisOFF. If the server is started with--debug-sync-timeout=, whereNNis a timeout value greater than 0, Debug Sync is enabled and the value ofdebug_syncisON - current signalfollowed by the signal name. Also,Nbecomes the default timeout for individual synchronization points.The session value can be read by any user and will have the same value as the global variable. The session value can be set by users that have the
SUPERprivilege to control synchronization points.For a description of the Debug Sync facility and how to use synchronization points, see MySQL Internals: Test Synchronization.
Command-Line Format --default_week_format=#Config-File Format default_week_formatOption Sets Variable Yes, default_week_formatVariable Name default_week_formatVariable Scope Both Dynamic Variable Yes Permitted Values Type numericDefault 0Range 0-7The default mode value to use for the
WEEK()function. See Section 11.6, “Date and Time Functions”.Command-Line Format --delay-key-write[=name]Config-File Format delay-key-writeOption Sets Variable Yes, delay_key_writeVariable Name delay-key-writeVariable Scope Global Dynamic Variable Yes Permitted Values Type enumerationDefault ONValid Values ON,OFF,ALLThis option applies only to
MyISAMtables. It can have one of the following values to affect handling of theDELAY_KEY_WRITEtable option that can be used inCREATE TABLEstatements.Option Description OFFDELAY_KEY_WRITEis ignored.ONMySQL honors any DELAY_KEY_WRITEoption specified inCREATE TABLEstatements. This is the default value.ALLAll new opened tables are treated as if they were created with the DELAY_KEY_WRITEoption enabled.If
DELAY_KEY_WRITEis enabled for a table, the key buffer is not flushed for the table on every index update, but only when the table is closed. This speeds up writes on keys a lot, but if you use this feature, you should add automatic checking of allMyISAMtables by starting the server with the--myisam-recoveroption (for example,--myisam-recover=BACKUP,FORCE). See Section 5.1.2, “Server Command Options”, and Section 13.5.1, “MyISAMStartup Options”.Warning
If you enable external locking with
--external-locking, there is no protection against index corruption for tables that use delayed key writes.Command-Line Format --delayed_insert_limit=#Config-File Format delayed_insert_limitOption Sets Variable Yes, delayed_insert_limitVariable Name delayed_insert_limitVariable Scope Global Dynamic Variable Yes Permitted Values Platform Bit Size 32Type numericDefault 100Range 1-4294967295Permitted Values Platform Bit Size 64Type numericDefault 100Range 1-18446744073709547520After inserting
delayed_insert_limitdelayed rows, theINSERT DELAYEDhandler thread checks whether there are anySELECTstatements pending. If so, it allows them to execute before continuing to insert delayed rows.Command-Line Format --delayed_insert_timeout=#Config-File Format delayed_insert_timeoutOption Sets Variable Yes, delayed_insert_timeoutVariable Name delayed_insert_timeoutVariable Scope Global Dynamic Variable Yes Permitted Values Type numericDefault 300How many seconds an
INSERT DELAYEDhandler thread should wait forINSERTstatements before terminating.Command-Line Format --delayed_queue_size=#Config-File Format delayed_queue_sizeOption Sets Variable Yes, delayed_queue_sizeVariable Name delayed_queue_sizeVariable Scope Global Dynamic Variable Yes Permitted Values Platform Bit Size 32Type numericDefault 1000Range 1-4294967295Permitted Values Platform Bit Size 64Type numericDefault 1000Range 1-18446744073709547520This is a per-table limit on the number of rows to queue when handling
INSERT DELAYEDstatements. If the queue becomes full, any client that issues anINSERT DELAYEDstatement waits until there is room in the queue again.Command-Line Format --div_precision_increment=#Config-File Format div_precision_incrementOption Sets Variable Yes, div_precision_incrementVariable Name div_precision_incrementVariable Scope Both Dynamic Variable Yes Permitted Values Type numericDefault 4Range 0-30This variable indicates the number of digits by which to increase the scale of the result of division operations performed with the
/operator. The default value is 4. The minimum and maximum values are 0 and 30, respectively. The following example illustrates the effect of increasing the default value.mysql>
SELECT 1/7;+--------+ | 1/7 | +--------+ | 0.1429 | +--------+ mysql>SET div_precision_increment = 12;mysql>SELECT 1/7;+----------------+ | 1/7 | +----------------+ | 0.142857142857 | +----------------+Command-Line Format --engine-condition-pushdownConfig-File Format engine-condition-pushdownOption Sets Variable Yes, engine_condition_pushdownVariable Name engine_condition_pushdownVariable Scope Both Dynamic Variable Yes Permitted Values Type booleanDefault ONWhen the value of this variable is 0 (
OFF), a query such asSELECT * FROM t WHERE mycol = 42, wheremycolis a nonindexed column, is executed as a full table scan. The storage engine sends every row to the MySQL server, which applies theWHEREcondition. Ifengine_condition_pushdownis set to 1 (ON), the condition is “pushed down” to the storage engine, which uses the condition to perform the scan, and sends back to the MySQL server only those rows that match the condition. By default, this variable isOFF.In MySQL 5.5, this variable is useful only with the
NDBCLUSTERstorage engine. However, we intend to implement it for additional storage engines in future MySQL releases.Setting this variable to
ONon a MySQL Server acting as a MySQL Cluster SQL node causesWHEREconditions on unindexed columns to be evaluated on the cluster's data nodes and only the rows that match to be sent back to the SQL node that issued the query. This means the amount of cluster data that must be sent over the network is greatly reduced, increasing the efficiency with which results are returned.For more information, see Section 7.2.7, “Condition Pushdown Optimization”.
Command-Line Format --event-scheduler[=value]Config-File Format event-schedulerOption Sets Variable Yes, event_schedulerVariable Name event_schedulerVariable Scope Global Dynamic Variable Yes Permitted Values Type enumerationDefault OFFValid Values ON,OFF,DISABLEDThis variable indicates the status of the Event Scheduler; possible values are
ON,OFF, andDISABLED, with the default beingOFF. This variable and its effects on the Event Scheduler's operation are discussed in greater detail in the Overview section of the Events chapter.Command-Line Format --expire_logs_days=#Config-File Format expire_logs_daysOption Sets Variable Yes, expire_logs_daysVariable Name expire_logs_daysVariable Scope Global Dynamic Variable Yes Permitted Values Type numericDefault 0Range 0-99The number of days for automatic binary log file removal. The default is 0, which means “no automatic removal.” Possible removals happen at startup and when the binary log is flushed. Log flushing occurs as indicated in Section 5.2, “MySQL Server Logs”.
To remove binary log files manually, use the
PURGE BINARY LOGSstatement. See Section 12.6.1.1, “PURGE BINARY LOGSSyntax”.Command-Line Format --flushConfig-File Format flushVariable Name flushVariable Scope Global Dynamic Variable Yes Permitted Values Type booleanDefault OFFIf
ON, the server flushes (synchronizes) all changes to disk after each SQL statement. Normally, MySQL does a write of all changes to disk only after each SQL statement and lets the operating system handle the synchronizing to disk. See Section B.5.4.2, “What to Do If MySQL Keeps Crashing”. This variable is set toONif you start mysqld with the--flushoption.Command-Line Format --flush_time=#Config-File Format flush_timeOption Sets Variable Yes, flush_timeVariable Name flush_timeVariable Scope Global Dynamic Variable Yes Permitted Values Type numericDefault 0Min Value 0Permitted Values Type (windows) numericDefault 1800Min Value 0If this is set to a nonzero value, all tables are closed every
flush_timeseconds to free up resources and synchronize unflushed data to disk. This option is best used only on Windows 9x or Me, or on systems with minimal resources.Command-Line Format --ft_boolean_syntax=nameConfig-File Format ft_boolean_syntaxVariable Name ft_boolean_syntaxVariable Scope Global Dynamic Variable Yes Permitted Values Type stringDefault +-><()~*:""&The list of operators supported by boolean full-text searches performed using
IN BOOLEAN MODE. See Section 11.8.2, “Boolean Full-Text Searches”.The default variable value is
'+ -><()~*:""&|'. The rules for changing the value are as follows:Operator function is determined by position within the string.
The replacement value must be 14 characters.
Each character must be an ASCII nonalphanumeric character.
Either the first or second character must be a space.
No duplicates are allowed except the phrase quoting operators in positions 11 and 12. These two characters are not required to be the same, but they are the only two that may be.
Positions 10, 13, and 14 (which by default are set to “
:”, “&”, and “|”) are reserved for future extensions.
Command-Line Format --ft_max_word_len=#Config-File Format ft_max_word_lenOption Sets Variable Yes, ft_max_word_lenVariable Name ft_max_word_lenVariable Scope Global Dynamic Variable No Permitted Values Type numericMin Value 10The maximum length of the word to be included in a
FULLTEXTindex.Note
FULLTEXTindexes must be rebuilt after changing this variable. UseREPAIR TABLE.tbl_nameQUICKCommand-Line Format --ft_min_word_len=#Config-File Format ft_min_word_lenOption Sets Variable Yes, ft_min_word_lenVariable Name ft_min_word_lenVariable Scope Global Dynamic Variable No Permitted Values Type numericDefault 4Min Value 1The minimum length of the word to be included in a
FULLTEXTindex.Note
FULLTEXTindexes must be rebuilt after changing this variable. UseREPAIR TABLE.tbl_nameQUICKCommand-Line Format --ft_query_expansion_limit=#Config-File Format ft_query_expansion_limitOption Sets Variable Yes, ft_query_expansion_limitVariable Name ft_query_expansion_limitVariable Scope Global Dynamic Variable No Permitted Values Type numericDefault 20Range 0-1000The number of top matches to use for full-text searches performed using
WITH QUERY EXPANSION.Command-Line Format --ft_stopword_file=nameConfig-File Format ft_stopword_fileOption Sets Variable Yes, ft_stopword_fileVariable Name ft_stopword_fileVariable Scope Global Dynamic Variable No Permitted Values Type filenameThe file from which to read the list of stopwords for full-text searches. The server looks for the file in the data directory unless an absolute path name is given to specify a different directory. All the words from the file are used; comments are not honored. By default, a built-in list of stopwords is used (as defined in the
storage/myisam/ft_static.cfile). Setting this variable to the empty string ('') disables stopword filtering.Note
FULLTEXTindexes must be rebuilt after changing this variable or the contents of the stopword file. UseREPAIR TABLE.tbl_nameQUICKCommand-Line Format --general-logConfig-File Format general-logOption Sets Variable Yes, general_logVariable Name general_logVariable Scope Global Dynamic Variable Yes Permitted Values Type booleanDefault OFFWhether the general query log is enabled. The value can be 0 (or
OFF) to disable the log or 1 (orON) to enable the log. The default value depends on whether the--general_logoption is given. The destination for log output is controlled by thelog_outputsystem variable; if that value isNONE, no log entries are written even if the log is enabled.Command-Line Format --general-log-file=file_nameConfig-File Format general_log_fileOption Sets Variable Yes, general_log_fileVariable Name general_log_fileVariable Scope Global Dynamic Variable Yes Permitted Values Type filenameDefault host_name.logThe name of the general query log file. The default value is
host_name.log--general_log_fileoption.Command-Line Format --group_concat_max_len=#Config-File Format group_concat_max_lenOption Sets Variable Yes, group_concat_max_lenVariable Name group_concat_max_lenVariable Scope Both Dynamic Variable Yes Permitted Values Platform Bit Size 32Type numericDefault 1024Range 4-4294967295Permitted Values Platform Bit Size 64Type numericDefault 1024Range 4-18446744073709547520The maximum allowed result length in bytes for the
GROUP_CONCAT()function. The default is 1024.YESif thezlibcompression library is available to the server,NOif not. If not, theCOMPRESS()andUNCOMPRESS()functions cannot be used.YESif thecrypt()system call is available to the server,NOif not. If not, theENCRYPT()function cannot be used.YESif mysqld supportsARCHIVEtables,NOif not.YESif mysqld supports dynamic loading of plugins,NOif not.YESif the server supports spatial data types,NOif not.YESif mysqld supportsInnoDBtables.DISABLEDif--skip-innodbis used.This variable is an alias for
have_ssl.YESif mysqld supports partitioning.YESif statement profiling is enabled,NOif not. See Section 12.5.5.31, “SHOW PROFILESyntax”.YESif mysqld supports the query cache,NOif not.YESifRTREEindexes are available,NOif not. (These are used for spatial indexes inMyISAMtables.)YESif mysqld supports SSL connections,NOif not.YESif symbolic link support is enabled,NOif not. This is required on Unix for support of theDATA DIRECTORYandINDEX DIRECTORYtable options, and on Windows for support of data directory symlinks.Variable Name hostnameVariable Scope Global Dynamic Variable No Permitted Values Type stringThe server sets this variable to the server host name at startup.
Command-Line Format --init-connect=nameConfig-File Format init_connectOption Sets Variable Yes, init_connectVariable Name init_connectVariable Scope Global Dynamic Variable Yes Permitted Values Type stringA string to be executed by the server for each client that connects. The string consists of one or more SQL statements. To specify multiple statements, separate them by semicolon characters. For example, each client begins by default with autocommit mode enabled. There is no global system variable to specify that autocommit should be disabled by default, but
init_connectcan be used to achieve the same effect:SET GLOBAL init_connect='SET autocommit=0';
This variable can also be set on the command line or in an option file. To set the variable as just shown using an option file, include these lines:
[mysqld] init_connect='SET autocommit=0'
Note that the content of
init_connectis not executed for users that have theSUPERprivilege. This is done so that an erroneous value forinit_connectdoes not prevent all clients from connecting. For example, the value might contain a statement that has a syntax error, thus causing client connections to fail. Not executinginit_connectfor users that have theSUPERprivilege enables them to open a connection and fix theinit_connectvalue.Command-Line Format --init-file=nameConfig-File Format init-fileOption Sets Variable Yes, init_fileVariable Name init_fileVariable Scope Global Dynamic Variable No Permitted Values Type filenameThe name of the file specified with the
--init-fileoption when you start the server. This should be a file containing SQL statements that you want the server to execute when it starts. Each statement must be on a single line and should not include comments. No statement terminator such as;,\g, or\Gshould be given at the end of each statement.Note that the
--init-fileoption is unavailable if MySQL was configured with the--disable-grant-optionsoption. See Section 2.10.2, “Typical configure Options”.innodb_xxxInnoDBsystem variables are listed in Section 13.6.3, “InnoDBStartup Options and System Variables”.Command-Line Format --interactive_timeout=#Config-File Format interactive_timeoutOption Sets Variable Yes, interactive_timeoutVariable Name interactive_timeoutVariable Scope Both Dynamic Variable Yes Permitted Values Type numericDefault 28800Min Value 1The number of seconds the server waits for activity on an interactive connection before closing it. An interactive client is defined as a client that uses the
CLIENT_INTERACTIVEoption tomysql_real_connect(). See alsowait_timeout.Command-Line Format --join_buffer_size=#Config-File Format join_buffer_sizeOption Sets Variable Yes, join_buffer_sizeVariable Name join_buffer_sizeVariable Scope Both Dynamic Variable Yes The size of the buffer that is used for plain index scans, range index scans, and joins that do not use indexes and thus perform full table scans. Normally, the best way to get fast joins is to add indexes. Increase the value of
join_buffer_sizeto get a faster full join when adding indexes is not possible. One join buffer is allocated for each full join between two tables. For a complex join between several tables for which indexes are not used, multiple join buffers might be necessary.The maximum allowable setting for
join_buffer_sizeis 4GB. Values larger than 4GB are allowed for 64-bit platforms (except 64-bit Windows, for which large values are truncated to 4GB with a warning).Command-Line Format --keep_files_on_create=#Config-File Format keep_files_on_createOption Sets Variable Yes, keep_files_on_createVariable Name keep_files_on_createVariable Scope Both Dynamic Variable Yes Permitted Values Type booleanDefault OFFIf a
MyISAMtable is created with noDATA DIRECTORYoption, the.MYDfile is created in the database directory. By default, ifMyISAMfinds an existing.MYDfile in this case, it overwrites it. The same applies to.MYIfiles for tables created with noINDEX DIRECTORYoption. To suppress this behavior, set thekeep_files_on_createvariable toON(1), in which caseMyISAMwill not overwrite existing files and returns an error instead. The default value isOFF(0).If a
MyISAMtable is created with aDATA DIRECTORYorINDEX DIRECTORYoption and an existing.MYDor.MYIfile is found, MyISAM always returns an error. It will not overwrite a file in the specified directory.Command-Line Format --key_buffer_size=#Config-File Format key_buffer_sizeOption Sets Variable Yes, key_buffer_sizeVariable Name key_buffer_sizeVariable Scope Global Dynamic Variable Yes Permitted Values Platform Bit Size 32Type numericDefault 8388608Range 8-4294967295Index blocks for
MyISAMtables are buffered and are shared by all threads.key_buffer_sizeis the size of the buffer used for index blocks. The key buffer is also known as the key cache.The maximum allowable setting for
key_buffer_sizeis 4GB on 32-bit platforms. Values larger than 4GB are allowed for 64-bit platforms. The effective maximum size might be less, depending on your available physical RAM and per-process RAM limits imposed by your operating system or hardware platform. The value of this variable indicates the amount of memory requested. Internally, the server allocates as much memory as possible up to this amount, but the actual allocation might be less.You can increase the value to get better index handling for all reads and multiple writes; on a system whose primary function is to run MySQL using the
MyISAMstorage engine, 25% of the machine's total memory is an acceptable value for this variable. However, you should be aware that, if you make the value too large (for example, more than 50% of the machine's total memory), your system might start to page and become extremely slow. This is because MySQL relies on the operating system to perform file system caching for data reads, so you must leave some room for the file system cache. You should also consider the memory requirements of any other storage engines that you may be using in addition toMyISAM.For even more speed when writing many rows at the same time, use
LOCK TABLES. See Section 7.2.22, “Speed ofINSERTStatements”.You can check the performance of the key buffer by issuing a
SHOW STATUSstatement and examining theKey_read_requests,Key_reads,Key_write_requests, andKey_writesstatus variables. (See Section 12.5.5, “SHOWSyntax”.) TheKey_reads/Key_read_requestsratio should normally be less than 0.01. TheKey_writes/Key_write_requestsratio is usually near 1 if you are using mostly updates and deletes, but might be much smaller if you tend to do updates that affect many rows at the same time or if you are using theDELAY_KEY_WRITEtable option.The fraction of the key buffer in use can be determined using
key_buffer_sizein conjunction with theKey_blocks_unusedstatus variable and the buffer block size, which is available from thekey_cache_block_sizesystem variable:1 - ((Key_blocks_unused × key_cache_block_size) / key_buffer_size)
This value is an approximation because some space in the key buffer is be allocated internally for administrative structures.
It is possible to create multiple
MyISAMkey caches. The size limit of 4GB applies to each cache individually, not as a group. See Section 7.4.5, “TheMyISAMKey Cache”.Command-Line Format --key_cache_age_threshold=#Config-File Format key_cache_age_thresholdOption Sets Variable Yes, key_cache_age_thresholdVariable Name key_cache_age_thresholdVariable Scope Global Dynamic Variable Yes Permitted Values Platform Bit Size 32Type numericDefault 300Range 100-4294967295Permitted Values Platform Bit Size 64Type numericDefault 300Range 100-18446744073709547520This value controls the demotion of buffers from the hot sublist of a key cache to the warm sublist. Lower values cause demotion to happen more quickly. The minimum value is 100. The default value is 300. See Section 7.4.5, “The
MyISAMKey Cache”.Command-Line Format --key_cache_block_size=#Config-File Format key_cache_block_sizeOption Sets Variable Yes, key_cache_block_sizeVariable Name key_cache_block_sizeVariable Scope Global Dynamic Variable Yes Permitted Values Type numericDefault 1024Range 512-16384The size in bytes of blocks in the key cache. The default value is 1024. See Section 7.4.5, “The
MyISAMKey Cache”.Command-Line Format --key_cache_division_limit=#Config-File Format key_cache_division_limitOption Sets Variable Yes, key_cache_division_limitVariable Name key_cache_division_limitVariable Scope Global Dynamic Variable Yes Permitted Values Type numericDefault 100Range 1-100The division point between the hot and warm sublists of the key cache buffer list. The value is the percentage of the buffer list to use for the warm sublist. Allowable values range from 1 to 100. The default value is 100. See Section 7.4.5, “The
MyISAMKey Cache”.Version Deprecated 5.5.0 Command-Line Format --language=nameConfig-File Format languageOption Sets Variable Yes, languageVariable Name languageVariable Scope Global Dynamic Variable No Deprecated 5.5.0, by lc-messages-dirPermitted Values Type filenameDefault /usr/local/mysql/share/mysql/english/The directory where error messages are located. See Section 9.2, “Setting the Error Message Language”.
languageis removed as of MySQL 5.5.0. Similar information is available from thelc_messages_dirandlc_messagesvariables.Variable Name large_files_supportVariable Scope Global Dynamic Variable No Whether mysqld was compiled with options for large file support.
Command-Line Format --large-pagesConfig-File Format large-pagesOption Sets Variable Yes, large_pagesVariable Name large_pagesVariable Scope Global Dynamic Variable No Platform Specific linux Permitted Values Type (linux) booleanDefault FALSEWhether large page support is enabled (via the
--large-pagesoption). See Section 7.5.9, “Enabling Large Page Support”.Variable Name large_page_sizeVariable Scope Global Dynamic Variable No Permitted Values Type (linux) numericDefault 0If large page support is enabled, this shows the size of memory pages. Currently, large memory pages are supported only on Linux; on other platforms, the value of this variable is always 0. See Section 7.5.9, “Enabling Large Page Support”.
Command-Line Format --lc-messages=nameConfig-File Format lc-messagesOption Sets Variable Yes, lc_messagesVariable Name lc-messagesVariable Scope Both Dynamic Variable Yes Permitted Values Type stringThe locale to use for error messages. The server converts the value to a language name and combines it with the value of the
lc_messages_dirto produce the location for the error message file. See Section 9.2, “Setting the Error Message Language”.Command-Line Format --lc-messages-dir=pathConfig-File Format lc-messages-dirOption Sets Variable Yes, lc_messages_dirVariable Name lc-messages-dirVariable Scope Global Dynamic Variable No Permitted Values Type stringThe directory where error messages are located. The value is used together with the value of
lc_messages_dirto produce the location for the error message file. See Section 9.2, “Setting the Error Message Language”.Variable Name lc_time_namesVariable Scope Both Dynamic Variable Yes Permitted Values Type stringThis variable specifies the locale that controls the language used to display day and month names and abbreviations. This variable affects the output from the
DATE_FORMAT(),DAYNAME()andMONTHNAME()functions. Locale names are POSIX-style values such as'ja_JP'or'pt_BR'. The default value is'en_US'regardless of your system's locale setting. For further information, see Section 9.7, “MySQL Server Locale Support”.Variable Name licenseVariable Scope Global Dynamic Variable No Permitted Values Type stringDefault GPLThe type of license the server has.
Variable Name local_infileVariable Scope Global Dynamic Variable Yes Permitted Values Type Whether
LOCALis supported forLOAD DATA INFILEstatements. See Section 5.3.5, “Security Issues withLOAD DATA LOCAL”.Version Introduced 6.0.14 Command-Line Format --lock_wait_timeout=#Config-File Format lock_wait_timeoutOption Sets Variable Yes, lock_wait_timeoutVariable Name lock_wait_timeoutVariable Scope Both Dynamic Variable Yes Permitted Values Type numericDefault 31536000Range 1-31536000This variable specifies the timeout in seconds for attempts to acquire metadata locks. The allowed values range from 1 to 3153600 (1 year). The default is 3153600.
This timeout applies to all statements that use metadata locks. These include DML and DDL operations on tables, views, stored procedures, and stored functions, as well as
LOCK TABLES,FLUSH TABLES WITH READ LOCK, andHANDLERstatements.The timeout value applies separately for each metadata lock attempt. A given statement can require more than one lock, so it is possible for the statement to block for longer than the
lock_wait_timeoutvalue before reporting a timeout error. When lock timeout occurs,ER_LOCK_WAIT_TIMEOUTis reported.lock_wait_timeoutdoes not apply to delayed inserts, which always execute with a timeout of 1 year. This is done to avoid unnecessary timeouts because a session that issues a delayed insert receives no notification of delayed insert timeouts.This variable was added in MySQL 5.5.3.
Variable Name locked_in_memoryVariable Scope Global Dynamic Variable No Whether logging of all statements to the general query log is enabled. See Section 5.2.3, “The General Query Log”.
This variable is deprecated; use
general_loginstead.Variable Name log_binVariable Scope Global Dynamic Variable No Whether the binary log is enabled. See Section 5.2.4, “The Binary Log”.
log_bin_trust_function_creatorsCommand-Line Format --log-bin-trust-function-creatorsConfig-File Format log-bin-trust-function-creatorsOption Sets Variable Yes, log_bin_trust_function_creatorsVariable Name log_bin_trust_function_creatorsVariable Scope Global Dynamic Variable Yes Permitted Values Type booleanDefault FALSEThis variable applies when binary logging is enabled. It controls whether stored function creators can be trusted not to create stored functions that will cause unsafe events to be written to the binary log. If set to 0 (the default), users are not allowed to create or alter stored functions unless they have the
SUPERprivilege in addition to theCREATE ROUTINEorALTER ROUTINEprivilege. A setting of 0 also enforces the restriction that a function must be declared with theDETERMINISTICcharacteristic, or with theREADS SQL DATAorNO SQLcharacteristic. If the variable is set to 1, MySQL does not enforce these restrictions on stored function creation. This variable also applies to trigger creation. See Section 18.6, “Binary Logging of Stored Programs”.Command-Line Format --log-error[=name]Config-File Format log-errorOption Sets Variable Yes, log_errorVariable Name log_errorVariable Scope Global Dynamic Variable No Permitted Values Type filenameThe location of the error log.
Command-Line Format --log-output[=name]Config-File Format log-outputOption Sets Variable Yes, log_outputVariable Name log_outputVariable Scope Global Dynamic Variable Yes Permitted Values Type enumerationDefault FILEValid Values TABLE,FILE,NONEThe destination for general query log and slow query log output. The value can be a comma-separated list of one or more of the words
TABLE(log to tables),FILE(log to files), orNONE(do not log to tables or files). The default value isTABLE.NONE, if present, takes precedence over any other specifiers. If the value isNONElog entries are not written even if the logs are enabled. If the logs are not enabled, no logging occurs even if the value oflog_outputis notNONE. For more information, see Section 5.2.1, “Selecting General Query and Slow Query Log Output Destinations”.Command-Line Format --log-queries-not-using-indexesConfig-File Format log-queries-not-using-indexesOption Sets Variable Yes, log_queries_not_using_indexesVariable Name log_queries_not_using_indexesVariable Scope Global Dynamic Variable Yes Permitted Values Type booleanWhether queries that do not use indexes are logged to the slow query log. See Section 5.2.5, “The Slow Query Log”.
Whether updates received by a slave server from a master server should be logged to the slave's own binary log. Binary logging must be enabled on the slave for this variable to have any effect. See Section 16.1.3, “Replication and Binary Logging Options and Variables”.
Command-Line Format --log-slow-queries[=name]Config-File Format log-slow-queriesOption Sets Variable Yes, log_slow_queriesVariable Name log_slow_queriesVariable Scope Global Dynamic Variable Yes Deprecated 5.1.29, by slow-query-logPermitted Values Type booleanWhether slow queries should be logged. “Slow” is determined by the value of the
long_query_timevariable. See Section 5.2.5, “The Slow Query Log”.This variable is deprecated; use
slow_query_loginstead.Command-Line Format --log-warnings[=#]Config-File Format log-warningsOption Sets Variable Yes, log_warningsVariable Name log_warningsVariable Scope Both Dynamic Variable Yes Disabled by skip-log-warningsPermitted Values Platform Bit Size 64Type numericDefault 1Range 0-18446744073709547520Whether to produce additional warning messages to the error log. It is enabled (1) by default and can be disabled by setting it to 0. Aborted connections and access-denied errors for new connection attempts are logged if the value is greater than 1. The server logs messages about statements that are unsafe for statement-based logging only if the value is greater than 0.
Command-Line Format --long_query_time=#Config-File Format long_query_timeOption Sets Variable Yes, long_query_timeVariable Name long_query_timeVariable Scope Both Dynamic Variable Yes Permitted Values Type numericDefault 10Min Value 0If a query takes longer than this many seconds, the server increments the
Slow_queriesstatus variable. If the slow query log is enabled, the query is logged to the slow query log file. This value is measured in real time, not CPU time, so a query that is under the threshold on a lightly loaded system might be above the threshold on a heavily loaded one. The minimum value is 0, and a resolution of microseconds is supported when logging to a file. However, the microseconds part is ignored and only integer values are written when logging to tables. The default value is 10. See Section 5.2.5, “The Slow Query Log”.Command-Line Format --low-priority-updatesConfig-File Format low-priority-updatesOption Sets Variable Yes, low_priority_updatesVariable Name low_priority_updatesVariable Scope Both Dynamic Variable Yes Permitted Values Type booleanDefault FALSEIf set to
1, allINSERT,UPDATE,DELETE, andLOCK TABLE WRITEstatements wait until there is no pendingSELECTorLOCK TABLE READon the affected table. This affects only storage engines that use only table-level locking (such asMyISAM,MEMORY, andMERGE). This variable previously was namedsql_low_priority_updates.Command-Line Format --lower_case_file_system[=#]Config-File Format lower_case_file_systemOption Sets Variable Yes, lower_case_file_systemVariable Name lower_case_file_systemVariable Scope Global Dynamic Variable No Permitted Values Type booleanThis variable describes the case sensitivity of file names on the file system where the data directory is located.
OFFmeans file names are case sensitive,ONmeans they are not case sensitive.Command-Line Format --lower_case_table_names[=#]Config-File Format lower_case_table_namesOption Sets Variable Yes, lower_case_table_namesVariable Name lower_case_table_namesVariable Scope Global Dynamic Variable No Permitted Values Type numericDefault 0Range 0-2If set to 1, table names are stored in lowercase on disk and table name comparisons are not case sensitive. If set to 2 table names are stored as given but compared in lowercase. This option also applies to database names and table aliases. See Section 8.2.2, “Identifier Case Sensitivity”.
If you are using
InnoDBtables, you should set this variable to 1 on all platforms to force names to be converted to lowercase.You should not set this variable to 0 if you are running MySQL on a system that does not have case-sensitive file names (such as Windows or Mac OS X). If this variable is not set at startup and the file system on which the data directory is located does not have case-sensitive file names, MySQL automatically sets
lower_case_table_namesto 2.Command-Line Format --max_allowed_packet=#Config-File Format max_allowed_packetOption Sets Variable Yes, max_allowed_packetVariable Name max_allowed_packetVariable Scope Both Dynamic Variable Yes Permitted Values Type numericDefault 1048576Range 1024-1073741824The maximum size of one packet or any generated/intermediate string.
The packet message buffer is initialized to
net_buffer_lengthbytes, but can grow up tomax_allowed_packetbytes when needed. This value by default is small, to catch large (possibly incorrect) packets.You must increase this value if you are using large
BLOBcolumns or long strings. It should be as big as the largestBLOByou want to use. The protocol limit formax_allowed_packetis 1GB. The value should be a multiple of 1024; nonmultiples are rounded down to the nearest multiple.When you change the message buffer size by changing the value of the
max_allowed_packetvariable, you should also change the buffer size on the client side if your client program allows it. On the client side,max_allowed_packethas a default of 1GB. Some programs such as mysql and mysqldump enable you to change the client-side value by settingmax_allowed_packeton the command line or in an option file.The session value of this variable is read only.
Command-Line Format --max_connect_errors=#Config-File Format max_connect_errorsOption Sets Variable Yes, max_connect_errorsVariable Name max_connect_errorsVariable Scope Global Dynamic Variable Yes Permitted Values Platform Bit Size 32Type numericDefault 10Range 1-4294967295Permitted Values Platform Bit Size 64Type numericDefault 10Range 1-18446744073709547520If there are more than this number of interrupted connections from a host, that host is blocked from further connections. You can unblock blocked hosts with the
FLUSH HOSTSstatement. If a connection is established successfully within fewer thanmax_connect_errorsattempts after a previous connection was interrupted, the error count for the host is cleared to zero. However, once a host is blocked, theFLUSH HOSTSstatement is the only way to unblock it.Command-Line Format --max_connections=#Config-File Format max_connectionsOption Sets Variable Yes, max_connectionsVariable Name max_connectionsVariable Scope Global Dynamic Variable Yes Permitted Values Type numericDefault 151Range 1-100000The number of simultaneous client connections allowed. By default, this is 151. See Section B.5.2.7, “
Too many connections”, for more information.MySQL Enterprise For notification that the maximum number of connections is getting dangerously high and for advice on setting the optimum value for
max_connectionssubscribe to the MySQL Enterprise Monitor. For more information, see http://www.mysql.com/products/enterprise/advisors.html.Increasing this value increases the number of file descriptors that mysqld requires. See Section 7.4.8, “How MySQL Opens and Closes Tables”, for comments on file descriptor limits.
Command-Line Format --max_delayed_threads=#Config-File Format max_delayed_threadsOption Sets Variable Yes, max_delayed_threadsVariable Name max_delayed_threadsVariable Scope Both Dynamic Variable Yes Permitted Values Type numericDefault 20Range 0-16384Do not start more than this number of threads to handle
INSERT DELAYEDstatements. If you try to insert data into a new table after allINSERT DELAYEDthreads are in use, the row is inserted as if theDELAYEDattribute wasn't specified. If you set this to 0, MySQL never creates a thread to handleDELAYEDrows; in effect, this disablesDELAYEDentirely.For the
SESSIONvalue of this variable, the only valid values are 0 or theGLOBALvalue.Command-Line Format --max_error_count=#Config-File Format max_error_countOption Sets Variable Yes, max_error_countVariable Name max_error_countVariable Scope Both Dynamic Variable Yes Permitted Values Type numericDefault 64Range 0-65535The maximum number of error, warning, and note messages to be stored for display by the
SHOW ERRORSandSHOW WARNINGSstatements.Command-Line Format --max_heap_table_size=#Config-File Format max_heap_table_sizeOption Sets Variable Yes, max_heap_table_sizeVariable Name max_heap_table_sizeVariable Scope Both Dynamic Variable Yes Permitted Values Type numericDefault 16777216Range 16384-4294967295This variable sets the maximum size to which
MEMORYtables are allowed to grow. The value of the variable is used to calculateMEMORYtableMAX_ROWSvalues. Setting this variable has no effect on any existingMEMORYtable, unless the table is re-created with a statement such asCREATE TABLEor altered withALTER TABLEorTRUNCATE TABLE. A server restart also sets the maximum size of existingMEMORYtables to the globalmax_heap_table_sizevalue.Note
On 64-bit platforms, the maximum value for this variable is 1844674407370954752.
MySQL Enterprise Subscribers to the MySQL Enterprise Monitor receive recommendations for the optimum setting for
max_heap_table_size. For more information, see http://www.mysql.com/products/enterprise/advisors.html.Variable Name max_insert_delayed_threadsVariable Scope Both Dynamic Variable Yes Permitted Values Type numericThis variable is a synonym for
max_delayed_threads.Command-Line Format --max_join_size=#Config-File Format max_join_sizeOption Sets Variable Yes, max_join_sizeVariable Name max_join_sizeVariable Scope Both Dynamic Variable Yes Permitted Values Type numericDefault 4294967295Range 1-4294967295Do not allow
SELECTstatements that probably need to examine more thanmax_join_sizerows (for single-table statements) or row combinations (for multiple-table statements) or that are likely to do more thanmax_join_sizedisk seeks. By setting this value, you can catchSELECTstatements where keys are not used properly and that would probably take a long time. Set it if your users tend to perform joins that lack aWHEREclause, that take a long time, or that return millions of rows.Setting this variable to a value other than
DEFAULTresets the value ofsql_big_selectsto0. If you set thesql_big_selectsvalue again, themax_join_sizevariable is ignored.If a query result is in the query cache, no result size check is performed, because the result has previously been computed and it does not burden the server to send it to the client.
This variable previously was named
sql_max_join_size.Command-Line Format --max_length_for_sort_data=#Config-File Format max_length_for_sort_dataOption Sets Variable Yes, max_length_for_sort_dataVariable Name max_length_for_sort_dataVariable Scope Both Dynamic Variable Yes Permitted Values Type numericDefault 1024Range 4-8388608The cutoff on the size of index values that determines which
filesortalgorithm to use. See Section 7.2.14, “ORDER BYOptimization”.Command-Line Format --max_prepared_stmt_count=#Config-File Format max_prepared_stmt_countOption Sets Variable Yes, max_prepared_stmt_countVariable Name max_prepared_stmt_countVariable Scope Global Dynamic Variable Yes Permitted Values Type numericDefault 16382Range 0-1048576This variable limits the total number of prepared statements in the server. It can be used in environments where there is the potential for denial-of-service attacks based on running the server out of memory by preparing huge numbers of statements. If the value is set lower than the current number of prepared statements, existing statements are not affected and can be used, but no new statements can be prepared until the current number drops below the limit. The default value is 16,382. The allowable range of values is from 0 to 1 million. Setting the value to 0 disables prepared statements.
Command-Line Format --max_relay_log_size=#Config-File Format max_relay_log_sizeOption Sets Variable Yes, max_relay_log_sizeVariable Name max_relay_log_sizeVariable Scope Global Dynamic Variable Yes Permitted Values Type numericDefault 0Range 0-1073741824If a write by a replication slave to its relay log causes the current log file size to exceed the value of this variable, the slave rotates the relay logs (closes the current file and opens the next one). If
max_relay_log_sizeis 0, the server usesmax_binlog_sizefor both the binary log and the relay log. Ifmax_relay_log_sizeis greater than 0, it constrains the size of the relay log, which enables you to have different sizes for the two logs. You must setmax_relay_log_sizeto between 4096 bytes and 1GB (inclusive), or to 0. The default value is 0. See Section 16.2.1, “Replication Implementation Details”.Command-Line Format --max_seeks_for_key=#Config-File Format max_seeks_for_keyOption Sets Variable Yes, max_seeks_for_keyVariable Name max_seeks_for_keyVariable Scope Both Dynamic Variable Yes Permitted Values Platform Bit Size 32Type numericDefault 4294967295Range 1-4294967295Permitted Values Platform Bit Size 64Type numericDefault 18446744073709547520Range 1-18446744073709547520Limit the assumed maximum number of seeks when looking up rows based on a key. The MySQL optimizer assumes that no more than this number of key seeks are required when searching for matching rows in a table by scanning an index, regardless of the actual cardinality of the index (see Section 12.5.5.23, “
SHOW INDEXSyntax”). By setting this to a low value (say, 100), you can force MySQL to prefer indexes instead of table scans.Command-Line Format --max_sort_length=#Config-File Format max_sort_lengthOption Sets Variable Yes, max_sort_lengthVariable Name max_sort_lengthVariable Scope Both Dynamic Variable Yes Permitted Values Type numericDefault 1024Range 4-8388608The number of bytes to use when sorting
BLOBorTEXTvalues. Only the firstmax_sort_lengthbytes of each value are used; the rest are ignored.Command-Line Format --max_sp_recursion_depth[=#]Config-File Format max_sp_recursion_depthOption Sets Variable Yes, max_sp_recursion_depthVariable Name max_sp_recursion_depthVariable Scope Both Dynamic Variable Yes Permitted Values Type numericDefault 0Max Value 255The number of times that any given stored procedure may be called recursively. The default value for this option is 0, which completely disallows recursion in stored procedures. The maximum value is 255.
Stored procedure recursion increases the demand on thread stack space. If you increase the value of
max_sp_recursion_depth, it may be necessary to increase thread stack size by increasing the value ofthread_stackat server startup.Command-Line Format --max_tmp_tables=#Config-File Format max_tmp_tablesOption Sets Variable Yes, max_tmp_tablesVariable Name max_tmp_tablesVariable Scope Both Dynamic Variable Yes Permitted Values Platform Bit Size 32Type numericDefault 32Range 1-4294967295Permitted Values Platform Bit Size 64Type numericDefault 32Range 1-18446744073709547520The maximum number of temporary tables a client can keep open at the same time. (This variable does not yet do anything.)
Command-Line Format --max_user_connections=#Config-File Format max_user_connectionsOption Sets Variable Yes, max_user_connectionsVariable Name max_user_connectionsVariable Scope Both Dynamic Variable Yes Permitted Values Type numericDefault 0Range 0-4294967295The maximum number of simultaneous connections allowed to any given MySQL user account. A value of 0 (the default) means “no limit.”
This variable has a global value that can be set at server startup or runtime. It also has a read-only session value that indicates the effective simultaneous-connection limit that applies to the account associated with the current session. The session value is initialized as follows:
If the user account has a nonzero
MAX_USER_CONNECTIONSresource limit, the sessionmax_user_connectionsvalue is set to that limit.Otherwise, the session
max_user_connectionsvalue is set to the global value.
Account resource limits are specified using the
GRANTstatement. See Section 5.5.4, “Setting Account Resource Limits”, and Section 12.5.1.3, “GRANTSyntax”.Command-Line Format --max_write_lock_count=#Config-File Format max_write_lock_countOption Sets Variable Yes, max_write_lock_countVariable Name max_write_lock_countVariable Scope Global Dynamic Variable Yes Permitted Values Platform Bit Size 32Type numericDefault 4294967295Range 1-4294967295Permitted Values Platform Bit Size 64Type numericDefault 18446744073709547520Range 1-18446744073709547520After this many write locks, allow some pending read lock requests to be processed in between.
Command-Line Format --min-examined-row-limit=#Config-File Format min-examined-row-limitVariable Name min_examined_row_limitVariable Scope Both Dynamic Variable Yes Permitted Values Platform Bit Size 32Type numericDefault 0Range 0-4294967295Permitted Values Platform Bit Size 64Type numericDefault 0Range 0-18446744073709547520Queries that examine fewer than this number of rows are not logged to the slow query log.
Command-Line Format --myisam_data_pointer_size=#Config-File Format myisam_data_pointer_sizeOption Sets Variable Yes, myisam_data_pointer_sizeVariable Name myisam_data_pointer_sizeVariable Scope Global Dynamic Variable Yes Permitted Values Type numericDefault 6Range 2-7The default pointer size in bytes, to be used by
CREATE TABLEforMyISAMtables when noMAX_ROWSoption is specified. This variable cannot be less than 2 or larger than 7. The default value is 6. See Section B.5.2.12, “The table is full”.Command-Line Format --myisam_max_sort_file_size=#Config-File Format myisam_max_sort_file_sizeOption Sets Variable Yes, myisam_max_sort_file_sizeVariable Name myisam_max_sort_file_sizeVariable Scope Global Dynamic Variable Yes Permitted Values Type numericDefault 2147483648The maximum size of the temporary file that MySQL is allowed to use while re-creating a
MyISAMindex (duringREPAIR TABLE,ALTER TABLE, orLOAD DATA INFILE). If the file size would be larger than this value, the index is created using the key cache instead, which is slower. The value is given in bytes.The default value is 2GB. If
MyISAMindex files exceed this size and disk space is available, increasing the value may help performance.Version Introduced 5.5.1 Command-Line Format --myisam_mmap_size=#Config-File Format myisam_mmap_sizeOption Sets Variable Yes, myisam_mmap_sizeVariable Name myisam_mmap_sizeVariable Scope Global Dynamic Variable No Permitted Values Platform Bit Size 32Type numericDefault 4294967295Range 7-4294967295Permitted Values Platform Bit Size 64Type numericDefault 18446744073709547520Range 7-18446744073709547520The maximum amount of memory to use for memory mapping compressed
MyISAMfiles. If many compressedMyISAMtables are used, the value can be decreased to reduce the likelihood of memory-swapping problems. This variable was added in MySQL 5.5.1.Variable Name myisam_recover_optionsVariable Scope Global Dynamic Variable No The value of the
--myisam-recoveroption. See Section 5.1.2, “Server Command Options”.Command-Line Format --myisam_repair_threads=#Config-File Format myisam_repair_threadsOption Sets Variable Yes, myisam_repair_threadsVariable Name myisam_repair_threadsVariable Scope Both Dynamic Variable Yes Permitted Values Platform Bit Size 32Type numericDefault 1Range 1-4294967295Permitted Values Platform Bit Size 64Type numericDefault 1Range 1-18446744073709547520If this value is greater than 1,
MyISAMtable indexes are created in parallel (each index in its own thread) during theRepair by sortingprocess. The default value is 1.Note
Multi-threaded repair is still beta-quality code.
Command-Line Format --myisam_sort_buffer_size=#Config-File Format myisam_sort_buffer_sizeOption Sets Variable Yes, myisam_sort_buffer_sizeVariable Name myisam_sort_buffer_sizeVariable Scope Both Dynamic Variable Yes Permitted Values Platform Bit Size 32Type numericDefault 8388608Range 4-4294967295Permitted Values Platform Bit Size 64Type numericDefault 8388608Range 4-18446744073709547520The size of the buffer that is allocated when sorting
MyISAMindexes during aREPAIR TABLEor when creating indexes withCREATE INDEXorALTER TABLE.The maximum allowable setting for
myisam_sort_buffer_sizeis 4GB. Values larger than 4GB are allowed for 64-bit platforms (except 64-bit Windows, for which large values are truncated to 4GB with a warning).Command-Line Format --myisam_stats_method=nameConfig-File Format myisam_stats_methodOption Sets Variable Yes, myisam_stats_methodVariable Name myisam_stats_methodVariable Scope Both Dynamic Variable Yes Permitted Values Type enumerationValid Values nulls_equal,nulls_unequal,nulls_ignoredHow the server treats
NULLvalues when collecting statistics about the distribution of index values forMyISAMtables. This variable has three possible values,nulls_equal,nulls_unequal, andnulls_ignored. Fornulls_equal, allNULLindex values are considered equal and form a single value group that has a size equal to the number ofNULLvalues. Fornulls_unequal,NULLvalues are considered unequal, and eachNULLforms a distinct value group of size 1. Fornulls_ignored,NULLvalues are ignored.The method that is used for generating table statistics influences how the optimizer chooses indexes for query execution, as described in Section 7.4.7, “
MyISAMIndex Statistics Collection”.Command-Line Format --myisam_use_mmapConfig-File Format myisam_use_mmapOption Sets Variable Yes, myisam_use_mmapVariable Name myisam_use_mmapVariable Scope Global Dynamic Variable Yes Permitted Values Type booleanDefault OFFUse memory mapping for reading and writing
MyISAMtables.Variable Name named_pipeVariable Scope Global Dynamic Variable No Platform Specific windows (Windows only.) Indicates whether the server supports connections over named pipes.
Command-Line Format --net_buffer_length=#Config-File Format net_buffer_lengthOption Sets Variable Yes, net_buffer_lengthVariable Name net_buffer_lengthVariable Scope Both Dynamic Variable Yes Permitted Values Type numericDefault 16384Range 1024-1048576Each client thread is associated with a connection buffer and result buffer. Both begin with a size given by
net_buffer_lengthbut are dynamically enlarged up tomax_allowed_packetbytes as needed. The result buffer shrinks tonet_buffer_lengthafter each SQL statement.This variable should not normally be changed, but if you have very little memory, you can set it to the expected length of statements sent by clients. If statements exceed this length, the connection buffer is automatically enlarged. The maximum value to which
net_buffer_lengthcan be set is 1MB.The session value of this variable is read only.
Command-Line Format --net_read_timeout=#Config-File Format net_read_timeoutOption Sets Variable Yes, net_read_timeoutVariable Name net_read_timeoutVariable Scope Both Dynamic Variable Yes Permitted Values Type numericDefault 30Min Value 1The number of seconds to wait for more data from a connection before aborting the read. This timeout applies only to TCP/IP connections, not to connections made via Unix socket files, named pipes, or shared memory. When the server is reading from the client,
net_read_timeoutis the timeout value controlling when to abort. When the server is writing to the client,net_write_timeoutis the timeout value controlling when to abort. See alsoslave_net_timeout.Command-Line Format --net_retry_count=#Config-File Format net_retry_countOption Sets Variable Yes, net_retry_countVariable Name net_retry_countVariable Scope Both Dynamic Variable Yes Permitted Values Platform Bit Size 32Type numericDefault 10Range 1-4294967295Permitted Values Platform Bit Size 64Type numericDefault 10Range 1-18446744073709547520If a read on a communication port is interrupted, retry this many times before giving up. This value should be set quite high on FreeBSD because internal interrupts are sent to all threads.
Command-Line Format --net_write_timeout=#Config-File Format net_write_timeoutOption Sets Variable Yes, net_write_timeoutVariable Name net_write_timeoutVariable Scope Both Dynamic Variable Yes Permitted Values Type numericDefault 60Min Value 1The number of seconds to wait for a block to be written to a connection before aborting the write. This timeout applies only to TCP/IP connections, not to connections made via Unix socket files, named pipes, or shared memory. See also
net_read_timeout.Command-Line Format --newConfig-File Format newOption Sets Variable Yes, newVariable Name newVariable Scope Both Dynamic Variable Yes Disabled by skip-newPermitted Values Type booleanDefault FALSEThis variable was used in MySQL 4.0 to turn on some 4.1 behaviors, and is retained for backward compatibility. In MySQL 5.5, its value is always
OFF.Command-Line Format oldConfig-File Format oldVariable Name oldVariable Scope Global Dynamic Variable No oldis a compatibility variable. It is disabled by default, but can be enabled at startup to revert the server to behaviors present in older versions.Currently, when
oldis enabled, it changes the default scope of index hints to that used prior to MySQL 5.1.17. That is, index hints with noFORclause apply only to how indexes are used for row retrieval and not to resolution ofORDER BYorGROUP BYclauses. (See Section 12.2.9.2, “Index Hint Syntax”.) Take care about enabling this in a replication setup. With statement-based binary logging, having different modes for the master and slaves might lead to replication errors.Command-Line Format --old-alter-tableConfig-File Format old-alter-tableOption Sets Variable Yes, old_alter_tableVariable Name old-alter-tableVariable Scope Both Dynamic Variable Yes Permitted Values Type booleanDefault OFFWhen this variable is enabled, the server does not use the optimized method of processing an
ALTER TABLEoperation. It reverts to using a temporary table, copying over the data, and then renaming the temporary table to the original, as used by MySQL 5.0 and earlier. For more information on the operation ofALTER TABLE, see Section 12.1.6, “ALTER TABLESyntax”.Command-Line Format --old_passwordsConfig-File Format old-passwordsOption Sets Variable Yes, old_passwordsVariable Name old_passwordsVariable Scope Both Dynamic Variable Yes Permitted Values Type booleanDefault FALSEWhether the server should use pre-4.1-style passwords for MySQL user accounts. See Section B.5.2.4, “
Client does not support authentication protocol”.This is not a variable, but it can be used when setting some variables. It is described in Section 12.5.4, “
SETSyntax”.Command-Line Format --open-files-limit=#Config-File Format open-files-limitOption Sets Variable Yes, open_files_limitVariable Name open_files_limitVariable Scope Global Dynamic Variable No Permitted Values Type numericDefault 0Range 0-65535The number of files that the operating system allows mysqld to open. This is the real value allowed by the system and might be different from the value you gave using the
--open-files-limitoption to mysqld or mysqld_safe. The value is 0 on systems where MySQL can't change the number of open files.Command-Line Format --optimizer_prune_level[=#]Config-File Format optimizer_prune_levelOption Sets Variable Yes, optimizer_prune_levelVariable Name optimizer_prune_levelVariable Scope Both Dynamic Variable Yes Permitted Values Type booleanDefault 1Controls the heuristics applied during query optimization to prune less-promising partial plans from the optimizer search space. A value of 0 disables heuristics so that the optimizer performs an exhaustive search. A value of 1 causes the optimizer to prune plans based on the number of rows retrieved by intermediate plans.
Command-Line Format --optimizer_search_depth[=#]Config-File Format optimizer_search_depthOption Sets Variable Yes, optimizer_search_depthVariable Name optimizer_search_depthVariable Scope Both Dynamic Variable Yes Permitted Values Type numericDefault 62The maximum depth of search performed by the query optimizer. Values larger than the number of relations in a query result in better query plans, but take longer to generate an execution plan for a query. Values smaller than the number of relations in a query return an execution plan quicker, but the resulting plan may be far from being optimal. If set to 0, the system automatically picks a reasonable value. If set to 63, the optimizer switches to the algorithm used in MySQL 5.0.0 (and previous versions) for performing searches. The value of 63 is deprecated and will be treated as invalid in a future MySQL release.
Command-Line Format --optimizer_switch=valueConfig-File Format optimizer_switchOption Sets Variable Yes, optimizer_switchVariable Name optimizer_switchVariable Scope Both Dynamic Variable Yes Permitted Values Type setValid Values index_merge={on|off},index_merge_intersection={on|off},index_merge_union={on|off}The
optimizer_switchsystem variable enables control over optimizer behavior. The value of this variable is a set of flags, each of which has a value ofonoroffto indicate whether the corresponding optimizer behavior is enabled or disabled. This variable has global and session values and be changed at runtime. The global default can be set at server startup.To see the current set of optimizer flags, select the variable value:
mysql>
SELECT @@optimizer_switch\G*************************** 1. row *************************** @@optimizer_switch: index_merge=on,index_merge_union=on, index_merge_sort_union=on,index_merge_intersection=onFor more information about the syntax of this variable and the optimizer behaviors that it controls, see Section 7.2.19, “Using
optimizer_switchto Control the Optimizer”.Command-Line Format --pid-file=nameConfig-File Format pid-fileOption Sets Variable Yes, pid_fileVariable Name pid_fileVariable Scope Global Dynamic Variable No Permitted Values Type filenameThe path name of the process ID (PID) file. This variable can be set with the
--pid-fileoption.Command-Line Format --plugin_dir=nameConfig-File Format plugin_dirOption Sets Variable Yes, plugin_dirVariable Name plugin_dirVariable Scope Global Dynamic Variable No Permitted Values Type filenameDefault /usr/local/mysql/lib/mysqlThe path name of the plugin directory.
Command-Line Format --port=#Config-File Format portOption Sets Variable Yes, portVariable Name portVariable Scope Global Dynamic Variable No Permitted Values Type numericDefault 3306The number of the port on which the server listens for TCP/IP connections. This variable can be set with the
--portoption.Command-Line Format --preload_buffer_size=#Config-File Format preload_buffer_sizeOption Sets Variable Yes, preload_buffer_sizeVariable Name preload_buffer_sizeVariable Scope Both Dynamic Variable Yes Permitted Values Type numericDefault 32768Range 1024-1073741824The size of the buffer that is allocated when preloading indexes.
Variable Name protocol_versionVariable Scope Global Dynamic Variable No Permitted Values Type numericThe version of the client/server protocol used by the MySQL server.
Variable Name pseudo_thread_idVariable Scope Session Dynamic Variable Yes Permitted Values Type numericThis variable is for internal server use.
Command-Line Format --query_alloc_block_size=#Config-File Format query_alloc_block_sizeOption Sets Variable Yes, query_alloc_block_sizeVariable Name query_alloc_block_sizeVariable Scope Both Dynamic Variable Yes Permitted Values Platform Bit Size 32Type numericDefault 8192Range 1024-4294967295Block Size 1024Permitted Values Platform Bit Size 64Type numericDefault 8192Range 1024-18446744073709547520Block Size 1024The allocation size of memory blocks that are allocated for objects created during statement parsing and execution. If you have problems with memory fragmentation, it might help to increase this parameter.
Command-Line Format --query_cache_limit=#Config-File Format query_cache_limitOption Sets Variable Yes, query_cache_limitVariable Name query_cache_limitVariable Scope Global Dynamic Variable Yes Permitted Values Platform Bit Size 32Type numericDefault 1048576Range 0-4294967295Permitted Values Platform Bit Size 64Type numericDefault 1048576Range 0-18446744073709547520Don't cache results that are larger than this number of bytes. The default value is 1MB.
Command-Line Format --query_cache_min_res_unit=#Config-File Format query_cache_min_res_unitOption Sets Variable Yes, query_cache_min_res_unitVariable Name query_cache_min_res_unitVariable Scope Global Dynamic Variable Yes Permitted Values Platform Bit Size 32Type numericDefault 4096Range 512-4294967295Permitted Values Platform Bit Size 64Type numericDefault 4096Range 512-18446744073709547520The minimum size (in bytes) for blocks allocated by the query cache. The default value is 4096 (4KB). Tuning information for this variable is given in Section 7.5.5.3, “Query Cache Configuration”.
Command-Line Format --query_cache_size=#Config-File Format query_cache_sizeOption Sets Variable Yes, query_cache_sizeVariable Name query_cache_sizeVariable Scope Global Dynamic Variable Yes Permitted Values Platform Bit Size 32Type numericDefault 0Range 0-4294967295Permitted Values Platform Bit Size 64Type numericDefault 0Range 0-18446744073709547520The amount of memory allocated for caching query results. The default value is 0, which disables the query cache. The allowable values are multiples of 1024; other values are rounded down to the nearest multiple. Note that
query_cache_sizebytes of memory are allocated even ifquery_cache_typeis set to 0. See Section 7.5.5.3, “Query Cache Configuration”, for more information.The query cache needs a minimum size of about 40KB to allocate its structures. (The exact size depends on system architecture.) If you set the value of
query_cache_sizetoo small, you'll get a warning, as described in Section 7.5.5.3, “Query Cache Configuration”.Command-Line Format --query_cache_type=#Config-File Format query_cache_typeOption Sets Variable Yes, query_cache_typeVariable Name query_cache_typeVariable Scope Both Dynamic Variable Yes Permitted Values Type enumerationDefault 1Valid Values 0,1,2Set the query cache type. Setting the
GLOBALvalue sets the type for all clients that connect thereafter. Individual clients can set theSESSIONvalue to affect their own use of the query cache. Possible values are shown in the following table.Option Description 0orOFFDon't cache results in or retrieve results from the query cache. Note that this does not deallocate the query cache buffer. To do that, you should set query_cache_sizeto 0.1orONCache all cacheable query results except for those that begin with SELECT SQL_NO_CACHE.2orDEMANDCache results only for cacheable queries that begin with SELECT SQL_CACHE.This variable defaults to
ON.If the server is started with
query_cache_typeset to 0, it does not acquire the query cache mutex at all, which means that the query cache cannot be enabled at runtime.Command-Line Format --query_cache_wlock_invalidateConfig-File Format query_cache_wlock_invalidateOption Sets Variable Yes, query_cache_wlock_invalidateVariable Name query_cache_wlock_invalidateVariable Scope Both Dynamic Variable Yes Permitted Values Type booleanDefault FALSENormally, when one client acquires a
WRITElock on aMyISAMtable, other clients are not blocked from issuing statements that read from the table if the query results are present in the query cache. Setting this variable to 1 causes acquisition of aWRITElock for a table to invalidate any queries in the query cache that refer to the table. This forces other clients that attempt to access the table to wait while the lock is in effect.Command-Line Format --query_prealloc_size=#Config-File Format query_prealloc_sizeOption Sets Variable Yes, query_prealloc_sizeVariable Name query_prealloc_sizeVariable Scope Both Dynamic Variable Yes Permitted Values Platform Bit Size 32Type numericDefault 8192Range 8192-4294967295Block Size 1024Permitted Values Platform Bit Size 64Type numericDefault 8192Range 8192-18446744073709547520Block Size 1024The size of the persistent buffer used for statement parsing and execution. This buffer is not freed between statements. If you are running complex queries, a larger
query_prealloc_sizevalue might be helpful in improving performance, because it can reduce the need for the server to perform memory allocation during query execution operations.Command-Line Format --range_alloc_block_size=#Config-File Format range_alloc_block_sizeOption Sets Variable Yes, range_alloc_block_sizeVariable Name range_alloc_block_sizeVariable Scope Both Dynamic Variable Yes Permitted Values Platform Bit Size 32Type numericDefault 4096Range 4096-4294967295Block Size 1024The size of blocks that are allocated when doing range optimization.
Command-Line Format --read_buffer_size=#Config-File Format read_buffer_sizeOption Sets Variable Yes, read_buffer_sizeVariable Name read_buffer_sizeVariable Scope Both Dynamic Variable Yes Permitted Values Type numericDefault 131072Range 8200-2147479552Each thread that does a sequential scan allocates a buffer of this size (in bytes) for each table it scans. If you do many sequential scans, you might want to increase this value, which defaults to 131072. The value of this variable should be a multiple of 4KB. If it is set to a value that is not a multiple of 4KB, its value will be rounded down to the nearest multiple of 4KB.
The maximum allowable setting for
read_buffer_sizeis 2GB.read_buffer_sizeandread_rnd_buffer_sizeare not specific to any storage engine and apply in a general manner for optimization. See Section 7.5.8, “How MySQL Uses Memory”, for example.Command-Line Format --read_onlyConfig-File Format read_onlyOption Sets Variable Yes, read_onlyVariable Name read_onlyVariable Scope Global Dynamic Variable Yes Permitted Values Type numericDefault 0This variable is off by default. When it is enabled, the server allows no updates except from users that have the
SUPERprivilege or (on a slave server) from updates performed by slave threads. On a slave server, this can be useful to ensure that the slave accepts updates only from its master server and not from clients. This variable does not apply toTEMPORARYtables, nor does it prevent the server from inserting rows into the log tables (see Section 5.2.1, “Selecting General Query and Slow Query Log Output Destinations”).read_onlyexists only as aGLOBALvariable, so changes to its value require theSUPERprivilege. Changes toread_onlyon a master server are not replicated to slave servers. The value can be set on a slave server independent of the setting on the master.The following conditions apply:
If you attempt to enable
read_onlywhile you have any explicit locks (acquired withLOCK TABLES) or have a pending transaction, an error occurs.If you attempt to enable
read_onlywhile other clients hold explicit table locks or have pending transactions, the attempt blocks until the locks are released and the transactions end. While the attempt to enableread_onlyis pending, requests by other clients for table locks or to begin transactions also block untilread_onlyhas been set.read_onlycan be enabled while you hold a global read lock (acquired withFLUSH TABLES WITH READ LOCK) because that does not involve table locks.
As of MySQL 5.5.3, attempts to set
read_onlyblock for active transactions that hold metadata locks until those transactions end.Command-Line Format --read_rnd_buffer_size=#Config-File Format read_rnd_buffer_sizeOption Sets Variable Yes, read_rnd_buffer_sizeVariable Name read_rnd_buffer_sizeVariable Scope Both Dynamic Variable Yes Permitted Values Type numericDefault 262144Range 8200-4294967295When reading rows in sorted order following a key-sorting operation, the rows are read through this buffer to avoid disk seeks. See Section 7.2.14, “
ORDER BYOptimization”. Setting the variable to a large value can improveORDER BYperformance by a lot. However, this is a buffer allocated for each client, so you should not set the global variable to a large value. Instead, change the session variable only from within those clients that need to run large queries.The maximum allowable setting for
read_rnd_buffer_sizeis 2GB.read_buffer_sizeandread_rnd_buffer_sizeare not specific to any storage engine and apply in a general manner for optimization. See Section 7.5.8, “How MySQL Uses Memory”, for example.Command-Line Format --relay_log_purgeConfig-File Format relay_log_purgeOption Sets Variable Yes, relay_log_purgeVariable Name relay_log_purgeVariable Scope Global Dynamic Variable Yes Permitted Values Type booleanDefault TRUEDisables or enables automatic purging of relay log files as soon as they are not needed any more. The default value is 1 (
ON).Command-Line Format --relay_log_space_limit=#Config-File Format relay_log_space_limitOption Sets Variable Yes, relay_log_space_limitVariable Name relay_log_space_limitVariable Scope Global Dynamic Variable No Permitted Values Platform Bit Size 32Type numericDefault 0Range 0-4294967295Permitted Values Platform Bit Size 64Type numericDefault 0Range 0-18446744073709547520The maximum amount of space to use for all relay logs.
The value of the
--report-hostoption.The value of the
--report-passwordoption.The value of the
--report-portoption.The value of the
--report-useroption.Controls whether semisynchronous replication is enabled on the master. To enable or disable the plugin, set this variable to 1 or 0, respectively. The default is 1.
This variable is available only if the master-side semisynchronous replication plugin is installed.
A value in seconds that controls how long the master waits on a commit for acknowledgment from a slave before timing out and reverting to asynchronous replication. The default value is 10 seconds.
This variable is available only if the master-side semisynchronous replication plugin is installed.
rpl_semi_sync_master_trace_levelThe semisynchronous replication debug trace level on the master. Currently, four levels are defined:
1 = general level (for example, time function failures)
16 = detail level (more verbose information)
32 = net wait level (more information about network waits)
64 = function level (information about function entry and exit)
This variable is available only if the master-side semisynchronous replication plugin is installed.
rpl_semi_sync_master_wait_no_slaveWith semisynchronous replication, for each transaction, the master waits until timeout for acknowledgement of receipt from some semisynchronous slave. If no response occurs during this period, the master reverts to normal replication. This variable controls whether the master waits for the timeout to expire before reverting to normal replication even if the slave count drops to zero during the timeout period.
If the value is
ON(the default), it is allowable for the slave count to drop to zero during the timeout period (for example, if slaves disconnect). The master still waits for the timeout, so as long as some slave reconnects and acknowledges the transaction within the timeout interval, semisynchronous replication continues.If the value is
OFF, the master reverts to normal replication if the slave count drops to zero during the timeout period.This variable is available only if the master-side semisynchronous replication plugin is installed.
Controls whether semisynchronous replication is enabled on the slave. To enable or disable the plugin, set this variable to 1 or 0, respectively. The default is 1.
This variable is available only if the slave-side semisynchronous replication plugin is installed.
rpl_semi_sync_slave_trace_levelThe semisynchronous replication debug trace level on the slave. See
rpl_semi_sync_master_trace_levelfor the allowable values.This variable is available only if the slave-side semisynchronous replication plugin is installed.
Command-Line Format --secure-authConfig-File Format secure-authOption Sets Variable Yes, secure_authVariable Name secure_authVariable Scope Global Dynamic Variable Yes Permitted Values Type booleanDefault FALSEIf the MySQL server has been started with the
--secure-authoption, it blocks connections from all accounts that have passwords stored in the old (pre-4.1) format. In that case, the value of this variable isON, otherwise it isOFF.You should enable this option if you want to prevent all use of passwords employing the old format (and hence insecure communication over the network).
Server startup fails with an error if this option is enabled and the privilege tables are in pre-4.1 format. See Section B.5.2.4, “
Client does not support authentication protocol”.Command-Line Format --secure-file-privConfig-File Format secure-file-privOption Sets Variable Yes, secure_file_privVariable Name secure_file_privVariable Scope Global Dynamic Variable No Permitted Values Type stringBy default, this variable is empty. If set to the name of a directory, it limits the effect of the
LOAD_FILE()function and theLOAD DATAandSELECT ... INTO OUTFILEstatements to work only with files in that directory.Command-Line Format --server-id=#Config-File Format server-idOption Sets Variable Yes, server_idVariable Name server_idVariable Scope Global Dynamic Variable Yes Permitted Values Type numericDefault 0Range 0-4294967295The server ID, used in replication to give each master and slave a unique identity. This variable is set by the
--server-idoption. For each server participating in replication, you should pick a positive integer in the range from 1 to 232 – 1 to act as that server's ID.Variable Name shared_memoryVariable Scope Global Dynamic Variable No Platform Specific windows (Windows only.) Whether the server allows shared-memory connections.
Variable Name shared_memory_base_nameVariable Scope Global Dynamic Variable No Platform Specific windows (Windows only.) The name of shared memory to use for shared-memory connections. This is useful when running multiple MySQL instances on a single physical machine. The default name is
MYSQL. The name is case sensitive.This is
OFFif mysqld uses external locking,ONif external locking is disabled.This is
ONif the server allows only local (non-TCP/IP) connections. On Unix, local connections use a Unix socket file. On Windows, local connections use a named pipe or shared memory. On NetWare, only TCP/IP connections are supported, so do not set this variable toON. This variable can be set toONwith the--skip-networkingoption.This prevents people from using the
SHOW DATABASESstatement if they do not have theSHOW DATABASESprivilege. This can improve security if you have concerns about users being able to see databases belonging to other users. Its effect depends on theSHOW DATABASESprivilege: If the variable value isON, theSHOW DATABASESstatement is allowed only to users who have theSHOW DATABASESprivilege, and the statement displays all database names. If the value isOFF,SHOW DATABASESis allowed to all users, but displays the names of only those databases for which the user has theSHOW DATABASESor other privilege.Command-Line Format --slow_launch_time=#Config-File Format slow_launch_timeOption Sets Variable Yes, slow_launch_timeVariable Name slow_launch_timeVariable Scope Global Dynamic Variable Yes Permitted Values Type numericDefault 2If creating a thread takes longer than this many seconds, the server increments the
Slow_launch_threadsstatus variable.Whether the slow query log is enabled. The value can be 0 (or
OFF) to disable the log or 1 (orON) to enable the log. The default value depends on whether the--slow_query_logoption is given. The destination for log output is controlled by thelog_outputsystem variable; if that value isNONE, no log entries are written even if the log is enabled.Command-Line Format --slow-query-log-file=file_nameConfig-File Format slow_query_log_fileOption Sets Variable Yes, slow_query_log_fileVariable Name slow_query_log_fileVariable Scope Global Dynamic Variable Yes Permitted Values Type filenameThe name of the slow query log file. The default value is
host_name-slow.log--slow_query_log_fileoption.Command-Line Format --socket=nameConfig-File Format socketOption Sets Variable Yes, socketVariable Name socketVariable Scope Global Dynamic Variable No Permitted Values Type filenameDefault /tmp/mysql.sockOn Unix platforms, this variable is the name of the socket file that is used for local client connections. The default is
/tmp/mysql.sock. (For some distribution formats, the directory might be different, such as/var/lib/mysqlfor RPMs.)On Windows, this variable is the name of the named pipe that is used for local client connections. The default value is
MySQL(not case sensitive).Command-Line Format --sort_buffer_size=#Config-File Format sort_buffer_sizeOption Sets Variable Yes, sort_buffer_sizeVariable Name sort_buffer_sizeVariable Scope Both Dynamic Variable Yes Permitted Values Platform Bit Size 32Type numericDefault 2097144Max Value 4294967295Permitted Values Platform Bit Size 64Type numericDefault 2097144Max Value 18446744073709547520Each thread that needs to do a sort allocates a buffer of this size. Increase this value for faster
ORDER BYorGROUP BYoperations. See Section B.5.4.4, “Where MySQL Stores Temporary Files”.The maximum allowable setting for
sort_buffer_sizeis 4GB. Values larger than 4GB are allowed for 64-bit platforms (except 64-bit Windows, for which large values are truncated to 4GB with a warning).Command-Line Format --sql-mode=nameConfig-File Format sql-modeOption Sets Variable Yes, sql_modeVariable Name sql_modeVariable Scope Both Dynamic Variable Yes Permitted Values Type setDefault ''Valid Values ALLOW_INVALID_DATES,ANSI_QUOTES,ERROR_FOR_DIVISION_BY_ZERO,HIGH_NOT_PRECEDENCE,IGNORE_SPACE,NO_AUTO_CREATE_USER,NO_AUTO_VALUE_ON_ZERO,NO_BACKSLASH_ESCAPES,NO_DIR_IN_CREATE,NO_ENGINE_SUBSTITUTION,NO_FIELD_OPTIONS,NO_KEY_OPTIONS,NO_TABLE_OPTIONS,NO_UNSIGNED_SUBTRACTION,NO_ZERO_DATE,NO_ZERO_IN_DATE,ONLY_FULL_GROUP_BY,PAD_CHAR_TO_FULL_LENGTH,PIPES_AS_CONCAT,REAL_AS_FLOAT,STRICT_ALL_TABLES,STRICT_TRANS_TABLESThe current server SQL mode, which can be set dynamically. See Section 5.1.8, “Server SQL Modes”.
Variable Name sql_select_limitVariable Scope Both Dynamic Variable Yes Permitted Values Type numericThe maximum number of rows to return from
SELECTstatements. The default value for a new connection is the maximum number of rows that the server allows per table, which depends on the server configuration and may be affected if the server build was configured with--with-big-tables. Typical default values are (232)–1 or (264)–1. If you have changed the limit, the default value can be restored by assigning a value ofDEFAULT.If a
SELECThas aLIMITclause, theLIMITtakes precedence over the value ofsql_select_limit.sql_select_limitdoes not apply toSELECTstatements executed within stored routines. It also does not apply toSELECTstatements that do not produce a result set to be returned to the client. These includeSELECTstatements in subqueries,CREATE TABLE ... SELECT, andINSERT INTO ... SELECT.Command-Line Format --ssl-ca=nameConfig-File Format ssl-caOption Sets Variable Yes, ssl_caVariable Name ssl_caVariable Scope Global Dynamic Variable No Permitted Values Type filenameThe path to a file with a list of trusted SSL CAs.
Command-Line Format --ssl-capath=nameConfig-File Format ssl-capathOption Sets Variable Yes, ssl_capathVariable Name ssl_capathVariable Scope Global Dynamic Variable No Permitted Values Type filenameThe path to a directory that contains trusted SSL CA certificates in PEM format.
Command-Line Format --ssl-cert=nameConfig-File Format ssl-certOption Sets Variable Yes, ssl_certVariable Name ssl_certVariable Scope Global Dynamic Variable No Permitted Values Type filenameThe name of the SSL certificate file to use for establishing a secure connection.
Command-Line Format --ssl-cipher=nameConfig-File Format ssl-cipherOption Sets Variable Yes, ssl_cipherVariable Name ssl_cipherVariable Scope Global Dynamic Variable No Permitted Values Type filenameA list of allowable ciphers to use for SSL encryption.
Command-Line Format --ssl-key=nameConfig-File Format ssl-keyOption Sets Variable Yes, ssl_keyVariable Name ssl_keyVariable Scope Global Dynamic Variable No Permitted Values Type stringThe name of the SSL key file to use for establishing a secure connection.
Variable Name storage_engineVariable Scope Both Dynamic Variable Yes Permitted Values Type enumerationThe default storage engine (table type). To set the storage engine at server startup, use the
--default-storage-engineoption. See Section 5.1.2, “Server Command Options”.Command-Line Format --sync-frmConfig-File Format sync_frmOption Sets Variable Yes, sync_frmVariable Name sync_frmVariable Scope Global Dynamic Variable Yes Permitted Values Type booleanDefault TRUEIf this variable is set to 1, when any nontemporary table is created its
.frmfile is synchronized to disk (usingfdatasync()). This is slower but safer in case of a crash. The default is 1.Variable Name system_time_zoneVariable Scope Global Dynamic Variable No Permitted Values Type stringThe server system time zone. When the server begins executing, it inherits a time zone setting from the machine defaults, possibly modified by the environment of the account used for running the server or the startup script. The value is used to set
system_time_zone. Typically the time zone is specified by theTZenvironment variable. It also can be specified using the--timezoneoption of the mysqld_safe script.The
system_time_zonevariable differs fromtime_zone. Although they might have the same value, the latter variable is used to initialize the time zone for each client that connects. See Section 9.6, “MySQL Server Time Zone Support”.Command-Line Format --table_definition_cache=#Config-File Format table_definition_cacheOption Sets Variable Yes, table_definition_cacheVariable Name table_definition_cacheVariable Scope Global Dynamic Variable Yes Permitted Values Type numericDefault 400Range 400-524288The number of table definitions that can be stored in the definition cache. If you use a large number of tables, you can create a large table definition cache to speed up opening of tables. The table definition cache takes less space and does not use file descriptors, unlike the normal table cache. The minimum and default values are both 400.
Version Removed 5.5.3 Command-Line Format --table_lock_wait_timeout=#Config-File Format table_lock_wait_timeoutOption Sets Variable Yes, table_lock_wait_timeoutVariable Name table_lock_wait_timeoutVariable Scope Global Dynamic Variable Yes Permitted Values Type numericDefault 50Range 1-1073741824This variable is unused. It was removed in 5.5.3.
Command-Line Format --table-open-cache=#Config-File Format table_open_cacheVariable Name table_open_cacheVariable Scope Global Dynamic Variable Yes Permitted Values Type numericDefault 400Range 400-524288The number of open tables for all threads. Increasing this value increases the number of file descriptors that mysqld requires. You can check whether you need to increase the table cache by checking the
Opened_tablesstatus variable. See Section 5.1.7, “Server Status Variables”. If the value ofOpened_tablesis large and you don't doFLUSH TABLESoften (which just forces all tables to be closed and reopened), then you should increase the value of thetable_open_cachevariable. For more information about the table cache, see Section 7.4.8, “How MySQL Opens and Closes Tables”.This variable was removed in MySQL 5.5.3. Use
storage_engineinstead.Command-Line Format --thread_cache_size=#Config-File Format thread_cache_sizeOption Sets Variable Yes, thread_cache_sizeVariable Name thread_cache_sizeVariable Scope Global Dynamic Variable Yes Permitted Values Type numericDefault 0Range 0-16384How many threads the server should cache for reuse. When a client disconnects, the client's threads are put in the cache if there are fewer than
thread_cache_sizethreads there. Requests for threads are satisfied by reusing threads taken from the cache if possible, and only when the cache is empty is a new thread created. This variable can be increased to improve performance if you have a lot of new connections. (Normally, this doesn't provide a notable performance improvement if you have a good thread implementation.) By examining the difference between theConnectionsandThreads_createdstatus variables, you can see how efficient the thread cache is. For details, see Section 5.1.7, “Server Status Variables”.Command-Line Format --thread_concurrency=#Config-File Format thread_concurrencyOption Sets Variable Yes, thread_concurrencyVariable Name thread_concurrencyVariable Scope Global Dynamic Variable No Permitted Values Type numericDefault 10Range 1-512This variable is specific to Solaris systems, for which mysqld invokes the
thr_setconcurrency()with the variable value. This function enables applications to give the threads system a hint about the desired number of threads that should be run at the same time.Command-Line Format --thread_handling=nameConfig-File Format thread_handlingOption Sets Variable Yes, thread_handlingVariable Name thread_handlingVariable Scope Global Dynamic Variable No The thread-handling model. The allowable values are
no-threads(the server uses one thread) andone-thread-per-connection(the server uses one thread to handle each client connection).no-threadsis useful for debugging under Linux; see MySQL Internals: Porting.Command-Line Format --thread_stack=#Config-File Format thread_stackOption Sets Variable Yes, thread_stackVariable Name thread_stackVariable Scope Global Dynamic Variable No Permitted Values Platform Bit Size 32Type numericDefault 196608Range 131072-4294967295Block Size 1024Permitted Values Platform Bit Size 64Type numericDefault 262144Range 131072-18446744073709547520Block Size 1024The stack size for each thread. Many of the limits detected by the
crash-metest are dependent on this value. See Section 7.1.3, “The MySQL Benchmark Suite”. The default of 192KB (256KB for 64-bit systems) is large enough for normal operation. If the thread stack size is too small, it limits the complexity of the SQL statements that the server can handle, the recursion depth of stored procedures, and other memory-consuming actions.This variable is unused.
Command-Line Format --default_time_zone=stringConfig-File Format default_time_zoneVariable Name time_zoneVariable Scope Both Dynamic Variable Yes Permitted Values Type stringThe current time zone. This variable is used to initialize the time zone for each client that connects. By default, the initial value of this is
'SYSTEM'(which means, “use the value ofsystem_time_zone”). The value can be specified explicitly at server startup with the--default-time-zoneoption. See Section 9.6, “MySQL Server Time Zone Support”.Command-Line Format --timed_mutexesConfig-File Format timed_mutexesOption Sets Variable Yes, timed_mutexesVariable Name timed_mutexesVariable Scope Global Dynamic Variable Yes Permitted Values Type booleanDefault OFFThis variable controls whether
InnoDBmutexes are timed. If this variable is set to 0 orOFF(the default), mutex timing is disabled. If the variable is set to 1 orON, mutex timing is enabled. With timing enabled, theos_wait_timesvalue in the output fromSHOW ENGINE INNODB MUTEXindicates the amount of time (in ms) spent in operating system waits. Otherwise, the value is 0.Command-Line Format --tmp_table_size=#Config-File Format tmp_table_sizeOption Sets Variable Yes, tmp_table_sizeVariable Name tmp_table_sizeVariable Scope Both Dynamic Variable Yes Permitted Values Type numericDefault system dependentRange 1024-4294967295The maximum size of internal in-memory temporary tables. (The actual limit is determined as the minimum of
tmp_table_sizeandmax_heap_table_size.) If an in-memory temporary table exceeds the limit, MySQL automatically converts it to an on-diskMyISAMtable. Increase the value oftmp_table_size(andmax_heap_table_sizeif necessary) if you do many advancedGROUP BYqueries and you have lots of memory. This variable does not apply to user-createdMEMORYtables.You can compare the number of internal on-disk temporary tables created to the total number of internal temporary tables created by comparing the values of the
Created_tmp_disk_tablesandCreated_tmp_tablesvariables.See also Section 7.5.10, “How MySQL Uses Internal Temporary Tables”.
Command-Line Format --tmpdir=nameConfig-File Format tmpdirOption Sets Variable Yes, tmpdirVariable Name tmpdirVariable Scope Global Dynamic Variable No Permitted Values Type filenameThe directory used for temporary files and temporary tables. This variable can be set to a list of several paths that are used in round-robin fashion. Paths should be separated by colon characters (“
:”) on Unix and semicolon characters (“;”) on Windows, NetWare, and OS/2.The multiple-directory feature can be used to spread the load between several physical disks. If the MySQL server is acting as a replication slave, you should not set
tmpdirto point to a directory on a memory-based file system or to a directory that is cleared when the server host restarts. A replication slave needs some of its temporary files to survive a machine restart so that it can replicate temporary tables orLOAD DATA INFILEoperations. If files in the temporary file directory are lost when the server restarts, replication fails. You can set the slave's temporary directory using theslave_load_tmpdirvariable. In that case, the slave won't use the generaltmpdirvalue and you can settmpdirto a nonpermanent location.Command-Line Format --transaction_alloc_block_size=#Config-File Format transaction_alloc_block_sizeOption Sets Variable Yes, transaction_alloc_block_sizeVariable Name transaction_alloc_block_sizeVariable Scope Both Dynamic Variable Yes Permitted Values Platform Bit Size 32Type numericDefault 8192Range 1024-4294967295Block Size 1024Permitted Values Platform Bit Size 64Type numericDefault 8192Range 1024-18446744073709547520Block Size 1024The amount in bytes by which to increase a per-transaction memory pool which needs memory. See the description of
transaction_prealloc_size.Command-Line Format --transaction_prealloc_size=#Config-File Format transaction_prealloc_sizeOption Sets Variable Yes, transaction_prealloc_sizeVariable Name transaction_prealloc_sizeVariable Scope Both Dynamic Variable Yes Permitted Values Platform Bit Size 32Type numericDefault 4096Range 1024-4294967295Block Size 1024Permitted Values Platform Bit Size 64Type numericDefault 4096Range 1024-18446744073709547520Block Size 1024There is a per-transaction memory pool from which various transaction-related allocations take memory. The initial size of the pool in bytes is
transaction_prealloc_size. For every allocation that cannot be satisfied from the pool because it has insufficient memory available, the pool is increased bytransaction_alloc_block_sizebytes. When the transaction ends, the pool is truncated totransaction_prealloc_sizebytes.By making
transaction_prealloc_sizesufficiently large to contain all statements within a single transaction, you can avoid manymalloc()calls.Variable Name tx_isolationVariable Scope Both Dynamic Variable Yes Permitted Values Type enumerationDefault REPEATABLE-READValid Values READ-UNCOMMITTED,READ-COMMITTED,REPEATABLE-READ,SERIALIZABLEThe default transaction isolation level. Defaults to
REPEATABLE-READ.This variable is set by the
SET TRANSACTION ISOLATION LEVELstatement. See Section 12.4.6, “SET TRANSACTIONSyntax”. If you settx_isolationdirectly to an isolation level name that contains a space, the name should be enclosed within quotes, with the space replaced by a dash. For example:SET tx_isolation = 'READ-COMMITTED';
Command-Line Format --updatable_views_with_limit=#Config-File Format updatable_views_with_limitOption Sets Variable Yes, updatable_views_with_limitVariable Name updatable_views_with_limitVariable Scope Both Dynamic Variable Yes Permitted Values Type booleanDefault 1This variable controls whether updates to a view can be made when the view does not contain all columns of the primary key defined in the underlying table, if the update statement contains a
LIMITclause. (Such updates often are generated by GUI tools.) An update is anUPDATEorDELETEstatement. Primary key here means aPRIMARY KEY, or aUNIQUEindex in which no column can containNULL.The variable can have two values:
1orYES: Issue a warning only (not an error message). This is the default value.0orNO: Prohibit the update.
The version number for the server.
The configure script has a
--with-commentoption that allows a comment to be specified when building MySQL. This variable contains the value of that comment.The type of machine or architecture on which MySQL was built.
Variable Name version_compile_osVariable Scope Global Dynamic Variable No Permitted Values Type stringThe type of operating system on which MySQL was built.
Command-Line Format --wait_timeout=#Config-File Format wait_timeoutOption Sets Variable Yes, wait_timeoutVariable Name wait_timeoutVariable Scope Both Dynamic Variable Yes Permitted Values Type numericDefault 28800Range 1-31536000Permitted Values Type (windows) numericDefault 28800Range 1-2147483The number of seconds the server waits for activity on a noninteractive connection before closing it. This timeout applies only to TCP/IP and Unix socket file connections, not to connections made via named pipes, or shared memory.
On thread startup, the session
wait_timeoutvalue is initialized from the globalwait_timeoutvalue or from the globalinteractive_timeoutvalue, depending on the type of client (as defined by theCLIENT_INTERACTIVEconnect option tomysql_real_connect()). See alsointeractive_timeout.
MySQL Enterprise Expert use of server system variables is part of the service offered by the MySQL Enterprise Monitor. To subscribe, see http://www.mysql.com/products/enterprise/advisors.html.
Several system variables exist only as session variables. These
cannot be set at server startup but can be assigned values at
runtime using the
SET
statement (except for those that are read only). Most of them are
not displayed by SHOW VARIABLES,
but you can obtain their values using
SELECT. This section describes the
session system variables. For information about setting or
displaying their values, see
Section 5.1.6, “Using System Variables”. For example:
mysql> SELECT @@autocommit;
+--------------+
| @@autocommit |
+--------------+
| 1 |
+--------------+
The lettercase of these variables does not matter.
The following table lists the system variables that have only session scope:
Table 5.3. Session System Variable Summary
| Name | Cmd-Line | Option file | System Var | Dynamic |
|---|---|---|---|---|
| autocommit | Yes | Yes | ||
| big-tables | Yes | Yes | ||
| - Variable: big_tables | Yes | Yes | ||
| error_count | Yes | No | ||
| foreign_key_checks | Yes | Yes | ||
| identity | Yes | Yes | ||
| insert_id | Yes | Yes | ||
| last_insert_id | Yes | Yes | ||
| profiling | Yes | Yes | ||
| pseudo_thread_id | Yes | Yes | ||
| rand_seed1 | Yes | Yes | ||
| rand_seed2 | Yes | Yes | ||
| sql_auto_is_null | Yes | Yes | ||
| sql_big_selects | Yes | Yes | ||
| sql_big_tables | Yes | Yes | ||
| sql_buffer_result | Yes | Yes | ||
| sql_log_bin | Yes | Yes | ||
| sql_log_off | Yes | Yes | ||
| sql_log_update | Yes | Yes | ||
| sql_notes | Yes | Yes | ||
| sql_quote_show_create | Yes | Yes | ||
| sql_safe_updates | Yes | Yes | ||
| sql_warnings | Yes | Yes |
The autocommit mode. If set to 1, all changes to a table take effect immediately. If set to 0, you must use
COMMITto accept a transaction orROLLBACKto cancel it. By default, client connections begin withautocommitset to 1. If you changeautocommitmode from 0 to 1, MySQL performs an automaticCOMMITof any open transaction. Another way to begin a transaction is to use aSTART TRANSACTIONorBEGINstatement. See Section 12.4.1, “START TRANSACTION,COMMIT, andROLLBACKSyntax”.If set to 1, all temporary tables are stored on disk rather than in memory. This is a little slower, but the error
The tabledoes not occur fortbl_nameis fullSELECToperations that require a large temporary table. The default value for a new connection is 0 (use in-memory temporary tables). Normally, you should never need to set this variable, because in-memory tables are automatically converted to disk-based tables as required.Note
This variable was formerly named
sql_big_tables.The number of errors that resulted from the last statement that generated messages. This variable is read only. See Section 12.5.5.18, “
SHOW ERRORSSyntax”.If set to 1 (the default), foreign key constraints for
InnoDBtables are checked. If set to 0, they are ignored. Disabling foreign key checking can be useful for reloadingInnoDBtables in an order different from that required by their parent/child relationships. See Section 13.6.4.4, “FOREIGN KEYConstraints”.Setting
foreign_key_checksto 0 also affects data definition statements:DROP SCHEMAdrops a schema even if it contains tables that have foreign keys that are referred to by tables outside the schema, andDROP TABLEdrops tables that have foreign keys that are referred to by other tables.Note
Setting
foreign_key_checksto 1 does not trigger a scan of the existing table data. Therefore, rows added to the table whileforeign_key_checks = 0will not be verified for consistency.This variable is a synonym for the
last_insert_idvariable. It exists for compatibility with other database systems. You can read its value withSELECT @@identity, and set it usingSET identity.The value to be used by the following
INSERTorALTER TABLEstatement when inserting anAUTO_INCREMENTvalue. This is mainly used with the binary log.The value to be returned from
LAST_INSERT_ID(). This is stored in the binary log when you useLAST_INSERT_ID()in a statement that updates a table. Setting this variable does not update the value returned by themysql_insert_id()C API function.If set to 0 (the default), statement profiling is disabled. If set to 1, statement profiling is enabled and the
SHOW PROFILESandSHOW PROFILEstatements provide access to profiling information. See Section 12.5.5.32, “SHOW PROFILESSyntax”.The number of statements for which to maintain profiling information if
profilingis enabled. The default value is 15. The maximum value is 100. Setting the value to 0 effectively disables profiling. See Section 12.5.5.32, “SHOW PROFILESSyntax”.The
rand_seed1andrand_seed2variables exist as session variables only, and can be set but not read. The variables — but not their values — are shown in the output ofSHOW VARIABLES.The purpose of these variables is to support replication of the
RAND()function. For statements that invokeRAND(), the master passes two values to the slave, where they are used to seed the random number generator. The slave uses these values to set the session variablesrand_seed1andrand_seed2so thatRAND()on the slave generates the same value as on the master.See the description for
rand_seed1.If this variable is set to 1 (the default), then after a statement that successfully inserts an automatically generated
AUTO_INCREMENTvalue, you can find that value by issuing a statement of the following form:SELECT * FROM
tbl_nameWHEREauto_colIS NULLIf the statement returns a row, the value returned is the same as if you invoked the
LAST_INSERT_ID()function. For details, including the return value after a multiple-row insert, see Section 11.11.3, “Information Functions”. If noAUTO_INCREMENTvalue was successfully inserted, theSELECTstatement returns no row.The behavior of retrieving an
AUTO_INCREMENTvalue by using anIS NULLcomparison is used by some ODBC programs, such as Access. See Section 21.1.7.1.1, “Obtaining Auto-Increment Values”. This behavior can be disabled by settingsql_auto_is_nullto 0.If set to 0, MySQL aborts
SELECTstatements that are likely to take a very long time to execute (that is, statements for which the optimizer estimates that the number of examined rows exceeds the value ofmax_join_size). This is useful when an inadvisableWHEREstatement has been issued. The default value for a new connection is 1, which allows allSELECTstatements.If you set the
max_join_sizesystem variable to a value other thanDEFAULT,sql_big_selectsis set to 0.If set to 1,
sql_buffer_resultforces results fromSELECTstatements to be put into temporary tables. This helps MySQL free the table locks early and can be beneficial in cases where it takes a long time to send results to the client. The default value is 0.If set to 0, no logging is done to the binary log for the client. The client must have the
SUPERprivilege to set this option. The default value is 1.If set to 1, no logging is done to the general query log for this client. The client must have the
SUPERprivilege to set this option. The default value is 0.This variable is deprecated, and is mapped to
sql_log_bin. It was removed in MySQL 5.5.3.If set to 1 (the default), warnings of
Notelevel are recorded. If set to 0,Notewarnings are suppressed. mysqldump includes output to set this variable to 0 so that reloading the dump file does not produce warnings for events that do not affect the integrity of the reload operation.If set to 1 (the default), the server quotes identifiers for
SHOW CREATE TABLEandSHOW CREATE DATABASEstatements. If set to 0, quoting is disabled. This option is enabled by default so that replication works for identifiers that require quoting. See Section 12.5.5.12, “SHOW CREATE TABLESyntax”, and Section 12.5.5.8, “SHOW CREATE DATABASESyntax”.If set to 1, MySQL aborts
UPDATEorDELETEstatements that do not use a key in theWHEREclause or aLIMITclause. This makes it possible to catchUPDATEorDELETEstatements where keys are not used properly and that would probably change or delete a large number of rows. The default value is 0.This variable controls whether single-row
INSERTstatements produce an information string if warnings occur. The default is 0. Set the value to 1 to produce an information string.timestamp = {timestamp_value| DEFAULT}Set the time for this client. This is used to get the original timestamp if you use the binary log to restore rows.
timestamp_valueshould be a Unix epoch timestamp, not a MySQL timestamp.SET timestampaffects the value returned byNOW()but not bySYSDATE(). This means that timestamp settings in the binary log have no effect on invocations ofSYSDATE(). The server can be started with the--sysdate-is-nowoption to causeSYSDATE()to be an alias forNOW(), in which caseSET timestampaffects both functions.If set to 1 (the default), uniqueness checks for secondary indexes in
InnoDBtables are performed. If set to 0, storage engines are allowed to assume that duplicate keys are not present in input data. If you know for certain that your data does not contain uniqueness violations, you can set this to 0 to speed up large table imports toInnoDB.Note that setting this variable to 0 does not require storage engines to ignore duplicate keys. An engine is still allowed to check for them and issue duplicate-key errors if it detects them.
The number of errors, warnings, and notes that resulted from the last statement that generated messages. This variable is read only. See Section 12.5.5.41, “
SHOW WARNINGSSyntax”.
The MySQL server maintains many system variables that indicate how
it is configured. Section 5.1.4, “Server System Variables”,
describes the meaning of these variables. Each system variable has
a default value. System variables can be set at server startup
using options on the command line or in an option file. Most of
them can be changed dynamically while the server is running by
means of the
SET
statement, which enables you to modify operation of the server
without having to stop and restart it. You can refer to system
variable values in expressions.
The server maintains two kinds of system variables. Global variables affect the overall operation of the server. Session variables affect its operation for individual client connections. A given system variable can have both a global and a session value. Global and session system variables are related as follows:
When the server starts, it initializes all global variables to their default values. These defaults can be changed by options specified on the command line or in an option file. (See Section 4.2.3, “Specifying Program Options”.)
The server also maintains a set of session variables for each client that connects. The client's session variables are initialized at connect time using the current values of the corresponding global variables. For example, the client's SQL mode is controlled by the session
sql_modevalue, which is initialized when the client connects to the value of the globalsql_modevalue.
System variable values can be set globally at server startup by
using options on the command line or in an option file. When you
use a startup option to set a variable that takes a numeric value,
the value can be given with a suffix of K,
M, or G (either uppercase or
lowercase) to indicate a multiplier of 1024,
10242 or
10243; that is, units of kilobytes,
megabytes, or gigabytes, respectively. Thus, the following command
starts the server with a query cache size of 16 megabytes and a
maximum packet size of one gigabyte:
mysqld --query_cache_size=16M --max_allowed_packet=1G
Within an option file, those variables are set like this:
[mysqld] query_cache_size=16M max_allowed_packet=1G
The lettercase of suffix letters does not matter;
16M and 16m are equivalent,
as are 1G and 1g.
If you want to restrict the maximum value to which a system
variable can be set at runtime with the
SET
statement, you can specify this maximum by using an option of the
form
--maximum-
at server startup. For example, to prevent the value of
var_name=valuequery_cache_size from being
increased to more than 32MB at runtime, use the option
--maximum-query_cache_size=32M.
Many system variables are dynamic and can be changed while the
server runs by using the
SET
statement. For a list, see
Section 5.1.6.2, “Dynamic System Variables”. To change a system
variable with
SET, refer
to it as var_name, optionally preceded
by a modifier:
To indicate explicitly that a variable is a global variable, precede its name by
GLOBALor@@global.. TheSUPERprivilege is required to set global variables.To indicate explicitly that a variable is a session variable, precede its name by
SESSION,@@session., or@@. Setting a session variable requires no special privilege, but a client can change only its own session variables, not those of any other client.LOCALand@@local.are synonyms forSESSIONand@@session..If no modifier is present,
SETchanges the session variable.
A SET
statement can contain multiple variable assignments, separated by
commas. If you set several system variables, the most recent
GLOBAL or SESSION modifier
in the statement is used for following variables that have no
modifier specified.
Examples:
SET sort_buffer_size=10000; SET @@local.sort_buffer_size=10000; SET GLOBAL sort_buffer_size=1000000, SESSION sort_buffer_size=1000000; SET @@sort_buffer_size=1000000; SET @@global.sort_buffer_size=1000000, @@local.sort_buffer_size=1000000;
The @@
syntax for system variables is supported for compatibility with
some other database systems.
var_name
If you change a session system variable, the value remains in effect until your session ends or until you change the variable to a different value. The change is not visible to other clients.
If you change a global system variable, the value is remembered
and used for new connections until the server restarts. (To make a
global system variable setting permanent, you should set it in an
option file.) The change is visible to any client that accesses
that global variable. However, the change affects the
corresponding session variable only for clients that connect after
the change. The global variable change does not affect the session
variable for any client that is currently connected (not even that
of the client that issues the
SET GLOBAL
statement).
To prevent incorrect usage, MySQL produces an error if you use
SET GLOBAL
with a variable that can only be used with
SET SESSION
or if you do not specify GLOBAL (or
@@global.) when setting a global variable.
To set a SESSION variable to the
GLOBAL value or a GLOBAL
value to the compiled-in MySQL default value, use the
DEFAULT keyword. For example, the following two
statements are identical in setting the session value of
max_join_size to the global
value:
SET max_join_size=DEFAULT; SET @@session.max_join_size=@@global.max_join_size;
Not all system variables can be set to DEFAULT.
In such cases, use of DEFAULT results in an
error.
You can refer to the values of specific global or sesson system
variables in expressions by using one of the
@@-modifiers. For example, you can retrieve
values in a SELECT statement like
this:
SELECT @@global.sql_mode, @@session.sql_mode, @@sql_mode;
When you refer to a system variable in an expression as
@@ (that is,
when you do not specify var_name@@global. or
@@session.), MySQL returns the session value if
it exists and the global value otherwise. (This differs from
SET @@, which always refers to
the session value.)
var_name =
value
Note
Some variables displayed by SHOW VARIABLES
may not be available using SELECT
@@ syntax; an
var_nameUnknown system variable occurs. As a
workaround in such cases, you can use SHOW VARIABLES
LIKE '.
var_name'
Suffixes for specifying a value multiplier can be used when
setting a variable at server startup, but not to set the value
with SET at
runtime. On the other hand, with
SET you can
assign a variable's value using an expression, which is not true
when you set a variable at server startup. For example, the first
of the following lines is legal at server startup, but the second
is not:
shell>mysql --max_allowed_packet=16Mshell>mysql --max_allowed_packet=16*1024*1024
Conversely, the second of the following lines is legal at runtime, but the first is not:
mysql>SET GLOBAL max_allowed_packet=16M;mysql>SET GLOBAL max_allowed_packet=16*1024*1024;
Note
Some system variables can be enabled with the
SET
statement by setting them to ON or
1, or disabled by setting them to
OFF or 0. However, to set
such a variable on the command line or in an option file, you
must set it to 1 or 0;
setting it to ON or OFF
will not work. For example, on the command line,
--delay_key_write=1 works but
--delay_key_write=ON does not.
To display system variable names and values, use the
SHOW VARIABLES statement:
mysql> SHOW VARIABLES;
+---------------------------------+-----------------------------------+
| Variable_name | Value |
+---------------------------------+-----------------------------------+
| auto_increment_increment | 1 |
| auto_increment_offset | 1 |
| automatic_sp_privileges | ON |
| back_log | 50 |
| basedir | /home/mysql/ |
| binlog_cache_size | 32768 |
| bulk_insert_buffer_size | 8388608 |
| character_set_client | latin1 |
| character_set_connection | latin1 |
| character_set_database | latin1 |
| character_set_results | latin1 |
| character_set_server | latin1 |
| character_set_system | utf8 |
| character_sets_dir | /home/mysql/share/mysql/charsets/ |
| collation_connection | latin1_swedish_ci |
| collation_database | latin1_swedish_ci |
| collation_server | latin1_swedish_ci |
...
| innodb_additional_mem_pool_size | 1048576 |
| innodb_autoextend_increment | 8 |
| innodb_buffer_pool_size | 8388608 |
| innodb_checksums | ON |
| innodb_commit_concurrency | 0 |
| innodb_concurrency_tickets | 500 |
| innodb_data_file_path | ibdata1:10M:autoextend |
| innodb_data_home_dir | |
...
| version | 5.1.6-alpha-log |
| version_comment | Source distribution |
| version_compile_machine | i686 |
| version_compile_os | suse-linux |
| wait_timeout | 28800 |
+---------------------------------+-----------------------------------+
With a LIKE clause, the statement
displays only those variables that match the pattern. To obtain a
specific variable name, use a LIKE
clause as shown:
SHOW VARIABLES LIKE 'max_join_size'; SHOW SESSION VARIABLES LIKE 'max_join_size';
To get a list of variables whose name match a pattern, use the
“%” wildcard character in a
LIKE clause:
SHOW VARIABLES LIKE '%size%'; SHOW GLOBAL VARIABLES LIKE '%size%';
Wildcard characters can be used in any position within the pattern
to be matched. Strictly speaking, because
“_” is a wildcard that matches any
single character, you should escape it as
“\_” to match it literally. In
practice, this is rarely necessary.
For SHOW VARIABLES, if you specify
neither GLOBAL nor SESSION,
MySQL returns SESSION values.
The reason for requiring the GLOBAL keyword
when setting GLOBAL-only variables but not when
retrieving them is to prevent problems in the future. If we were
to remove a SESSION variable that has the same
name as a GLOBAL variable, a client with the
SUPER privilege might accidentally
change the GLOBAL variable rather than just the
SESSION variable for its own connection. If we
add a SESSION variable with the same name as a
GLOBAL variable, a client that intends to
change the GLOBAL variable might find only its
own SESSION variable changed.
A structured variable differs from a regular system variable in two respects:
Its value is a structure with components that specify server parameters considered to be closely related.
There might be several instances of a given type of structured variable. Each one has a different name and refers to a different resource maintained by the server.
MySQL 5.5 supports one structured variable type, which specifies parameters governing the operation of key caches. A key cache structured variable has these components:
This section describes the syntax for referring to structured
variables. Key cache variables are used for syntax examples, but
specific details about how key caches operate are found
elsewhere, in Section 7.4.5, “The MyISAM Key Cache”.
To refer to a component of a structured variable instance, you
can use a compound name in
instance_name.component_name format.
Examples:
hot_cache.key_buffer_size hot_cache.key_cache_block_size cold_cache.key_cache_block_size
For each structured system variable, an instance with the name
of default is always predefined. If you refer
to a component of a structured variable without any instance
name, the default instance is used. Thus,
default.key_buffer_size and
key_buffer_size both refer to
the same system variable.
Structured variable instances and components follow these naming rules:
For a given type of structured variable, each instance must have a name that is unique within variables of that type. However, instance names need not be unique across structured variable types. For example, each structured variable has an instance named
default, sodefaultis not unique across variable types.The names of the components of each structured variable type must be unique across all system variable names. If this were not true (that is, if two different types of structured variables could share component member names), it would not be clear which default structured variable to use for references to member names that are not qualified by an instance name.
If a structured variable instance name is not legal as an unquoted identifier, refer to it as a quoted identifier using backticks. For example,
hot-cacheis not legal, but`hot-cache`is.global,session, andlocalare not legal instance names. This avoids a conflict with notation such as@@global.for referring to nonstructured system variables.var_name
Currently, the first two rules have no possibility of being violated because the only structured variable type is the one for key caches. These rules will assume greater significance if some other type of structured variable is created in the future.
With one exception, you can refer to structured variable components using compound names in any context where simple variable names can occur. For example, you can assign a value to a structured variable using a command-line option:
shell> mysqld --hot_cache.key_buffer_size=64K
In an option file, use this syntax:
[mysqld] hot_cache.key_buffer_size=64K
If you start the server with this option, it creates a key cache
named hot_cache with a size of 64KB in
addition to the default key cache that has a default size of
8MB.
Suppose that you start the server as follows:
shell>mysqld --key_buffer_size=256K \--extra_cache.key_buffer_size=128K \--extra_cache.key_cache_block_size=2048
In this case, the server sets the size of the default key cache
to 256KB. (You could also have written
--default.key_buffer_size=256K.) In addition,
the server creates a second key cache named
extra_cache that has a size of 128KB, with
the size of block buffers for caching table index blocks set to
2048 bytes.
The following example starts the server with three different key caches having sizes in a 3:1:1 ratio:
shell>mysqld --key_buffer_size=6M \--hot_cache.key_buffer_size=2M \--cold_cache.key_buffer_size=2M
Structured variable values may be set and retrieved at runtime
as well. For example, to set a key cache named
hot_cache to a size of 10MB, use either of
these statements:
mysql>SET GLOBAL hot_cache.key_buffer_size = 10*1024*1024;mysql>SET @@global.hot_cache.key_buffer_size = 10*1024*1024;
To retrieve the cache size, do this:
mysql> SELECT @@global.hot_cache.key_buffer_size;
However, the following statement does not work. The variable is
not interpreted as a compound name, but as a simple string for a
LIKE pattern-matching operation:
mysql> SHOW GLOBAL VARIABLES LIKE 'hot_cache.key_buffer_size';
This is the exception to being able to use structured variable names anywhere a simple variable name may occur.
Many server system variables are dynamic and can be set at
runtime using SET
GLOBAL or
SET
SESSION. You can also obtain their values using
SELECT. See
Section 5.1.6, “Using System Variables”.
The following table shows the full list of all dynamic system
variables. The last column indicates for each variable whether
GLOBAL or SESSION (or
both) apply. The table also lists session options that can be
set with the
SET
statement. Section 5.1.5, “Session System Variables”, discusses
these options.
Variables that have a type of “string” take a
string value. Variables that have a type of
“numeric” take a numeric value. Variables that have
a type of “boolean” can be set to 0, 1,
ON or OFF. (If you set
them on the command line or in an option file, use the numeric
values.) Variables that are marked as “enumeration”
normally should be set to one of the available values for the
variable, but can also be set to the number that corresponds to
the desired enumeration value. For enumerated system variables,
the first enumeration value corresponds to 0. This differs from
ENUM columns, for which the first
enumeration value corresponds to 1.
Table 5.4. Dynamic Variable Summary
MySQL Enterprise Improper configuration of system variables can adversely affect performance and security. The MySQL Enterprise Monitor continually monitors system variables and provides expert advice about appropriate settings. For more information, see http://www.mysql.com/products/enterprise/advisors.html.
The server maintains many status variables that provide
information about its operation. You can view these variables and
their values by using the SHOW [GLOBAL | SESSION]
STATUS statement (see Section 12.5.5.36, “SHOW STATUS Syntax”).
The optional GLOBAL keyword aggregates the
values over all connections, and SESSION shows
the values for the current connection.
mysql> SHOW GLOBAL STATUS;
+-----------------------------------+------------+
| Variable_name | Value |
+-----------------------------------+------------+
| Aborted_clients | 0 |
| Aborted_connects | 0 |
| Bytes_received | 155372598 |
| Bytes_sent | 1176560426 |
...
| Connections | 30023 |
| Created_tmp_disk_tables | 0 |
| Created_tmp_files | 3 |
| Created_tmp_tables | 2 |
...
| Threads_created | 217 |
| Threads_running | 88 |
| Uptime | 1389872 |
+-----------------------------------+------------+
The following table lists all available server status variables:
Table 5.5. Status Variable Summary
Many status variables are reset to 0 by the FLUSH
STATUS statement.
MySQL Enterprise For expert advice on using status variables, subscribe to the MySQL Enterprise Monitor. For more information, see http://www.mysql.com/products/enterprise/advisors.html.
The status variables have the following meanings. Variables with no version indicated were already present prior to MySQL 5.5. For information regarding their implementation history, see MySQL 5.4 Reference Manual.
The number of connections that were aborted because the client died without closing the connection properly. See Section B.5.2.11, “Communication Errors and Aborted Connections”.
The number of failed attempts to connect to the MySQL server. See Section B.5.2.11, “Communication Errors and Aborted Connections”.
The number of transactions that used the temporary binary log cache but that exceeded the value of
binlog_cache_sizeand used a temporary file to store statements from the transaction.The number of transactions that used the temporary binary log cache.
The number of bytes received from all clients.
The number of bytes sent to all clients.
The
Com_statement counter variables indicate the number of times eachxxxxxxstatement has been executed. There is one status variable for each type of statement. For example,Com_deleteandCom_insertcountDELETEandINSERTstatements, respectively. However, if a query result is returned from query cache, the server increments theQcache_hitsstatus variable, notCom_select. See Section 7.5.5.4, “Query Cache Status and Maintenance”.All of the
Com_stmt_variables are increased even if a prepared statement argument is unknown or an error occurred during execution. In other words, their values correspond to the number of requests issued, not to the number of requests successfully completed.xxxThe
Com_stmt_status variables are as follows:xxxCom_stmt_prepareCom_stmt_executeCom_stmt_fetchCom_stmt_send_long_dataCom_stmt_resetCom_stmt_close
Those variables stand for prepared statement commands. Their names refer to the
COM_command set used in the network layer. In other words, their values increase whenever prepared statement API calls such as mysql_stmt_prepare(), mysql_stmt_execute(), and so forth are executed. However,xxxCom_stmt_prepare,Com_stmt_executeandCom_stmt_closealso increase forPREPARE,EXECUTE, orDEALLOCATE PREPARE, respectively. Additionally, the values of the older statement counter variablesCom_prepare_sql,Com_execute_sql, andCom_dealloc_sqlincrease for thePREPARE,EXECUTE, andDEALLOCATE PREPAREstatements.Com_stmt_fetchstands for the total number of network round-trips issued when fetching from cursors.Com_stmt_reprepareindicated the number of times statements were automatically reprepared by the server after metadata changes to tables or views referred to by the statement. A reprepare operation incrementsCom_stmt_reprepareis incremented, and alsoCom_stmt_prepare.Whether the client connection uses compression in the client/server protocol.
The number of connection attempts (successful or not) to the MySQL server.
The number of internal on-disk temporary tables created by the server while executing statements.
If an internal temporary table is created initially as an in-memory table but becomes too large, MySQL automatically converts it to an on-disk table. The maximum size for in-memory temporary tables is the minimum of the
tmp_table_sizeandmax_heap_table_sizevalues. IfCreated_tmp_disk_tablesis large, you may want to increase thetmp_table_sizeormax_heap_table_sizevalues. value to lessen the likelihood that internal temporary tables in memory will be converted to on-disk tables.You can compare the number of internal on-disk temporary tables created to the total number of internal temporary tables created by comparing the values of the
Created_tmp_disk_tablesandCreated_tmp_tablesvariables.See also Section 7.5.10, “How MySQL Uses Internal Temporary Tables”.
How many temporary files mysqld has created.
The number of internal temporary tables created by the server while executing statements.
You can compare the number of internal on-disk temporary tables created to the total number of internal temporary tables created by comparing the values of the
Created_tmp_disk_tablesandCreated_tmp_tablesvariables.See also Section 7.5.10, “How MySQL Uses Internal Temporary Tables”.
Each invocation of the
SHOW STATUSstatement uses an internal temporary table and increments the globalCreated_tmp_tablesvalue.The number of rows written with
INSERT DELAYEDfor which some error occurred (probablyduplicate key).The number of
INSERT DELAYEDhandler threads in use.The number of
INSERT DELAYEDrows written.The number of executed
FLUSHstatements.The number of internal
COMMITstatements.The number of times that rows have been deleted from tables.
A counter for the prepare phase of two-phase commit operations.
The number of times the first entry in an index was read. If this value is high, it suggests that the server is doing a lot of full index scans; for example,
SELECT col1 FROM foo, assuming thatcol1is indexed.The number of requests to read a row based on a key. If this value is high, it is a good indication that your tables are properly indexed for your queries.
The number of requests to read the next row in key order. This value is incremented if you are querying an index column with a range constraint or if you are doing an index scan.
The number of requests to read the previous row in key order. This read method is mainly used to optimize
ORDER BY ... DESC.The number of requests to read a row based on a fixed position. This value is high if you are doing a lot of queries that require sorting of the result. You probably have a lot of queries that require MySQL to scan entire tables or you have joins that don't use keys properly.
The number of requests to read the next row in the data file. This value is high if you are doing a lot of table scans. Generally this suggests that your tables are not properly indexed or that your queries are not written to take advantage of the indexes you have.
The number of requests for a storage engine to perform a rollback operation.
The number of requests for a storage engine to place a savepoint.
The number of requests for a storage engine to roll back to a savepoint.
The number of requests to update a row in a table.
The number of requests to insert a row in a table.
The number of pages containing data (dirty or clean).
Innodb_buffer_pool_pages_dirtyThe number of pages currently dirty.
Innodb_buffer_pool_pages_flushedThe number of buffer pool page-flush requests.
The number of free pages.
Innodb_buffer_pool_pages_latchedThe number of latched pages in
InnoDBbuffer pool. These are pages currently being read or written or that cannot be flushed or removed for some other reason. Calculation of this variable is expensive, so it is available only when theUNIV_DEBUGsystem is defined at server build time.The number of pages that are busy because they have been allocated for administrative overhead such as row locks or the adaptive hash index. This value can also be calculated as
Innodb_buffer_pool_pages_total–Innodb_buffer_pool_pages_free–Innodb_buffer_pool_pages_data.Innodb_buffer_pool_pages_totalThe total size of the buffer pool, in pages.
The number of pages read into the
InnoDBbuffer pool by the read-ahead background thread.Innodb_buffer_pool_read_ahead_evictedThe number of pages read into the
InnoDBbuffer pool by the read-ahead background thread that were subsequently evicted without having been accessed by queries.Innodb_buffer_pool_read_requestsThe number of logical read requests
InnoDBhas done.The number of logical reads that
InnoDBcould not satisfy from the buffer pool, and had to read directly from the disk.Normally, writes to the
InnoDBbuffer pool happen in the background. However, if it is necessary to read or create a page and no clean pages are available, it is also necessary to wait for pages to be flushed first. This counter counts instances of these waits. If the buffer pool size has been set properly, this value should be small.Innodb_buffer_pool_write_requestsThe number writes done to the
InnoDBbuffer pool.The number of
fsync()operations so far.The current number of pending
fsync()operations.The current number of pending reads.
The current number of pending writes.
The amount of data read since the server was started.
The total number of data reads.
The total number of data writes.
The amount of data written so far, in bytes.
The number of pages that have been written for doublewrite operations. See Section 13.6.11.1, “
InnoDBDisk I/O”.The number of doublewrite operations that have been performed. See Section 13.6.11.1, “
InnoDBDisk I/O”.Indicates whether the server was built with atomic instructions. This variable was added in in MySQL 5.4.2.
Indicates whether the server was built with atomic instructions. This variable was renamed to
Innodb_have_atomic_builtinsin MySQL 5.4.2.Indicates whether the built-in
InnoDBmemory manager is used. (ONmeans it is used,OFFmeans it is not.) This variable was removed in in MySQL 5.4.2.The number of times that the log buffer was too small and a wait was required for it to be flushed before continuing.
The number of log write requests.
The number of physical writes to the log file.
The number of
fsync()writes done to the log file.The number of pending log file
fsync()operations.The number of pending log file writes.
The number of bytes written to the log file.
The compiled-in
InnoDBpage size (default 16KB). Many values are counted in pages; the page size allows them to be easily converted to bytes.The number of pages created.
The number of pages read.
The number of pages written.
The number of row locks currently being waited for.
The total time spent in acquiring row locks, in milliseconds.
The average time to acquire a row lock, in milliseconds.
The maximum time to acquire a row lock, in milliseconds.
The number of times a row lock had to be waited for.
The number of rows deleted from
InnoDBtables.The number of rows inserted into
InnoDBtables.The number of rows read from
InnoDBtables.The number of rows updated in
InnoDBtables.The number of wakeups that should not have occurred. These are wakeups in a condition on a mutex when the condition is not yet met so the thread must go back to sleep. This variable was removed in in MySQL 5.4.2.
The number of key blocks in the key cache that have changed but have not yet been flushed to disk.
The number of unused blocks in the key cache. You can use this value to determine how much of the key cache is in use; see the discussion of
key_buffer_sizein Section 5.1.4, “Server System Variables”.The number of used blocks in the key cache. This value is a high-water mark that indicates the maximum number of blocks that have ever been in use at one time.
The number of requests to read a key block from the cache.
The number of physical reads of a key block from disk. If
Key_readsis large, then yourkey_buffer_sizevalue is probably too small. The cache miss rate can be calculated asKey_reads/Key_read_requests.The number of requests to write a key block to the cache.
The number of physical writes of a key block to disk.
The total cost of the last compiled query as computed by the query optimizer. This is useful for comparing the cost of different query plans for the same query. The default value of 0 means that no query has been compiled yet. The default value is 0.
Last_query_costhas session scope.The
Last_query_costvalue can be computed accurately only for simple “flat” queries, not complex queries such as those with subqueries orUNION. For the latter, the value is set to 0.The maximum number of connections that have been in use simultaneously since the server started.
The number of rows waiting to be written in
INSERT DELAYqueues.The number of files that are open. This count includes regular files opened by the server. It does not include other types of files such as sockets or pipes. Also, the count does not include files that storage engines open using their own internal functions rather than asking the server level to do so.
The number of streams that are open (used mainly for logging).
The number of cached
.frmfiles.The number of tables that are open.
The number of files that have been opened with
my_open()(amysyslibrary function). Parts of the server that open files without using this function do not increment the count.The number of
.frmfiles that have been cached.The number of tables that have been opened. If
Opened_tablesis big, yourtable_open_cachevalue is probably too small.The current number of prepared statements. (The maximum number of statements is given by the
max_prepared_stmt_countsystem variable.)The number of free memory blocks in the query cache.
The amount of free memory for the query cache.
The number of query cache hits.
The number of queries added to the query cache.
The number of queries that were deleted from the query cache because of low memory.
The number of noncached queries (not cacheable, or not cached due to the
query_cache_typesetting).The number of queries registered in the query cache.
The total number of blocks in the query cache.
The number of statements executed by the server. This variable includes statements executed within stored programs, unlike the
Questionsvariable.The number of statements executed by the server. This includes only statements sent to the server by clients and not statements executed within stored programs, unlike the
Queriesvariable.The number of semisynchronous slaves.
This variable is available only if the master-side semisynchronous replication plugin is installed.
Rpl_semi_sync_master_net_avg_wait_timeThe average time the master waited for a slave reply.
This variable is available only if the master-side semisynchronous replication plugin is installed.
Rpl_semi_sync_master_net_wait_timeThe total time the master waited for slave replies.
This variable is available only if the master-side semisynchronous replication plugin is installed.
Rpl_semi_sync_master_net_waitsThe total number of times the master waited for slave replies.
This variable is available only if the master-side semisynchronous replication plugin is installed.
The number of times the master turned off semisynchronous replication.
This variable is available only if the master-side semisynchronous replication plugin is installed.
The number of commits that were not acknowledged successfully by a slave.
This variable is available only if the master-side semisynchronous replication plugin is installed.
Whether semisynchronous replication currently is operational on the master. The value is 1 if the plugin has been enabled and a commit acknowledgment has not occurred. It is 0 if the plugin is not enabled or the master has fallen back to asynchronous replication due to commit acknowledgment timeout.
This variable is available only if the master-side semisynchronous replication plugin is installed.
Rpl_semi_sync_master_timefunc_failuresThe number of times the master failed when calling time functions such as
gettimeofday().This variable is available only if the master-side semisynchronous replication plugin is installed.
Rpl_semi_sync_master_tx_avg_wait_timeThe average time the master waited for each transaction.
This variable is available only if the master-side semisynchronous replication plugin is installed.
Rpl_semi_sync_master_tx_wait_timeThe total time the master waited for transactions.
This variable is available only if the master-side semisynchronous replication plugin is installed.
The total number of times the master waited for transactions.
This variable is available only if the master-side semisynchronous replication plugin is installed.
Rpl_semi_sync_master_wait_pos_backtraverseThe total number of times the master waited for an event with binary coordinates lower than events waited for previously. This can occur when the order in which transactions start waiting for a reply is different from the order in which their binary log events are written.
This variable is available only if the master-side semisynchronous replication plugin is installed.
Rpl_semi_sync_master_wait_sessionsThe number of sessions currently waiting for slave replies.
This variable is available only if the master-side semisynchronous replication plugin is installed.
The number of commits that were acknowledged successfully by a slave.
This variable is available only if the master-side semisynchronous replication plugin is installed.
Whether semisynchronous replication currently is operational on the slave. This is 1 if the plugin has been enabled and the slave I/O thread is running, 0 otherwise.
This variable is available only if the slave-side semisynchronous replication plugin is installed.
The status of fail-safe replication (not yet implemented).
The number of joins that perform table scans because they do not use indexes. If this value is not 0, you should carefully check the indexes of your tables.
The number of joins that used a range search on a reference table.
The number of joins that used ranges on the first table. This is normally not a critical issue even if the value is quite large.
The number of joins without keys that check for key usage after each row. If this is not 0, you should carefully check the indexes of your tables.
The number of joins that did a full scan of the first table.
Shows the replication heartbeat interval (in seconds) on a replication slave.
The number of temporary tables that the slave SQL thread currently has open.
This counter increments with each replication heartbeat received by a replication slave since the last time that the slave was restarted or reset, or a
CHANGE MASTER TOstatement was issued.The total number of times since startup that the replication slave SQL thread has retried transactions.
This is
ONif this server is a replication slave that is connected to a replication master, and both the I/O and SQL threads are running; otherwise, it isOFF.The number of threads that have taken more than
slow_launch_timeseconds to create.The number of queries that have taken more than
long_query_timeseconds. See Section 5.2.5, “The Slow Query Log”.The number of merge passes that the sort algorithm has had to do. If this value is large, you should consider increasing the value of the
sort_buffer_sizesystem variable.The number of sorts that were done using ranges.
The number of sorted rows.
The number of sorts that were done by scanning the table.
The number of negotiates needed to establish the connection.
The number of accepted SSL connections.
The number of callback cache hits.
The current SSL cipher (empty for non-SSL connections).
The list of possible SSL ciphers.
The number of SSL connection attempts to an SSL-enabled master.
The number of negotiates needed to establish the connection to an SSL-enabled master.
The SSL context verification depth (how many certificates in the chain are tested).
The SSL context verification mode.
The default SSL timeout.
The number of successful SSL connections to the server.
The number of successful slave connections to an SSL-enabled master.
The number of SSL session cache hits.
The number of SSL session cache misses.
The SSL session cache mode.
The number of SSL session cache overflows.
The SSL session cache size.
The number of SSL session cache timeouts.
How many SSL connections were reused from the cache.
Ssl_used_session_cache_entriesHow many SSL session cache entries were used.
The verification depth for replication SSL connections.
The verification mode for replication SSL connections.
The SSL version number.
The number of times that a request for a table lock could be granted immediately.
The number of times that a request for a table lock could not be granted immediately and a wait was needed. If this is high and you have performance problems, you should first optimize your queries, and then either split your table or tables or use replication.
For the memory-mapped implementation of the log that is used by mysqld when it acts as the transaction coordinator for recovery of internal XA transactions, this variable indicates the largest number of pages used for the log since the server started. If the product of
Tc_log_max_pages_usedandTc_log_page_sizeis always significantly less than the log size, the size is larger than necessary and can be reduced. (The size is set by the--log-tc-sizeoption. Currently, this variable is unused: It is unneeded for binary log-based recovery, and the memory-mapped recovery log method is not used unless the number of storage engines capable of two-phase commit is greater than one. (InnoDBis the only applicable engine.)The page size used for the memory-mapped implementation of the XA recovery log. The default value is determined using
getpagesize(). Currently, this variable is unused for the same reasons as described forTc_log_max_pages_used.For the memory-mapped implementation of the recovery log, this variable increments each time the server was not able to commit a transaction and had to wait for a free page in the log. If this value is large, you might want to increase the log size (with the
--log-tc-sizeoption). For binary log-based recovery, this variable increments each time the binary log cannot be closed because there are two-phase commits in progress. (The close operation waits until all such transactions are finished.)The number of threads in the thread cache.
The number of currently open connections.
The number of threads created to handle connections. If
Threads_createdis big, you may want to increase thethread_cache_sizevalue. The cache miss rate can be calculated asThreads_created/Connections.The number of threads that are not sleeping.
The number of seconds that the server has been up.
The number of seconds since the most recent
FLUSH STATUSstatement.
The MySQL server can operate in different SQL modes, and can apply these modes differently for different clients. This capability enables each application to tailor the server's operating mode to its own requirements.
For answers to some questions that are often asked about server SQL modes in MySQL, see Section A.3, “MySQL 5.5 FAQ — Server SQL Mode”.
Modes define what SQL syntax MySQL should support and what kind of data validation checks it should perform. This makes it easier to use MySQL in different environments and to use MySQL together with other database servers.
You can set the default SQL mode by starting
mysqld with the
--sql-mode="
option, or by using
modes"sql-mode="
in modes"my.cnf (Unix operating systems) or
my.ini (Windows).
modes is a list of different modes
separated by comma (“,”)
characters. The default value is empty (no modes set). The
modes value also can be empty
(--sql-mode="" on the command line,
or sql-mode="" in
my.cnf on Unix systems or in
my.ini on Windows) if you want to clear it
explicitly.
You can change the SQL mode at runtime by using a SET
[GLOBAL|SESSION]
sql_mode=' statement to
set the modes'sql_mode system value.
Setting the GLOBAL variable requires the
SUPER privilege and affects the
operation of all clients that connect from that time on. Setting
the SESSION variable affects only the current
client. Any client can change its own session
sql_mode value at any time.
Important
SQL mode and user-defined partitioning. Changing the server SQL mode after creating and inserting data into partitioned tables can cause major changes in the behavior of such tables, and could lead to loss or corruption of data. It is strongly recommended that you never change the SQL mode once you have created tables employing user-defined partitioning.
When replicating partitioned tables, differing SQL modes on master and slave can also lead to problems. For best results, you should always use the same server SQL mode on the master and on the slave.
See Section 17.5, “Restrictions and Limitations on Partitioning”, for more information.
You can retrieve the current global or session
sql_mode value with the following
statements:
SELECT @@GLOBAL.sql_mode; SELECT @@SESSION.sql_mode;
The most important sql_mode
values are probably these:
This mode changes syntax and behavior to conform more closely to standard SQL.
If a value could not be inserted as given into a transactional table, abort the statement. For a nontransactional table, abort the statement if the value occurs in a single-row statement or the first row of a multiple-row statement. More detail is given later in this section.
Make MySQL behave like a “traditional” SQL database system. A simple description of this mode is “give an error instead of a warning” when inserting an incorrect value into a column.
When this manual refers to “strict mode,” it means a
mode where at least one of
STRICT_TRANS_TABLES or
STRICT_ALL_TABLES is enabled.
The following list describes all supported modes:
Don't do full checking of dates. Check only that the month is in the range from 1 to 12 and the day is in the range from 1 to 31. This is very convenient for Web applications where you obtain year, month, and day in three different fields and you want to store exactly what the user inserted (without date validation). This mode applies to
DATEandDATETIMEcolumns. It does not applyTIMESTAMPcolumns, which always require a valid date.The server requires that month and day values be legal, and not merely in the range 1 to 12 and 1 to 31, respectively. With strict mode disabled, invalid dates such as
'2004-04-31'are converted to'0000-00-00'and a warning is generated. With strict mode enabled, invalid dates generate an error. To allow such dates, enableALLOW_INVALID_DATES.Treat “
"” as an identifier quote character (like the “`” quote character) and not as a string quote character. You can still use “`” to quote identifiers with this mode enabled. WithANSI_QUOTESenabled, you cannot use double quotes to quote literal strings, because it is interpreted as an identifier.Produce an error in strict mode (otherwise a warning) when a division by zero (or
MOD(X,0)) occurs during anINSERTorUPDATE. If this mode is not enabled, MySQL instead returnsNULLfor divisions by zero. ForINSERT IGNOREorUPDATE IGNORE, MySQL generates a warning for divisions by zero, but the result of the operation isNULL.The precedence of the
NOToperator is such that expressions such asNOT a BETWEEN b AND care parsed asNOT (a BETWEEN b AND c). In some older versions of MySQL, the expression was parsed as(NOT a) BETWEEN b AND c. The old higher-precedence behavior can be obtained by enabling theHIGH_NOT_PRECEDENCESQL mode.mysql>
SET sql_mode = '';mysql>SELECT NOT 1 BETWEEN -5 AND 5;-> 0 mysql>SET sql_mode = 'HIGH_NOT_PRECEDENCE';mysql>SELECT NOT 1 BETWEEN -5 AND 5;-> 1Allow spaces between a function name and the “
(” character. This causes built-in function names to be treated as reserved words. As a result, identifiers that are the same as function names must be quoted as described in Section 8.2, “Schema Object Names”. For example, because there is aCOUNT()function, the use ofcountas a table name in the following statement causes an error:mysql>
CREATE TABLE count (i INT);ERROR 1064 (42000): You have an error in your SQL syntaxThe table name should be quoted:
mysql>
CREATE TABLE `count` (i INT);Query OK, 0 rows affected (0.00 sec)The
IGNORE_SPACESQL mode applies to built-in functions, not to user-defined functions or stored functions. It is always allowable to have spaces after a UDF or stored function name, regardless of whetherIGNORE_SPACEis enabled.For further discussion of
IGNORE_SPACE, see Section 8.2.4, “Function Name Parsing and Resolution”.Prevent the
GRANTstatement from automatically creating new users if it would otherwise do so, unless a nonempty password also is specified.NO_AUTO_VALUE_ON_ZEROaffects handling ofAUTO_INCREMENTcolumns. Normally, you generate the next sequence number for the column by inserting eitherNULLor0into it.NO_AUTO_VALUE_ON_ZEROsuppresses this behavior for0so that onlyNULLgenerates the next sequence number.This mode can be useful if
0has been stored in a table'sAUTO_INCREMENTcolumn. (Storing0is not a recommended practice, by the way.) For example, if you dump the table with mysqldump and then reload it, MySQL normally generates new sequence numbers when it encounters the0values, resulting in a table with contents different from the one that was dumped. EnablingNO_AUTO_VALUE_ON_ZERObefore reloading the dump file solves this problem. mysqldump now automatically includes in its output a statement that enablesNO_AUTO_VALUE_ON_ZERO, to avoid this problem.Disable the use of the backslash character (“
\”) as an escape character within strings. With this mode enabled, backslash becomes an ordinary character like any other.When creating a table, ignore all
INDEX DIRECTORYandDATA DIRECTORYdirectives. This option is useful on slave replication servers.Control automatic substitution of the default storage engine when a statement such as
CREATE TABLEorALTER TABLEspecifies a storage engine that is disabled or not compiled in.Because storage engines can be pluggable at runtime, unavailable engines are treated the same way:
With
NO_ENGINE_SUBSTITUTIONdisabled, forCREATE TABLEthe default engine is used and a warning occurs if the desired engine is unavailable. ForALTER TABLE, a warning occurs and the table is not altered.With
NO_ENGINE_SUBSTITUTIONenabled, an error occurs and the table is not created or altered if the desired engine is unavailable.Do not print MySQL-specific column options in the output of
SHOW CREATE TABLE. This mode is used by mysqldump in portability mode.Do not print MySQL-specific index options in the output of
SHOW CREATE TABLE. This mode is used by mysqldump in portability mode.Do not print MySQL-specific table options (such as
ENGINE) in the output ofSHOW CREATE TABLE. This mode is used by mysqldump in portability mode.In integer subtraction operations, do not mark the result as
UNSIGNEDif one of the operands is unsigned. In other words, the result of a subtraction is always signed whenever this mode is in effect, even if one of the operands is unsigned. For example, compare the type of columnc2in tablet1with that of columnc2in tablet2:mysql>
SET SQL_MODE='';mysql>CREATE TABLE test (c1 BIGINT UNSIGNED NOT NULL);mysql>CREATE TABLE t1 SELECT c1 - 1 AS c2 FROM test;mysql>DESCRIBE t1;+-------+---------------------+------+-----+---------+-------+ | Field | Type | Null | Key | Default | Extra | +-------+---------------------+------+-----+---------+-------+ | c2 | bigint(21) unsigned | | | 0 | | +-------+---------------------+------+-----+---------+-------+ mysql>SET SQL_MODE='NO_UNSIGNED_SUBTRACTION';mysql>CREATE TABLE t2 SELECT c1 - 1 AS c2 FROM test;mysql>DESCRIBE t2;+-------+------------+------+-----+---------+-------+ | Field | Type | Null | Key | Default | Extra | +-------+------------+------+-----+---------+-------+ | c2 | bigint(21) | | | 0 | | +-------+------------+------+-----+---------+-------+Note that this means that
BIGINT UNSIGNEDis not 100% usable in all contexts. See Section 11.9, “Cast Functions and Operators”.mysql>
SET SQL_MODE = '';mysql>SELECT CAST(0 AS UNSIGNED) - 1;+-------------------------+ | CAST(0 AS UNSIGNED) - 1 | +-------------------------+ | 18446744073709551615 | +-------------------------+ mysql>SET SQL_MODE = 'NO_UNSIGNED_SUBTRACTION';mysql>SELECT CAST(0 AS UNSIGNED) - 1;+-------------------------+ | CAST(0 AS UNSIGNED) - 1 | +-------------------------+ | -1 | +-------------------------+In strict mode, don't allow
'0000-00-00'as a valid date. You can still insert zero dates with theIGNOREoption. When not in strict mode, the date is accepted but a warning is generated.In strict mode, do not accept dates where the year part is nonzero but the month or day part is 0 (for example,
'0000-00-00'is legal but'2010-00-01'and'2010-01-00'are not). If used with theIGNOREoption, MySQL inserts a'0000-00-00'date for any such date. When not in strict mode, the date is accepted but a warning is generated.Do not allow queries for which the
SELECTlist refers to nonaggregated columns that are not named in theGROUP BYclause. The following query is invalid with this mode enabled becauseaddressis not named in theGROUP BYclause:SELECT name, address, MAX(age) FROM t GROUP BY name;
This mode also restricts references to nonaggregated columns in the
HAVINGclause that are not named in theGROUP BYclause.By default, trailing spaces are trimmed from
CHARcolumn values on retrieval. IfPAD_CHAR_TO_FULL_LENGTHis enabled, trimming does not occur and retrievedCHARvalues are padded to their full length. This mode does not apply toVARCHARcolumns, for which trailing spaces are retained on retrieval.mysql>
CREATE TABLE t1 (c1 CHAR(10));Query OK, 0 rows affected (0.37 sec) mysql>INSERT INTO t1 (c1) VALUES('xy');Query OK, 1 row affected (0.01 sec) mysql>SET sql_mode = '';Query OK, 0 rows affected (0.00 sec) mysql>SELECT c1, CHAR_LENGTH(c1) FROM t1;+------+-----------------+ | c1 | CHAR_LENGTH(c1) | +------+-----------------+ | xy | 2 | +------+-----------------+ 1 row in set (0.00 sec) mysql>SET sql_mode = 'PAD_CHAR_TO_FULL_LENGTH';Query OK, 0 rows affected (0.00 sec) mysql>SELECT c1, CHAR_LENGTH(c1) FROM t1;+------------+-----------------+ | c1 | CHAR_LENGTH(c1) | +------------+-----------------+ | xy | 10 | +------------+-----------------+ 1 row in set (0.00 sec)Treat
||as a string concatenation operator (same asCONCAT()) rather than as a synonym forOR.Treat
REALas a synonym forFLOAT. By default, MySQL treatsREALas a synonym forDOUBLE.Enable strict mode for all storage engines. Invalid data values are rejected. Additional detail follows.
Enable strict mode for transactional storage engines, and when possible for nontransactional storage engines. Additional details follow.
Strict mode controls how MySQL handles input values that are
invalid or missing. A value can be invalid for several reasons.
For example, it might have the wrong data type for the column, or
it might be out of range. A value is missing when a new row to be
inserted does not contain a value for a
non-NULL column that has no explicit
DEFAULT clause in its definition. (For a
NULL column, NULL is
inserted if the value is missing.)
For transactional tables, an error occurs for invalid or missing
values in a statement when either of the
STRICT_ALL_TABLES or
STRICT_TRANS_TABLES modes are
enabled. The statement is aborted and rolled back.
For nontransactional tables, the behavior is the same for either mode, if the bad value occurs in the first row to be inserted or updated. The statement is aborted and the table remains unchanged. If the statement inserts or modifies multiple rows and the bad value occurs in the second or later row, the result depends on which strict option is enabled:
For
STRICT_ALL_TABLES, MySQL returns an error and ignores the rest of the rows. However, in this case, the earlier rows still have been inserted or updated. This means that you might get a partial update, which might not be what you want. To avoid this, it is best to use single-row statements because these can be aborted without changing the table.For
STRICT_TRANS_TABLES, MySQL converts an invalid value to the closest valid value for the column and insert the adjusted value. If a value is missing, MySQL inserts the implicit default value for the column data type. In either case, MySQL generates a warning rather than an error and continues processing the statement. Implicit defaults are described in Section 10.1.4, “Data Type Default Values”.
Strict mode disallows invalid date values such as
'2004-04-31'. It does not disallow dates with
zero month or day parts such as '2004-04-00' or
“zero” dates. To disallow these as well, enable the
NO_ZERO_IN_DATE and
NO_ZERO_DATE SQL modes in
addition to strict mode.
If you are not using strict mode (that is, neither
STRICT_TRANS_TABLES nor
STRICT_ALL_TABLES is enabled),
MySQL inserts adjusted values for invalid or missing values and
produces warnings. In strict mode, you can produce this behavior
by using INSERT
IGNORE or UPDATE IGNORE. See
Section 12.5.5.41, “SHOW WARNINGS Syntax”.
Strict mode does not affect whether foreign key constraints are
checked. foreign_key_checks can
be used for that. (See
Section 5.1.5, “Session System Variables”.)
The following special modes are provided as shorthand for combinations of mode values from the preceding list.
The descriptions include all mode values that are available in the most recent version of MySQL. For older versions, a combination mode does not include individual mode values that are not available except in newer versions.
Equivalent to
REAL_AS_FLOAT,PIPES_AS_CONCAT,ANSI_QUOTES,IGNORE_SPACE.ANSImode also causes the server to return an error for queries where a set functionSwith an outer referenceS(outer_ref)SELECT * FROM t1 WHERE t1.a IN (SELECT MAX(t1.b) FROM t2 WHERE ...);
Here,
MAX(t1.b)cannot aggregated in the outer query because it appears in theWHEREclause of that query. Standard SQL requires an error in this situation. IfANSImode is not enabled, the server treatsS(outer_ref)S(const)Equivalent to
PIPES_AS_CONCAT,ANSI_QUOTES,IGNORE_SPACE,NO_KEY_OPTIONS,NO_TABLE_OPTIONS,NO_FIELD_OPTIONS.Equivalent to
PIPES_AS_CONCAT,ANSI_QUOTES,IGNORE_SPACE,NO_KEY_OPTIONS,NO_TABLE_OPTIONS,NO_FIELD_OPTIONS,NO_AUTO_CREATE_USER.Equivalent to
PIPES_AS_CONCAT,ANSI_QUOTES,IGNORE_SPACE,NO_KEY_OPTIONS,NO_TABLE_OPTIONS,NO_FIELD_OPTIONS.Equivalent to
NO_FIELD_OPTIONS,HIGH_NOT_PRECEDENCE.Equivalent to
NO_FIELD_OPTIONS,HIGH_NOT_PRECEDENCE.Equivalent to
PIPES_AS_CONCAT,ANSI_QUOTES,IGNORE_SPACE,NO_KEY_OPTIONS,NO_TABLE_OPTIONS,NO_FIELD_OPTIONS,NO_AUTO_CREATE_USER.Equivalent to
PIPES_AS_CONCAT,ANSI_QUOTES,IGNORE_SPACE,NO_KEY_OPTIONS,NO_TABLE_OPTIONS,NO_FIELD_OPTIONS.Equivalent to
STRICT_TRANS_TABLES,STRICT_ALL_TABLES,NO_ZERO_IN_DATE,NO_ZERO_DATE,ERROR_FOR_DIVISION_BY_ZERO,NO_AUTO_CREATE_USER, andNO_ENGINE_SUBSTITUTION.
MySQL Server supports a HELP
statement that returns online information from the MySQL Reference
manual (see Section 12.3.3, “HELP Syntax”). The proper operation of this
statement requires that the help tables in the
mysql database be initialized with help topic
information, which is done by processing the contents of the
fill_help_tables.sql script.
For a MySQL binary distribution on Unix, help table setup occurs when you run mysql_install_db. For an RPM distribution on Linux or binary distribution on Windows, help table setup occurs as part of the MySQL installation process.
For a MySQL source distribution, you can find the
fill_help_tables.sql file in the
scripts directory. To load the file manually,
make sure that you have initialized the mysql
database by running mysql_install_db, and then
process the file with the mysql client as
follows:
shell> mysql -u root mysql < fill_help_tables.sql
If you are working with Bazaar and a MySQL development source
tree, the tree doesn't contain
fill_help_tables.sql. You can download the
proper file for your version of MySQL from
http://dev.mysql.com/doc/. After downloading and
uncompressing the file, process it with mysql
as just described.
On Unix, signals can be sent to processes. mysqld responds to signals sent to it as follows:
SIGTERMcauses the server to shut down.SIGHUPcauses the server to reload the grant tables and flush the logs (likeFLUSH PRIVILEGESandFLUSH LOGS). It also writes a status report to the error log that has this format:Status information: Current dir: /var/mysql/data/ Running threads: 0 Stack size: 196608 Current locks: Key caches: default Buffer_size: 8388600 Block_size: 1024 Division_limit: 100 Age_limit: 300 blocks used: 0 not flushed: 0 w_requests: 0 writes: 0 r_requests: 0 reads: 0 handler status: read_key: 0 read_next: 0 read_rnd 0 read_first: 1 write: 0 delete 0 update: 0 Table status: Opened tables: 5 Open tables: 0 Open files: 7 Open streams: 0 Alarm status: Active alarms: 1 Max used alarms: 2 Next alarm time: 67
On some Mac OS X 10.3 versions, mysqld ignores
SIGHUP and SIGQUIT.
The server shutdown process takes place as follows:
The shutdown process is initiated.
Server shutdown can be initiated several ways. For example, a user with the
SHUTDOWNprivilege can execute a mysqladmin shutdown command. mysqladmin can be used on any platform supported by MySQL. Other operating system-specific shutdown initiation methods are possible as well: The server shuts down on Unix when it receives aSIGTERMsignal. A server running as a service on Windows shuts down when the services manager tells it to.The server creates a shutdown thread if necessary.
Depending on how shutdown was initiated, the server might create a thread to handle the shutdown process. If shutdown was requested by a client, a shutdown thread is created. If shutdown is the result of receiving a
SIGTERMsignal, the signal thread might handle shutdown itself, or it might create a separate thread to do so. If the server tries to create a shutdown thread and cannot (for example, if memory is exhausted), it issues a diagnostic message that appears in the error log:Error: Can't create thread to kill server
The server stops accepting new connections.
To prevent new activity from being initiated during shutdown, the server stops accepting new client connections. It does this by closing the network connections to which it normally listens for connections: the TCP/IP port, the Unix socket file, the Windows named pipe, and shared memory on Windows.
The server terminates current activity.
For each thread that is associated with a client connection, the connection to the client is broken and the thread is marked as killed. Threads die when they notice that they are so marked. Threads for idle connections die quickly. Threads that currently are processing statements check their state periodically and take longer to die. For additional information about thread termination, see Section 12.5.6.4, “
KILLSyntax”, in particular for the instructions about killedREPAIR TABLEorOPTIMIZE TABLEoperations onMyISAMtables.For threads that have an open transaction, the transaction is rolled back. Note that if a thread is updating a nontransactional table, an operation such as a multiple-row
UPDATEorINSERTmay leave the table partially updated, because the operation can terminate before completion.If the server is a master replication server, threads associated with currently connected slaves are treated like other client threads. That is, each one is marked as killed and exits when it next checks its state.
If the server is a slave replication server, the I/O and SQL threads, if active, are stopped before client threads are marked as killed. The SQL thread is allowed to finish its current statement (to avoid causing replication problems), and then stops. If the SQL thread was in the middle of a transaction at this point, the transaction is rolled back.
Storage engines are shut down or closed.
At this stage, the table cache is flushed and all open tables are closed.
Each storage engine performs any actions necessary for tables that it manages. For example,
MyISAMflushes any pending index writes for a table.InnoDBflushes its buffer pool to disk, unlessinnodb_fast_shutdownis 2, writes the current LSN to the tablespace, and terminates its own internal threads.The server exits.
MySQL has several different logs that can help you find out what is going on inside mysqld.
| Log Type | Information Written to Log |
| The error log | Problems encountered starting, running, or stopping mysqld |
| The general query log | Established client connections and statements received from clients |
| The binary log | All statements that change data (also used for replication) |
| The slow query log | All queries that took more than
long_query_time seconds to
execute or didn't use indexes |
By default, all log files are created in the
mysqld data directory. You can force
mysqld to close and reopen the log files (or in
some cases switch to a new log) by flushing the logs. Log flushing
occurs when you issue a FLUSH
LOGS statement or execute a mysqladmin
flush-logs, mysqladmin refresh,
mysqldump --flush-logs, or mysqldump
--master-data command. See Section 12.5.6.3, “FLUSH Syntax”,
Section 4.5.2, “mysqladmin — Client for Administering a MySQL Server”, and Section 4.5.4, “mysqldump — A Database Backup Program”. In
addition, the binary log is flushed when its size reaches the value
of the max_binlog_size system
variable.
If you are using MySQL replication capabilities, slave replication servers maintain additional log files called relay logs. Chapter 16, Replication, discusses relay log contents and configuration.
The server can write general query and slow query entries to log tables, log files, or both. For details, see Section 5.2.1, “Selecting General Query and Slow Query Log Output Destinations”.
You can also control during runtime the general query and slow query logs. You can enable or disable logging, or change the name of the log file. See Section 5.2.3, “The General Query Log”, and Section 5.2.5, “The Slow Query Log”.
See Section 5.3.2.1, “Administrator Guidelines for Password Security”, for information about keeping logs secure.
MySQL Enterprise The MySQL Enterprise Monitor provides a number of advisors specifically related to the various log files. For more information, see http://www.mysql.com/products/enterprise/advisors.html.
MySQL Server provides flexible control over the destination for
log output. Log entries can be written to log files or to the
general_log and
slow_log tables in the mysql
database. If logging is enabled, either or both destinations can
be selected.
Currently, logging to tables incurs significantly more server overhead than logging to files. If you enable the general log or slow query log and require highest performance, you should log to files and not to tables.
Log control at server startup.
The --log-output option specifies
the destination for log output, if logging is enabled, but the
option does not in itself enable the logs. The syntax for this
option is
--log-output[=:
value,...]
If
--log-outputis given with a value, the value can be a comma-separated list of one or more of the wordsTABLE(log to tables),FILE(log to files), orNONE(do not log to tables or files).NONE, if present, takes precedence over any other specifiers.If
--log-outputis omitted or given without a value, the default logging destination isFILE.
The --general_log option, if given,
enables logging to the general query log for the selected log
destinations. --general_log takes
an optional argument of 1 or 0 to enable or disable the log. To
specify a file name other than the default for file logging, use
--general_log_file=.
Similarly, the file_name--slow_query_log
option, if given, enables logging to the slow query log for the
selected destinations and
--slow_query_log_file=
specifies a file name for file logging. If either log is enabled,
the server opens the corresponding log file and writes startup
messages to it. However, further logging of queries to the file
does not occur unless the file_nameFILE log destination
is selected.
Examples:
To write general query log entries to the log table and the log file, use
--log-output=TABLE,FILEto select both log destinations and the--general_logoption to enable the general query log.To write general and slow query log entries only to the log tables, use
--log-output=TABLEto select tables as the log destination and the--general_logand--slow_query_logoptions to enable both logs.To write slow query log entries only to the log file, use
--log-output=FILEto select files as the log destination and the--slow_query_logoption to enable the slow query log. (In this case, because the default log destination isFILE, you could omit the--log-outputoption.)
Log control at runtime. Several system variables are associated with log tables and files and enable runtime control over logging:
The global
log_outputsystem variable indicates the current logging destination. It can be modified at runtime to change the destination.The global
general_logandslow_query_logvariables indicate whether the general query log and slow query log are enabled (ON) or disabled (OFF). You can set these variables at runtime to control whether the logs are enabled.The global
general_log_fileandslow_query_log_filevariables indicate the names of the general query log and slow query log files. You can set these variables at server startup or at runtime to change the names of the log files.The session
sql_log_offvariable can be set toONorOFFto disable or enable general query logging for the current connection.
The use of tables for log output offers the following benefits:
Log entries have a standard format. To display the current structure of the log tables, use these statements:
SHOW CREATE TABLE mysql.general_log; SHOW CREATE TABLE mysql.slow_log;
Log contents are accessible via SQL statements. This enables the use of queries that select only those log entries that satisfy specific criteria. For example, to select log contents associated with a particular client (which can be useful for identifying problematic queries from that client), it is easier to do this using a log table than a log file.
Logs are accessible remotely through any client that can connect to the server and issue queries (if the client has the appropriate log table privileges). It is not necessary to log in to the server host and directly access the file system.
The log table implementation has the following characteristics:
In general, the primary purpose of log tables is to provide an interface for users to observe the runtime execution of the server, not to interfere with its runtime execution.
CREATE TABLE,ALTER TABLE, andDROP TABLEare valid operations on a log table. ForALTER TABLEandDROP TABLE, the log table cannot be in use and must be disabled, as described later.By default, the log tables use the
CSVstorage engine that writes data in comma-separated values format. For users who have access to the.CSVfiles that contain log table data, the files are easy to import into other programs such as spreadsheets that can process CSV input.The log tables can be altered to use the
MyISAMstorage engine. You cannot useALTER TABLEto alter a log table that is in use. The log must be disabled first. No engines other thanCSVorMyISAMare legal for the log tables.To disable logging so that you can alter (or drop) a log table, you can use the following strategy. The example uses the general query log; the procedure for the slow query log is similar but uses the
slow_logtable andslow_query_logsystem variable.SET @old_log_state = @@global.general_log; SET GLOBAL general_log = 'OFF'; ALTER TABLE mysql.general_log ENGINE = MyISAM; SET GLOBAL general_log = @old_log_state;
TRUNCATE TABLEis a valid operation on a log table. It can be used to expire log entries.RENAME TABLEis a valid operation on a log table. You can atomically rename a log table (to perform log rotation, for example) using the following strategy:USE mysql; CREATE TABLE IF NOT EXISTS general_log2 LIKE general_log; RENAME TABLE general_log TO general_log_backup, general_log2 TO general_log;
LOCK TABLEScannot be used on a log table.INSERT,DELETE, andUPDATEcannot be used on a log table. These operations are allowed only internally to the server itself.FLUSH TABLES WITH READ LOCKand the state of the globalread_onlysystem variable have no effect on log tables. The server can always write to the log tables.Entries written to the log tables are not written to the binary log and thus are not replicated to slave servers.
To flush the log tables or log files, use
FLUSH TABLESorFLUSH LOGS, respectively.Partitioning of log tables is not permitted.
The error log contains information indicating when mysqld was started and stopped and also any critical errors that occur while the server is running. If mysqld notices a table that needs to be automatically checked or repaired, it writes a message to the error log.
On some operating systems, the error log contains a stack trace if mysqld dies. The trace can be used to determine where mysqld died. See MySQL Internals: Porting.
You can specify where mysqld writes the error
log with the
--log-error[=
option. If no file_name]file_name value is given,
mysqld uses the name
host_name.errFLUSH
LOGS, the error log is renamed with the suffix
-old and mysqld creates a
new empty log file. (No renaming occurs if the
--log-error option was not given to
mysqld.)
If you do not specify --log-error,
or (on Windows) if you use the
--console option, errors are
written to stderr, the standard error output.
Usually this is your terminal.
On Windows, error output is always written to the
.err file if
--console is not given.
In addition, on Windows, events and error messages are written to
the Windows Event Log within the Application log. Entries marked
as Warning and Note are
written to the Event Log, but informational messages (such as
information statements from individual storage engines) are not
copied to the Event Log. The log entries will have a source of
MySQL. You cannot disable writing information
to the Windows Event Log.
The --log-warnings option or
log_warnings system variable can
be used to control warning logging to the error log. The default
value is enabled (1). Warning logging can be disabled using a
value of 0. If the value is greater than 1, aborted connections
are written to the error log, and access-denied errors for new
connection attempts are written. See
Section B.5.2.11, “Communication Errors and Aborted Connections”.
If you use mysqld_safe to start
mysqld, mysqld_safe arranges
for mysqld to write error messages to a log
file or to syslog
mysqld_safe has three error-logging options,
--syslog,
--skip-syslog,
and --log-error. The default
with no logging options or with
--skip-syslog
is to use the default log file. To explicitly specify use of an
error log file, specify
--log-error=
to mysqld_safe, and
mysqld_safe will arrange for
mysqld to write messages to a log file. To use
file_namesyslog instead, specify the
--syslog option.
If you specify --log-error in an
option file in a section that mysqld reads,
mysqld_safe also will find and use the option.
If mysqld_safe is used to start
mysqld and mysqld dies
unexpectedly, mysqld_safe notices that it needs
to restart mysqld and writes a
restarted mysqld message to the error log.
The general query log is a general record of what mysqld is doing. The server writes information to this log when clients connect or disconnect, and it logs each SQL statement received from clients. The general query log can be very useful when you suspect an error in a client and want to know exactly what the client sent to mysqld.
mysqld writes statements to the query log in the order that it receives them, which might differ from the order in which they are executed. This logging order contrasts to the binary log, for which statements are written after they are executed but before any locks are released. (Also, the query log contains all statements, whereas the binary log does not contain statements that only select data.)
By default, the general query log is disabled. Use
--general_log[={0|1}] to specify
the initial general query log state explicitly. With no argument
or an argument of 1, --general_log
enables the log. With an argument of 0, this option disables the
log. You can use
--general_log_file=
to specify a log file name. You can also use
file_name--log-output to specify the log
destination (as described in Section 5.2.1, “Selecting General Query and Slow Query Log Output Destinations”). The
older options to enable the general query log,
--log and -l, are
deprecated.
If you specify no name for the general query log file, the default
name is
host_name.log
For runtime control of the general query log, use the global
general_log and
general_log_file system
variables. Set general_log to 0
(or OFF) to disable the log or to 1 (or
ON) to enable it. Set
general_log_file to specify the
name of the log file. If a log file already is open, it is closed
and the new file is opened.
When the general query log is enabled, output is written to any
destinations specified by the
--log-output option or
log_output system variable. If
you enable the log, the server opens the log file and writes
startup messages to it. However, further logging of queries to the
file does not occur unless the FILE log
destination is selected. If the destination is
NONE, no queries are written even if the
general log is enabled. Setting the log file name has no effect on
logging if the log destination value does not contain
FILE.
Server restarts and log flushing do not cause a new general query log file to be generated (although flushing closes and reopens it). On Unix, you can rename the file and create a new one by using the following commands:
shell>mvshell>host_name.loghost_name-old.logmysqladmin flush-logsshell>cpshell>host_name-old.logbackup-directoryrmhost_name-old.log
On Windows, you can rename the general query log or slow query log
while the server has it open. You cannot rename the error log file
while the server has it open. You must stop the server and rename
the file, and then restart the server to create a new log file.
However, a stop and restart can be avoided by using
FLUSH LOGS, which
causes the server to rename the error log with an
-old suffix and open a new error log.
You can disable the general query log at runtime:
SET GLOBAL general_log = 'OFF';
With the log disabled, rename the log file externally; for example, from the command line. Then enable the log again:
SET GLOBAL general_log = 'ON';
This method works on any platform and does not require a server restart.
The session sql_log_off variable
can be set to ON or OFF to
disable or enable general query logging for the current
connection.
The general query log should be protected because logged statements might contain passwords. See Section 5.3.2.1, “Administrator Guidelines for Password Security”.
The binary log contains “events” that describe
database changes such as table creation operations or changes to
table data. It also contains events for statements that
potentially could have made changes (for example, a
DELETE which matched no rows),
unless row-based logging is used. The binary log also contains
information about how long each statement took that updated data.
The binary log has two important purposes:
For replication, the binary log is used on master replication servers as a record of the statements to be sent to slave servers. The master server sends the events contained in its binary log to its slaves, which execute those events to make the same data changes that were made on the master. See Section 16.2, “Replication Implementation”.
Certain data recovery operations require use of the binary log. After a backup has been restored, the events in the binary log that were recorded after the backup was made are re-executed. These events bring databases up to date from the point of the backup. See Section 6.5, “Point-in-Time (Incremental) Recovery Using the Binary Log”.
Running a server with binary logging enabled makes performance about 1% slower. However, the benefits of the binary log in allowing you to set up replication and for restore operations generally outweigh this minor performance decrement.
For information about server options and variables affecting the operation of binary logging, see Section 16.1.3.4, “Binary Log Options and Variables”.
The binary log is not used for statements such as
SELECT or
SHOW that do not modify data. If
you want to log all statements (for example, to identify a problem
query), use the general query log. See
Section 5.2.3, “The General Query Log”.
The binary log should be protected because logged statements might contain passwords. See Section 5.3.2.1, “Administrator Guidelines for Password Security”.
The format of the events recorded in the binary log is dependent on the binary logging format. Three format types are supported, row-based logging, statement-based logging and mixed-base logging. The binary logging format used depends on the MySQL version. For more information on logging formats, see Section 5.2.4.1, “Binary Logging Formats”.
MySQL Enterprise The binary log can also be used to track significant DDL events. Analyzing the binary log in this way is an integral part of the MySQL Enterprise Monitor. For more information, see http://www.mysql.com/products/enterprise/advisors.html.
To enable the binary log, start the server with the
--log-bin[=
option. If no base_name]base_name value is given,
the default name is the value of the pid-file
option (which by default is the name of host machine) followed by
-bin. If the basename is given, the server
writes the file in the data directory unless the basename is given
with a leading absolute path name to specify a different
directory. It is recommended that you specify a basename; see
Additional Known Issues, for the reason.
If you supply an extension in the log name (for example,
--log-bin=),
the extension is silently removed and ignored.
base_name.extension
mysqld appends a numeric extension to the
binary log basename to generate binary log file names. The number
increases each time the server creates a new log file, thus
creating an ordered series of files. The server creates a new file
in the series each time it starts or flushes the logs. The server
also creates a new binary log file automatically after the current
log's size reaches
max_binlog_size. A binary log
file may become larger than
max_binlog_size if you are using
large transactions because a transaction is written to the file in
one piece, never split between files.
To keep track of which binary log files have been used,
mysqld also creates a binary log index file
that contains the names of all used binary log files. By default,
this has the same basename as the binary log file, with the
extension '.index'. You can change the name of
the binary log index file with the
--log-bin-index[=
option. You should not manually edit this file while
mysqld is running; doing so would confuse
mysqld.
file_name]
The term “binary log file” generally denotes an individual numbered file containing database events. The term “binary log” collectively denotes the set of numbered binary log files plus the index file.
The server evaluates the
--binlog-do-db and
--binlog-ignore-db options in the
same way as it does the
--replicate-do-db and
--replicate-ignore-db options. For
information about how this is done, see
Section 16.2.3.1, “Evaluation of Database-Level Replication and Binary Logging Options”.
A replication slave server by default does not write to its own
binary log any data modifications that are received from the
replication master. To log these modifications, start the slave
with the --log-slave-updates option
in addition to the --log-bin option
(see Section 16.1.3.3, “Replication Slave Options and Variables”).
You can delete all binary log files with the
RESET MASTER statement, or a subset
of them with PURGE BINARY LOGS. See
Section 12.5.6.6, “RESET Syntax”, and Section 12.6.1.1, “PURGE BINARY LOGS Syntax”.
If you are using replication, you should not delete old binary log
files on the master until you are sure that no slave still needs
to use them. For example, if your slaves never run more than three
days behind, once a day you can execute mysqladmin
flush-logs on the master and then remove any logs that
are more than three days old. You can remove the files manually,
but it is preferable to use PURGE BINARY
LOGS, which also safely updates the binary log index
file for you (and which can take a date argument). See
Section 12.6.1.1, “PURGE BINARY LOGS Syntax”.
A client that has the SUPER
privilege can disable binary logging of its own statements by
using a SET sql_log_bin=0 statement. See
Section 5.1.5, “Session System Variables”.
You can display the contents of binary log files with the mysqlbinlog utility. This can be useful when you want to reprocess statements in the log for a recovery operation. For example, you can update a MySQL server from the binary log as follows:
shell> mysqlbinlog log_file | mysql -h server_name
mysqlbinlog also can be used to display replication slave relay log file contents because they are written using the same format as binary log files. For more information on the mysqlbinlog utility and how to use it, see Section 4.6.7, “mysqlbinlog — Utility for Processing Binary Log Files”. For more information about the binary log and recovery operations, see Section 6.5, “Point-in-Time (Incremental) Recovery Using the Binary Log”.
Binary logging is done immediately after a statement completes but before any locks are released or any commit is done. This ensures that the log is logged in execution order.
Updates to nontransactional tables are stored in the binary log immediately after execution.
Within an uncommitted transaction, all updates
(UPDATE,
DELETE, or
INSERT) that change transactional
tables such as InnoDB tables are cached until a
COMMIT statement is received by the
server. At that point, mysqld writes the entire
transaction to the binary log before the
COMMIT is executed. When the thread
that handles the transaction starts, it allocates a buffer of
binlog_cache_size to buffer
statements. If a statement is bigger than this, the thread opens a
temporary file to store the transaction. The temporary file is
deleted when the thread ends.
The Binlog_cache_use status
variable shows the number of transactions that used this buffer
(and possibly a temporary file) for storing statements. The
Binlog_cache_disk_use status
variable shows how many of those transactions actually had to use
a temporary file. These two variables can be used for tuning
binlog_cache_size to a large
enough value that avoids the use of temporary files.
The max_binlog_cache_size system
variable (default 4GB, which is also the maximum) can be used to
restrict the total size used to cache a multiple-statement
transaction. If a transaction is larger than this many bytes, it
fails and rolls back. The minimum value is 4096.
Modifications to nontransactional tables cannot be rolled back. If
a transaction that is rolled back includes modifications to
nontransactional tables, the entire transaction is logged with a
ROLLBACK
statement at the end to ensure that the modifications to those
tables are replicated.
If you are using the binary log and row based logging, concurrent
inserts are converted to normal inserts for CREATE ...
SELECT or
INSERT ...
SELECT statement. This is done to ensure that you can
re-create an exact copy of your tables by applying the log during
a backup operation. If you are using statement-based logging, the
original statement is written to the log.
The binary log format has some known limitations that can affect recovery from backups. See Section 16.4.1, “Replication Features and Issues”.
Binary logging for stored programs is done as described in Section 18.6, “Binary Logging of Stored Programs”.
Note that the binary log format differs in MySQL 5.5 from previous versions of MySQL, due to enhancements in replication. See Section 16.4.2, “Replication Compatibility Between MySQL Versions”.
Writes to the binary log file and binary log index file are
handled in the same way as writes to MyISAM
tables. See Section B.5.4.3, “How MySQL Handles a Full Disk”.
By default, the binary log is not synchronized to disk at each
write. So if the operating system or machine (not only the MySQL
server) crashes, there is a chance that the last statements of the
binary log are lost. To prevent this, you can make the binary log
be synchronized to disk after every N
writes to the binary log, with the
sync_binlog system variable. See
Section 5.1.4, “Server System Variables”. 1 is the safest value
for sync_binlog, but also the
slowest. Even with sync_binlog
set to 1, there is still the chance of an inconsistency between
the table content and binary log content in case of a crash. For
example, if you are using InnoDB tables and the
MySQL server processes a COMMIT
statement, it writes the whole transaction to the binary log and
then commits this transaction into InnoDB. If
the server crashes between those two operations, the transaction
is rolled back by InnoDB at restart but still
exists in the binary log. To resolve this, you should set
--innodb_support_xa to 1. Although
this option is related to the support of XA transactions in
InnoDB, it also ensures that the binary log and InnoDB data files
are synchronized.
For this option to provide a greater degree of safety, the MySQL
server should also be configured to synchronize the binary log and
the InnoDB logs to disk at every transaction.
The InnoDB logs are synchronized by default,
and sync_binlog=1 can be used to synchronize
the binary log. The effect of this option is that at restart after
a crash, after doing a rollback of transactions, the MySQL server
cuts rolled back InnoDB transactions from the
binary log. This ensures that the binary log reflects the exact
data of InnoDB tables, and so, that the slave
remains in synchrony with the master (not receiving a statement
which has been rolled back).
If the MySQL server discovers at crash recovery that the binary
log is shorter than it should have been, it lacks at least one
successfully committed InnoDB transaction. This
should not happen if sync_binlog=1 and the
disk/file system do an actual sync when they are requested to
(some don't), so the server prints an error message The
binary log . In this case, this binary log is not
correct and replication should be restarted from a fresh snapshot
of the master's data.
file_name is shorter than
its expected size
For MySQL 5.1.20 and later (and MySQL 5.0.46 and later for backward compatibility), the session values of the following system variables are written to the binary log and honored by the replication slave when parsing the binary log:
sql_mode(except that theNO_DIR_IN_CREATEmode is not replicated; see Section 16.4.1.31, “Replication and Variables”)
A number of different logging formats are used to record information in the binary log. The exact format employed depends on the version of MySQL being used. There are three logging formats:
Replication capabilities in MySQL originally were based on propagation of SQL statements from master to slave. This is called statement-based logging. You can cause this format to be used by starting the server with
--binlog-format=STATEMENT.In row-based logging, the master writes events to the binary log that indicate how individual table rows are affected. You can cause the server to use row-based logging by starting it with
--binlog-format=ROW.A third option is also available: mixed logging. With mixed logging, statement-based logging is used by default, but the logging mode switches automatically to row-based in certain cases as described below. You can cause MySQL to use mixed logging explicitly by starting mysqld with the option
--binlog-format=MIXED.
Statement-based logging is the default logging mode in MySQL 5.5.
The logging format can also be set or limited by the storage engine being used. This helps to eliminate issues when replicating certain statements between a master and slave which are using different storage engines.
With statement-based replication, there may be issues with replicating nondeterministic statements. In deciding whether or not a given statement is safe for statement-based replication, MySQL determines whether it can guarantee that the statement can be replicated using statement-based logging. If MySQL cannot make this guarantee, it marks the statement as potentially unreliable and issues the warning, Statement may not be safe to log in statement format.
You can avoid these issues by using MySQL's row-based replication instead.
The default binary logging format is statement-based in MySQL 5.5.
You can select the binary logging format explicitly by starting
the MySQL server with
--binlog-format=.
When set, all replication slaves connecting to the server will
read the events according to this setting. The supported values
for typetype are:
STATEMENTcauses logging to be statement-based.ROWcauses logging to be row-based.MIXEDcauses logging to use mixed format.
The logging format also can be switched at runtime. To specify
the format globally for all clients, set the global value of the
binlog_format system variable:
mysql>SET GLOBAL binlog_format = 'STATEMENT';mysql>SET GLOBAL binlog_format = 'ROW';mysql>SET GLOBAL binlog_format = 'MIXED';
An individual client can control the logging format for its own
statements by setting the session value of
binlog_format:
mysql>SET SESSION binlog_format = 'STATEMENT';mysql>SET SESSION binlog_format = 'ROW';mysql>SET SESSION binlog_format = 'MIXED';
To change the global or session
binlog_format value, you must
have the SUPER privilege.
In addition to switching the logging format manually, a slave
server may switch the format automatically.
This happens when the server is running in either
STATEMENT or MIXED format
and encounters an event in the binary log that is written in
ROW logging format. In that case, the slave
switches to row-based replication temporarily for that event,
and switches back to the previous format afterwards.
There are several reasons why a client might want to set binary logging on a per-session basis:
A session that makes many small changes to the database might want to use row-based logging.
A session that performs updates that match many rows in the
WHEREclause might want to use statement-based logging because it will be more efficient to log a few statements than many rows.Some statements require a lot of execution time on the master, but result in just a few rows being modified. It might therefore be beneficial to replicate them using row-based logging.
There are exceptions when you cannot switch the replication format at runtime:
From within a stored function or a trigger
If the
NDBCLUSTERstorage engine is enabledIf the session is currently in row-based replication mode and has open temporary tables
Trying to switch the format in any of these cases results in an error.
Switching the replication format at runtime is not recommended
when any temporary tables exist, because temporary tables are
logged only when using statement-based replication, whereas with
row-based replication they are not logged. With mixed
replication, temporary tables are usually logged; exceptions
happen with user-defined functions (UDFs) and with the
UUID() function.
With the binary log format set to ROW, many
changes are written to the binary log using the row-based
format. Some changes, however, still use the statement-based
format. Examples include all DDL (data definition language)
statements such as CREATE TABLE,
ALTER TABLE, or
DROP TABLE.
The --binlog-row-event-max-size
option is available for servers that are capable of row-based
replication. Rows are stored into the binary log in chunks
having a size in bytes not exceeding the value of this option.
The value must be a multiple of 256. The default value is 1024.
Warning
When using statement-based logging for replication, it is possible for the data on the master and slave to become different if a statement is designed in such a way that the data modification is nondeterministic; that is, it is left to the will of the query optimizer. In general, this is not a good practice even outside of replication. For a detailed explanation of this issue, see Additional Known Issues.
When running in MIXED mode, automatic
switching from statement-based to row-based replication takes
place under the following conditions:
When a function contains
UUID().When 2 or more tables with
AUTO_INCREMENTcolumns are updated.When any
INSERT DELAYEDis executed.When the body of a view requires row-based replication, the statement creating the view also uses it — for example, this occurs when the statement creating a view uses the
UUID()function.When a call to a UDF is involved.
If a statement is logged by row and the client that executed the statement has any temporary tables, logging by row is used for all subsequent statements (except for those accessing temporary tables) until all temporary tables in use by that client are dropped.
This is true whether or not any temporary tables are actually logged.
Temporary tables cannot be logged using the row-based format; thus, once row-based logging is used, all subsequent statements using that table are unsafe, and we approximate this condition by treating all statements made by that client as unsafe until the client no longer holds any temporary tables.
When
FOUND_ROWS()orROW_COUNT()is used. (Bug#12092, Bug#30244)When
USER(),CURRENT_USER(), orCURRENT_USERis used. (Bug#28086)When a statement refers to one or more system variables. (Bug#31168)
Exception. The following system variables, when used with session scope (only), do not cause the logging format to switch:
For information about determining system variable scope, see Section 5.1.6, “Using System Variables”.
For information about how replication treats
sql_mode, see Section 16.4.1.31, “Replication and Variables”.When one of the tables involved is a log table in the
mysqldatabase.When the
LOAD_FILE()function is used. (Bug#39701)
Note
A warning is generated if you try to execute a statement using
statement-based logging that should be written using row-based
logging. The warning is shown both in the client (in the
output of SHOW WARNINGS) and
through the mysqld error log. A warning is
added to the SHOW WARNINGS
table each time such a statement is executed. However, only
the first statement that generated the warning for each client
session is written to the mysqld error log
to prevent flooding the log.
In addition to the decisions above, individual engines can also determine the logging format used when information in a table is updated. The following table lists the logging formats supported by each storage engine:
| Storage Engine | Row Logging Supported | Statement Logging Supported |
|---|---|---|
ARCHIVE | Yes | Yes |
BLACKHOLE | Yes | Yes |
CSV | Yes | Yes |
EXAMPLE | Yes | No |
FEDERATED | Yes | Yes |
HEAP | Yes | Yes |
InnoDB | Yes | Yes when the transaction isolation level is
REPEATABLE READ or
SERIALIZABLE; No
otherwise. |
MyISAM | Yes | Yes |
MERGE | Yes | Yes |
NDBCLUSTER | Yes | No |
A given storage engine can support either or both logging formats; the logging capabilities of an individual engine can be further defined as follows:
If an engine supports row-based logging, the engine is said to be row-logging capable.
If an engine supports statement-based logging, the engine is said to be statement-logging capable.
When determining the logging mode to be used, the capabilities of all the tables affected by the event are combined. The set of affected tables is then marked according to these rules:
A set of tables is defined as row logging restricted if the tables are row logging capable but not statement logging capable.
A set of tables is defined as statement logging restricted if the tables are statement logging capable but not row logging capable.
Once the determination of the possible logging formats required
by the statement is complete it is compared to the current
binlog_format setting. The
following table is used to decide how the information is
recorded in the binary log or, if appropriate, whether an error
is raised. In the table, a safe operation is defined as one that
is deterministic.
Several rules decide whether the statement is deterministic or not, as shown in the following table, where SLR stands for “statement-logging restricted” and RLR stands for “row-logging restricted”. A statement is statement-logging restricted if one or more of the tables it accesses is not statement-logging capable. Similarly, a statement is row-logging restricted if any table accessed by the statement is not row-logging capable.
| Condition | Action | ||||
|---|---|---|---|---|---|
| Safe/unsafe | binlog_format | SLR | RLR | Error/Warning | Logged as |
| Safe | STATEMENT | Yes | Yes | Error: not loggable | |
| Safe | STATEMENT | Yes | No | STATEMENT | |
| Safe | STATEMENT | No | Yes | Error: not loggable | |
| Safe | STATEMENT | No | No | STATEMENT | |
| Safe | MIXED | Yes | Yes | Error: not loggable | |
| Safe | MIXED | Yes | No | STATEMENT | |
| Safe | MIXED | No | Yes | ROW | |
| Safe | MIXED | No | No | STATEMENT | |
| Safe | ROW | Yes | Yes | Error: not loggable | |
| Safe | ROW | Yes | No | Error: not loggable | |
| Safe | ROW | No | Yes | ROW | |
| Safe | ROW | No | No | ROW | |
| Unsafe | STATEMENT | Yes | Yes | Error: not loggable | |
| Unsafe | STATEMENT | Yes | No | Warning: unsafe | STATEMENT |
| Unsafe | STATEMENT | No | Yes | Error: not loggable | |
| Unsafe | STATEMENT | No | No | Warning: unsafe | STATEMENT |
| Unsafe | MIXED | Yes | Yes | Error: not loggable | |
| Unsafe | MIXED | Yes | No | Error: not loggable | |
| Unsafe | MIXED | No | Yes | ROW | |
| Unsafe | MIXED | No | No | ROW | |
| Unsafe | ROW | Yes | Yes | Error: not loggable | |
| Unsafe | ROW | Yes | No | Error: not loggable | |
| Unsafe | ROW | No | Yes | ROW | |
| Unsafe | ROW | No | No | ROW | |
When a warning is produced by the determination, a standard
MySQL warning is produced (and is available using
SHOW WARNINGS). The information
is also written to the mysqld error log. Only
one error for each error instance per client connection is
logged. The log message will include the SQL statement that was
attempted.
If a slave server was started with
--log-warnings enabled, the slave
prints messages to the error log to provide information about
its status, such as the binary log and relay log coordinates
where it starts its job, when it is switching to another relay
log, when it reconnects after a disconnect, and so forth.
The contents of the grant tables in the mysql
database can be modified directly (for example, with
INSERT or
DELETE) or indirectly (for
example, with GRANT or
CREATE USER). Statements that
affect mysql database tables are written to
the binary log using the following rules:
Data manipulation statements that change data in
mysqldatabase tables directly are logged according to the setting of thebinlog_formatsystem variable. This pertains to statements such asINSERT,UPDATE,DELETE,REPLACE,DO,LOAD DATA INFILE,SELECT, andTRUNCATE TABLE.Statements that change the
mysqldatabase indirectly are logged as statements regardless of the value ofbinlog_format. This pertains to statements such asGRANT,REVOKE,SET PASSWORD,RENAME USER,CREATE(all forms exceptCREATE TABLE ... SELECT),ALTER(all forms), andDROP(all forms).
CREATE TABLE ...
SELECT is a combination of data definition and data
manipulation. The CREATE TABLE
part is logged using statement format and the
SELECT part is logged according
to the value of binlog_format.
The slow query log consists of all SQL statements that took more
than long_query_time seconds to
execute and required at least
min_examined_row_limit rows to be
examined. The time to acquire the initial table locks is not
counted as execution time. mysqld writes a
statement to the slow query log after it has been executed and
after all locks have been released, so log order might be
different from execution order. The default value of
long_query_time is 10. The
minimum value is 0, and a resolution of microseconds is supported
when logging to a file. However, the microseconds part is ignored
and only integer values are written when logging to tables.
By default, the slow query log is disabled. Use
--slow_query_log[={0|1}] to specify
the initial slow query log state explicitly. With no argument or
an argument of 1, --slow_query_log
enables the log. With an argument of 0, this option disables the
log. You can use
--slow_query_log_file=
to specify a log file name. You can also use
file_name--log-output to specify the log
destination (as described in Section 5.2.1, “Selecting General Query and Slow Query Log Output Destinations”). The
older option to enable the slow query log file,
--log-slow-queries, is deprecated.
If you specify no name for the slow query log file, the default
name is
host_name-slow.log
For runtime control of the slow query log, use the global
slow_query_log and
slow_query_log_file system
variables. Set slow_query_log to
0 (or OFF) to disable the log or to 1 (or
ON) to enable it. Set
slow_query_log_file to specify
the name of the log file. If a log file already is open, it is
closed and the new file is opened.
When the slow query log is enabled, output is written to any
destinations specified by the
--log-output option or
log_output system variable. If
you enable the log, the server opens the log file and writes
startup messages to it. However, further logging of queries to the
file does not occur unless the FILE log
destination is selected. If the destination is
NONE, no queries are written even if the slow
query log is enabled. Setting the log file name has no effect on
logging if the log destination value does not contain
FILE.
The slow query log can be used to find queries that take a long time to execute and are therefore candidates for optimization. However, examining a long slow query log can become a difficult task. To make this easier, you can process a slow query log file using the mysqldumpslow command to summarize the queries that appear in the log. See Section 4.6.8, “mysqldumpslow — Summarize Slow Query Log Files”.
In MySQL 5.5, queries that do not use indexes are
logged in the slow query log if the
--log-queries-not-using-indexes
option is specified. See Section 5.1.2, “Server Command Options”.
MySQL Enterprise Excessive table scans are indicative of missing or poorly optimized indexes. Using an advisor specifically designed for the task, the MySQL Enterprise Monitor can identify such problems and offer advice on resolution. For more information, see http://www.mysql.com/products/enterprise/advisors.html.
In MySQL 5.5, the
--log-slow-admin-statements server
option enables you to request logging of slow administrative
statements such as OPTIMIZE TABLE,
ANALYZE TABLE, and
ALTER TABLE to the slow query log.
Queries handled by the query cache are not added to the slow query log, nor are queries that would not benefit from the presence of an index because the table has zero rows or one row.
A replication slave does not write replicated queries to the slow
query log, unless it is run using the
--log-slow-slave-statements option.
The slow query log should be protected because logged statements might contain passwords. See Section 5.3.2.1, “Administrator Guidelines for Password Security”.
MySQL Server can create a number of different log files that make it easy to see what is going on. See Section 5.2, “MySQL Server Logs”. However, you must clean up these files regularly to ensure that the logs do not take up too much disk space.
When using MySQL with logging enabled, you may want to back up and remove old log files from time to time and tell MySQL to start logging to new files. See Section 6.2, “Database Backup Methods”.
On a Linux (Red Hat) installation, you can use the
mysql-log-rotate script for this. If you
installed MySQL from an RPM distribution, this script should have
been installed automatically. You should be careful with this
script if you are using the binary log for replication. You should
not remove binary logs until you are certain that their contents
have been processed by all slaves.
On other systems, you must install a short script yourself that you start from cron (or its equivalent) for handling log files.
For the binary log, you can set the
expire_logs_days system variable
to expire binary log files automatically after a given number of
days (see Section 5.1.4, “Server System Variables”). If you are
using replication, you should set the variable no lower than the
maximum number of days your slaves might lag behind the master.
You can force MySQL to start using new log files by flushing the
logs. Log flushing occurs when you issue a
FLUSH LOGS
statement or execute a mysqladmin flush-logs,
mysqladmin refresh, mysqldump
--flush-logs, or mysqldump
--master-data command. See Section 12.5.6.3, “FLUSH Syntax”,
Section 4.5.2, “mysqladmin — Client for Administering a MySQL Server”, and Section 4.5.4, “mysqldump — A Database Backup Program”. In
addition, the binary log is flushed when its size reaches the
value of the max_binlog_size
system variable.
A log flushing operation does the following:
If general query logging or slow query logging to a log file is enabled, the server closes and reopens the general query log file or slow query log file.
If binary logging is enabled, the server closes the current binary log file and opens a new log file with the next sequence number.
If the server was given an error log file name with the
--log-erroroption, it renames the error log with the suffix-oldand creates a new empty error log file.
The server creates a new binary log file when you flush the logs.
However, it just closes and reopens the general and slow query log
files. To cause new files to be created on Unix, rename the
current logs before flushing them. At flush time, the server will
open new logs with the original names. For example, if the general
and slow query logs are named mysql.log and
mysql-slow.log, you can use a series of
commands like this:
shell>cdshell>mysql-data-directorymv mysql.log mysql.oldshell>mv mysql-slow.log mysql-slow.oldshell>mysqladmin flush-logs
At this point, you can make a backup of
mysql.old and
mysql-slow.log and then remove them from
disk.
On Windows, you can rename the general query log or slow query log
while the server has it open. You cannot rename the error log file
while the server has it open. You must stop the server and rename
the file, and then restart the server to create a new log file.
However, a stop and restart can be avoided by using
FLUSH LOGS, which
causes the server to rename the error log with an
-old suffix and open a new error log.
You can disable the general query log or slow query log at runtime:
SET GLOBAL general_log = 'OFF'; SET GLOBAL slow_query_log = 'OFF';
With the logs disabled, rename the log files externally; for example, from the command line. Then enable the logs again:
SET GLOBAL general_log = 'ON'; SET GLOBAL slow_query_log = 'ON';
This method works on any platform and does not require a server restart.
This section describes some general security issues to be aware of and what you can do to make your MySQL installation more secure against attack or misuse. For information specifically about the access control system that MySQL uses for setting up user accounts and checking database access, see Section 5.4, “The MySQL Access Privilege System”.
For answers to some questions that are often asked about MySQL Server security issues, see Section A.9, “MySQL 5.5 FAQ — Security”.
Anyone using MySQL on a computer connected to the Internet should read this section to avoid the most common security mistakes.
In discussing security, we emphasize the necessity of fully protecting the entire server host (not just the MySQL server) against all types of applicable attacks: eavesdropping, altering, playback, and denial of service. We do not cover all aspects of availability and fault tolerance here.
MySQL uses security based on Access Control Lists (ACLs) for all connections, queries, and other operations that users can attempt to perform. There is also support for SSL-encrypted connections between MySQL clients and servers. Many of the concepts discussed here are not specific to MySQL at all; the same general ideas apply to almost all applications.
When running MySQL, follow these guidelines whenever possible:
Do not ever give anyone (except MySQL
rootaccounts) access to theusertable in themysqldatabase! This is critical.Learn the MySQL access privilege system. The
GRANTandREVOKEstatements are used for controlling access to MySQL. Do not grant more privileges than necessary. Never grant privileges to all hosts.Checklist:
Try
mysql -u root. If you are able to connect successfully to the server without being asked for a password, anyone can connect to your MySQL server as the MySQLrootuser with full privileges! Review the MySQL installation instructions, paying particular attention to the information about setting arootpassword. See Section 2.11.3, “Securing the Initial MySQL Accounts”.Use the
SHOW GRANTSstatement to check which accounts have access to what. Then use theREVOKEstatement to remove those privileges that are not necessary.
Do not store any plain-text passwords in your database. If your computer becomes compromised, the intruder can take the full list of passwords and use them. Instead, use
MD5(),SHA1(), or some other one-way hashing function and store the hash value.Do not choose passwords from dictionaries. Special programs exist to break passwords. Even passwords like “xfish98” are very bad. Much better is “duag98” which contains the same word “fish” but typed one key to the left on a standard QWERTY keyboard. Another method is to use a password that is taken from the first characters of each word in a sentence (for example, “Mary had a little lamb” results in a password of “Mhall”). The password is easy to remember and type, but difficult to guess for someone who does not know the sentence.
MySQL Enterprise MySQL Enterprise subscribers can find an example of a function that checks password security in the Knowledge Base article, Checking Password Complexity. To subscribe to MySQL Enterprise see http://www.mysql.com/products/enterprise/advisors.html.
Invest in a firewall. This protects you from at least 50% of all types of exploits in any software. Put MySQL behind the firewall or in a demilitarized zone (DMZ).
Checklist:
Try to scan your ports from the Internet using a tool such as
nmap. MySQL uses port 3306 by default. This port should not be accessible from untrusted hosts. Another simple way to check whether or not your MySQL port is open is to try the following command from some remote machine, whereserver_hostis the host name or IP number of the host on which your MySQL server runs:shell>
telnetserver_host3306If you get a connection and some garbage characters, the port is open, and should be closed on your firewall or router, unless you really have a good reason to keep it open. If telnet hangs or the connection is refused, the port is blocked, which is how you want it to be.
Do not trust any data entered by users of your applications. They can try to trick your code by entering special or escaped character sequences in Web forms, URLs, or whatever application you have built. Be sure that your application remains secure if a user enters something like “
; DROP DATABASE mysql;”. This is an extreme example, but large security leaks and data loss might occur as a result of hackers using similar techniques, if you do not prepare for them.A common mistake is to protect only string data values. Remember to check numeric data as well. If an application generates a query such as
SELECT * FROM table WHERE ID=234when a user enters the value234, the user can enter the value234 OR 1=1to cause the application to generate the querySELECT * FROM table WHERE ID=234 OR 1=1. As a result, the server retrieves every row in the table. This exposes every row and causes excessive server load. The simplest way to protect from this type of attack is to use single quotes around the numeric constants:SELECT * FROM table WHERE ID='234'. If the user enters extra information, it all becomes part of the string. In a numeric context, MySQL automatically converts this string to a number and strips any trailing nonnumeric characters from it.Sometimes people think that if a database contains only publicly available data, it need not be protected. This is incorrect. Even if it is allowable to display any row in the database, you should still protect against denial of service attacks (for example, those that are based on the technique in the preceding paragraph that causes the server to waste resources). Otherwise, your server becomes unresponsive to legitimate users.
Checklist:
Try to enter single and double quote marks (“
'” and “"”) in all of your Web forms. If you get any kind of MySQL error, investigate the problem right away.Try to modify dynamic URLs by adding
%22(“"”),%23(“#”), and%27(“'”) to them.Try to modify data types in dynamic URLs from numeric to character types using the characters shown in the previous examples. Your application should be safe against these and similar attacks.
Try to enter characters, spaces, and special symbols rather than numbers in numeric fields. Your application should remove them before passing them to MySQL or else generate an error. Passing unchecked values to MySQL is very dangerous!
Check the size of data before passing it to MySQL.
Have your application connect to the database using a user name different from the one you use for administrative purposes. Do not give your applications any access privileges they do not need.
Many application programming interfaces provide a means of escaping special characters in data values. Properly used, this prevents application users from entering values that cause the application to generate statements that have a different effect than you intend:
MySQL C API: Use the
mysql_real_escape_string()API call.MySQL++: Use the
escapeandquotemodifiers for query streams.PHP: Use the
mysql_real_escape_string()function (available as of PHP 4.3.0, prior to that PHP version usemysql_escape_string(), and prior to PHP 4.0.3, useaddslashes()). Note that onlymysql_real_escape_string()is character set-aware; the other functions can be “bypassed” when using (invalid) multi-byte character sets. In PHP 5, you can use themysqliextension, which supports the improved MySQL authentication protocol and passwords, as well as prepared statements with placeholders.Perl DBI: Use placeholders or the
quote()method.Ruby DBI: Use placeholders or the
quote()method.Java JDBC: Use a
PreparedStatementobject and placeholders.
Other programming interfaces might have similar capabilities.
Do not transmit plain (unencrypted) data over the Internet. This information is accessible to everyone who has the time and ability to intercept it and use it for their own purposes. Instead, use an encrypted protocol such as SSL or SSH. MySQL supports internal SSL connections as of version 4.0. Another technique is to use SSH port-forwarding to create an encrypted (and compressed) tunnel for the communication.
Learn to use the tcpdump and strings utilities. In most cases, you can check whether MySQL data streams are unencrypted by issuing a command like the following:
shell>
tcpdump -l -i eth0 -w - src or dst port 3306 | stringsThis works under Linux and should work with small modifications under other systems.
Warning
If you do not see plaintext data, this does not always mean that the information actually is encrypted. If you need high security, you should consult with a security expert.
Passwords occur in several contexts within MySQL. The following sections provide guidelines that enable administrators and end users to keep these passwords secure and avoid exposing them. There is also a discussion of how MySQL uses password hashing internally.
Database administrators should use the following guidelines to keep passwords secure.
MySQL stores passwords for user accounts in the
mysql.user table. Access to this table should
never be granted to any nonadministrative accounts.
Passwords can appear as plain text in SQL statements such as
CREATE USER,
GRANT, and
SET PASSWORD. If these statements
are logged by the MySQL server, the passwords become available
to anyone with access to the logs. This applies to the general
query log, the slow query log, and the binary log (see
Section 5.2, “MySQL Server Logs”). To guard against unwarranted
exposure to log files, they should be located in a directory
that restricts access to only the server and the database
administrator. If you log to tables in the
mysql database, access to the tables should
never be granted to any nonadministrative accounts.
Replication slaves store the password for the replication master
in the master.info file. Access to this
file should be restricted to the database adminstrator.
Database backups that include tables or log files containing passwords should be protected using a restricted access mode.
MySQL users should use the following guidelines to keep passwords secure.
When you run a client program to connect to the MySQL server, it is inadvisable to specify your password in a way that exposes it to discovery by other users. The methods you can use to specify your password when you run client programs are listed here, along with an assessment of the risks of each method. In short, the safest methods are to have the client program prompt for the password or to specify the password in a properly protected option file.
Use a
-poryour_pass--password=option on the command line. For example:your_passshell>
mysql -u francis -pfrankdb_nameThis is convenient but insecure, because your password becomes visible to system status programs such as ps that may be invoked by other users to display command lines. MySQL clients typically overwrite the command-line password argument with zeros during their initialization sequence. However, there is still a brief interval during which the value is visible. Also, on some systems this overwriting strategy is ineffective and the password remains visible to ps. (SystemV Unix systems and perhaps others are subject to this problem.)
If your operating environment is set up to display your current command in the title bar of your terminal window, the password remains visible as long as the command is running, even if the command has scrolled out of view in the window content area.
Use the
-por--passwordoption on the command line with no password value specified. In this case, the client program solicits the password interactively:shell>
mysql -u francis -pEnter password: ********db_nameThe “
*” characters indicate where you enter your password. The password is not displayed as you enter it.It is more secure to enter your password this way than to specify it on the command line because it is not visible to other users. However, this method of entering a password is suitable only for programs that you run interactively. If you want to invoke a client from a script that runs noninteractively, there is no opportunity to enter the password from the keyboard. On some systems, you may even find that the first line of your script is read and interpreted (incorrectly) as your password.
Store your password in an option file. For example, on Unix you can list your password in the
[client]section of the.my.cnffile in your home directory:[client] password=your_pass
To keep the password safe, the file should not be accessible to anyone but yourself. To ensure this, set the file access mode to
400or600. For example:shell>
chmod 600 .my.cnfSection 4.2.3.3, “Using Option Files”, discusses option files in more detail.
Store your password in the
MYSQL_PWDenvironment variable. See Section 2.14, “Environment Variables”.This method of specifying your MySQL password must be considered extremely insecure and should not be used. Some versions of ps include an option to display the environment of running processes. If you set
MYSQL_PWD, your password is exposed to any other user who runs ps. Even on systems without such a version of ps, it is unwise to assume that there are no other methods by which users can examine process environments.
On Unix, the mysql client writes a record of
executed statements to a history file (see
Section 4.5.1, “mysql — The MySQL Command-Line Tool”). By default, this file is named
.mysql_history and is created in your home
directory. Passwords can appear as plain text in SQL statements
such as CREATE USER,
GRANT, and
SET PASSWORD, so if you use these
statements, they are logged in the history file. To keep this
file safe, use a restrictive access mode, the same way as
described earlier for the .my.cnf file.
If your command interpreter is configured to maintain a history,
any file in which the commands are saved will contain MySQL
passwords entered on the command line. For example,
bash uses
~/.bash_history. Any such file should had a
restrictive access mode.
MySQL user accounts are listed in the user
table of the mysql database. Each MySQL
account is assigned a password, although what is stored in the
Password column of the
user table is not the plaintext version of
the password, but a hash value computed from it. Password hash
values are computed by the
PASSWORD() function.
MySQL uses passwords in two phases of client/server communication:
When a client attempts to connect to the server, there is an initial authentication step in which the client must present a password that has a hash value matching the hash value stored in the
usertable for the account that the client wants to use.After the client connects, it can (if it has sufficient privileges) set or change the password hashes for accounts listed in the
usertable. The client can do this by using thePASSWORD()function to generate a password hash, or by using theGRANTorSET PASSWORDstatements.
In other words, the server uses hash values
during authentication when a client first attempts to connect.
The server generates hash values if a
connected client invokes the
PASSWORD() function or uses a
GRANT or SET
PASSWORD statement to set or change a password.
The password hashing mechanism was updated in MySQL 4.1 to provide better security and to reduce the risk of passwords being intercepted. However, this new mechanism is understood only by MySQL 4.1 (and newer) servers and clients, which can result in some compatibility problems. A 4.1 or newer client can connect to a pre-4.1 server, because the client understands both the old and new password hashing mechanisms. However, a pre-4.1 client that attempts to connect to a 4.1 or newer server may run into difficulties. For example, a 3.23 mysql client that attempts to connect to a 5.5 server may fail with the following error message:
shell> mysql -h localhost -u root
Client does not support authentication protocol requested
by server; consider upgrading MySQL client
Another common example of this phenomenon occurs for attempts to
use the older PHP mysql extension after
upgrading to MySQL 4.1 or newer. (See
Section 21.10.6, “Common Problems with MySQL and PHP”.)
The following discussion describes the differences between the
old and new password mechanisms, and what you should do if you
upgrade your server but need to maintain backward compatibility
with pre-4.1 clients. Additional information can be found in
Section B.5.2.4, “Client does not support authentication protocol”. This information is of particular
importance to PHP programmers migrating MySQL databases from
version 4.0 or lower to version 4.1 or higher.
Note
This discussion contrasts 4.1 behavior with pre-4.1 behavior, but the 4.1 behavior described here actually begins with 4.1.1. MySQL 4.1.0 is an “odd” release because it has a slightly different mechanism than that implemented in 4.1.1 and up. Differences between 4.1.0 and more recent versions are described further in MySQL 5.4 Reference Manual.
Prior to MySQL 4.1, password hashes computed by the
PASSWORD() function are 16 bytes
long. Such hashes look like this:
mysql> SELECT PASSWORD('mypass');
+--------------------+
| PASSWORD('mypass') |
+--------------------+
| 6f8c114b58f2ce9e |
+--------------------+
The Password column of the
user table (in which these hashes are stored)
also is 16 bytes long before MySQL 4.1.
As of MySQL 4.1, the PASSWORD()
function has been modified to produce a longer 41-byte hash
value:
mysql> SELECT PASSWORD('mypass');
+-------------------------------------------+
| PASSWORD('mypass') |
+-------------------------------------------+
| *6C8989366EAF75BB670AD8EA7A7FC1176A95CEF4 |
+-------------------------------------------+
Accordingly, the Password column in the
user table also must be 41 bytes long to
store these values:
If you perform a new installation of MySQL 5.5, the
Passwordcolumn is made 41 bytes long automatically.Upgrading from MySQL 4.1 (4.1.1 or later in the 4.1 series) to MySQL 5.5 should not give rise to any issues in this regard because both versions use the same password hashing mechanism. If you wish to upgrade an older release of MySQL to version 5.5, you should upgrade to version 4.1 first, then upgrade the 4.1 installation to 5.5.
A widened Password column can store password
hashes in both the old and new formats. The format of any given
password hash value can be determined two ways:
The obvious difference is the length (16 bytes versus 41 bytes).
A second difference is that password hashes in the new format always begin with a “
*” character, whereas passwords in the old format never do.
The longer password hash format has better cryptographic properties, and client authentication based on long hashes is more secure than that based on the older short hashes.
The differences between short and long password hashes are relevant both for how the server uses passwords during authentication and for how it generates password hashes for connected clients that perform password-changing operations.
The way in which the server uses password hashes during
authentication is affected by the width of the
Password column:
If the column is short, only short-hash authentication is used.
If the column is long, it can hold either short or long hashes, and the server can use either format:
Pre-4.1 clients can connect, although because they know only about the old hashing mechanism, they can authenticate only using accounts that have short hashes.
4.1 and later clients can authenticate using accounts that have short or long hashes.
Even for short-hash accounts, the authentication process is actually a bit more secure for 4.1 and later clients than for older clients. In terms of security, the gradient from least to most secure is:
Pre-4.1 client authenticating with short password hash
4.1 or later client authenticating with short password hash
4.1 or later client authenticating with long password hash
The way in which the server generates password hashes for
connected clients is affected by the width of the
Password column and by the
--old-passwords option. A 4.1 or
later server generates long hashes only if certain conditions
are met: The Password column must be wide
enough to hold long values and the
--old-passwords option must not
be given. These conditions apply as follows:
The
Passwordcolumn must be wide enough to hold long hashes (41 bytes). If the column has not been updated and still has the pre-4.1 width of 16 bytes, the server notices that long hashes cannot fit into it and generates only short hashes when a client performs password-changing operations usingPASSWORD(),GRANT, orSET PASSWORD. This is the behavior that occurs if you have upgraded to 4.1 but have not yet run the mysql_upgrade program to widen thePasswordcolumn.If the
Passwordcolumn is wide, it can store either short or long password hashes. In this case,PASSWORD(),GRANT, andSET PASSWORDgenerate long hashes unless the server was started with the--old-passwordsoption. That option forces the server to generate short password hashes instead.
The purpose of the
--old-passwords option is to
enable you to maintain backward compatibility with pre-4.1
clients under circumstances where the server would otherwise
generate long password hashes. The option doesn't affect
authentication (4.1 and later clients can still use accounts
that have long password hashes), but it does prevent creation of
a long password hash in the user table as the
result of a password-changing operation. Were that to occur, the
account no longer could be used by pre-4.1 clients. Without the
--old-passwords option, the
following undesirable scenario is possible:
An old client connects to an account that has a short password hash.
The client changes its own password. Without
--old-passwords, this results in the account having a long password hash.The next time the old client attempts to connect to the account, it cannot, because the account has a long password hash that requires the new hashing mechanism during authentication. (Once an account has a long password hash in the user table, only 4.1 and later clients can authenticate for it, because pre-4.1 clients do not understand long hashes.)
This scenario illustrates that, if you must support older
pre-4.1 clients, it is dangerous to run a 4.1 or newer server
without using the --old-passwords
option. By running the server with
--old-passwords,
password-changing operations do not generate long password
hashes and thus do not cause accounts to become inaccessible to
older clients. (Those clients cannot inadvertently lock
themselves out by changing their password and ending up with a
long password hash.)
The downside of the
--old-passwords option is that
any passwords you create or change use short hashes, even for
4.1 clients. Thus, you lose the additional security provided by
long password hashes. If you want to create an account that has
a long hash (for example, for use by 4.1 clients), you must do
so while running the server without
--old-passwords.
MySQL Enterprise
Subscribers to the MySQL Enterprise Monitor are automatically
alerted whenever a server is running with the
--old-passwords option. For
more information, see
http://www.mysql.com/products/enterprise/advisors.html.
The following scenarios are possible for running a 4.1 or later server:
Scenario 1: Short
Password column in user table:
Only short hashes can be stored in the
Passwordcolumn.The server uses only short hashes during client authentication.
For connected clients, password hash-generating operations involving
PASSWORD(),GRANT, orSET PASSWORDuse short hashes exclusively. Any change to an account's password results in that account having a short password hash.The
--old-passwordsoption can be used but is superfluous because with a shortPasswordcolumn, the server generates only short password hashes anyway.
Scenario 2: Long
Password column; server not started with
--old-passwords option:
Short or long hashes can be stored in the
Passwordcolumn.4.1 and later clients can authenticate using accounts that have short or long hashes.
Pre-4.1 clients can authenticate only using accounts that have short hashes.
For connected clients, password hash-generating operations involving
PASSWORD(),GRANT, orSET PASSWORDuse long hashes exclusively. A change to an account's password results in that account having a long password hash.
As indicated earlier, a danger in this scenario is that it is
possible for accounts that have a short password hash to become
inaccessible to pre-4.1 clients. A change to such an account's
password made via GRANT,
PASSWORD(), or
SET PASSWORD results in the
account being given a long password hash. From that point on, no
pre-4.1 client can authenticate to that account until the client
upgrades to 4.1.
To deal with this problem, you can change a password in a
special way. For example, normally you use
SET PASSWORD as follows to change
an account password:
SET PASSWORD FOR 'some_user'@'some_host' = PASSWORD('mypass');
To change the password but create a short hash, use the
OLD_PASSWORD() function instead:
SET PASSWORD FOR 'some_user'@'some_host' = OLD_PASSWORD('mypass');
OLD_PASSWORD() is useful for
situations in which you explicitly want to generate a short
hash.
Scenario 3: Long
Password column; 4.1 or newer server started
with --old-passwords option:
Short or long hashes can be stored in the
Passwordcolumn.4.1 and later clients can authenticate for accounts that have short or long hashes (but note that it is possible to create long hashes only when the server is started without
--old-passwords).Pre-4.1 clients can authenticate only for accounts that have short hashes.
For connected clients, password hash-generating operations involving
PASSWORD(),GRANT, orSET PASSWORDuse short hashes exclusively. Any change to an account's password results in that account having a short password hash.
In this scenario, you cannot create accounts that have long
password hashes, because the
--old-passwords option prevents
generation of long hashes. Also, if you create an account with a
long hash before using the
--old-passwords option, changing
the account's password while
--old-passwords is in effect
results in the account being given a short password, causing it
to lose the security benefits of a longer hash.
The disadvantages for these scenarios may be summarized as follows:
In scenario 1, you cannot take advantage of longer hashes that provide more secure authentication.
In scenario 2, accounts with short hashes become inaccessible to
pre-4.1 clients if you change their passwords without explicitly
using OLD_PASSWORD().
In scenario 3, --old-passwords
prevents accounts with short hashes from becoming inaccessible,
but password-changing operations cause accounts with long hashes
to revert to short hashes, and you cannot change them back to
long hashes while --old-passwords
is in effect.
An upgrade to MySQL version 4.1 or later can cause compatibility
issues for applications that use
PASSWORD() to generate passwords
for their own purposes. Applications really should not do this,
because PASSWORD() should be used
only to manage passwords for MySQL accounts. But some
applications use PASSWORD() for
their own purposes anyway.
If you upgrade to 4.1 or later from a pre-4.1 version of MySQL
and run the server under conditions where it generates long
password hashes, an application using
PASSWORD() for its own passwords
breaks. The recommended course of action in such cases is to
modify the application to use another function, such as
SHA1() or
MD5(), to produce hashed values.
If that is not possible, you can use the
OLD_PASSWORD() function, which is
provided for generate short hashes in the old format. However,
you should note that
OLD_PASSWORD() may one day no
longer be supported.
If the server is running under circumstances where it generates
short hashes, OLD_PASSWORD() is
available but is equivalent to
PASSWORD().
PHP programmers migrating their MySQL databases from version 4.0 or lower to version 4.1 or higher should see Section 21.10, “MySQL PHP API”.
When you connect to a MySQL server, you should use a password. The password is not transmitted in clear text over the connection. Password handling during the client connection sequence was upgraded in MySQL 4.1.1 to be very secure. If you are still using pre-4.1.1-style passwords, the encryption algorithm is not as strong as the newer algorithm. With some effort, a clever attacker who can sniff the traffic between the client and the server can crack the password. (See Section 5.3.2.3, “Password Hashing in MySQL”, for a discussion of the different password handling methods.)
MySQL Enterprise The MySQL Enterprise Monitor enforces best practices for maximizing the security of your servers. For more information, see http://www.mysql.com/products/enterprise/advisors.html.
All other information is transferred as text, and can be read by anyone who is able to watch the connection. If the connection between the client and the server goes through an untrusted network, and you are concerned about this, you can use the compressed protocol to make traffic much more difficult to decipher. You can also use MySQL's internal SSL support to make the connection even more secure. See Section 5.5.6, “Using SSL for Secure Connections”. Alternatively, use SSH to get an encrypted TCP/IP connection between a MySQL server and a MySQL client. You can find an Open Source SSH client at http://www.openssh.org/, and a commercial SSH client at http://www.ssh.com/.
To make a MySQL system secure, you should strongly consider the following suggestions:
Require all MySQL accounts to have a password. A client program does not necessarily know the identity of the person running it. It is common for client/server applications that the user can specify any user name to the client program. For example, anyone can use the mysql program to connect as any other person simply by invoking it as
mysql -uifother_userdb_nameother_userhas no password. If all accounts have a password, connecting using another user's account becomes much more difficult.For a discussion of methods for setting passwords, see Section 5.5.5, “Assigning Account Passwords”.
Never run the MySQL server as the Unix
rootuser. This is extremely dangerous, because any user with theFILEprivilege is able to cause the server to create files asroot(for example,~root/.bashrc). To prevent this, mysqld refuses to run asrootunless that is specified explicitly using the--user=rootoption.mysqld can (and should) be run as an ordinary, unprivileged user instead. You can create a separate Unix account named
mysqlto make everything even more secure. Use this account only for administering MySQL. To start mysqld as a different Unix user, add auseroption that specifies the user name in the[mysqld]group of themy.cnfoption file where you specify server options. For example:[mysqld] user=mysql
This causes the server to start as the designated user whether you start it manually or by using mysqld_safe or mysql.server. For more details, see Section 5.3.6, “How to Run MySQL as a Normal User”.
Running mysqld as a Unix user other than
rootdoes not mean that you need to change therootuser name in theusertable. User names for MySQL accounts have nothing to do with user names for Unix accounts.Do not allow the use of symlinks to tables. (This capability can be disabled with the
--skip-symbolic-linksoption.) This is especially important if you run mysqld asroot, because anyone that has write access to the server's data directory then could delete any file in the system! See Section 7.6.1.2, “Using Symbolic Links for Tables on Unix”.Make sure that the only Unix user account with read or write privileges in the database directories is the account that is used for running mysqld.
Do not grant the
PROCESSorSUPERprivilege to nonadministrative users. The output of mysqladmin processlist andSHOW PROCESSLISTshows the text of any statements currently being executed, so any user who is allowed to see the server process list might be able to see statements issued by other users such asUPDATE user SET password=PASSWORD('not_secure').mysqld reserves an extra connection for users who have the
SUPERprivilege, so that a MySQLrootuser can log in and check server activity even if all normal connections are in use.The
SUPERprivilege can be used to terminate client connections, change server operation by changing the value of system variables, and control replication servers.Do not grant the
FILEprivilege to nonadministrative users. Any user that has this privilege can write a file anywhere in the file system with the privileges of the mysqld daemon. To make this a bit safer, files generated withSELECT ... INTO OUTFILEdo not overwrite existing files and are writable by everyone.The
FILEprivilege may also be used to read any file that is world-readable or accessible to the Unix user that the server runs as. With this privilege, you can read any file into a database table. This could be abused, for example, by usingLOAD DATAto load/etc/passwdinto a table, which then can be displayed withSELECT.If you do not trust your DNS, you should use IP numbers rather than host names in the grant tables. In any case, you should be very careful about creating grant table entries using host name values that contain wildcards.
If you want to restrict the number of connections allowed to a single account, you can do so by setting the
max_user_connectionsvariable in mysqld. TheGRANTstatement also supports resource control options for limiting the extent of server use allowed to an account. See Section 12.5.1.3, “GRANTSyntax”.
The following mysqld options affect security:
Table 5.6. Security Option/Variable Summary
| Name | Cmd-Line | Option file | System Var | Status Var | Var Scope | Dynamic |
|---|---|---|---|---|---|---|
| allow-suspicious-udfs | Yes | Yes | ||||
| automatic_sp_privileges | Yes | Global | Yes | |||
| chroot | Yes | Yes | ||||
| des-key-file | Yes | Yes | ||||
| local_infile | Yes | Global | Yes | |||
| local-infile | Yes | Yes | ||||
| - Variable: local_infile | ||||||
| old-passwords | Yes | Yes | Both | Yes | ||
| - Variable: old_passwords | Yes | Both | Yes | |||
| safe-show-database | Yes | Yes | Yes | Global | Yes | |
| safe-user-create | Yes | Yes | ||||
| secure-auth | Yes | Yes | Global | Yes | ||
| - Variable: secure_auth | Yes | Global | Yes | |||
| secure-file-priv | Yes | Yes | Global | No | ||
| - Variable: secure_file_priv | Yes | Global | No | |||
| skip-grant-tables | Yes | Yes | ||||
| skip-name-resolve | Yes | Yes | ||||
| skip-networking | Yes | Yes | Global | No | ||
| - Variable: skip_networking | Yes | Global | No | |||
| skip-show-database | Yes | Yes | Global | No | ||
| - Variable: skip_show_database | Yes | Global | No |
This option controls whether user-defined functions that have only an
xxxsymbol for the main function can be loaded. By default, the option is off and only UDFs that have at least one auxiliary symbol can be loaded; this prevents attempts at loading functions from shared object files other than those containing legitimate UDFs. See Section 22.3.2.6, “User-Defined Function Security Precautions”.If you start the server with
--local-infile=0, clients cannot useLOCALinLOAD DATAstatements. See Section 5.3.5, “Security Issues withLOAD DATA LOCAL”.Force the server to generate short (pre-4.1) password hashes for new passwords. This is useful for compatibility when the server must support older client programs. See Section 5.3.2.3, “Password Hashing in MySQL”.
MySQL Enterprise The MySQL Enterprise Monitor offers advice on the security implications of using this option. For subscription information, see http://www.mysql.com/products/enterprise/advisors.html.
--safe-show-database(OBSOLETE)In previous versions of MySQL, this option caused the
SHOW DATABASESstatement to display the names of only those databases for which the user had some kind of privilege. In MySQL 5.5, this option is no longer available as this is now the default behavior, and there is aSHOW DATABASESprivilege that can be used to control access to database names on a per-account basis. See Section 12.5.1.3, “GRANTSyntax”.If this option is enabled, a user cannot create new MySQL users by using the
GRANTstatement unless the user has theINSERTprivilege for themysql.usertable or any column in the table. If you want a user to have the ability to create new users that have those privileges that the user has the right to grant, you should grant the user the following privilege:GRANT INSERT(user) ON mysql.user TO '
user_name'@'host_name';This ensures that the user cannot change any privilege columns directly, but has to use the
GRANTstatement to give privileges to other users.Disallow authentication for accounts that have old (pre-4.1) passwords.
The mysql client also has a
--secure-authoption, which prevents connections to a server if the server requires a password in old format for the client account.This option limits the effect of the
LOAD_FILE()function and theLOAD DATAandSELECT ... INTO OUTFILEstatements to work only with files in the specified directory.This option causes the server not to use the privilege system at all. This gives anyone with access to the server unrestricted access to all databases. You can cause a running server to start using the grant tables again by executing mysqladmin flush-privileges or mysqladmin reload command from a system shell, or by issuing a MySQL
FLUSH PRIVILEGESstatement. This option also suppresses loading of plugins and user-defined functions (UDFs).Host names are not resolved. All
Hostcolumn values in the grant tables must be IP numbers orlocalhost.Do not allow TCP/IP connections over the network. All connections to mysqld must be made via Unix socket files.
With this option, the
SHOW DATABASESstatement is allowed only to users who have theSHOW DATABASESprivilege, and the statement displays all database names. Without this option,SHOW DATABASESis allowed to all users, but displays each database name only if the user has theSHOW DATABASESprivilege or some privilege for the database. Note that any global privilege is a privilege for the database.Options that begin with
--sslspecify whether to allow clients to connect via SSL and indicate where to find SSL keys and certificates. See Section 5.5.6.3, “SSL Command Options”.
The LOAD DATA statement can load a
file that is located on the server host, or it can load a file
that is located on the client host when the
LOCAL keyword is specified.
There are two potential security issues with supporting the
LOCAL version of LOAD
DATA statements:
The transfer of the file from the client host to the server host is initiated by the MySQL server. In theory, a patched server could be built that would tell the client program to transfer a file of the server's choosing rather than the file named by the client in the
LOAD DATAstatement. Such a server could access any file on the client host to which the client user has read access.In a Web environment where the clients are connecting from a Web server, a user could use
LOAD DATA LOCALto read any files that the Web server process has read access to (assuming that a user could run any command against the SQL server). In this environment, the client with respect to the MySQL server actually is the Web server, not the remote program being run by the user who connects to the Web server.
To deal with these problems, we changed how
LOAD DATA
LOCAL is handled as of MySQL 3.23.49 and MySQL 4.0.2
(4.0.13 on Windows):
By default, all MySQL clients and libraries in binary distributions are compiled with the
--enable-local-infileoption, to be compatible with MySQL 3.23.48 and before.If you build MySQL from source but do not invoke configure with the
--enable-local-infileoption,LOAD DATA LOCALcannot be used by any client unless it is written explicitly to invokemysql_options(... MYSQL_OPT_LOCAL_INFILE, 0). See Section 21.9.3.49, “mysql_options()”.You can disable all
LOAD DATA LOCALcommands from the server side by starting mysqld with the--local-infile=0option.For the mysql command-line client, enable
LOAD DATA LOCALby specifying the--local-infile[=1]option, or disable it with the--local-infile=0option. For mysqlimport, local data file loading is off by default; enable it with the--localor-Loption. In any case, successful use of a local load operation requires that the server is enabled to allow it.If you use
LOAD DATA LOCALin Perl scripts or other programs that read the[client]group from option files, you can add thelocal-infile=1option to that group. However, to keep this from causing problems for programs that do not understandlocal-infile, specify it using theloose-prefix:[client] loose-local-infile=1
If
LOAD DATA LOCALis disabled, either in the server or the client, a client that attempts to issue such a statement receives the following error message:ERROR 1148: The used command is not allowed with this MySQL version
MySQL Enterprise
Security advisors notify subscribers to the MySQL Enterprise
Monitor whenever a server is started with the
--local-infile option enabled.
For more information, see
http://www.mysql.com/products/enterprise/advisors.html.
On Windows, you can run the server as a Windows service using a normal user account.
On Unix, the MySQL server mysqld can be started
and run by any user. However, you should avoid running the server
as the Unix root user for security reasons. To
change mysqld to run as a normal unprivileged
Unix user user_name, you must do the
following:
Stop the server if it is running (use mysqladmin shutdown).
Change the database directories and files so that
user_namehas privileges to read and write files in them (you might need to do this as the Unixrootuser):shell>
chown -Ruser_name/path/to/mysql/datadirIf you do not do this, the server will not be able to access databases or tables when it runs as
user_name.If directories or files within the MySQL data directory are symbolic links,
chown -Rmight not follow symbolic links for you. If it does not, you will also need to follow those links and change the directories and files they point to.Start the server as user
user_name. Another alternative is to start mysqld as the Unixrootuser and use the--user=option. mysqld starts up, then switches to run as the Unix useruser_nameuser_namebefore accepting any connections.To start the server as the given user automatically at system startup time, specify the user name by adding a
useroption to the[mysqld]group of the/etc/my.cnfoption file or themy.cnfoption file in the server's data directory. For example:[mysqld] user=
user_name
If your Unix machine itself isn't secured, you should assign
passwords to the MySQL root accounts in the
grant tables. Otherwise, any user with a login account on that
machine can run the mysql client with a
--user=root option and perform any
operation. (It is a good idea to assign passwords to MySQL
accounts in any case, but especially so when other login accounts
exist on the server host.) See
Section 2.11, “Post-Installation Setup and Testing”.
The primary function of the MySQL privilege system is to
authenticate a user who connects from a given host and to associate
that user with privileges on a database such as
SELECT,
INSERT,
UPDATE, and
DELETE. Additional functionality
includes the ability to have anonymous users and to grant privileges
for MySQL-specific functions such as
LOAD DATA
INFILE and administrative operations.
There are some things that you cannot do with the MySQL privilege system:
You cannot explicitly specify that a given user should be denied access. That is, you cannot explicitly match a user and then refuse the connection.
You cannot specify that a user has privileges to create or drop tables in a database but not to create or drop the database itself.
A password applies globally to an account. You cannot associate a password with a specific object such as a database, table, or routine.
The user interface to the MySQL privilege system consists of SQL
statements such as CREATE USER,
GRANT, and
REVOKE. See
Section 12.5.1, “Account Management Statements”.
Internally, the server stores privilege information in the grant
tables of the mysql database (that is, in the
database named mysql). The MySQL server reads the
contents of these tables into memory when it starts and bases
access-control decisions on the in-memory copies of the grant
tables.
The MySQL privilege system ensures that all users may perform only the operations allowed to them. As a user, when you connect to a MySQL server, your identity is determined by the host from which you connect and the user name you specify. When you issue requests after connecting, the system grants privileges according to your identity and what you want to do.
MySQL considers both your host name and user name in identifying you
because there is no reason to assume that a given user name belongs
to the same person on all hosts. For example, the user
joe who connects from
office.example.com need not be the same person as
the user joe who connects from
home.example.com. MySQL handles this by allowing
you to distinguish users on different hosts that happen to have the
same name: You can grant one set of privileges for connections by
joe from office.example.com,
and a different set of privileges for connections by
joe from home.example.com. To
see what privileges a given account has, use the
SHOW GRANTS statement. For example:
SHOW GRANTS FOR 'joe'@'office.example.com'; SHOW GRANTS FOR 'joe'@'home.example.com';
MySQL access control involves two stages when you run a client program that connects to the server:
Stage 1: The server accepts or rejects the connection based on your identity and whether you can verify your identity by supplying the correct password.
Stage 2: Assuming that you can
connect, the server checks each statement you issue to determine
whether you have sufficient privileges to perform it. For example,
if you try to select rows from a table in a database or drop a table
from the database, the server verifies that you have the
SELECT privilege for the table or the
DROP privilege for the database.
For a more detailed description of what happens during each stage, see Section 5.4.4, “Access Control, Stage 1: Connection Verification”, and Section 5.4.5, “Access Control, Stage 2: Request Verification”.
If your privileges are changed (either by yourself or someone else) while you are connected, those changes do not necessarily take effect immediately for the next statement that you issue. For details about the conditions under which the server reloads the grant tables, see Section 5.4.6, “When Privilege Changes Take Effect”.
For general security-related advice, see Section 5.3, “General Security Issues”. For help in diagnosing privilege-related problems, see Section 5.4.7, “Causes of Access-Denied Errors”.
MySQL provides privileges that apply in different contexts and at different levels of operation:
Administrative privileges enable users to manage operation of the MySQL server. These privileges are global because they are not specific to a particular database.
Database privileges apply to a database and to all objects within it. These privileges can be granted for specific databases, or globally so that they apply to all databases.
Privileges for database objects such as tables, indexes, views, and stored routines can be granted for specific objects within a database, for all objects of a given type within a database (for example, all tables in a database), or globally for all objects of a given type in all databases).
Information about account privileges is stored in the
user, db,
host, tables_priv,
columns_priv, and procs_priv
tables in the mysql database (see
Section 5.4.2, “Privilege System Grant Tables”). The MySQL server reads
the contents of these tables into memory when it starts and
reloads them under the circumstances indicated in
Section 5.4.6, “When Privilege Changes Take Effect”. Access-control decisions are
based on the in-memory copies of the grant tables.
Some releases of MySQL introduce changes to the structure of the grant tables to add new access privileges or features. Whenever you update to a new version of MySQL, you should update your grant tables to make sure that they have the current structure so that you can take advantage of any new capabilities. See Section 4.4.7, “mysql_upgrade — Check Tables for MySQL Upgrade”.
The following table shows the privilege names used at the SQL
level in the GRANT and
REVOKE statements, along with the
column name associated with each privilege in the grant tables and
the context in which the privilege applies.
| Privilege | Column | Context |
CREATE | Create_priv | databases, tables, or indexes |
DROP | Drop_priv | databases or tables |
GRANT OPTION | Grant_priv | databases, tables, or stored routines |
REFERENCES | References_priv | databases or tables |
EVENT | Event_priv | databases |
ALTER | Alter_priv | tables |
DELETE | Delete_priv | tables |
INDEX | Index_priv | tables |
INSERT | Insert_priv | tables |
SELECT | Select_priv | tables |
UPDATE | Update_priv | tables |
CREATE TEMPORARY TABLES | Create_tmp_table_priv | tables |
LOCK TABLES | Lock_tables_priv | tables |
TRIGGER | Trigger_priv | tables |
CREATE VIEW | Create_view_priv | views |
SHOW VIEW | Show_view_priv | views |
ALTER ROUTINE | Alter_routine_priv | stored routines |
CREATE ROUTINE | Create_routine_priv | stored routines |
EXECUTE | Execute_priv | stored routines |
FILE | File_priv | file access on server host |
CREATE TABLESPACE | Create_tablespace_priv | server administration |
CREATE USER | Create_user_priv | server administration |
PROCESS | Process_priv | server administration |
RELOAD | Reload_priv | server administration |
REPLICATION CLIENT | Repl_client_priv | server administration |
REPLICATION SLAVE | Repl_slave_priv | server administration |
SHOW DATABASES | Show_db_priv | server administration |
SHUTDOWN | Shutdown_priv | server administration |
SUPER | Super_priv | server administration |
ALL [PRIVILEGES] | server administration | |
USAGE | server administration |
The following list provides a general description of each privilege available in MySQL. Particular SQL statements might have more specific privilege requirements than indicated here. If so, the description for the statement in question provides the details.
The
ALLorALL PRIVILEGESprivilege specifier is shorthand. It stands for “all privileges available at a given privilege level” (exceptGRANT OPTION). For example, grantingALLat the global or table level grants all global privileges or all table-level privileges.The
ALTERprivilege enables use ofALTER TABLEto change the structure of or rename tables. (ALTER TABLEalso requires theINSERTandCREATEprivileges.)MySQL Enterprise In some circumstances, the
ALTERprivilege is entirely unnecessary — on slaves where there are no nonreplicated tables, for instance. The MySQL Enterprise Monitor notifies subscribers when accounts have inappropriate privileges. For more information, see http://www.mysql.com/products/enterprise/advisors.html.The
ALTER ROUTINEprivilege is needed to alter or drop stored routines (procedures and functions).The
CREATEprivilege enables creation of new databases and tables.The
CREATE ROUTINEprivilege is needed to create stored routines (procedures and functions).The
CREATE TABLESPACEprivilege is needed to create, alter, or drop tablespaces and log file groups.The
CREATE TEMPORARY TABLESprivilege enables the use of the keywordTEMPORARYinCREATE TABLEstatements.The
CREATE USERprivilege enables use ofCREATE USER,DROP USER,RENAME USER, andREVOKE ALL PRIVILEGES.The
CREATE VIEWprivilege enables use ofCREATE VIEW.The
DELETEprivilege enables rows to be deleted from tables in a database.The
DROPprivilege enables you to drop (remove) existing databases, tables, and views. TheDROPprivilege is required in order to use the statementALTER TABLE ... DROP PARTITIONon a partitioned table. TheDROPprivilege is also required forTRUNCATE TABLE. If you grant theDROPprivilege for themysqldatabase to a user, that user can drop the database in which the MySQL access privileges are stored.The
EVENTprivilege is required to create, alter, or drop events for the Event Scheduler.The
EXECUTEprivilege is required to execute stored routines (procedures and functions).The
FILEprivilege gives you permission to read and write files on the server host using theLOAD DATA INFILEandSELECT ... INTO OUTFILEstatements and theLOAD_FILE()function. A user who has theFILEprivilege can read any file on the server host that is either world-readable or readable by the MySQL server. (This implies the user can read any file in any database directory, because the server can access any of those files.) TheFILEprivilege also enables the user to create new files in any directory where the MySQL server has write access. As a security measure, the server will not overwrite existing files.The
GRANT OPTIONprivilege enables you to give to other users or remove from other users those privileges that you yourself possess.The
INDEXprivilege enables you to create or drop (remove) indexes.INDEXapplies to existing tables. If you have theCREATEprivilege for a table, you can include index definitions in theCREATE TABLEstatement.The
INSERTprivilege enables rows to be inserted into tables in a database.INSERTis also required for theANALYZE TABLE,OPTIMIZE TABLE, andREPAIR TABLEtable-maintenance statements.The
LOCK TABLESprivilege enables the use of explicitLOCK TABLESstatements to lock tables for which you have theSELECTprivilege. This includes the use of write locks, which prevents other sessions from reading the locked table.The
PROCESSprivilege pertains to display of information about the threads executing within the server (that is, information about the statements being executed by sessions). The privilege enables use ofSHOW PROCESSLISTor mysqladmin processlist to see threads belonging to other accounts; you can always see your own threads.The
REFERENCESprivilege currently is unused.The
RELOADprivilege enables use of theFLUSHstatement. It also enables mysqladmin commands that are equivalent toFLUSHoperations:flush-hosts,flush-logs,flush-privileges,flush-status,flush-tables,flush-threads,refresh, andreload.The
reloadcommand tells the server to reload the grant tables into memory.flush-privilegesis a synonym forreload. Therefreshcommand closes and reopens the log files and flushes all tables. The otherflush-commands perform functions similar toxxxrefresh, but are more specific and may be preferable in some instances. For example, if you want to flush just the log files,flush-logsis a better choice thanrefresh.The
REPLICATION CLIENTprivilege enables the use ofSHOW MASTER STATUSandSHOW SLAVE STATUS.The
REPLICATION SLAVEprivilege should be granted to accounts that are used by slave servers to connect to the current server as their master. Without this privilege, the slave cannot request updates that have been made to databases on the master server.The
SELECTprivilege enables you to select rows from tables in a database.SELECTstatements require theSELECTprivilege only if they actually retrieve rows from a table. SomeSELECTstatements do not access tables and can be executed without permission for any database. For example, you can useSELECTas a simple calculator to evaluate expressions that make no reference to tables:SELECT 1+1; SELECT PI()*2;
The
SELECTprivilege is also needed for other statements that read column values. For example,SELECTis needed for columns referenced on the right hand side ofcol_name=exprassignment inUPDATEstatements or for columns named in theWHEREclause ofDELETEorUPDATEstatements.The
SHOW DATABASESprivilege enables the account to see database names by issuing theSHOW DATABASEstatement. Accounts that do not have this privilege see only databases for which they have some privileges, and cannot use the statement at all if the server was started with the--skip-show-databaseoption. Note that any global privilege is a privilege for the database.MySQL Enterprise The
SHOW DATABASESprivilege should be granted only to users who need to see all the databases on a MySQL server. Subscribers to the MySQL Enterprise Monitor are alerted when servers are started without the--skip-show-databaseoption. For more information, see http://www.mysql.com/products/enterprise/advisors.html.The
SHOW VIEWprivilege enables use ofSHOW CREATE VIEW.The
SHUTDOWNprivilege enables use of the mysqladmin shutdown command. There is no corresponding SQL statement.The
SUPERprivilege enables an account to useCHANGE MASTER TO,KILLor mysqladmin kill to kill threads belonging to other accounts (you can always kill your own threads),PURGE BINARY LOGS, configuration changes viaSET GLOBALto modify global system variables, the mysqladmin debug command, enabling or disabling logging, performing updates even if theread_onlysystem variable is enabled, starting and stopping replication on slave servers, and allows you to connect (once) even if the connection limit controlled by themax_connectionssystem variable is reached.To create or alter stored functions if binary logging is enabled, you may also need the
SUPERprivilege, as described in Section 18.6, “Binary Logging of Stored Programs”.The
TRIGGERprivilege enables you to create and drop triggers. You must have this privilege for a table to create or drop triggers for that table.The
UPDATEprivilege enables rows to be updated in tables in a database.The
USAGEprivilege specifier stands for “no privileges.” It is used at the global level withGRANTto modify account attributes such as resource limits or SSL characteristics without affecting existing account privileges.
It is a good idea to grant to an account only those privileges
that it needs. You should exercise particular caution in granting
the FILE and administrative
privileges:
The
FILEprivilege can be abused to read into a database table any files that the MySQL server can read on the server host. This includes all world-readable files and files in the server's data directory. The table can then be accessed usingSELECTto transfer its contents to the client host.The
GRANT OPTIONprivilege enables users to give their privileges to other users. Two users that have different privileges and with theGRANT OPTIONprivilege are able to combine privileges.The
ALTERprivilege may be used to subvert the privilege system by renaming tables.The
SHUTDOWNprivilege can be abused to deny service to other users entirely by terminating the server.The
PROCESSprivilege can be used to view the plain text of currently executing statements, including statements that set or change passwords.The
SUPERprivilege can be used to terminate other sessions or change how the server operates.Privileges granted for the
mysqldatabase itself can be used to change passwords and other access privilege information. Passwords are stored encrypted, so a malicious user cannot simply read them to know the plain text password. However, a user with write access to theusertablePasswordcolumn can change an account's password, and then connect to the MySQL server using that account.MySQL Enterprise Accounts with unnecessary global privileges constitute a security risk. Subscribers to the MySQL Enterprise Monitor are automatically alerted to the existence of such accounts. For detailed information, see http://www.mysql.com/products/enterprise/advisors.html.
Normally, you manipulate the contents of the grant tables in the
mysql database indirectly by using statements
such as GRANT and
REVOKE to set up accounts and
control the privileges available to each one. See
Section 12.5.1, “Account Management Statements”. The discussion here
describes the underlying structure of the grant tables and how the
server uses their contents when interacting with clients.
Some tables in the mysql database do not hold
grant information and are discussed elsewhere:
The
eventtable contains information about Event Scheduler events: See Section 18.4, “Using the Event Scheduler”.The
functable contains information about user-defined functions: See Section 22.3, “Adding New Functions to MySQL”.The
help_tables are used for server-side help: See Section 5.1.9, “Server-Side Help”.xxxThe
plugintable contains information about server plugins: See Section 22.2, “The MySQL Plugin Interface”.The
proctable contains information about stored functions and procedures: See Section 18.2, “Using Stored Routines (Procedures and Functions)”.The
serverstable is used by theFEDERATEDstorage engine: See Section 13.11.2.2, “Creating aFEDERATEDTable UsingCREATE SERVER”.The
time_zone_tables contain time zone information: See Section 9.6, “MySQL Server Time Zone Support”.xxxTables with
_login their name are used for logging: See Section 5.2, “MySQL Server Logs”.
Each grant table contains scope columns and privilege columns:
Scope columns determine the scope of each row (entry) in the tables; that is, the context in which the row applies. For example, a
usertable row withHostandUservalues of'thomas.loc.gov'and'bob'would be used for authenticating connections made to the server from the hostthomas.loc.govby a client that specifies a user name ofbob. Similarly, adbtable row withHost,User, andDbcolumn values of'thomas.loc.gov','bob'and'reports'would be used whenbobconnects from the hostthomas.loc.govto access thereportsdatabase. Thetables_privandcolumns_privtables contain scope columns indicating tables or table/column combinations to which each row applies. Theprocs_privscope columns indicate the stored routine to which each row applies.Privilege columns indicate which privileges are granted by a table row; that is, what operations can be performed. The server combines the information in the various grant tables to form a complete description of a user's privileges. Section 5.4.5, “Access Control, Stage 2: Request Verification”, describes the rules that are used to do this.
The server uses the grant tables in the following manner:
The
usertable scope columns determine whether to reject or allow incoming connections. For allowed connections, any privileges granted in theusertable indicate the user's global (superuser) privileges. Any privilege granted in this table applies to all databases on the server.Note
Because any global privilege is considered a privilege for all databases, any global privilege enables a user to see all database names with
SHOW DATABASESor by examining theSCHEMATAtable ofINFORMATION_SCHEMA.The
dbtable scope columns determine which users can access which databases from which hosts. The privilege columns determine which operations are allowed. A privilege granted at the database level applies to the database and to all objects in the database, such as tables and stored programs.The
hosttable is used in conjunction with thedbtable when you want a givendbtable row to apply to several hosts. For example, if you want a user to be able to use a database from several hosts in your network, leave theHostvalue empty in the user'sdbtable row, then populate thehosttable with a row for each of those hosts. This mechanism is described more detail in Section 5.4.5, “Access Control, Stage 2: Request Verification”.The
tables_privandcolumns_privtables are similar to thedbtable, but are more fine-grained: They apply at the table and column levels rather than at the database level. A privilege granted at the table level applies to the table and to all its columns. A privilege granted at the column level applies only to a specific column.The
procs_privtable applies to stored routines. A privilege granted at the routine level applies only to a single routine.
The server uses the user,
db, and host tables in the
mysql database at both the first and second
stages of access control (see Section 5.4, “The MySQL Access Privilege System”).
The columns in the user and
db tables are shown here. The
host table is similar to the
db table but has a specialized use as described
in Section 5.4.5, “Access Control, Stage 2: Request Verification”.
| Table Name | user | db |
| Scope columns | Host | Host |
User | Db | |
Password | User | |
| Privilege columns | Select_priv | Select_priv |
Insert_priv | Insert_priv | |
Update_priv | Update_priv | |
Delete_priv | Delete_priv | |
Index_priv | Index_priv | |
Alter_priv | Alter_priv | |
Create_priv | Create_priv | |
Drop_priv | Drop_priv | |
Grant_priv | Grant_priv | |
Create_view_priv | Create_view_priv | |
Show_view_priv | Show_view_priv | |
Create_routine_priv | Create_routine_priv | |
Alter_routine_priv | Alter_routine_priv | |
Execute_priv | Execute_priv | |
Trigger_priv | Trigger_priv | |
Event_priv | Event_priv | |
Create_tmp_table_priv | Create_tmp_table_priv | |
Lock_tables_priv | Lock_tables_priv | |
References_priv | References_priv | |
Reload_priv | ||
Shutdown_priv | ||
Process_priv | ||
File_priv | ||
Show_db_priv | ||
Super_priv | ||
Repl_slave_priv | ||
Repl_client_priv | ||
Create_user_priv | ||
Create_tablespace_priv | ||
| Security columns | ssl_type | |
ssl_cipher | ||
x509_issuer | ||
x509_subject | ||
| Resource control columns | max_questions | |
max_updates | ||
max_connections | ||
max_user_connections |
During the second stage of access control, the server performs
request verification to make sure that each client has sufficient
privileges for each request that it issues. In addition to the
user, db, and
host grant tables, the server may also consult
the tables_priv and
columns_priv tables for requests that involve
tables. The latter tables provide finer privilege control at the
table and column levels. They have the columns shown in the
following table.
| Table Name | tables_priv | columns_priv |
| Scope columns | Host | Host |
Db | Db | |
User | User | |
Table_name | Table_name | |
Column_name | ||
| Privilege columns | Table_priv | Column_priv |
Column_priv | ||
| Other columns | Timestamp | Timestamp |
Grantor |
The Timestamp and Grantor
columns currently are unused and are discussed no further here.
For verification of requests that involve stored routines, the
server may consult the procs_priv table, which
has the columns shown in the following table.
| Table Name | procs_priv |
| Scope columns | Host |
Db | |
User | |
Routine_name | |
Routine_type | |
| Privilege columns | Proc_priv |
| Other columns | Timestamp |
Grantor |
The Routine_type column is an
ENUM column with values of
'FUNCTION' or 'PROCEDURE' to
indicate the type of routine the row refers to. This column
enables privileges to be granted separately for a function and a
procedure with the same name.
The Timestamp and Grantor
columns currently are unused and are discussed no further here.
Scope columns in the grant tables contain strings. They are declared as shown here; the default value for each is the empty string.
| Column Name | Type |
Host | CHAR(60) |
User | CHAR(16) |
Password | CHAR(41) |
Db | CHAR(64) |
Table_name | CHAR(64) |
Column_name | CHAR(64) |
Routine_name | CHAR(64) |
For access-checking purposes, comparisons of
User, Password,
Db, and Table_name values
are case sensitive. Comparisons of Host,
Column_name, and
Routine_name values are not case sensitive.
In the user, db, and
host tables, each privilege is listed in a
separate column that is declared as ENUM('N','Y') DEFAULT
'N'. In other words, each privilege can be disabled or
enabled, with the default being disabled.
In the tables_priv,
columns_priv, and procs_priv
tables, the privilege columns are declared as
SET columns. Values in these
columns can contain any combination of the privileges controlled
by the table. Only those privileges listed in the column value are
enabled.
| Table Name | Column Name | Possible Set Elements |
tables_priv | Table_priv | 'Select', 'Insert', 'Update', 'Delete', 'Create', 'Drop',
'Grant', 'References', 'Index', 'Alter', 'Create View',
'Show view', 'Trigger' |
tables_priv | Column_priv | 'Select', 'Insert', 'Update', 'References' |
columns_priv | Column_priv | 'Select', 'Insert', 'Update', 'References' |
procs_priv | Proc_priv | 'Execute', 'Alter Routine', 'Grant' |
Administrative privileges (such as
RELOAD or
SHUTDOWN) are specified only in the
user table. Administrative operations are
operations on the server itself and are not database-specific, so
there is no reason to list these privileges in the other grant
tables. Consequently, to determine whether you can perform an
administrative operation, the server need consult only the
user table.
The FILE privilege also is
specified only in the user table. It is not an
administrative privilege as such, but your ability to read or
write files on the server host is independent of the database you
are accessing.
The mysqld server reads the contents of the
grant tables into memory when it starts. You can tell it to reload
the tables by issuing a
FLUSH PRIVILEGES
statement or executing a mysqladmin
flush-privileges or mysqladmin reload
command. Changes to the grant tables take effect as indicated in
Section 5.4.6, “When Privilege Changes Take Effect”.
When you modify an account's privileges, it is a good idea to
verify that the changes set up privileges the way you want. To
check the privileges for a given account, use the
SHOW GRANTS statement (see
Section 12.5.5.22, “SHOW GRANTS Syntax”). For example, to determine the
privileges that are granted to an account with user name and host
name values of bob and
pc84.example.com, use this statement:
SHOW GRANTS FOR 'bob'@'pc84.example.com';
MySQL account names consist of a user name and a host name. This enables creation of accounts for users with the same name who can connect from different hosts. This section describes how to write account names, including special values and wildcard rules.
Within SQL statements such as CREATE
USER, GRANT, and
SET PASSWORD, account names are
written using the following rules:
Syntax for account names is
'.user_name'@'host_name'An account name consisting only of a user name is equivalent to
'. For example,user_name'@'%''me'is equivalent to'me'@'%'.The user name and host name need not be quoted if they are legal as unquoted identifiers. Quotes are necessary to specify a
user_namestring containing special characters (such as “-”), or ahost_namestring containing special characters or wildcard characters (such as “%”); for example,'test-user'@'%.com'.Quote user names and host names as identifiers or as strings, using either backticks (“
`”), single quotes (“'”), or double quotes (“"”).The user name and host name parts, if quoted, must be quoted separately. That is, write
'me'@'localhost', not'me@localhost'; the latter is interpreted as'me@localhost'@'%'.
Account names are stored in grant tables using separate columns for the user name and host name parts:
The
usertable contains one row for each account. TheUserandHostcolumns store the user name and host name. Another column,Password, stores the account password. This table also indicates which global privileges the account has.Other grant tables indicate privileges an account has for databases and objects within databases. These tables have
UserandHostcolumns to store the account name. Each row in these tables associates with the account in theusertable that has the sameUserandHostvalues.
For additional detail about grant table structure, see Section 5.4.2, “Privilege System Grant Tables”.
User names and host names have certain special values or wildcard conventions, as described following.
A user name is either a nonblank value that literally matches the
user name for incoming connection attempts, or a blank value
(empty string) that matches any user name. An account with a blank
user name is an anonymous user. To specify an anonymous user in
SQL statements, use a quoted empty user name part, such as
''@'localhost'.
The host part of an account name can take many forms, and wildcards are allowed:
A host value can be a host name or an IP number.
'localhost'indicates the local host.'127.0.0.1'indicates the loopback interface.You can use the wildcard characters “
%” and “_” in host values. These have the same meaning as for pattern-matching operations performed with theLIKEoperator. For example, a host value of'%'matches any host name, whereas a value of'%.mysql.com'matches any host in themysql.comdomain.'192.168.1.%'matches any host in the 192.168.1 class C network.Because you can use IP wildcard values in host values (for example,
'192.168.1.%'to match every host on a subnet), someone could try to exploit this capability by naming a host192.168.1.somewhere.com. To foil such attempts, MySQL disallows matching on host names that start with digits and a dot. Thus, if you have a host named something like1.2.example.com, its name never matches the host part of account names. An IP wildcard value can match only IP numbers, not host names.MySQL Enterprise An overly broad host specifier such as “
%” constitutes a security risk. The MySQL Enterprise Monitor provides safeguards against this kind of vulnerability. For more information, see http://www.mysql.com/products/enterprise/advisors.html.For host values specified as IP numbers, you can specify a netmask indicating how many address bits to use for the network number. The syntax is
host_ip/netmaskCREATE USER 'david'@'192.58.197.0/255.255.255.0';
This enables
davidto connect from any client host having an IP numberclient_ipfor which the following condition is true:client_ip&netmask=host_ipThat is, for the
CREATE USERstatement just shown:client_ip& 255.255.255.0 = 192.58.197.0IP numbers that satisfy this condition and can connect to the MySQL server are those in the range from
192.58.197.0to192.58.197.255.The netmask can only be used to tell the server to use 8, 16, 24, or 32 bits of the address. Examples:
192.0.0.0/255.0.0.0: anything on the 192 class A network192.168.0.0/255.255.0.0: anything on the 192.168 class B network192.168.1.0/255.255.255.0: anything on the 192.168.1 class C network192.168.1.1: only this specific IP
The following netmask (28 bits) will not work:
192.168.0.1/255.255.255.240
When you attempt to connect to a MySQL server, the server accepts or rejects the connection based on your identity and whether you can verify your identity by supplying the correct password. If not, the server denies access to you completely. Otherwise, the server accepts the connection, and then enters Stage 2 and waits for requests.
Your identity is based on two pieces of information:
The client host from which you connect
Your MySQL user name
Identity checking is performed using the three
user table scope columns
(Host, User, and
Password). The server accepts the connection
only if the Host and User
columns in some user table row match the client
host name and user name and the client supplies the password
specified in that row. The rules for allowable
Host and User values are
given in Section 5.4.3, “Specifying Account Names”.
If the User column value is nonblank, the user
name in an incoming connection must match exactly. If the
User value is blank, it matches any user name.
If the user table row that matches an incoming
connection has a blank user name, the user is considered to be an
anonymous user with no name, not a user with the name that the
client actually specified. This means that a blank user name is
used for all further access checking for the duration of the
connection (that is, during Stage 2).
The Password column can be blank. This is not a
wildcard and does not mean that any password matches. It means
that the user must connect without specifying a password.
Nonblank Password values in the
user table represent encrypted passwords. MySQL
does not store passwords in plaintext form for anyone to see.
Rather, the password supplied by a user who is attempting to
connect is encrypted (using the
PASSWORD() function). The encrypted
password then is used during the connection process when checking
whether the password is correct. (This is done without the
encrypted password ever traveling over the connection.) See
Section 5.5.1, “User Names and Passwords”.
From MySQL's point of view, the encrypted password is the
real password, so you should never give
anyone access to it. In particular, do not give
nonadministrative users read access to tables in the
mysql database.
The following table shows how various combinations of
Host and User values in the
user table apply to incoming connections.
Host Value | User Value | Allowable Connections |
'thomas.loc.gov' | 'fred' | fred, connecting from
thomas.loc.gov |
'thomas.loc.gov' | '' | Any user, connecting from thomas.loc.gov |
'%' | 'fred' | fred, connecting from any host |
'%' | '' | Any user, connecting from any host |
'%.loc.gov' | 'fred' | fred, connecting from any host in the
loc.gov domain |
'x.y.%' | 'fred' | fred, connecting from x.y.net,
x.y.com, x.y.edu,
and so on; this is probably not useful |
'144.155.166.177' | 'fred' | fred, connecting from the host with IP address
144.155.166.177 |
'144.155.166.%' | 'fred' | fred, connecting from any host in the
144.155.166 class C subnet |
'144.155.166.0/255.255.255.0' | 'fred' | Same as previous example |
It is possible for the client host name and user name of an
incoming connection to match more than one row in the
user table. The preceding set of examples
demonstrates this: Several of the entries shown match a connection
from thomas.loc.gov by fred.
When multiple matches are possible, the server must determine which of them to use. It resolves this issue as follows:
Whenever the server reads the
usertable into memory, it sorts the rows.When a client attempts to connect, the server looks through the rows in sorted order.
The server uses the first row that matches the client host name and user name.
To see how this works, suppose that the user
table looks like this:
+-----------+----------+- | Host | User | ... +-----------+----------+- | % | root | ... | % | jeffrey | ... | localhost | root | ... | localhost | | ... +-----------+----------+-
When the server reads the table into memory, it orders the rows
with the most-specific Host values first.
Literal host names and IP numbers are the most specific. (The
specificity if a literal IP number is not affected by whether it
has a netmask, so 192.168.1.13 and
192.168.1.0/255.255.255.0 are considered
equally specific.) The pattern '%' means
“any host” and is least specific. Rows with the same
Host value are ordered with the most-specific
User values first (a blank
User value means “any user” and is
least specific). For the user table just shown,
the result after sorting looks like this:
+-----------+----------+- | Host | User | ... +-----------+----------+- | localhost | root | ... | localhost | | ... | % | jeffrey | ... | % | root | ... +-----------+----------+-
When a client attempts to connect, the server looks through the
sorted rows and uses the first match found. For a connection from
localhost by jeffrey, two of
the rows from the table match: the one with
Host and User values of
'localhost' and '', and the
one with values of '%' and
'jeffrey'. The 'localhost'
row appears first in sorted order, so that is the one the server
uses.
Here is another example. Suppose that the user
table looks like this:
+----------------+----------+- | Host | User | ... +----------------+----------+- | % | jeffrey | ... | thomas.loc.gov | | ... +----------------+----------+-
The sorted table looks like this:
+----------------+----------+- | Host | User | ... +----------------+----------+- | thomas.loc.gov | | ... | % | jeffrey | ... +----------------+----------+-
A connection by jeffrey from
thomas.loc.gov is matched by the first row,
whereas a connection by jeffrey from any host
is matched by the second.
Note
It is a common misconception to think that, for a given user
name, all rows that explicitly name that user are used first
when the server attempts to find a match for the connection.
This is not true. The preceding example illustrates this, where
a connection from thomas.loc.gov by
jeffrey is first matched not by the row
containing 'jeffrey' as the
User column value, but by the row with no
user name. As a result, jeffrey is
authenticated as an anonymous user, even though he specified a
user name when connecting.
If you are able to connect to the server, but your privileges are
not what you expect, you probably are being authenticated as some
other account. To find out what account the server used to
authenticate you, use the
CURRENT_USER() function. (See
Section 11.11.3, “Information Functions”.) It returns a value in
user_name@host_nameUser and
Host values from the matching
user table row. Suppose that
jeffrey connects and issues the following
query:
mysql> SELECT CURRENT_USER();
+----------------+
| CURRENT_USER() |
+----------------+
| @localhost |
+----------------+
The result shown here indicates that the matching
user table row had a blank
User column value. In other words, the server
is treating jeffrey as an anonymous user.
Another way to diagnose authentication problems is to print out
the user table and sort it by hand to see where
the first match is being made.
After you establish a connection, the server enters Stage 2 of
access control. For each request that you issue via that
connection, the server determines what operation you want to
perform, then checks whether you have sufficient privileges to do
so. This is where the privilege columns in the grant tables come
into play. These privileges can come from any of the
user, db,
host, tables_priv,
columns_priv, or procs_priv
tables. (You may find it helpful to refer to
Section 5.4.2, “Privilege System Grant Tables”, which lists the columns
present in each of the grant tables.)
The user table grants privileges that are
assigned to you on a global basis and that apply no matter what
the default database is. For example, if the
user table grants you the
DELETE privilege, you can delete
rows from any table in any database on the server host! In other
words, user table privileges are superuser
privileges. It is wise to grant privileges in the
user table only to superusers such as database
administrators. For other users, you should leave all privileges
in the user table set to 'N'
and grant privileges at more specific levels only. You can grant
privileges for particular databases, tables, columns, or routines.
The db and host tables grant
database-specific privileges. Values in the scope columns of these
tables can take the following forms:
A blank
Uservalue in thedbtable matches the anonymous user. A nonblank value matches literally; there are no wildcards in user names.The wildcard characters “
%” and “_” can be used in theHostandDbcolumns of either table. These have the same meaning as for pattern-matching operations performed with theLIKEoperator. If you want to use either character literally when granting privileges, you must escape it with a backslash. For example, to include the underscore character (“_”) as part of a database name, specify it as “\_” in theGRANTstatement.A
'%'Hostvalue in thedbtable means “any host.” A blankHostvalue in thedbtable means “consult thehosttable for further information” (a process that is described later in this section).A
'%'or blankHostvalue in thehosttable means “any host.”A
'%'or blankDbvalue in either table means “any database.”
The server reads the db and
host tables into memory and sorts them at the
same time that it reads the user table. The
server sorts the db table based on the
Host, Db, and
User scope columns, and sorts the
host table based on the Host
and Db scope columns. As with the
user table, sorting puts the most-specific
values first and least-specific values last, and when the server
looks for matching entries, it uses the first match that it finds.
The tables_priv,
columns_priv, and procs_priv
tables grant table-specific, column-specific, and routine-specific
privileges. Values in the scope columns of these tables can take
the following forms:
The wildcard characters “
%” and “_” can be used in theHostcolumn. These have the same meaning as for pattern-matching operations performed with theLIKEoperator.A
'%'or blankHostvalue means “any host.”The
Db,Table_name,Column_name, andRoutine_namecolumns cannot contain wildcards or be blank.
The server sorts the tables_priv,
columns_priv, and procs_priv
tables based on the Host,
Db, and User columns. This
is similar to db table sorting, but simpler
because only the Host column can contain
wildcards.
The server uses the sorted tables to verify each request that it
receives. For requests that require administrative privileges such
as SHUTDOWN or
RELOAD, the server checks only the
user table row because that is the only table
that specifies administrative privileges. The server grants access
if the row allows the requested operation and denies access
otherwise. For example, if you want to execute mysqladmin
shutdown but your user table row
doesn't grant the SHUTDOWN
privilege to you, the server denies access without even checking
the db or host tables. (They
contain no Shutdown_priv column, so there is no
need to do so.)
For database-related requests
(INSERT,
UPDATE, and so on), the server
first checks the user's global (superuser) privileges by looking
in the user table row. If the row allows the
requested operation, access is granted. If the global privileges
in the user table are insufficient, the server
determines the user's database-specific privileges by checking the
db and host tables:
The server looks in the
dbtable for a match on theHost,Db, andUsercolumns. TheHostandUsercolumns are matched to the connecting user's host name and MySQL user name. TheDbcolumn is matched to the database that the user wants to access. If there is no row for theHostandUser, access is denied.If there is a matching
dbtable row and itsHostcolumn is not blank, that row defines the user's database-specific privileges.If the matching
dbtable row'sHostcolumn is blank, it signifies that thehosttable enumerates which hosts should be allowed access to the database. In this case, a further lookup is done in thehosttable to find a match on theHostandDbcolumns. If nohosttable row matches, access is denied. If there is a match, the user's database-specific privileges are computed as the intersection (not the union!) of the privileges in thedbandhosttable entries; that is, the privileges that are'Y'in both entries. (This way you can grant general privileges in thedbtable row and then selectively restrict them on a host-by-host basis using thehosttable entries.)
After determining the database-specific privileges granted by the
db and host table entries,
the server adds them to the global privileges granted by the
user table. If the result allows the requested
operation, access is granted. Otherwise, the server successively
checks the user's table and column privileges in the
tables_priv and columns_priv
tables, adds those to the user's privileges, and allows or denies
access based on the result. For stored-routine operations, the
server uses the procs_priv table rather than
tables_priv and
columns_priv.
Expressed in boolean terms, the preceding description of how a user's privileges are calculated may be summarized like this:
global privileges OR (database privileges AND host privileges) OR table privileges OR column privileges OR routine privileges
It may not be apparent why, if the global user
row privileges are initially found to be insufficient for the
requested operation, the server adds those privileges to the
database, table, and column privileges later. The reason is that a
request might require more than one type of privilege. For
example, if you execute an
INSERT INTO ...
SELECT statement, you need both the
INSERT and the
SELECT privileges. Your privileges
might be such that the user table row grants
one privilege and the db table row grants the
other. In this case, you have the necessary privileges to perform
the request, but the server cannot tell that from either table by
itself; the privileges granted by the entries in both tables must
be combined.
The host table is not affected by the
GRANT or
REVOKE statements, so it is unused
in most MySQL installations. If you modify it directly, you can
use it for some specialized purposes, such as to maintain a list
of secure servers on the local network that are granted all
privileges.
You can also use the host table to indicate
hosts that are not secure. Suppose that you
have a machine public.your.domain that is
located in a public area that you do not consider secure. You can
enable access to all hosts on your network except that machine by
using host table entries like this:
+--------------------+----+- | Host | Db | ... +--------------------+----+- | public.your.domain | % | ... (all privileges set to 'N') | %.your.domain | % | ... (all privileges set to 'Y') +--------------------+----+-
When mysqld starts, it reads all grant table contents into memory. The in-memory tables become effective for access control at that point.
If you modify the grant tables indirectly using account-management
statements such as GRANT,
REVOKE, or SET
PASSWORD, the server notices these changes and loads the
grant tables into memory again immediately.
If you modify the grant tables directly using statements such as
INSERT,
UPDATE, or
DELETE, your changes have no effect
on privilege checking until you either restart the server or tell
it to reload the tables. If you change the grant tables directly
but forget to reload them, your changes have no
effect until you restart the server. This may leave you
wondering why your changes do not seem to make any difference!
To tell the sever to reload the grant tables, perform a
flush-privileges operation. This can be done by issuing a
FLUSH PRIVILEGES
statement or by executing a mysqladmin
flush-privileges or mysqladmin reload
command.
When the server reloads the grant tables, privileges for each existing client connection are affected as follows:
Table and column privilege changes take effect with the client's next request.
Database privilege changes take effect the next time the client executes a
USEstatement.db_nameNote
Client applications may cache the database name; thus, this effect may not be visible to them without actually changing to a different database or flushing the privileges.
Global privileges and passwords are unaffected for a connected client. These changes take effect only for subsequent connections.
If the server is started with the
--skip-grant-tables option, it does
not read the grant tables or implement any access control. Anyone
can connect and do anything. To cause a server thus started to
read the tables and enable access checking, flush the privileges.
If you encounter problems when you try to connect to the MySQL server, the following items describe some courses of action you can take to correct the problem.
Make sure that the server is running. If it is not, clients cannot connect to it. For example, if an attempt to connect to the server fails with a message such as one of those following, one cause might be that the server is not running:
shell>
mysqlERROR 2003: Can't connect to MySQL server on 'host_name' (111) shell>mysqlERROR 2002: Can't connect to local MySQL server through socket '/tmp/mysql.sock' (111)It might be that the server is running, but you are trying to connect using a TCP/IP port, named pipe, or Unix socket file different from the one on which the server is listening. To correct this when you invoke a client program, specify a
--portoption to indicate the proper port number, or a--socketoption to indicate the proper named pipe or Unix socket file. To find out where the socket file is, you can use this command:shell>
netstat -ln | grep mysqlMake sure that the server has not been configured to ignore network connections or (if you are attempting to connect remotely) that it has not been configured to listen only locally on its network interfaces. If the server was started with
--skip-networking, it will not accept TCP/IP connections at all. If the server was started with--bind-address=127.0.0.1, it will listen for TCP/IP connections only locally on the loopback interface and will not accept remote connections.Check to make sure that there is no firewall blocking access to MySQL. Your firewall may be configured on the basis of the application being executed, or the port number used by MySQL for communication (3306 by default). Under Linux or Unix, check your IP tables (or similar) configuration to ensure that the port has not been blocked. Under Windows, applications such as ZoneAlarm or the Windows XP personal firewall may need to be configured not to block the MySQL port.
The grant tables must be properly set up so that the server can use them for access control. For some distribution types (such as binary distributions on Windows, or RPM distributions on Linux), the installation process initializes the
mysqldatabase containing the grant tables. For distributions that do not do this, you must initialize the grant tables manually by running the mysql_install_db script. For details, see Section 2.11.2, “Unix Post-Installation Procedures”.To determine whether you need to initialize the grant tables, look for a
mysqldirectory under the data directory. (The data directory normally is nameddataorvarand is located under your MySQL installation directory.) Make sure that you have a file nameduser.MYDin themysqldatabase directory. If not, execute the mysql_install_db script. After running this script and starting the server, test the initial privileges by executing this command:shell>
mysql -u root testThe server should let you connect without error.
After a fresh installation, you should connect to the server and set up your users and their access permissions:
shell>
mysql -u root mysqlThe server should let you connect because the MySQL
rootuser has no password initially. That is also a security risk, so setting the password for therootaccounts is something you should do while you're setting up your other MySQL accounts. For instructions on setting the initial passwords, see Section 2.11.3, “Securing the Initial MySQL Accounts”.MySQL Enterprise The MySQL Enterprise Monitor enforces security-related best practices. For example, subscribers are alerted whenever there is any account without a password. For more information, see http://www.mysql.com/products/enterprise/advisors.html.
If you have updated an existing MySQL installation to a newer version, did you run the mysql_upgrade script? If not, do so. The structure of the grant tables changes occasionally when new capabilities are added, so after an upgrade you should always make sure that your tables have the current structure. For instructions, see Section 4.4.7, “mysql_upgrade — Check Tables for MySQL Upgrade”.
If a client program receives the following error message when it tries to connect, it means that the server expects passwords in a newer format than the client is capable of generating:
shell>
mysqlClient does not support authentication protocol requested by server; consider upgrading MySQL clientFor information on how to deal with this, see Section 5.3.2.3, “Password Hashing in MySQL”, and Section B.5.2.4, “
Client does not support authentication protocol”.Remember that client programs use connection parameters specified in option files or environment variables. If a client program seems to be sending incorrect default connection parameters when you have not specified them on the command line, check any applicable option files and your environment. For example, if you get
Access deniedwhen you run a client without any options, make sure that you have not specified an old password in any of your option files!You can suppress the use of option files by a client program by invoking it with the
--no-defaultsoption. For example:shell>
mysqladmin --no-defaults -u root versionThe option files that clients use are listed in Section 4.2.3.3, “Using Option Files”. Environment variables are listed in Section 2.14, “Environment Variables”.
If you get the following error, it means that you are using an incorrect
rootpassword:shell>
mysqladmin -u root -pAccess denied for user 'root'@'localhost' (using password: YES)xxxxverIf the preceding error occurs even when you have not specified a password, it means that you have an incorrect password listed in some option file. Try the
--no-defaultsoption as described in the previous item.For information on changing passwords, see Section 5.5.5, “Assigning Account Passwords”.
If you have lost or forgotten the
rootpassword, see Section B.5.4.1, “How to Reset the Root Password”.If you change a password by using
SET PASSWORD,INSERT, orUPDATE, you must encrypt the password using thePASSWORD()function. If you do not usePASSWORD()for these statements, the password will not work. For example, the following statement assigns a password, but fails to encrypt it, so the user is not able to connect afterward:SET PASSWORD FOR 'abe'@'
host_name' = 'eagle';Instead, set the password like this:
SET PASSWORD FOR 'abe'@'
host_name' = PASSWORD('eagle');The
PASSWORD()function is unnecessary when you specify a password using theCREATE USERorGRANTstatements or the mysqladmin password command. Each of those automatically usesPASSWORD()to encrypt the password. See Section 5.5.5, “Assigning Account Passwords”, and Section 12.5.1.1, “CREATE USERSyntax”.localhostis a synonym for your local host name, and is also the default host to which clients try to connect if you specify no host explicitly.To avoid this problem on such systems, you can use a
--host=127.0.0.1option to name the server host explicitly. This will make a TCP/IP connection to the local mysqld server. You can also use TCP/IP by specifying a--hostoption that uses the actual host name of the local host. In this case, the host name must be specified in ausertable row on the server host, even though you are running the client program on the same host as the server.The
Access deniederror message tells you who you are trying to log in as, the client host from which you are trying to connect, and whether you were using a password. Normally, you should have one row in theusertable that exactly matches the host name and user name that were given in the error message. For example, if you get an error message that containsusing password: NO, it means that you tried to log in without a password.If you get an
Access deniederror when trying to connect to the database withmysql -u, you may have a problem with theuser_nameusertable. Check this by executingmysql -u root mysqland issuing this SQL statement:SELECT * FROM user;
The result should include a row with the
HostandUsercolumns matching your client's host name and your MySQL user name.If the following error occurs when you try to connect from a host other than the one on which the MySQL server is running, it means that there is no row in the
usertable with aHostvalue that matches the client host:Host ... is not allowed to connect to this MySQL server
You can fix this by setting up an account for the combination of client host name and user name that you are using when trying to connect.
If you do not know the IP number or host name of the machine from which you are connecting, you should put a row with
'%'as theHostcolumn value in theusertable. After trying to connect from the client machine, use aSELECT USER()query to see how you really did connect. Then change the'%'in theusertable row to the actual host name that shows up in the log. Otherwise, your system is left insecure because it allows connections from any host for the given user name.On Linux, another reason that this error might occur is that you are using a binary MySQL version that is compiled with a different version of the
glibclibrary than the one you are using. In this case, you should either upgrade your operating system orglibc, or download a source distribution of MySQL version and compile it yourself. A source RPM is normally trivial to compile and install, so this is not a big problem.If you specify a host name when trying to connect, but get an error message where the host name is not shown or is an IP number, it means that the MySQL server got an error when trying to resolve the IP number of the client host to a name:
shell>
mysqladmin -u root -pAccess denied for user 'root'@'' (using password: YES)xxxx-hsome_hostnameverIf you try to connect as
rootand get the following error, it means that you do not have a row in theusertable with aUsercolumn value of'root'and that mysqld cannot resolve the host name for your client:Access denied for user ''@'unknown'
These errors indicate a DNS problem. To fix it, execute mysqladmin flush-hosts to reset the internal DNS host name cache. See Section 7.5.11, “How MySQL Uses DNS”.
Some permanent solutions are:
Determine what is wrong with your DNS server and fix it.
Specify IP numbers rather than host names in the MySQL grant tables.
Put an entry for the client machine name in
/etc/hostson Unix or\windows\hostson Windows.Start mysqld with the
--skip-name-resolveoption.Start mysqld with the
--skip-host-cacheoption.On Unix, if you are running the server and the client on the same machine, connect to
localhost. Unix connections tolocalhostuse a Unix socket file rather than TCP/IP.On Windows, if you are running the server and the client on the same machine and the server supports named pipe connections, connect to the host name
.(period). Connections to.use a named pipe rather than TCP/IP.
If
mysql -u root testworks butmysql -hresults inyour_hostname-u root testAccess denied(whereyour_hostnameis the actual host name of the local host), you may not have the correct name for your host in theusertable. A common problem here is that theHostvalue in theusertable row specifies an unqualified host name, but your system's name resolution routines return a fully qualified domain name (or vice versa). For example, if you have an entry with host'pluto'in theusertable, but your DNS tells MySQL that your host name is'pluto.example.com', the entry does not work. Try adding an entry to theusertable that contains the IP number of your host as theHostcolumn value. (Alternatively, you could add an entry to theusertable with aHostvalue that contains a wildcard; for example,'pluto.%'. However, use ofHostvalues ending with “%” is insecure and is not recommended!)If
mysql -uworks butuser_nametestmysql -udoes not, you have not granted access to the given user for the database nameduser_nameother_dbother_db.If
mysql -uworks when executed on the server host, butuser_namemysql -hdoes not work when executed on a remote client host, you have not enabled access to the server for the given user name from the remote host.host_name-uuser_nameIf you cannot figure out why you get
Access denied, remove from theusertable all entries that haveHostvalues containing wildcards (entries that contain'%'or'_'characters). A very common error is to insert a new entry withHost='%'andUser=', thinking that this allows you to specifysome_user'localhostto connect from the same machine. The reason that this does not work is that the default privileges include an entry withHost='localhost'andUser=''. Because that entry has aHostvalue'localhost'that is more specific than'%', it is used in preference to the new entry when connecting fromlocalhost! The correct procedure is to insert a second entry withHost='localhost'andUser=', or to delete the entry withsome_user'Host='localhost'andUser=''. After deleting the entry, remember to issue aFLUSH PRIVILEGESstatement to reload the grant tables. See also Section 5.4.4, “Access Control, Stage 1: Connection Verification”.If you are able to connect to the MySQL server, but get an
Access deniedmessage whenever you issue aSELECT ... INTO OUTFILEorLOAD DATA INFILEstatement, your entry in theusertable does not have theFILEprivilege enabled.If you change the grant tables directly (for example, by using
INSERT,UPDATE, orDELETEstatements) and your changes seem to be ignored, remember that you must execute aFLUSH PRIVILEGESstatement or a mysqladmin flush-privileges command to cause the server to reload the privilege tables. Otherwise, your changes have no effect until the next time the server is restarted. Remember that after you change therootpassword with anUPDATEcommand, you will not need to specify the new password until after you flush the privileges, because the server will not know you've changed the password yet!If your privileges seem to have changed in the middle of a session, it may be that a MySQL administrator has changed them. Reloading the grant tables affects new client connections, but it also affects existing connections as indicated in Section 5.4.6, “When Privilege Changes Take Effect”.
If you have access problems with a Perl, PHP, Python, or ODBC program, try to connect to the server with
mysql -uoruser_namedb_namemysql -u. If you are able to connect using the mysql client, the problem lies with your program, not with the access privileges. (There is no space betweenuser_name-pyour_passdb_name-pand the password; you can also use the--password=syntax to specify the password. If you use theyour_pass-por--passwordoption with no password value, MySQL prompts you for the password.)For testing purposes, start the mysqld server with the
--skip-grant-tablesoption. Then you can change the MySQL grant tables and use the mysqlaccess script to check whether your modifications have the desired effect. When you are satisfied with your changes, execute mysqladmin flush-privileges to tell the mysqld server to reload the privileges. This enables you to begin using the new grant table contents without stopping and restarting the server.If you get the following error, you may have a problem with the
dborhosttable:Access to database denied
If the entry selected from the
dbtable has an empty value in theHostcolumn, make sure that there are one or more corresponding entries in thehosttable specifying which hosts thedbtable entry applies to. This problem occurs infrequently because thehosttable is rarely used.If everything else fails, start the mysqld server with a debugging option (for example,
--debug=d,general,query). This prints host and user information about attempted connections, as well as information about each command issued. See MySQL Internals: Porting.If you have any other problems with the MySQL grant tables and feel you must post the problem to the mailing list, always provide a dump of the MySQL grant tables. You can dump the tables with the mysqldump mysql command. To file a bug report, see the instructions at Section 1.7, “How to Report Bugs or Problems”. In some cases, you may need to restart mysqld with
--skip-grant-tablesto run mysqldump.
This section describes how to set up accounts for clients of your MySQL server. It discusses the following topics:
The meaning of account names and passwords as used in MySQL and how that compares to names and passwords used by your operating system
How to set up new accounts and remove existing accounts
How to change passwords
Guidelines for using passwords securely
How to use secure connections with SSL
See also Section 12.5.1, “Account Management Statements”, which describes the syntax and use for all user-management SQL statements.
A MySQL account is defined in terms of a user name and the client host or hosts from which the user can connect to the server. The account also has a password. There are several distinctions between the way user names and passwords are used by MySQL and the way they are used by your operating system:
User names, as used by MySQL for authentication purposes, have nothing to do with user names (login names) as used by Windows or Unix. On Unix, most MySQL clients by default try to log in using the current Unix user name as the MySQL user name, but that is for convenience only. The default can be overridden easily, because client programs allow any user name to be specified with a
-uor--useroption. Because this means that anyone can attempt to connect to the server using any user name, you cannot make a database secure in any way unless all MySQL accounts have passwords. Anyone who specifies a user name for an account that has no password is able to connect successfully to the server.MySQL user names can be up to 16 characters long. Operating system user names, because they are completely unrelated to MySQL user names, may be of a different maximum length. For example, Unix user names typically are limited to eight characters.
Warning
The limit on MySQL user name length is hard-coded in the MySQL servers and clients, and trying to circumvent it by modifying the definitions of the tables in the
mysqldatabase does not work.You should never alter any of the tables in the
mysqldatabase in any manner whatsoever except by means of the procedure that is described in Section 4.4.7, “mysql_upgrade — Check Tables for MySQL Upgrade”. Attempting to redefine MySQL's system tables in any other fashion results in undefined (and unsupported!) behavior.MySQL passwords have nothing to do with passwords for logging in to your operating system. There is no necessary connection between the password you use to log in to a Windows or Unix machine and the password you use to access the MySQL server on that machine.
MySQL encrypts passwords using its own algorithm. This encryption is the same as that implemented by the
PASSWORD()SQL function but differs from that used during the Unix login process. Unix password encryption is the same as that implemented by theENCRYPT()SQL function. See the descriptions of thePASSWORD()andENCRYPT()functions in Section 11.11.2, “Encryption and Compression Functions”.From version 4.1 on, MySQL employs a stronger authentication method that has better password protection during the connection process than in earlier versions. It is secure even if TCP/IP packets are sniffed or the
mysqldatabase is captured. (In earlier versions, even though passwords are stored in encrypted form in theusertable, knowledge of the encrypted password value could be used to connect to the MySQL server.) Section 5.3.2.3, “Password Hashing in MySQL”, discusses password encryption further.
When you install MySQL, the grant tables are populated with an
initial set of accounts. These accounts have names and access
privileges that are described in
Section 2.11.3, “Securing the Initial MySQL Accounts”, which also discusses how to
assign passwords to them. Thereafter, you normally set up, modify,
and remove MySQL accounts using statements such as
GRANT and
REVOKE. See
Section 12.5.1, “Account Management Statements”.
When you connect to a MySQL server with a command-line client, you should specify the user name and password for the account that you want to use:
shell> mysql --user=monty --password=guess db_name
If you prefer short options, the command looks like this:
shell> mysql -u monty -pguess db_name
There must be no space between the
-p option and the following password value. For
additional information about specifying user names, passwords, and
other connection parameters, see Section 4.2.2, “Connecting to the MySQL Server”.
You can create MySQL accounts in two ways:
By using statements intended for creating accounts, such as
CREATE USERorGRANT. These statements cause the server to make appropriate modifications to the grant tables.By manipulating the MySQL grant tables directly with statements such as
INSERT,UPDATE, orDELETE.
The preferred method is to use account-creation statements because
they are more concise and less error-prone than manipulating the
grant tables directly. CREATE USER
and GRANT are described in
Section 12.5.1, “Account Management Statements”.
Another option for creating accounts is to use one of several
available third-party programs that offer capabilities for MySQL
account administration. phpMyAdmin is one such
program.
The following examples show how to use the
mysql client program to set up new accounts.
These examples assume that privileges have been set up according
to the defaults described in Section 2.11.3, “Securing the Initial MySQL Accounts”.
This means that to make changes, you must connect to the MySQL
server as the MySQL root user, and the
root account must have the
INSERT privilege for the
mysql database and the
RELOAD administrative privilege.
As noted in the examples where appropriate, some of the statements
will fail if the server's SQL mode has been set to enable certain
restrictions. In particular, strict mode
(STRICT_TRANS_TABLES,
STRICT_ALL_TABLES) and
NO_AUTO_CREATE_USER will prevent
the server from accepting some of the statements. Workarounds are
indicated for these cases. For more information about SQL modes
and their effect on grant table manipulation, see
Section 5.1.8, “Server SQL Modes”, and Section 12.5.1.3, “GRANT Syntax”.
First, use the mysql program to connect to the
server as the MySQL root user:
shell> mysql --user=root mysql
If you have assigned a password to the root
account, you'll also need to supply a --password
or -p option, both for this
mysql command and for those later in this
section.
After connecting to the server as root, you can
add new accounts. The following statements use
GRANT to set up four new accounts:
mysql>CREATE USER 'monty'@'localhost' IDENTIFIED BY 'some_pass';mysql>GRANT ALL PRIVILEGES ON *.* TO 'monty'@'localhost'->WITH GRANT OPTION;mysql>CREATE USER 'monty'@'%' IDENTIFIED BY 'some_pass';mysql>GRANT ALL PRIVILEGES ON *.* TO 'monty'@'%'->WITH GRANT OPTION;mysql>CREATE USER 'admin'@'localhost';mysql>GRANT RELOAD,PROCESS ON *.* TO 'admin'@'localhost';mysql>CREATE USER 'dummy'@'localhost';
The accounts created by these statements have the following properties:
Two of the accounts have a user name of
montyand a password ofsome_pass. Both accounts are superuser accounts with full privileges to do anything. The'monty'@'localhost'account can be used only when connecting from the local host. The'monty'@'%'account uses the'%'wildcard for the host part, so it can be used to connect from any host.It is necessary to have both accounts for
montyto be able to connect from anywhere asmonty. Without thelocalhostaccount, the anonymous-user account forlocalhostthat is created by mysql_install_db would take precedence whenmontyconnects from the local host. As a result,montywould be treated as an anonymous user. The reason for this is that the anonymous-user account has a more specificHostcolumn value than the'monty'@'%'account and thus comes earlier in theusertable sort order. (usertable sorting is discussed in Section 5.4.4, “Access Control, Stage 1: Connection Verification”.)The
'admin'@'localhost'account has no password. This account can be used only byadminto connect from the local host. It is granted theRELOADandPROCESSadministrative privileges. These privileges allow theadminuser to execute the mysqladmin reload, mysqladmin refresh, and mysqladmin flush-xxxcommands, as well as mysqladmin processlist . No privileges are granted for accessing any databases. You could add such privileges later by issuing additionalGRANTstatements.The
'dummy'@'localhost'account has no password. This account can be used only to connect from the local host. No privileges are granted. It is assumed that you will grant specific privileges to the account later.
The statements that create accounts with no password will fail if
the NO_AUTO_CREATE_USER SQL mode
is enabled. To deal with this, use an IDENTIFIED
BY clause that specifies a nonempty password.
To check the privileges for an account, use
SHOW GRANTS:
mysql> SHOW GRANTS FOR 'admin'@'localhost';
+-----------------------------------------------------+
| Grants for admin@localhost |
+-----------------------------------------------------+
| GRANT RELOAD, PROCESS ON *.* TO 'admin'@'localhost' |
+-----------------------------------------------------+
As an alternative to CREATE USER
and GRANT, you can create the same
accounts directly by issuing INSERT
statements and then telling the server to reload the grant tables
using FLUSH
PRIVILEGES:
shell>mysql --user=root mysqlmysql>INSERT INTO user->VALUES('localhost','monty',PASSWORD('some_pass'),->'Y','Y','Y','Y','Y','Y','Y','Y','Y','Y','Y','Y','Y','Y');mysql>INSERT INTO user->VALUES('%','monty',PASSWORD('some_pass'),->'Y','Y','Y','Y','Y','Y','Y','Y','Y','Y','Y','Y','Y','Y',->'Y','Y','Y','Y','Y','Y','Y','Y','Y','Y','Y','Y','Y','Y',->'','','','',0,0,0,0);mysql>INSERT INTO user SET Host='localhost',User='admin',->Reload_priv='Y', Process_priv='Y';mysql>INSERT INTO user (Host,User,Password)->VALUES('localhost','dummy','');mysql>FLUSH PRIVILEGES;
When you create accounts with
INSERT, it is necessary to use
FLUSH PRIVILEGES
to tell the server to reload the grant tables. Otherwise, the
changes go unnoticed until you restart the server. With
CREATE USER,
FLUSH PRIVILEGES
is unnecessary.
The reason for using the PASSWORD()
function with INSERT is to encrypt
the password. The CREATE USER
statement encrypts the password for you, so
PASSWORD() is unnecessary.
The 'Y' values enable privileges for the
accounts. Depending on your MySQL version, you may have to use a
different number of 'Y' values in the first two
INSERT statements. The
INSERT statement for the
admin account employs the more readable
extended INSERT syntax using
SET.
In the INSERT statement for the
dummy account, only the
Host, User, and
Password columns in the user
table row are assigned values. None of the privilege columns are
set explicitly, so MySQL assigns them all the default value of
'N'. This is equivalent to what
CREATE USER does.
If strict SQL mode is enabled, all columns that have no default
value must have a value specified. In this case,
INSERT statements must explicitly
specify values for the ssl_cipher,
x509_issuer, and
x509_subject columns.
To set up a superuser account, it is necessary only to create a
user table entry with the privilege columns set
to 'Y'. The user table
privileges are global, so no entries in any of the other grant
tables are needed.
The next examples create three accounts and give them access to
specific databases. Each of them has a user name of
custom and password of
obscure.
To create the accounts with CREATE
USER and GRANT, use the
following statements:
shell>mysql --user=root mysqlmysql>CREATE USER 'custom'@'localhost' IDENTIFIED BY 'obscure';mysql>GRANT SELECT,INSERT,UPDATE,DELETE,CREATE,DROP->ON bankaccount.*->TO 'custom'@'localhost';mysql>CREATE USER 'custom'@'host47.example.com' IDENTIFIED BY 'obscure';mysql>GRANT SELECT,INSERT,UPDATE,DELETE,CREATE,DROP->ON expenses.*->TO 'custom'@'host47.example.com';mysql>CREATE USER 'custom'@'server.domain' IDENTIFIED BY 'obscure';mysql>GRANT SELECT,INSERT,UPDATE,DELETE,CREATE,DROP->ON customer.*->TO 'custom'@'server.domain';
The three accounts can be used as follows:
The first account can access the
bankaccountdatabase, but only from the local host.The second account can access the
expensesdatabase, but only from the hosthost47.example.com.The third account can access the
customerdatabase, but only from the hostserver.domain.
To set up the custom accounts without
GRANT, use
INSERT statements as follows to
modify the grant tables directly:
shell>mysql --user=root mysqlmysql>INSERT INTO user (Host,User,Password)->VALUES('localhost','custom',PASSWORD('obscure'));mysql>INSERT INTO user (Host,User,Password)->VALUES('host47.example.com','custom',PASSWORD('obscure'));mysql>INSERT INTO user (Host,User,Password)->VALUES('server.domain','custom',PASSWORD('obscure'));mysql>INSERT INTO db->(Host,Db,User,Select_priv,Insert_priv,->Update_priv,Delete_priv,Create_priv,Drop_priv)->VALUES('localhost','bankaccount','custom',->'Y','Y','Y','Y','Y','Y');mysql>INSERT INTO db->(Host,Db,User,Select_priv,Insert_priv,->Update_priv,Delete_priv,Create_priv,Drop_priv)->VALUES('host47.example.com','expenses','custom',->'Y','Y','Y','Y','Y','Y');mysql>INSERT INTO db->(Host,Db,User,Select_priv,Insert_priv,->Update_priv,Delete_priv,Create_priv,Drop_priv)->VALUES('server.domain','customer','custom',->'Y','Y','Y','Y','Y','Y');mysql>FLUSH PRIVILEGES;
The first three INSERT statements
add user table entries that allow the user
custom to connect from the various hosts with
the given password, but grant no global privileges (all privileges
are set to the default value of 'N'). The next
three INSERT statements add
db table entries that grant privileges to
custom for the bankaccount,
expenses, and customer
databases, but only when accessed from the proper hosts. As usual
when you modify the grant tables directly, you must tell the
server to reload them with
FLUSH PRIVILEGES
so that the privilege changes take effect.
To create a user who has access from all machines in a given
domain (for example, mydomain.com), you can use
the “%” wildcard character in the
host part of the account name:
mysql> CREATE USER 'myname'@'%.mydomain.com' IDENTIFIED BY 'mypass';
To do the same thing by modifying the grant tables directly, do this:
mysql>INSERT INTO user (Host,User,Password,...)->VALUES('%.mydomain.com','myname',PASSWORD('mypass'),...);mysql>FLUSH PRIVILEGES;
To remove an account, use the DROP
USER statement, which is described in
Section 12.5.1.2, “DROP USER Syntax”.
One means of limiting use of MySQL server resources is to set the
global max_user_connections
system variable to a nonzero value. This limits the number of
simultaneous connections that can be made by any given account,
but places no limits on what a client can do once connected. In
addition, setting
max_user_connections does not
allow for management of individual accounts. Both types of control
are of interest to many MySQL administrators, particularly those
working for Internet Service Providers.
In MySQL 5.5, you can limit use of the following server resources for individual accounts:
The number of queries that an account can issue per hour
The number of updates that an account can issue per hour
The number of times an account can connect to the server per hour
The number of simultaneous connections to the server by an account
Any statement that a client can issue counts against the query limit (unless its results are served from the query cache). Only statements that modify databases or tables count against the update limit.
An “account” in this context corresponds to a row in
the mysql.user table. That is, a connection is
assessed against the User and
Host values in the user
table row that applies to the connection. For example, an account
'usera'@'%.example.com' corresponds to a row in
the user table that has User
and Host values of usera and
%.example.com, to allow
usera to connect from any host in the
example.com domain. In this case, the server
applies resource limits in this row collectively to all
connections by usera from any host in the
example.com domain because all such connections
use the same account.
Before MySQL 5.0.3, an “account” was assessed against
the actual host from which a user connects. This older method
accounting may be selected by starting the server with the
--old-style-user-limits option. In
this case, if usera connects simultaneously
from host1.example.com and
host2.example.com, the server applies the
account resource limits separately to each connection. If
usera connects again from
host1.example.com, the server applies the
limits for that connection together with the existing connection
from that host.
To set resource limits for an account, use the
GRANT statement (see
Section 12.5.1.3, “GRANT Syntax”). Provide a WITH clause
that names each resource to be limited. The default value for each
limit is zero (no limit). For example, to create a new account
that can access the customer database, but only
in a limited fashion, issue these statements:
mysql>CREATE USER 'francis'@'localhost' IDENTIFIED BY 'frank';mysql>GRANT ALL ON customer.* TO 'francis'@'localhost'->WITH MAX_QUERIES_PER_HOUR 20->MAX_UPDATES_PER_HOUR 10->MAX_CONNECTIONS_PER_HOUR 5->MAX_USER_CONNECTIONS 2;
The limit types need not all be named in the
WITH clause, but those named can be present in
any order. The value for each per-hour limit should be an integer
representing a count per hour. For
MAX_USER_CONNECTIONS, the limit is an integer
representing the maximum number of simultaneous connections by the
account. If this limit is set to zero, the global
max_user_connections system
variable value determines the number of simultaneous connections.
If max_user_connections is also
zero, there is no limit for the account.
To modify existing limits for an account, use a
GRANT USAGE
statement at the global level (ON *.*). The
following statement changes the query limit for
francis to 100:
mysql>GRANT USAGE ON *.* TO 'francis'@'localhost'->WITH MAX_QUERIES_PER_HOUR 100;
The statement modifies only the limit value specified and leaves the account otherwise unchanged.
To remove a limit, set its value to zero. For example, to remove
the limit on how many times per hour francis
can connect, use this statement:
mysql>GRANT USAGE ON *.* TO 'francis'@'localhost'->WITH MAX_CONNECTIONS_PER_HOUR 0;
As mentioned previously, the simultaneous-connection limit for an
account is determined from the
MAX_USER_CONNECTIONS limit and the
max_user_connections system
variable. Suppose that the global
max_user_connections value is 10
and three accounts have resource limits specified with
GRANT:
GRANT ... TO 'user1'@'localhost' WITH MAX_USER_CONNECTIONS 0; GRANT ... TO 'user2'@'localhost' WITH MAX_USER_CONNECTIONS 5; GRANT ... TO 'user3'@'localhost' WITH MAX_USER_CONNECTIONS 20;
user1 has a connection limit of 10 (the global
max_user_connections value)
because it has a zero MAX_USER_CONNECTIONS
limit). user2 and user3 have
connection limits of 5 and 20, respectively, because they have
nonzero MAX_USER_CONNECTIONS limits.
The server stores resource limits for an account in the
user table row corresponding to the account.
The max_questions,
max_updates, and
max_connections columns store the per-hour
limits, and the max_user_connections column
stores the MAX_USER_CONNECTIONS limit. (See
Section 5.4.2, “Privilege System Grant Tables”.)
Resource-use counting takes place when any account has a nonzero limit placed on its use of any of the resources.
As the server runs, it counts the number of times each account uses resources. If an account reaches its limit on number of connections within the last hour, further connections for the account are rejected until that hour is up. Similarly, if the account reaches its limit on the number of queries or updates, further queries or updates are rejected until the hour is up. In all such cases, an appropriate error message is issued.
Resource counting is done per account, not per client. For example, if your account has a query limit of 50, you cannot increase your limit to 100 by making two simultaneous client connections to the server. Queries issued on both connections are counted together.
The current per-hour resource-use counts can be reset globally for all accounts, or individually for a given account:
To reset the current counts to zero for all accounts, issue a
FLUSH USER_RESOURCESstatement. The counts also can be reset by reloading the grant tables (for example, with aFLUSH PRIVILEGESstatement or a mysqladmin reload command).The counts for an individual account can be set to zero by re-granting it any of its limits. To do this, use
GRANT USAGEas described earlier and specify a limit value equal to the value that the account currently has.
Counter resets do not affect the
MAX_USER_CONNECTIONS limit.
All counts begin at zero when the server starts; counts are not carried over through a restart.
For the MAX_USER_CONNECTIONS limit, an edge
case can occur if the account currently has open the maximum
number of connections allowed to it: A disconnect followed quickly
by a connect can result in an error
(ER_TOO_MANY_USER_CONNECTIONS or
ER_USER_LIMIT_REACHED) if the
server has not fully processed the disconnect by the time the
connect occurs. When the server finishes disconnect processing,
another connection will once more be allowed.
To assign a password when you create a new account with
CREATE USER, include an
IDENTIFIED BY clause:
mysql> CREATE USER 'jeffrey'@'localhost' IDENTIFIED BY 'biscuit';
To assign or change a password for an existing account, one way is
to issue a SET PASSWORD statement:
mysql> SET PASSWORD FOR 'jeffrey'@'localhost' = PASSWORD('biscuit');
Only users such as root that have update access
to the mysql database can change the password
for other users. If you are not connected as an anonymous user,
you can change your own password by omitting the
FOR clause:
mysql> SET PASSWORD = PASSWORD('biscuit');
You can also use a GRANT
USAGE statement at the global level (ON
*.*) to assign a password to an account without
affecting the account's current privileges:
mysql> GRANT USAGE ON *.* TO 'jeffrey'@'localhost' IDENTIFIED BY 'biscuit';
Passwords can be assigned from the command line by using the mysqladmin command:
shell> mysqladmin -u user_name -h host_name password "newpwd"
The account for which this command resets the password is the one
with a user table row that matches
user_name in the
User column and the client host from
which you connect in the Host
column.
Although it is generally preferable to assign passwords using one
of the preceding methods, you can also do so by modifying the
user table directly:
To establish a password when creating a new account, provide a value for the
Passwordcolumn:shell>
mysql -u root mysqlmysql>INSERT INTO user (Host,User,Password)->VALUES('localhost','jeffrey',PASSWORD('biscuit'));mysql>FLUSH PRIVILEGES;To change the password for an existing account, use
UPDATEto set thePasswordcolumn value:shell>
mysql -u root mysqlmysql>UPDATE user SET Password = PASSWORD('bagel')->WHERE Host = 'localhost' AND User = 'francis';mysql>FLUSH PRIVILEGES;
When you assign passwords using CREATE
USER or GRANT with an
IDENTIFIED BY clause or with the
mysqladmin password command, they take care of
encrypting the password for you.
When you assign an account a nonempty password using
SET PASSWORD,
INSERT, or
UPDATE, you must use the
PASSWORD() function to encrypt the
password. PASSWORD() is necessary
because the user table stores passwords in
encrypted form, not as plaintext. If you forget that fact, you are
likely to set passwords like this:
shell>mysql -u root mysqlmysql>INSERT INTO user (Host,User,Password)->VALUES('localhost','jeffrey','biscuit');mysql>FLUSH PRIVILEGES;
The result is that the literal value 'biscuit'
is stored as the password in the user table,
not the encrypted value. When jeffrey attempts
to connect to the server using this password, the value is
encrypted and compared to the value stored in the
user table. However, the stored value is the
literal string 'biscuit', so the comparison
fails and the server rejects the connection:
shell> mysql -u jeffrey -pbiscuit test
Access denied
Note
PASSWORD() encryption differs
from Unix password encryption. See Section 5.5.1, “User Names and Passwords”.
MySQL supports secure (encrypted) connections between MySQL
clients and the server using the Secure Sockets Layer (SSL)
protocol. This section discusses how to use SSL connections. For
information on how to require users to use SSL connections, see
the discussion of the REQUIRE clause of the
GRANT statement in
Section 12.5.1.3, “GRANT Syntax”.
The standard configuration of MySQL is intended to be as fast as possible, so encrypted connections are not used by default. Doing so would make the client/server protocol much slower. Encrypting data is a CPU-intensive operation that requires the computer to do additional work and can delay other MySQL tasks. For applications that require the security provided by encrypted connections, the extra computation is warranted.
MySQL allows encryption to be enabled on a per-connection basis. You can choose a normal unencrypted connection or a secure encrypted SSL connection according the requirements of individual applications.
Secure connections are based on the OpenSSL API and are available through the MySQL C API. Replication uses the C API, so secure connections can be used between master and slave servers.
Another way to connect securely is from within an SSH connection to the MySQL server host. For an example, see Section 5.5.7, “Connecting to MySQL Remotely from Windows with SSH”.
To understand how MySQL uses SSL, it is necessary to explain some basic SSL and X509 concepts. People who are familiar with these can skip this part of the discussion.
By default, MySQL uses unencrypted connections between the
client and the server. This means that someone with access to
the network could watch all your traffic and look at the data
being sent or received. They could even change the data while it
is in transit between client and server. To improve security a
little, you can compress client/server traffic by using the
--compress option when invoking client
programs. However, this does not foil a determined attacker.
When you need to move information over a network in a secure fashion, an unencrypted connection is unacceptable. Encryption is the way to make any kind of data unreadable. In fact, today's practice requires many additional security elements from encryption algorithms. They should resist many kind of known attacks such as changing the order of encrypted messages or replaying data twice.
SSL is a protocol that uses different encryption algorithms to ensure that data received over a public network can be trusted. It has mechanisms to detect any data change, loss, or replay. SSL also incorporates algorithms that provide identity verification using the X509 standard.
X509 makes it possible to identify someone on the Internet. It is most commonly used in e-commerce applications. In basic terms, there should be some company called a “Certificate Authority” (or CA) that assigns electronic certificates to anyone who needs them. Certificates rely on asymmetric encryption algorithms that have two encryption keys (a public key and a secret key). A certificate owner can show the certificate to another party as proof of identity. A certificate consists of its owner's public key. Any data encrypted with this public key can be decrypted only using the corresponding secret key, which is held by the owner of the certificate.
If you need more information about SSL, X509, or encryption, use your favorite Internet search engine to search for the keywords in which you are interested.
To use SSL connections between the MySQL server and client programs, your system must support either OpenSSL or yaSSL and your version of MySQL must be built with SSL support.
To make it easier to use secure connections, MySQL is bundled with yaSSL. (MySQL and yaSSL employ the same licensing model, whereas OpenSSL uses an Apache-style license.) yaSSL support initially was available only for a few platforms, but now it is available on all MySQL platforms supported by Oracle Corporation.
To get secure connections to work with MySQL and SSL, you must do the following:
If you are not using a binary (precompiled) version of MySQL that has been built with SSL support, and you are going to use OpenSSL rather than the bundled yaSSL library, install OpenSSL if it has not already been installed. We have tested MySQL with OpenSSL 0.9.6. To obtain OpenSSL, visit http://www.openssl.org.
Building MySQL using OpenSSL requires a shared OpenSSL library, otherwise linker errors occur. Alternatively, build MySQL using yaSSL.
If you are not using a binary (precompiled) version of MySQL that has been built with SSL support, configure a MySQL source distribution to use SSL. When you configure MySQL, invoke the configure script like this:
shell>
./configure --with-sslThat configures the distribution to use the bundled yaSSL library. To use OpenSSL instead, specify the
--with-ssloption with the path to the directory where the OpenSSL header files and libraries are located:shell>
./configure --with-ssl=pathNote that yaSSL support on Unix platforms requires that either
/dev/urandomor/dev/randombe available to retrieve true random numbers. For additional information (especially regarding yaSSL on Solaris versions prior to 2.8 and HP-UX), see Bug#13164.Make sure that the
userin themysqldatabase includes the SSL-related columns (beginning withssl_andx509_). If yourusertable does not have these columns, it must be upgraded; see Section 4.4.7, “mysql_upgrade — Check Tables for MySQL Upgrade”.To check whether a server binary is compiled with SSL support, invoke it with the
--ssloption. An error will occur if the server does not support SSL:shell>
mysqld --ssl --help060525 14:18:52 [ERROR] mysqld: unknown option '--ssl'To check whether a running mysqld server supports SSL, examine the value of the
have_sslsystem variable (if you have nohave_sslvariable, check forhave_openssl):mysql>
SHOW VARIABLES LIKE 'have_ssl';+---------------+-------+ | Variable_name | Value | +---------------+-------+ | have_ssl | YES | +---------------+-------+If the value is
YES, the server supports SSL connections. If the value isDISABLED, the server supports SSL connections but was not started with the appropriate--ssl-options (described later in this section).xxx
To enable SSL connections, the proper SSL-related options must be used (see Section 5.5.6.3, “SSL Command Options”).
To start the MySQL server so that it allows clients to connect via SSL, use the options that identify the key and certificate files the server needs when establishing a secure connection:
shell>mysqld --ssl-ca=ca-cert.pem\--ssl-cert=server-cert.pem\--ssl-key=server-key.pem
--ssl-caidentifies the Certificate Authority (CA) certificate.--ssl-certidentifies the server public key. This can be sent to the client and authenticated against the CA certificate that it has.--ssl-keyidentifies the server private key.
To establish a secure connection to a MySQL server with SSL
support, the options that a client must specify depend on the
SSL requirements of the user account that the client uses. (See
the discussion of the REQUIRE clause in
Section 12.5.1.3, “GRANT Syntax”.)
If the account has no special SSL requirements or was created
using a GRANT statement that
includes the REQUIRE SSL option, a client can
connect securely by using just the
--ssl-ca option:
shell> mysql --ssl-ca=ca-cert.pem
To require that a client certificate also be specified, create
the account using the REQUIRE X509 option.
Then the client must also specify the proper client key and
certificate files or the server will reject the connection:
shell>mysql --ssl-ca=ca-cert.pem\--ssl-cert=client-cert.pem\--ssl-key=client-key.pem
In other words, the options are similar to those used for the server. Note that the Certificate Authority certificate has to be the same.
A client can determine whether the current connection with the
server uses SSL by checking the value of the
Ssl_cipher status variable.
The value of Ssl_cipher is
nonempty if SSL is used, and empty otherwise. For example:
mysql> SHOW STATUS LIKE 'Ssl_cipher';
+---------------+--------------------+
| Variable_name | Value |
+---------------+--------------------+
| Ssl_cipher | DHE-RSA-AES256-SHA |
+---------------+--------------------+
For the mysql client, you can use the
STATUS or \s command and
check the SSL line:
mysql> \s
...
SSL: Not in use
...
Or:
mysql> \s
...
SSL: Cipher in use is DHE-RSA-AES256-SHA
...
To establish a secure connection from within an application
program, use the mysql_ssl_set()
C API function to set the appropriate certificate options before
calling mysql_real_connect().
See Section 21.9.3.67, “mysql_ssl_set()”. After the connection is
established, you can use
mysql_get_ssl_cipher() to
determine whether SSL is in use. A non-NULL
return value indicates a secure connection and names the SSL
cipher used for encryption. A NULL return
value indicates that SSL is not being used. See
Section 21.9.3.33, “mysql_get_ssl_cipher()”.
The following list describes options that are used for specifying the use of SSL, certificate files, and key files. They can be given on the command line or in an option file. These options are not available unless MySQL has been built with SSL support. See Section 5.5.6.2, “Using SSL Connections”.
Table 5.7. SSL Option/Variable Summary
| Name | Cmd-Line | Option file | System Var | Status Var | Var Scope | Dynamic |
|---|---|---|---|---|---|---|
| ssl | Yes | Yes | ||||
| ssl-ca | Yes | Yes | Global | No | ||
| - Variable: ssl_ca | Yes | Global | No | |||
| ssl-capath | Yes | Yes | Global | No | ||
| - Variable: ssl_capath | Yes | Global | No | |||
| ssl-cert | Yes | Yes | Global | No | ||
| - Variable: ssl_cert | Yes | Global | No | |||
| ssl-cipher | Yes | Yes | Global | No | ||
| - Variable: ssl_cipher | Yes | Global | No | |||
| ssl-key | Yes | Yes | Global | No | ||
| - Variable: ssl_key | Yes | Global | No | |||
| ssl-verify-server-cert | Yes | Yes |
For the server, this option specifies that the server allows SSL connections. For a client program, it allows the client to connect to the server using SSL. This option is not sufficient in itself to cause an SSL connection to be used. You must also specify the
--ssl-caoption, and possibly the--ssl-certand--ssl-keyoptions.This option is more often used in its opposite form to override any other SSL options and indicate that SSL should not be used. To do this, specify the option as
--skip-sslor--ssl=0.Note that use of
--ssldoes not require an SSL connection. For example, if the server or client is compiled without SSL support, a normal unencrypted connection is used.The secure way to require use of an SSL connection is to create an account on the server that includes a
REQUIRE SSLclause in theGRANTstatement. Then use that account to connect to the server, where both the server and the client have SSL support enabled.The
REQUIREclause allows other SSL-related restrictions as well. The description ofREQUIREin Section 12.5.1.3, “GRANTSyntax”, provides additional detail about which SSL command options may or must be specified by clients that connect using accounts that are created using the variousREQUIREoptions.The path to a file that contains a list of trusted SSL CAs.
The path to a directory that contains trusted SSL CA certificates in PEM format.
The name of the SSL certificate file to use for establishing a secure connection.
A list of allowable ciphers to use for SSL encryption. For greatest portability,
cipher_listshould be a list of one or more cipher names, separated by colons. Examples:--ssl-cipher=AES128-SHA --ssl-cipher=DHE-RSA-AES256-SHA:AES128-SHA
This format is understood both by OpenSSL and yaSSL. OpenSSL supports a more flexible syntax for specifying ciphers, as described in the OpenSSL documentation at http://www.openssl.org/docs/apps/ciphers.html. However, this extended syntax will fail if used with a MySQL installation compiled against yaSSL.
If no cipher in the list is supported, SSL connections will not work.
The name of the SSL key file to use for establishing a secure connection.
This option is available for client programs only, not the server. It causes the server's Common Name value in the certificate that the server sends to the client to be verified against the host name that the client uses for connecting to the server, and the connection is rejected if there is a mismatch. This feature can be used to prevent man-in-the-middle attacks. Verification is disabled by default.
If you use SSL when establishing a client connection, you can
tell the client not to authenticate the server certificate by
specifying neither --ssl-ca nor
--ssl-capath. The server still
verifies the client according to any applicable requirements
established via GRANT statements
for the client, and it still uses any
--ssl-ca/--ssl-capath
values that were passed to server at startup time.
This section demonstrates how to set up SSL certificate and key files for use by MySQL servers and clients. The first example shows a simplified procedure such as you might use from the command line. The second shows a script that contains more detail. The first two examples are intended for use on Unix and both use the openssl command that is part of OpenSSL. The third example describes how to set up SSL files on Windows.
Following the third example, instructions are given for using the files to test SSL connections. You can also use the files as described in Section 5.5.6.2, “Using SSL Connections”.
Example 1: Creating SSL files from the command line on Unix
The following example shows a set of commands to create MySQL server and client certificate and key files. You will need to respond to several prompts by the openssl commands. For testing, you can press Enter to all prompts. For production use, you should provide nonempty responses.
# Create clean environment shell>rm -rf newcertsshell>mkdir newcerts && cd newcerts# Create CA certificate shell>openssl genrsa 2048 > ca-key.pemshell>openssl req -new -x509 -nodes -days 1000 \-key ca-key.pem > ca-cert.pem# Create server certificate shell>openssl req -newkey rsa:2048 -days 1000 \-nodes -keyout server-key.pem > server-req.pemshell>openssl x509 -req -in server-req.pem -days 1000 \-CA ca-cert.pem -CAkey ca-key.pem -set_serial 01 > server-cert.pem# Create client certificate shell>openssl req -newkey rsa:2048 -days 1000 \-nodes -keyout client-key.pem > client-req.pemshell>openssl x509 -req -in client-req.pem -days 1000 \-CA ca-cert.pem -CAkey ca-key.pem -set_serial 01 > client-cert.pem
Example 2: Creating SSL files using a script on Unix
Here is an example script that shows how to set up SSL certificates for MySQL:
DIR=`pwd`/openssl
PRIV=$DIR/private
mkdir $DIR $PRIV $DIR/newcerts
cp /usr/share/ssl/openssl.cnf $DIR
replace ./demoCA $DIR -- $DIR/openssl.cnf
# Create necessary files: $database, $serial and $new_certs_dir
# directory (optional)
touch $DIR/index.txt
echo "01" > $DIR/serial
#
# Generation of Certificate Authority(CA)
#
openssl req -new -x509 -keyout $PRIV/cakey.pem -out $DIR/ca-cert.pem \
-days 3600 -config $DIR/openssl.cnf
# Sample output:
# Using configuration from /home/monty/openssl/openssl.cnf
# Generating a 1024 bit RSA private key
# ................++++++
# .........++++++
# writing new private key to '/home/monty/openssl/private/cakey.pem'
# Enter PEM pass phrase:
# Verifying password - Enter PEM pass phrase:
# -----
# You are about to be asked to enter information that will be
# incorporated into your certificate request.
# What you are about to enter is what is called a Distinguished Name
# or a DN.
# There are quite a few fields but you can leave some blank
# For some fields there will be a default value,
# If you enter '.', the field will be left blank.
# -----
# Country Name (2 letter code) [AU]:FI
# State or Province Name (full name) [Some-State]:.
# Locality Name (eg, city) []:
# Organization Name (eg, company) [Internet Widgits Pty Ltd]:MySQL AB
# Organizational Unit Name (eg, section) []:
# Common Name (eg, YOUR name) []:MySQL admin
# Email Address []:
#
# Create server request and key
#
openssl req -new -keyout $DIR/server-key.pem -out \
$DIR/server-req.pem -days 3600 -config $DIR/openssl.cnf
# Sample output:
# Using configuration from /home/monty/openssl/openssl.cnf
# Generating a 1024 bit RSA private key
# ..++++++
# ..........++++++
# writing new private key to '/home/monty/openssl/server-key.pem'
# Enter PEM pass phrase:
# Verifying password - Enter PEM pass phrase:
# -----
# You are about to be asked to enter information that will be
# incorporated into your certificate request.
# What you are about to enter is what is called a Distinguished Name
# or a DN.
# There are quite a few fields but you can leave some blank
# For some fields there will be a default value,
# If you enter '.', the field will be left blank.
# -----
# Country Name (2 letter code) [AU]:FI
# State or Province Name (full name) [Some-State]:.
# Locality Name (eg, city) []:
# Organization Name (eg, company) [Internet Widgits Pty Ltd]:MySQL AB
# Organizational Unit Name (eg, section) []:
# Common Name (eg, YOUR name) []:MySQL server
# Email Address []:
#
# Please enter the following 'extra' attributes
# to be sent with your certificate request
# A challenge password []:
# An optional company name []:
#
# Remove the passphrase from the key
#
openssl rsa -in $DIR/server-key.pem -out $DIR/server-key.pem
#
# Sign server cert
#
openssl ca -policy policy_anything -out $DIR/server-cert.pem \
-config $DIR/openssl.cnf -infiles $DIR/server-req.pem
# Sample output:
# Using configuration from /home/monty/openssl/openssl.cnf
# Enter PEM pass phrase:
# Check that the request matches the signature
# Signature ok
# The Subjects Distinguished Name is as follows
# countryName :PRINTABLE:'FI'
# organizationName :PRINTABLE:'MySQL AB'
# commonName :PRINTABLE:'MySQL admin'
# Certificate is to be certified until Sep 13 14:22:46 2003 GMT
# (365 days)
# Sign the certificate? [y/n]:y
#
#
# 1 out of 1 certificate requests certified, commit? [y/n]y
# Write out database with 1 new entries
# Data Base Updated
#
# Create client request and key
#
openssl req -new -keyout $DIR/client-key.pem -out \
$DIR/client-req.pem -days 3600 -config $DIR/openssl.cnf
# Sample output:
# Using configuration from /home/monty/openssl/openssl.cnf
# Generating a 1024 bit RSA private key
# .....................................++++++
# .............................................++++++
# writing new private key to '/home/monty/openssl/client-key.pem'
# Enter PEM pass phrase:
# Verifying password - Enter PEM pass phrase:
# -----
# You are about to be asked to enter information that will be
# incorporated into your certificate request.
# What you are about to enter is what is called a Distinguished Name
# or a DN.
# There are quite a few fields but you can leave some blank
# For some fields there will be a default value,
# If you enter '.', the field will be left blank.
# -----
# Country Name (2 letter code) [AU]:FI
# State or Province Name (full name) [Some-State]:.
# Locality Name (eg, city) []:
# Organization Name (eg, company) [Internet Widgits Pty Ltd]:MySQL AB
# Organizational Unit Name (eg, section) []:
# Common Name (eg, YOUR name) []:MySQL user
# Email Address []:
#
# Please enter the following 'extra' attributes
# to be sent with your certificate request
# A challenge password []:
# An optional company name []:
#
# Remove the passphrase from the key
#
openssl rsa -in $DIR/client-key.pem -out $DIR/client-key.pem
#
# Sign client cert
#
openssl ca -policy policy_anything -out $DIR/client-cert.pem \
-config $DIR/openssl.cnf -infiles $DIR/client-req.pem
# Sample output:
# Using configuration from /home/monty/openssl/openssl.cnf
# Enter PEM pass phrase:
# Check that the request matches the signature
# Signature ok
# The Subjects Distinguished Name is as follows
# countryName :PRINTABLE:'FI'
# organizationName :PRINTABLE:'MySQL AB'
# commonName :PRINTABLE:'MySQL user'
# Certificate is to be certified until Sep 13 16:45:17 2003 GMT
# (365 days)
# Sign the certificate? [y/n]:y
#
#
# 1 out of 1 certificate requests certified, commit? [y/n]y
# Write out database with 1 new entries
# Data Base Updated
#
# Create a my.cnf file that you can use to test the certificates
#
cnf=""
cnf="$cnf [client]"
cnf="$cnf ssl-ca=$DIR/ca-cert.pem"
cnf="$cnf ssl-cert=$DIR/client-cert.pem"
cnf="$cnf ssl-key=$DIR/client-key.pem"
cnf="$cnf [mysqld]"
cnf="$cnf ssl-ca=$DIR/ca-cert.pem"
cnf="$cnf ssl-cert=$DIR/server-cert.pem"
cnf="$cnf ssl-key=$DIR/server-key.pem"
echo $cnf | replace " " '
' > $DIR/my.cnf
Example 3: Creating SSL files on Windows
Download OpenSSL for Windows. An overview of available packages can be seen here: http://www.slproweb.com/products/Win32OpenSSL.html
Choose of the following packages, depending on your architecture (32-bit or 64-bit):
Win32 OpenSSL v0.9.8l Light, available at: http://www.slproweb.com/download/Win32OpenSSL_Light-0_9_8l.exe
Win64 OpenSSL v0.9.8l Light, available at: http://www.slproweb.com/download/Win64OpenSSL_Light-0_9_8l.exe
if a message occurs during setup indicating
'...critical component is missing: Microsoft Visual C++
2008 Redistributables', cancel the setup and download
one of the following packages as well, again depending on your
architecture (32-bit or 64-bit):
Visual C++ 2008 Redistributables (x86), available at: http://www.microsoft.com/downloads/details.aspx?familyid=9B2DA534-3E03-4391-8A4D-074B9F2BC1BF
Visual C++ 2008 Redistributables (x64), available at: http://www.microsoft.com/downloads/details.aspx?familyid=bd2a6171-e2d6-4230-b809-9a8d7548c1b6
After installing the additional package, restart the OpenSSL setup.
During installation, leave the default
C:\OpenSSL as the install path, and also
leave the default option 'Copy OpenSSL DLL files to the
Windows system directory' selected.
When the installation has finished, add
C:\OpenSSL\bin to the Windows System Path
variable of your server:
On the Windows desktop, right-click on the My Computer icon, and select .
Next select the tab from the menu that appears, and click the button.
Under System Variables, select , and then click the button. The dialogue should appear.
Add
';C:\OpenSSL\bin'to the end (notice the semicolon).Press OK 3 times.
Check that OpenSSL was correctly integrated into the Path variable by opening a new command console (Start>Run>cmd.exe) and verifying that OpenSSL is available:
Microsoft Windows [Version ...] Copyright (c) 2006 Microsoft Corporation. All rights reserved. C:\Windows\system32>
cd \C:\>opensslOpenSSL>exit<<< If you see the OpenSSL prompt, installation was successful. C:\>
Depending on your version of Windows, the preceding instructions might be slightly different.
After OpenSSL has been installed, use the instructions from Example 1 (shown earlier in this section), with the following changes:
Change the follow Unix commands:
# Create clean environment shell>
rm -rf newcertsshell>mkdir newcerts && cd newcertsOn Windows, use these commands instead:
# Create clean environment shell>
md c:\newcertsshell>cd c:\newcertsWhen a
'\'character is shown at the end of a command line, this'\'character must be removed and the command lines entered all on a single line.For references to
my.cnfoption files, substitutemy.iniinstead.
Testing SSL connections
To test SSL connections, start the server as follows, where
$DIR is the path name to the directory where
the sample my.cnf option file is located:
shell> mysqld --defaults-file=$DIR/my.cnf &
Then invoke a client program using the same option file:
shell> mysql --defaults-file=$DIR/my.cnf
If you have a MySQL source distribution, you can also test your
setup by modifying the preceding my.cnf
file to refer to the demonstration certificate and key files in
the mysql-test/std_data directory of the
distribution.
This section describes how to get a secure connection to a remote
MySQL server with SSH. The information was provided by David
Carlson <dcarlson@mplcomm.com>.
Install an SSH client on your Windows machine. As a user, the best nonfree one I have found is from
SecureCRTfrom http://www.vandyke.com/. Another option isf-securefrom http://www.f-secure.com/. You can also find some free ones onGoogleat http://directory.google.com/Top/Computers/Internet/Protocols/SSH/Clients/Windows/.Start your Windows SSH client. Set
Host_Name =. Setyourmysqlserver_URL_or_IPuserid=to log in to your server. Thisyour_useriduseridvalue might not be the same as the user name of your MySQL account.Set up port forwarding. Either do a remote forward (Set
local_port: 3306,remote_host:,yourmysqlservername_or_ipremote_port: 3306) or a local forward (Setport: 3306,host: localhost,remote port: 3306).Save everything, otherwise you will have to redo it the next time.
Log in to your server with the SSH session you just created.
On your Windows machine, start some ODBC application (such as Access).
Create a new file in Windows and link to MySQL using the ODBC driver the same way you normally do, except type in
localhostfor the MySQL host server, notyourmysqlservername.
At this point, you should have an ODBC connection to MySQL, encrypted using SSH.
Applications can use the following guidelines to perform auditing that ties database activity to MySQL accounts.
MySQL accounts correspond to rows in the
mysql.user table. When a client connects
successfully, the server authenticates the client to a particular
row in this table. The User and
Host column values in this row uniquely
identify the account and correspond to the
'
format in which account names are written in SQL statements.
user_name'@'host_name'
The account used to authenticate a client determines which
privileges the client has. Normally, the
CURRENT_USER() function can be
invoked to determine which account this is for the client user.
Its value is constructed from the User and
Host columns of the user
table row for the account.
However, there are circumstances under which the
CURRENT_USER() value corresponds
not to the client user but to a different account. This occurs in
contexts when privilege checking is not based the client's
account:
Stored routines (procedures and functions) defined with the
SQL SECURITY DEFINERcharacteristicViews defined with the
SQL SECURITY DEFINERcharacteristicTriggers and events
In those contexts, privilege checking is done against the
DEFINER account and
CURRENT_USER() refers to that
account, not to the account for the client who invoked the stored
routine or view or who caused the trigger to activate. To
determine the invoking user, you can call the
USER() function, which returns a
value indicating the actual user name provided by the client and
the host from which the client connected. However, this value does
not necessarily correspond directly to an account in the
user table, because the
USER() value never contains
wildcards, whereas account values (as returned by
CURRENT_USER()) may contain user
name and host name wildcards.
For example, a blank user name matches any user, so an account of
''@'localhost' enables clients to connect as an
anonymous user from the local host with any user name. If this
case, if a client connects as user1 from the
local host, USER() and
CURRENT_USER() return different
values:
mysql> SELECT USER(), CURRENT_USER();
+-----------------+----------------+
| USER() | CURRENT_USER() |
+-----------------+----------------+
| user1@localhost | @localhost |
+-----------------+----------------+
The host name part of an account can contain wildcards, too. If
the host name contains a '%' or
'_' pattern character or uses netmask notation,
the account can be used for clients connecting from multiple hosts
and the CURRENT_USER() value will
not indicate which one. For example, the account
'user2'@'%.example.com' can be used by
user2 to connect from any host in the
example.com domain. If user2
connects from remote.example.com,
USER() and
CURRENT_USER() return different
values:
mysql> SELECT USER(), CURRENT_USER();
+--------------------------+---------------------+
| USER() | CURRENT_USER() |
+--------------------------+---------------------+
| user2@remote.example.com | user2@%.example.com |
+--------------------------+---------------------+
If an application must invoke
USER() for user auditing (for
example, if it does auditing from within triggers) but must also
be able to associate the USER()
value with an account in the user table, it is
necessary to avoid accounts that contain wildcards in the
User or Host column.
Specifically, do not allow User to be empty
(which creates an anonymous-user account), and do not allow
pattern characters or netmask notation in Host
values. All accounts must have a nonempty User
value and literal Host value.
With respect to the previous examples, the
''@'localhost' and
'user2'@'%.example.com' accounts should be
changed not to use wildcards:
RENAME USER ''@'localhost' TO 'user1'@'localhost'; RENAME USER 'user2'@'%.example.com' TO 'user2'@'remote.example.com';
If user2 must be able to connect from several
hosts in the example.com domain, there should
be a separate account for each host.
To extract the user name or host name part from a
CURRENT_USER() or
USER() value, use the
SUBSTRING() function:
mysql>SELECT SUBSTRING_INDEX(CURRENT_USER(),'@',1);+---------------------------------------+ | SUBSTRING_INDEX(CURRENT_USER(),'@',1) | +---------------------------------------+ | user1 | +---------------------------------------+ mysql>SELECT SUBSTRING_INDEX(CURRENT_USER(),'@',-1);+----------------------------------------+ | SUBSTRING_INDEX(CURRENT_USER(),'@',-1) | +----------------------------------------+ | localhost | +----------------------------------------+
In some cases, you might want to run multiple mysqld servers on the same machine. You might want to test a new MySQL release while leaving your existing production setup undisturbed. Or you might want to give different users access to different mysqld servers that they manage themselves. (For example, you might be an Internet Service Provider that wants to provide independent MySQL installations for different customers.)
To run multiple servers on a single machine, each server must have unique values for several operating parameters. These can be set on the command line or in option files. See Section 4.2.3, “Specifying Program Options”.
At least the following options must be different for each server:
--portcontrols the port number for TCP/IP connections. (Alternatively, if the host has multiple network addresses, you can use--bind-addressto cause different servers to listen to different interfaces.)--socketcontrols the Unix socket file path on Unix and the name of the named pipe on Windows. On Windows, it is necessary to specify distinct pipe names only for those servers that support named-pipe connections.--shared-memory-base-name=nameThis option currently is used only on Windows. It designates the shared-memory name used by a Windows server to allow clients to connect via shared memory. It is necessary to specify distinct shared-memory names only for those servers that support shared-memory connections.
This option is used only on Unix. It indicates the path name of the file in which the server writes its process ID.
If you use the following log file options, they must be different for each server:
Section 5.2.6, “Server Log Maintenance”, discusses the log file options further.
For better performance, you can specify the following options differently for each server, to spread the load between several physical disks:
Having different temporary directories also makes it easier to determine which MySQL server created any given temporary file.
With very limited exceptions, each server should use a different
data directory, which is specified using the
--datadir=
option.
path
Warning
Normally, you should never have two servers that update data in
the same databases. This may lead to unpleasant surprises if your
operating system does not support fault-free system locking. If
(despite this warning) you run multiple servers using the same
data directory and they have logging enabled, you must use the
appropriate options to specify log file names that are unique to
each server. Otherwise, the servers try to log to the same files.
Please note that this kind of setup only works with
MyISAM and MERGE tables, and
not with any of the other storage engines.
The warning against sharing a data directory among servers also applies in an NFS environment. Allowing multiple MySQL servers to access a common data directory over NFS is a very bad idea.
The primary problem is that NFS is the speed bottleneck. It is not meant for such use.
Another risk with NFS is that you must devise a way to ensure that two or more servers do not interfere with each other. Usually NFS file locking is handled by the
lockddaemon, but at the moment there is no platform that performs locking 100% reliably in every situation.
Make it easy for yourself: Forget about sharing a data directory among servers over NFS. A better solution is to have one computer that contains several CPUs and use an operating system that handles threads efficiently.
If you have multiple MySQL installations in different locations, you
can specify the base installation directory for each server with the
--basedir=
option to cause each server to use a different data directory, log
files, and PID file. (The defaults for all these values are
determined relative to the base directory). In that case, the only
other options you need to specify are the
path--socket and
--port options. Suppose that you
install different versions of MySQL using tar
file binary distributions. These install in different locations, so
you can start the server for each installation using the command
bin/mysqld_safe under its corresponding base
directory. mysqld_safe determines the proper
--basedir option to pass to
mysqld, and you need specify only the
--socket and
--port options to
mysqld_safe.
As discussed in the following sections, it is possible to start
additional servers by setting environment variables or by specifying
appropriate command-line options. However, if you need to run
multiple servers on a more permanent basis, it is more convenient to
use option files to specify for each server those option values that
must be unique to it. The
--defaults-file option is useful for
this purpose.
You can run multiple servers on Windows by starting them manually from the command line, each with appropriate operating parameters. On Windows NT-based systems, you also have the option of installing several servers as Windows services and running them that way. General instructions for running MySQL servers from the command line or as services are given in Section 2.3, “Installing MySQL on Windows”. This section describes how to make sure that you start each server with different values for those startup options that must be unique per server, such as the data directory. These options are described in Section 5.6, “Running Multiple MySQL Servers on the Same Machine”.
To start multiple servers manually from the command line, you
can specify the appropriate options on the command line or in an
option file. It is more convenient to place the options in an
option file, but it is necessary to make sure that each server
gets its own set of options. To do this, create an option file
for each server and tell the server the file name with a
--defaults-file option when you
run it.
Suppose that you want to run mysqld on port
3307 with a data directory of C:\mydata1,
and mysqld-debug on port 3308 with a data
directory of C:\mydata2. (To do this, make
sure that before you start the servers, each data directory
exists and has its own copy of the mysql
database that contains the grant tables.) Then create two option
files. For example, create one file named
C:\my-opts1.cnf that looks like this:
[mysqld] datadir = C:/mydata1 port = 3307
Create a second file named C:\my-opts2.cnf
that looks like this:
[mysqld] datadir = C:/mydata2 port = 3308
Then start each server with its own option file:
C:\>C:\mysql\bin\mysqld --defaults-file=C:\my-opts1.cnfC:\>C:\mysql\bin\mysqld-debug --defaults-file=C:\my-opts2.cnf
On NT, each server starts in the foreground (no new prompt appears until the server exits later), so you will need to issue those two commands in separate console windows.
To shut down the servers, you must connect to each using the appropriate port number:
C:\>C:\mysql\bin\mysqladmin --port=3307 shutdownC:\>C:\mysql\bin\mysqladmin --port=3308 shutdown
Servers configured as just described allow clients to connect
over TCP/IP. If your version of Windows supports named pipes and
you also want to allow named-pipe connections, use the
mysqld or mysqld-debug
server and specify options that enable the named pipe and
specify its name. Each server that supports named-pipe
connections must use a unique pipe name. For example, the
C:\my-opts1.cnf file might be written like
this:
[mysqld] datadir = C:/mydata1 port = 3307 enable-named-pipe socket = mypipe1
Then start the server this way:
C:\> C:\mysql\bin\mysqld --defaults-file=C:\my-opts1.cnf
Modify C:\my-opts2.cnf similarly for use by
the second server.
A similar procedure applies for servers that you want to support
shared-memory connections. Enable such connections with the
--shared-memory option and
specify a unique shared-memory name for each server with the
--shared-memory-base-name option.
On NT-based systems, a MySQL server can run as a Windows service. The procedures for installing, controlling, and removing a single MySQL service are described in Section 2.3.11, “Starting MySQL as a Windows Service”.
You can also install multiple MySQL servers as services. In this case, you must make sure that each server uses a different service name in addition to all the other parameters that must be unique for each server.
For the following instructions, assume that you want to run the
mysqld server from two different versions of
MySQL that are installed at C:\mysql-5.0.19
and C:\mysql-5.5.3,
respectively. (This might be the case if you are running 5.0.19
as your production server, but also want to conduct tests using
5.5.3.)
The following principles apply when installing a MySQL service
with the --install or
--install-manual option:
If you specify no service name, the server uses the default service name of
MySQLand the server reads options from the[mysqld]group in the standard option files.If you specify a service name after the
--installoption, the server ignores the[mysqld]option group and instead reads options from the group that has the same name as the service. The server reads options from the standard option files.If you specify a
--defaults-fileoption after the service name, the server ignores the standard option files and reads options only from the[mysqld]group of the named file.
Note
In MySQL 5.5, all servers read the
[mysqld] group if they read the standard
option files, whether installed using the default service name
(MySQL) or another service name. This
allows you to use the [mysqld] group for
options that should be used by all MySQL services, and an
option group named after each service for use by the server
installed with that service name.
Based on the preceding information, you have several ways to set up multiple services. The following instructions describe some examples. Before trying any of them, be sure that you shut down and remove any existing MySQL services first.
Approach 1: Specify the options for all services in one of the standard option files. To do this, use a different service name for each server. Suppose that you want to run the 5.0.19 mysqld using the service name of
mysqld1and the 5.5.3 mysqld using the service namemysqld2. In this case, you can use the[mysqld1]group for 5.0.19 and the[mysqld2]group for 5.5.3. For example, you can set upC:\my.cnflike this:# options for mysqld1 service [mysqld1] basedir = C:/mysql-5.0.19 port = 3307 enable-named-pipe socket = mypipe1 # options for mysqld2 service [mysqld2] basedir = C:/mysql-5.5.3 port = 3308 enable-named-pipe socket = mypipe2
Install the services as follows, using the full server path names to ensure that Windows registers the correct executable program for each service:
C:\>
C:\mysql-5.0.19\bin\mysqld --install mysqld1C:\>C:\mysql-5.5.3\bin\mysqld --install mysqld2To start the services, use the services manager, or use NET START with the appropriate service names:
C:\>
NET START mysqld1C:\>NET START mysqld2To stop the services, use the services manager, or use NET STOP with the appropriate service names:
C:\>
NET STOP mysqld1C:\>NET STOP mysqld2Approach 2: Specify options for each server in separate files and use
--defaults-filewhen you install the services to tell each server what file to use. In this case, each file should list options using a[mysqld]group.With this approach, to specify options for the 5.0.19 mysqld-nt, create a file
C:\my-opts1.cnfthat looks like this:[mysqld] basedir = C:/mysql-5.0.19 port = 3307 enable-named-pipe socket = mypipe1
For the 5.5.3 mysqld, create a file
C:\my-opts2.cnfthat looks like this:[mysqld] basedir = C:/mysql-5.5.3 port = 3308 enable-named-pipe socket = mypipe2
Install the services as follows (enter each command on a single line):
C:\>
C:\mysql-5.0.19\bin\mysqld --install mysqld1--defaults-file=C:\my-opts1.cnfC:\>C:\mysql-5.5.3\bin\mysqld --install mysqld2--defaults-file=C:\my-opts2.cnfTo use a
--defaults-fileoption when you install a MySQL server as a service, you must precede the option with the service name.After installing the services, start and stop them the same way as in the preceding example.
To remove multiple services, use mysqld
--remove for each one, specifying a service name
following the --remove option. If the service
name is the default (MySQL), you can omit it.
The easiest way is to run multiple servers on Unix is to compile them with different TCP/IP ports and Unix socket files so that each one is listening on different network interfaces. Compiling in different base directories for each installation also results automatically in a separate, compiled-in data directory, log file, and PID file location for each server.
Assume that an existing 5.0.19 server is configured for the
default TCP/IP port number (3306) and Unix socket file
(/tmp/mysql.sock). To configure a new
5.5.3 server to have different operating parameters,
use a configure command something like this:
shell>./configure --with-tcp-port=port_number\--with-unix-socket-path=file_name\--prefix=/usr/local/mysql-5.5.3
Here, port_number and
file_name must be different from the
default TCP/IP port number and Unix socket file path name, and the
--prefix value should specify an
installation directory different from the one under which the
existing MySQL installation is located.
If you have a MySQL server listening on a given port number, you can use the following command to find out what operating parameters it is using for several important configurable variables, including the base directory and Unix socket file name:
shell> mysqladmin --host=host_name --port=port_number variables
With the information displayed by that command, you can tell what option values not to use when configuring an additional server.
Note that if you specify localhost as a host
name, mysqladmin defaults to using a Unix
socket file connection rather than TCP/IP. You can explicitly
specify the connection protocol to use by using the
--protocol={TCP|SOCKET|PIPE|MEMORY}
option.
You don't have to compile a new MySQL server just to start with a different Unix socket file and TCP/IP port number. It is also possible to use the same server binary and start each invocation of it with different parameter values at runtime. One way to do so is by using command-line options:
shell> mysqld_safe --socket=file_name --port=port_number
To start a second server, provide different
--socket and
--port option values, and pass a
--datadir=
option to mysqld_safe so that the server uses a
different data directory.
path
Another way to achieve a similar effect is to use environment variables to set the Unix socket file name and TCP/IP port number:
shell>MYSQL_UNIX_PORT=/tmp/mysqld-new.sockshell>MYSQL_TCP_PORT=3307shell>export MYSQL_UNIX_PORT MYSQL_TCP_PORTshell>mysql_install_db --user=mysqlshell>mysqld_safe --datadir=/path/to/datadir &
This is a quick way of starting a second server to use for testing. The nice thing about this method is that the environment variable settings apply to any client programs that you invoke from the same shell. Thus, connections for those clients are automatically directed to the second server.
Section 2.14, “Environment Variables”, includes a list of other environment variables you can use to affect mysqld.
For automatic server execution, the startup script that is executed at boot time should execute the following command once for each server with an appropriate option file path for each command:
shell> mysqld_safe --defaults-file=file_name
Each option file should contain option values specific to a given server.
On Unix, the mysqld_multi script is another way to start multiple servers. See Section 4.3.4, “mysqld_multi — Manage Multiple MySQL Servers”.
To connect with a client program to a MySQL server that is listening to different network interfaces from those compiled into your client, you can use one of the following methods:
Start the client with
--host=host_name--port=to connect via TCP/IP to a remote server, withport_number--host=127.0.0.1--port=to connect via TCP/IP to a local server, or withport_number--host=localhost--socket=to connect to a local server via a Unix socket file or a Windows named pipe.file_nameStart the client with
--protocol=TCPto connect via TCP/IP,--protocol=SOCKETto connect via a Unix socket file,--protocol=PIPEto connect via a named pipe, or--protocol=MEMORYto connect via shared memory. For TCP/IP connections, you may also need to specify--hostand--portoptions. For the other types of connections, you may need to specify a--socketoption to specify a Unix socket file or Windows named-pipe name, or a--shared-memory-base-nameoption to specify the shared-memory name. Shared-memory connections are supported only on Windows.On Unix, set the
MYSQL_UNIX_PORTandMYSQL_TCP_PORTenvironment variables to point to the Unix socket file and TCP/IP port number before you start your clients. If you normally use a specific socket file or port number, you can place commands to set these environment variables in your.loginfile so that they apply each time you log in. See Section 2.14, “Environment Variables”.Specify the default Unix socket file and TCP/IP port number in the
[client]group of an option file. For example, you can useC:\my.cnfon Windows, or the.my.cnffile in your home directory on Unix. See Section 4.2.3.3, “Using Option Files”.In a C program, you can specify the socket file or port number arguments in the
mysql_real_connect()call. You can also have the program read option files by callingmysql_options(). See Section 21.9.3, “C API Function Descriptions”.If you are using the Perl
DBD::mysqlmodule, you can read options from MySQL option files. For example:$dsn = "DBI:mysql:test;mysql_read_default_group=client;" . "mysql_read_default_file=/usr/local/mysql/data/my.cnf"; $dbh = DBI->connect($dsn, $user, $password);See Section 21.11, “MySQL Perl API”.
Other programming interfaces may provide similar capabilities for reading option files.
The DTrace probes in the MySQL server are designed to provide
information about the execution of queries within MySQL and the
different areas of the system being utilized during that process.
The organization and triggering of the probes means that the
execution of an entire query can be monitored with one level of
probes (query-start and
query-done) but by monitoring other probes you
can get successively more detailed information about the execution
of the query in terms of the locks used, sort methods and even
row-by-row and storage-engine level execution information.
The DTrace probes are organized so that you can follow the entire query process, from the point of connection from a client, through the query execution, row-level operations, and back out again. You can think of the probes as being fired within a specific sequence during a typical client connect/execute/disconnect sequence, as shown in the following figure.
Global information is provided in the arguments to the DTrace probes
at various levels. Global information, that is, the connection ID
and user/host and where relevant the query string, is provided at
key levels (connection-start,
command-start, query-start,
and query-exec-start). As you go deeper into the
probes, it is assumed either you are only interested in the
individual executions (row-level probes provide information on the
database and table name only), or that you will combine the
row-level probes with the notional parent probes to provide the
information about a specific query. Examples of this will be given
as the format and arguments of each probe are provided.
For more information on DTrace and writing DTrace scripts, read the DTrace User Guide.
Support for DTrace probes was added in MySQL 5.4.0. DTrace probes in
MySQL are supported on Solaris 10 Update 5 (Solaris 5/08), and
OpenSolaris 2008.05 and higher on SPARC, x86 and x86_64 platforms.
Probes are also supported on Mac OS X 10.4 and higher. Enabling the
probes should be automatic on these platforms. To explicitly enable
or disable the probes during building, use the
--enable-dtrace or
--disable-dtrace
option to configure.
- 5.7.1.1. Connection Probes
- 5.7.1.2. Command Probes
- 5.7.1.3. Query Probes
- 5.7.1.4. Query Parsing Probes
- 5.7.1.5. Query Cache Probes
- 5.7.1.6. Query Execution Probes
- 5.7.1.7. Row-Level Probes
- 5.7.1.8. Read Row Probes
- 5.7.1.9. Index Probes
- 5.7.1.10. Lock Probes
- 5.7.1.11. Filesort Probes
- 5.7.1.12. Statement Probes
- 5.7.1.13. Network Probes
- 5.7.1.14. Keycache Probes
MySQL supports the following static probes, organized into groups of functionality, starting with MySQL 5.4.0.
Table 5.8. MySQL DTrace Probes
| Group | Probes | Introduced |
|---|---|---|
| Connection | connection-start, connection-done | 5.4.0 |
| Command | command-start, command-done | 5.4.0 |
| Query | query-start, query-done | 5.4.0 |
| Query Parsing | query-parse-start,
query-parse-done | 5.4.0 |
| Query Cache | query-cache-hit, query-cache-miss | 5.4.0 |
| Query Execution | query-exec-start, query-exec-done | 5.4.0 |
| Row Level | insert-row-start, insert-row-done | 5.4.0 |
update-row-start, update-row-done | 5.4.0 | |
delete-row-start, delete-row-done | 5.4.0 | |
| Row Reads | read-row-start, read-row-done | 5.4.0 |
| Index Reads | index-read-row-start,
index-read-row-done | 5.4.0 |
| Lock | handler-rdlock-start,
handler-rdlock-done | 5.4.0 |
handler-wrlock-start,
handler-wrlock-done | 5.4.0 | |
handler-unlock-start,
handler-unlock-done | 5.4.0 | |
| Filesort | filesort-start, filesort-done | 5.4.0 |
| Statement | select-start, select-done | 5.4.0 |
insert-start, insert-done | 5.4.0 | |
insert-select-start,
insert-select-done | 5.4.0 | |
update-start, update-done | 5.4.0 | |
multi-update-start,
multi-update-done | 5.4.0 | |
delete-start, delete-done | 5.4.0 | |
multi-delete-start,
multi-delete-done | 5.4.0 | |
| Network | net-read-start, net-read-done,
net-write-start,
net-write-done | 5.4.0 |
| Keycache | keycache-read-start,
keycache-read-block,
keycache-read-done,
keycache-read-hit,
keycache-read-miss,
keycache-write-start,
keycache-write-block,
keycache-write-done | 5.4.0 |
Note
When extracting the argument data from the probes, each argument
is available as
arg, starting
with Narg0. To identify each argument within
the definitions they are provided with a descriptive name, but
you must access the information using the corresponding
arg parameter.
N
The connection-start and
connection-done probes enclose a connection
from a client, regardless of whether the connection is through a
socket or network connection.
connection-start(connectionid, user, host) connection-done(status, connectionid)
connection-start— is triggered after a connection and successful login/authentication have been completed by a client. The arguments contain the connection information:connectionid— is anunsigned longcontaining the connection ID. This is the same as the process ID shown as theIdvalue in the output fromSHOW PROCESSLIST.user— is the username used when authenticating. The value will be blank for the anonymous user.host— is the host of the client connection. For a connection made using UNIX sockets, the value will be blank.
connection-done— is triggered just as the connection to the client has been closed. The arguments are:status— the status of the connection when it was closed. A logout operation will have a value of 0; any other termination of the connection has a nonzero value.connectionid— the connection ID of the connection that was closed.
The following D script will quantify and summarize the average duration of individual connections, and provide a count, dumping the information every 60 seconds:
#!/usr/sbin/dtrace -s
mysql*:::connection-start
{
self->start = timestamp;
}
mysql*:::connection-done
/self->start/
{
@ = quantize(((timestamp - self->start)/1000000));
self->start = 0;
}
tick-60s
{
printa(@);
}
When executed on a server with a large number of clients you might see output similar to this:
1 57413 :tick-60s
value ------------- Distribution ------------- count
-1 | 0
0 |@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@ 30011
1 | 59
2 | 5
4 | 20
8 | 29
16 | 18
32 | 27
64 | 30
128 | 11
256 | 10
512 | 1
1024 | 6
2048 | 8
4096 | 9
8192 | 8
16384 | 2
32768 | 1
65536 | 1
131072 | 0
262144 | 1
524288 | 0
The command probes are executed before and after a client
command is executed, including any SQL statement that might be
executed during that period. Commands include operations such as
the initialization of the DB, use of the
COM_CHANGE_USER operation (supported by the
MySQL protocol), and manipulation of prepared statements. Many
of these commands are used only by the MySQL client API from
various connectors such as PHP and Java.
command-start(connectionid, command, user, host) command-done(status)
command-start— triggered when a command is submitted to the server.connectionid— the connection ID of the client executing the command.command— an integer representing the command that was executed. Possible values are shown in the following table.Value Name Description 00 COM_SLEEP Internal thread state 01 COM_QUIT Close connection 02 COM_INIT_DB Select database ( USE ...)03 COM_QUERY Execute a query 04 COM_FIELD_LIST Get a list of fields 05 COM_CREATE_DB Create a database (deprecated) 06 COM_DROP_DB Drop a database (deprecated) 07 COM_REFRESH Refresh connection 08 COM_SHUTDOWN Shutdown server 09 COM_STATISTICS Get statistics 10 COM_PROCESS_INFO Get processes ( SHOW PROCESSLIST)11 COM_CONNECT Initialize connection 12 COM_PROCESS_KILL Kill process 13 COM_DEBUG Get debug information 14 COM_PING Ping 15 COM_TIME Internal thread state 16 COM_DELAYED_INSERT Internal thread state 17 COM_CHANGE_USER Change user 18 COM_BINLOG_DUMP Used by a replication slave or mysqlbinlog to initiate a binary log read 19 COM_TABLE_DUMP Used by a replication slave to get the master table information 20 COM_CONNECT_OUT Used by a replication slave to log a connection to the server 21 COM_REGISTER_SLAVE Used by a replication slave during registration 22 COM_STMT_PREPARE Prepare a statement 23 COM_STMT_EXECUTE Execute a statement 24 COM_STMT_SEND_LONG_DATA Used by a client when requesting extended data 25 COM_STMT_CLOSE Close a prepared statement 26 COM_STMT_RESET Reset a prepared statement 27 COM_SET_OPTION Set a server option 28 COM_STMT_FETCH Fetch a prepared statement user— the user executing the command.host— the client host.
command-done— triggered when the command execution completes. Thestatusargument contains 0 if the command executed successfully, or 1 if the statement was terminated before normal completion.
The command-start and
command-done probes are best used when
combined with the statement probes to get an idea of overall
execution time.
The query-start and
query-done probes are triggered when a
specific query is received by the server and when the query has
been completed and the information has been successfully sent to
the client.
query-start(query, connectionid, database, user, host) query-done(status)
query-start— is triggered after the query string has been received from the client. The arguments are:query— the full text of the submitted query.connectionid— the connection ID of the client that submitted the query. The connection ID equals the connection ID returned when the client first connects and theIdvalue in the output fromSHOW PROCESSLIST.database— the database name on which the query is being executed.user— the username used to connect to the server.host— the hostname of the client.
query-done— is triggered once the query has been executed and the information has been returned to the client. The probe includes a single argument,status, which returns 0 when the query is successfully executed and 1 if there was an error.
You can get a simple report of the execution time for each query using the following D script:
#!/usr/sbin/dtrace -s
#pragma D option quiet
dtrace:::BEGIN
{
printf("%-20s %-20s %-40s %-9s\n", "Who", "Database", "Query", "Time(ms)");
}
mysql*:::query-start
{
self->query = copyinstr(arg0);
self->connid = arg1;
self->db = copyinstr(arg2);
self->who = strjoin(copyinstr(arg3),strjoin("@",copyinstr(arg4)));
self->querystart = timestamp;
}
mysql*:::query-done
{
printf("%-20s %-20s %-40s %-9d\n",self->who,self->db,self->query,
(timestamp - self->querystart) / 1000000);
}When executing the above script you should get a basic idea of the execution time of your queries:
shell> ./query.d Who Database Query Time(ms) root@localhost test select * from t1 order by i limit 10 0 root@localhost test set global query_cache_size=0 0 root@localhost test select * from t1 order by i limit 10 776 root@localhost test select * from t1 order by i limit 10 773 root@localhost test select * from t1 order by i desc limit 10 795
The query parsing probes are triggered before the original SQL statement is parsed and when the parsing of the statement and determination of the execution model required to process the statement has been completed:
query-parse-start(query) query-parse-done(status)
query-parse-start— is triggered just before the statement is parsed by the MySQL query parser. The single argument,query, is a string containing the full text of the original query.query-parse-done— is triggered when the parsing of the original statement has been completed. Thestatusis an integer describing the status of the operation. A0indicates that the query was successfully parsed. A1indicates that the parsing of the query failed.
For example, you could monitor the execution time for parsing a given query using the following D script:
#!/usr/sbin/dtrace -s
#pragma D option quiet
mysql*:::query-parse-start
{
self->parsestart = timestamp;
self->parsequery = copyinstr(arg0);
}
mysql*:::query-parse-done
/arg0 == 0/
{
printf("Parsing %s: %d microseconds\n", self->parsequery,((timestamp - self->parsestart)/1000));
}
mysql*:::query-parse-done
/arg0 != 0/
{
printf("Error parsing %s: %d microseconds\n", self->parsequery,((timestamp - self->parsestart)/1000));
}
In the above script a predicate is used on
query-parse-done so that different output is
generated based on the status value of the probe.
When running the script and monitoring the execution:
shell> ./query-parsing.d Error parsing select from t1 join (t2) on (t1.i = t2.i) order by t1.s,t1.i limit 10: 36 ms Parsing select * from t1 join (t2) on (t1.i = t2.i) order by t1.s,t1.i limit 10: 176 ms
The query cache probes are fired when executing any query. The
query-cache-hit query is triggered when a
query exists in the query cache and can be used to return the
query cache information. The arguments contain the original
query text and the number of rows returned from the query cache
for the query. If the query is not within the query cache, or
the query cache is not enabled, then the
query-cache-miss probe is triggered instead.
query-cache-hit(query, rows) query-cache-miss(query)
query-cache-hit— triggered when the query has been found within the query cache. The first argument,query, contains the original text of the query. The second argument,rows, is an integer containing the number of rows in the cached query.query-cache-misss— triggered when the query is not found within the query cache. The first argument,query, contains the original text of the query.
The query cache probes are best combined with a probe on the main query so that you can determine the differences in times between using or not using the query cache for specified queries. For example, in the following D script, the query and query cache information are combined into the information output during monitoring:
#!/usr/sbin/dtrace -s
#pragma D option quiet
dtrace:::BEGIN
{
printf("%-20s %-20s %-40s %2s %-9s\n", "Who", "Database", "Query", "QC", "Time(ms)");
}
mysql*:::query-start
{
self->query = copyinstr(arg0);
self->connid = arg1;
self->db = copyinstr(arg2);
self->who = strjoin(copyinstr(arg3),strjoin("@",copyinstr(arg4)));
self->querystart = timestamp;
self->qc = 0;
}
mysql*:::query-cache-hit
{
self->qc = 1;
}
mysql*:::query-cache-miss
{
self->qc = 0;
}
mysql*:::query-done
{
printf("%-20s %-20s %-40s %-2s %-9d\n",self->who,self->db,self->query,(self->qc ? "Y" : "N"),
(timestamp - self->querystart) / 1000000);
}When executing the script you can see the effects of the query cache. Initially the query cache is disabled. If you set the query cache size and then execute the query multiple times you should see that the query cache is being used to return the query data:
shell> ./query-cache.d root@localhost test select * from t1 order by i limit 10 N 1072 root@localhost set global query_cache_size=262144 N 0 root@localhost test select * from t1 order by i limit 10 N 781 root@localhost test select * from t1 order by i limit 10 Y 0
The query execution probe is triggered when the actual execution of the query starts, after the parsing and checking the query cache but before any privilege checks or optimization. By comparing the difference between the start and done probes you can monitor the time actually spent servicing the query (instead of just handling the parsing and other elements of the query).
query-exec-start(query, connectionid, database, user, host, exec_type) query-exec-done(status)
Note
The information provided in the arguments for
query-start and
query-exec-start are almost identical and
designed so that you can choose to monitor either the entire
query process (using query-start) or only
the execution (using query-exec-start)
while exposing the core information about the user, client,
and query being executed.
query-exec-start— is triggered when the execution of a individual query is started. The arguments are:query— the full text of the submitted query.connectionid— the connection ID of the client that submitted the query. The connection ID equals the connection ID returned when the client first connects and theIdvalue in the output fromSHOW PROCESSLIST.database— the database name on which the query is being executed.user— the username used to connect to the server.host— the hostname of the client.exec_type— the type of execution. Execution types are determined based on the contents of the query and where it was submitted. The values for each type are shown in the following table.Value Description 0 Executed query from sql_parse, top-level query. 1 Executed prepared statement 2 Executed cursor statement 3 Executed query in stored procedure
query-exec-done— is triggered when the execution of the query has completed. The probe includes a single argument,status, which returns 0 when the query is successfully executed and 1 if there was an error.
The *row-{start,done} probes are triggered
each time a row operation is pushed down to a storage engine.
For example, if you execute an
INSERT statement with 100 rows of
data, then the insert-row-start and
insert-row-done probes will be triggered 100
times each, for each row insert.
insert-row-start(database, table) insert-row-done(status) update-row-start(database, table) update-row-done(status) delete-row-start(database, table) delete-row-done(status)
insert-row-start— is triggered before a row is inserted into a table.insert-row-done— is triggered after a row is inserted into a table.update-row-start— is triggered before a row is updated in a table.update-row-done— is triggered before a row is updated in a table.delete-row-start— is triggered before a row is deleted from a table.delete-row-done— is triggered before a row is deleted from a table.
The arguments supported by the probes are consistent for the
corresponding start and
done probes in each case:
database— the database name.table— the table name.status— the status; 0 for success or 1 for failure.
Because the row-level probes are triggered for each individual
row access, these probes can be triggered many thousands of
times each second, which may have a detrimental effect on both
the monitoring script and MySQL. The DTrace environment should
limit the triggering on these probes to prevent the performance
being adversely affected. Either use the probes sparingly, or
use counter or aggregation functions to report on these probes
and then provide a summary when the script terminates or as part
of a query-done or
query-exec-done probes.
The following example script summarizes the duration of each row operation within a larger query:
#!/usr/sbin/dtrace -s
#pragma D option quiet
dtrace:::BEGIN
{
printf("%-2s %-10s %-10s %9s %9s %-s \n",
"St", "Who", "DB", "ConnID", "Dur ms", "Query");
}
mysql*:::query-start
{
self->query = copyinstr(arg0);
self->who = strjoin(copyinstr(arg3),strjoin("@",copyinstr(arg4)));
self->db = copyinstr(arg2);
self->connid = arg1;
self->querystart = timestamp;
self->rowdur = 0;
}
mysql*:::query-done
{
this->elapsed = (timestamp - self->querystart) /1000000;
printf("%2d %-10s %-10s %9d %9d %s\n",
arg0, self->who, self->db,
self->connid, this->elapsed, self->query);
}
mysql*:::query-done
/ self->rowdur /
{
printf("%34s %9d %s\n", "", (self->rowdur/1000000), "-> Row ops");
}
mysql*:::insert-row-start
{
self->rowstart = timestamp;
}
mysql*:::delete-row-start
{
self->rowstart = timestamp;
}
mysql*:::update-row-start
{
self->rowstart = timestamp;
}
mysql*:::insert-row-done
{
self->rowdur += (timestamp-self->rowstart);
}
mysql*:::delete-row-done
{
self->rowdur += (timestamp-self->rowstart);
}
mysql*:::update-row-done
{
self->rowdur += (timestamp-self->rowstart);
}
Running the above script with a query that inserts data into a table, you can monitor the exact time spent performing the raw row insertion:
St Who DB ConnID Dur ms Query
0 @localhost test 13 20767 insert into t1(select * from t2)
4827 -> Row ops
The read row probes are triggered at a storage engine level each
time a row read operation occurs. These probes are specified
within each storage engine (as opposed to the
*row-start probes which are in the storage
engine interface). These probes can therefore be used to monitor
individual storage engine row-level operations and performance.
Because these probes are triggered around the storage engine row
read interface, they may be hit a significant number of times
during a basic query.
read-row-start(database, table, scan_flag) read-row-done(status)
read-row-start— triggered when a row is read by the storage engine from the specifieddatabaseandtable. Thescan_flagis set to 1 (true) when the read is part of a table scan (that is, a sequential read), or 0 (false) when the read is of a specific record.read-row-done— triggerd when a row read operation within a storage engine completes. Thestatusreturns 0 on success, or a positive value on failure.
The index probes are triggered each time a a row is read using one of the indexes for the specified table. The probe is triggered within the corresponding storage engine for the table.
index-read-row-start(database, table) index-read-row-done(status)
index-read-row-start— triggered when a row is read by the storage engine from the specifieddatabaseandtable.index-read-row-done— triggerd when an indexed row read operation within a storage engine completes. Thestatusreturns 0 on success, or a positive value on failure.
The lock probes are called whenever an external lock is requested by MySQL for a table using the corresponding lock mechanism on the table as defined by the table's engine type. There are three different types of lock, the read lock, write lock, and unlock operations. Using the probes you can determine the duration of the external locking routine (that is, the time taken by the storage engine to implement the lock, including any time waiting for another lock to become free) and the total duration of the lock/unlock process.
handler-rdlock-start(database, table) handler-rdlock-done(status) handler-wrlock-start(database, table) handler-wrlock-done(status) handler-unlock-start(database, table) handler-unlock-done(status)
handler-rdlock-start— triggered when a read lock is requested on the specifieddatabaseandtable.handler-wrlock-start— triggered when a write lock is requested on the specifieddatabaseandtable.handler-unlock-start— triggered when an unlock request is made on the specifieddatabaseandtable.handler-rdlock-done— triggered when a read lock request completes. Thestatusis 0 if the lock operation succeeded, or>0on failure.handler-wrlock-done— triggered when a write lock request completes. Thestatusis 0 if the lock operation succeeded, or>0on failure.handler-unlock-done— triggered when an unlock request completes. Thestatusis 0 if the unlock operation succeeded, or>0on failure.
You can use arrays to monitor the locking and unlocking of individual tables and then calculate the duration of the entire table lock using the following script:
#!/usr/sbin/dtrace -s
#pragma D option quiet
mysql*:::handler-rdlock-start
{
self->rdlockstart = timestamp;
this->lockref = strjoin(copyinstr(arg0),strjoin("@",copyinstr(arg1)));
self->lockmap[this->lockref] = self->rdlockstart;
printf("Start: Lock->Read %s.%s\n",copyinstr(arg0),copyinstr(arg1));
}
mysql*:::handler-wrlock-start
{
self->wrlockstart = timestamp;
this->lockref = strjoin(copyinstr(arg0),strjoin("@",copyinstr(arg1)));
self->lockmap[this->lockref] = self->rdlockstart;
printf("Start: Lock->Write %s.%s\n",copyinstr(arg0),copyinstr(arg1));
}
mysql*:::handler-unlock-start
{
self->unlockstart = timestamp;
this->lockref = strjoin(copyinstr(arg0),strjoin("@",copyinstr(arg1)));
printf("Start: Lock->Unlock %s.%s (%d ms lock duration)\n",
copyinstr(arg0),copyinstr(arg1),
(timestamp - self->lockmap[this->lockref])/1000000);
}
mysql*:::handler-rdlock-done
{
printf("End: Lock->Read %d ms\n",
(timestamp - self->rdlockstart)/1000000);
}
mysql*:::handler-wrlock-done
{
printf("End: Lock->Write %d ms\n",
(timestamp - self->wrlockstart)/1000000);
}
mysql*:::handler-unlock-done
{
printf("End: Lock->Unlock %d ms\n",
(timestamp - self->unlockstart)/1000000);
}
When executed, you should get information both about the duration of the locking process itself, and of the locks on a specific table:
Start: Lock->Read test.t2 End: Lock->Read 0 ms Start: Lock->Unlock test.t2 (25743 ms lock duration) End: Lock->Unlock 0 ms Start: Lock->Read test.t2 End: Lock->Read 0 ms Start: Lock->Unlock test.t2 (1 ms lock duration) End: Lock->Unlock 0 ms Start: Lock->Read test.t2 End: Lock->Read 0 ms Start: Lock->Unlock test.t2 (1 ms lock duration) End: Lock->Unlock 0 ms Start: Lock->Read test.t2 End: Lock->Read 0 ms
The filesort probes are triggered whenever a filesort operation
is applied to a table. For more information on filesort and the
conditions under which it occurs, see
Section 7.2.14, “ORDER BY Optimization”.
filesort-start(database, table) filesort-done(status, rows)
filesort-start— is triggered when the filesort operation starts on a table. The two arguments to the probe,databaseandtable, will identify the table being sorted.filesort-done— is triggered when the filesort operation completes. Two arguments are supplied, thestatus(0 for success, 1 for failure), and the number of rows sorted during the filesort process.
An example of this is in the following script, which tracks the duration of the filesort process in addition to the duration of the main query:
#!/usr/sbin/dtrace -s
#pragma D option quiet
dtrace:::BEGIN
{
printf("%-2s %-10s %-10s %9s %18s %-s \n",
"St", "Who", "DB", "ConnID", "Dur microsec", "Query");
}
mysql*:::query-start
{
self->query = copyinstr(arg0);
self->who = strjoin(copyinstr(arg3),strjoin("@",copyinstr(arg4)));
self->db = copyinstr(arg2);
self->connid = arg1;
self->querystart = timestamp;
self->filesort = 0;
self->fsdb = "";
self->fstable = "";
}
mysql*:::filesort-start
{
self->filesort = timestamp;
self->fsdb = copyinstr(arg0);
self->fstable = copyinstr(arg1);
}
mysql*:::filesort-done
{
this->elapsed = (timestamp - self->filesort) /1000;
printf("%2d %-10s %-10s %9d %18d Filesort on %s\n",
arg0, self->who, self->fsdb,
self->connid, this->elapsed, self->fstable);
}
mysql*:::query-done
{
this->elapsed = (timestamp - self->querystart) /1000;
printf("%2d %-10s %-10s %9d %18d %s\n",
arg0, self->who, self->db,
self->connid, this->elapsed, self->query);
}
Executing a query on a large table with an ORDER
BY clause that triggers a filesort, and then creating
an index on the table and then repeating the same query, you can
see the difference in execution speed:
St Who DB ConnID Dur microsec Query 0 @localhost test 14 11335469 Filesort on t1 0 @localhost test 14 11335787 select * from t1 order by i limit 100 0 @localhost test 14 466734378 create index t1a on t1 (i) 0 @localhost test 14 26472 select * from t1 order by i limit 100
The individual statement probes are provided to give specific
information about different statement types. For the start
probes the string of the query is provided as a the only
argument. Depending on the statement type, the information
provided by the corresponding done probe will differ. For all
done probes the status of the operation (0
for success, >0 for failure) is provided.
For SELECT,
INSERT,
INSERT ... (SELECT FROM
...), DELETE, and
DELETE FROM
t1,t2 operations the number of rows affected is
returned.
For UPDATE and
UPDATE t1,t2
... statements the number of rows matched and the
number of rows actually changed is provided. This is because the
number of rows actually matched by the corresponding
WHERE clause, and the number of rows changed
can differ. MySQL does not update the value of a row if the
value already matches the new setting.
select-start(query) select-done(status,rows) insert-start(query) insert-done(status,rows) insert-select-start(query) insert-select-done(status,rows) update-start(query) update-done(status,rowsmatched,rowschanged) multi-update-start(query) multi-update-done(status,rowsmatched,rowschanged) delete-start(query) delete-done(status,rows) multi-delete-start(query) multi-delete-done(status,rows)
select-start— triggered before aSELECTstatement.select-done— triggered at the end of aSELECTstatement.insert-start— triggered before aINSERTstatement.insert-done— triggered at the end of anINSERTstatement.insert-select-start— triggered before anINSERT ... SELECTstatement.insert-select-done— triggered at the end of anINSERT ... SELECTstatement.update-start— triggered before anUPDATEstatement.update-done— triggered at the end of anUPDATEstatement.multi-update-start— triggered before anUPDATEstatement involving multiple tables.multi-update-done— triggered at the end of anUPDATEstatement involving multiple tables.delete-start— triggered before aDELETEstatement.delete-done— triggered at the end of aDELETEstatement.multi-delete-start— triggered before aDELETEstatement involving multiple tables.multi-delete-done— triggered at the end of aDELETEstatement involving multiple tables.
The arguments for the statement probes are:
query— the query string.status— the status of the query.0for success, and>0for failure.rows— the number of rows affected by the statement. This returns the number rows found forSELECT, the number of rows deleted forDELETE, and the number of rows successfully inserted forINSERT.rowsmatched— the number of rows matched by theWHEREclause of anUPDATEoperation.rowschanged— the number of rows actually changed during anUPDATEoperation.
You use these probes to monitor the execution of these statement types without having to monitor the user or client executing the statements. A simple example of this is to track the execution times:
#!/usr/sbin/dtrace -s
#pragma D option quiet
dtrace:::BEGIN
{
printf("%-60s %-8s %-8s %-8s\n", "Query", "RowsU", "RowsM", "Dur (ms)");
}
mysql*:::update-start, mysql*:::insert-start,
mysql*:::delete-start, mysql*:::multi-delete-start,
mysql*:::multi-delete-done, mysql*:::select-start,
mysql*:::insert-select-start, mysql*:::multi-update-start
{
self->query = copyinstr(arg0);
self->querystart = timestamp;
}
mysql*:::insert-done, mysql*:::select-done,
mysql*:::delete-done, mysql*:::multi-delete-done, mysql*:::insert-select-done
/ self->querystart /
{
this->elapsed = ((timestamp - self->querystart)/1000000);
printf("%-60s %-8d %-8d %d\n",
self->query,
0,
arg1,
this->elapsed);
self->querystart = 0;
}
mysql*:::update-done, mysql*:::multi-update-done
/ self->querystart /
{
this->elapsed = ((timestamp - self->querystart)/1000000);
printf("%-60s %-8d %-8d %d\n",
self->query,
arg1,
arg2,
this->elapsed);
self->querystart = 0;
}When executed you can see the basic execution times and rows matches:
Query RowsU RowsM Dur (ms) select * from t2 0 275 0 insert into t2 (select * from t2) 0 275 9 update t2 set i=5 where i > 75 110 110 8 update t2 set i=5 where i < 25 254 134 12 delete from t2 where i < 5 0 0 0
Another alternative is to use the aggregation functions in DTrace to aggregate the execution time of individual statements together:
#!/usr/sbin/dtrace -s
#pragma D option quiet
mysql*:::update-start, mysql*:::insert-start,
mysql*:::delete-start, mysql*:::multi-delete-start,
mysql*:::multi-delete-done, mysql*:::select-start,
mysql*:::insert-select-start, mysql*:::multi-update-start
{
self->querystart = timestamp;
}
mysql*:::select-done
{
@statements["select"] = sum(((timestamp - self->querystart)/1000000));
}
mysql*:::insert-done, mysql*:::insert-select-done
{
@statements["insert"] = sum(((timestamp - self->querystart)/1000000));
}
mysql*:::update-done, mysql*:::multi-update-done
{
@statements["update"] = sum(((timestamp - self->querystart)/1000000));
}
mysql*:::delete-done, mysql*:::multi-delete-done
{
@statements["delete"] = sum(((timestamp - self->querystart)/1000000));
}
tick-30s
{
printa(@statements);
}
The script just shown aggregates the times spent doing each operation, which could be used to help benchmark a standard suite of tests.
delete 0 update 0 insert 23 select 2484 delete 0 update 0 insert 39 select 10744 delete 0 update 26 insert 56 select 10944 delete 0 update 26 insert 2287 select 15985
The network probes monitor the transfer of information from the MySQL server and clients of all types over the network. The probes are defined as follows:
net-read-start() net-read-done(status, bytes) net-write-start(bytes) net-write-done(status)
net-read-start— triggered when a network read operation is started.net-read-done— triggered when the network read operation completes. Thestatusis anintegerrepresenting the return status for the operation,0for success and1for failure. Thebytesargument is an integer specifying the number of bytes read during the process.net-start-bytes— triggered when data is written to a network socket. The single argument,bytes, specifies the number of bytes written to the network socket.net-write-done— triggered when the network write operation has completed. The single argument,status, is an integer representing the return status for the operation,0for success and1for failure.
You can use the network probes to monitor the time spent reading
from and writing to network clients during execution. The
following D script provides an example of this. Both the
cumlative time for the read or write is calculated, and the
number of bytes. Note that the dynamic variable size has been
increased (using the dynvarsize option) to
cope with the rapid firing of the individual probes for the
network reads/writes.
#!/usr/sbin/dtrace -s
#pragma D option quiet
#pragma D option dynvarsize=4m
dtrace:::BEGIN
{
printf("%-2s %-30s %-10s %9s %18s %-s \n",
"St", "Who", "DB", "ConnID", "Dur microsec", "Query");
}
mysql*:::query-start
{
self->query = copyinstr(arg0);
self->who = strjoin(copyinstr(arg3),strjoin("@",copyinstr(arg4)));
self->db = copyinstr(arg2);
self->connid = arg1;
self->querystart = timestamp;
self->netwrite = 0;
self->netwritecum = 0;
self->netwritebase = 0;
self->netread = 0;
self->netreadcum = 0;
self->netreadbase = 0;
}
mysql*:::net-write-start
{
self->netwrite += arg0;
self->netwritebase = timestamp;
}
mysql*:::net-write-done
{
self->netwritecum += (timestamp - self->netwritebase);
self->netwritebase = 0;
}
mysql*:::net-read-start
{
self->netreadbase = timestamp;
}
mysql*:::net-read-done
{
self->netread += arg1;
self->netreadcum += (timestamp - self->netreadbase);
self->netreadbase = 0;
}
mysql*:::query-done
{
this->elapsed = (timestamp - self->querystart) /1000000;
printf("%2d %-30s %-10s %9d %18d %s\n",
arg0, self->who, self->db,
self->connid, this->elapsed, self->query);
printf("Net read: %d bytes (%d ms) write: %d bytes (%d ms)\n",
self->netread, (self->netreadcum/1000000),
self->netwrite, (self->netwritecum/1000000));
}When executing the above script on a machine with a remote client, you can see that approximately a third of the time spent executing the query is related to writing the query results back to the client.
St Who DB ConnID Dur microsec Query 0 root@::ffff:192.168.0.108 test 31 3495 select * from t1 limit 1000000 Net read: 0 bytes (0 ms) write: 10000075 bytes (1220 ms)
The keycache probes are triggered when using the index key cache used with the MyISAM storage engine. Probes exist to monitor when data is read into the keycache, cached key data is written from the cache into a cached file, or when accessing the keycache.
Keycache usage indicates when data is read or written from the index files into the cache, and can be used to monitor how efficient the memory allocatd to the keycache is being used. A high number of keycache reads across a range of queries may indicate that the keycache is too small for size of data being accessed.
keycache-read-start(filepath, bytes, mem_used, mem_free) keycache-read-block(bytes) keycache-read-hit() keycache-read-miss() keycache-read-done(mem_used, mem_free) keycache-write-start(filepath, bytes, mem_used, mem_free) keycache-write-block(bytes) keycache-write-done(mem_used, mem_free)
When reading data from the index files into the keycache, the
process first initializes the read operation (indicated by
keycache-read-start), then loads blocks of
data (keycache-read-block), and then the read
block is either matches the data being identified
(keycache-read-hit) or more data needs to be
read (keycache-read-miss). Once the read
operation has completed, reading stops with the
keycache-read-done.
Data will be read from the index file into the keycache only when the specified key is not aleady within the keycache.
keycache-read-start— triggered when the keycache read operation is started. Data is read from the specifiedfilepath, reading the specified number ofbytes. Themem_usedandmem_availindicate memory currently used by the keycache and the amount of memory available within the keycache.keycache-read-block— triggered when the keycache reads a block of data, of the specified number ofbytes, from the index file into the keycache.keycache-read-hit— triggered when the block of data read from the index file matches the key data requested.keycache-read-miss— triggered when the block of data read from the index file does not match the key data needed.keycache-read-done— triggered when the keycache read operation has completed. Themem_usedandmem_availindicate memory currently used by the keycache and the amount of memory available within the keycache.
Keycache writes occur when the index information is updated
during an INSERT, UPDATE,
or DELETE operation, and the cached key
information is flushed back to the index file.
keycache-write-start— triggered when the keycache write operation is started. Data is written to the specifiedfilepath, reading the specified number ofbytes. Themem_usedandmem_availindicate memory currently used by the keycache and the amount of memory available within the keycache.keycache-write-block— triggered when the keycache writes a block of data, of the specified number ofbytes, to the index file from the keycache.keycache-write-done— triggered when the keycache write operation has completed. Themem_usedandmem_availindicate memory currently used by the keycache and the amount of memory available within the keycache.